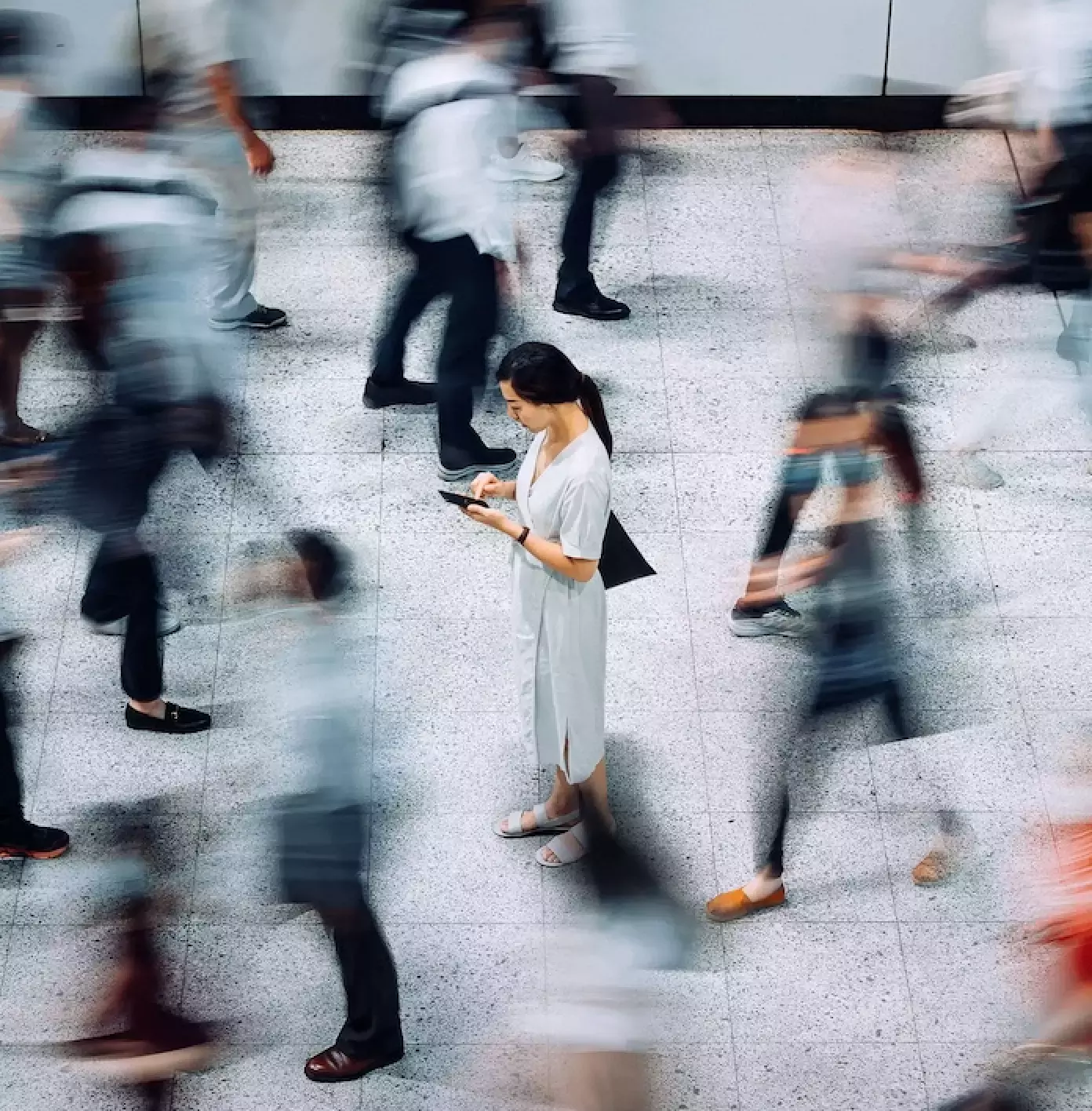
The most damaging cyber threats today don’t target machines or systems—they target humans. From employees clicking on malicious links to being deceived by emails posing as executives and suppliers, human-targeted attacks jeopardize businesses worldwide every day. That’s why we developed superior solutions to address the four top human risks: threat, impersonation, data loss and identity.
2024 Data Loss Landscape Report
2024 State of the Phish
Google and Yahoo will enforce stricter email rules. Are you ready?
Proofpoint Named a Leader in The Forrester Wave™: Enterprise Email Security, Q2 2023
Featured | Analyst Report
Proofpoint Named a Leader in The Forrester Wave™: Enterprise Email Security, Q2 2023
Learn more2024 Data Loss Landscape Report
2024 State of the Phish
Google and Yahoo will enforce stricter email rules. Are you ready?
Proofpoint Named a Leader in The Forrester Wave™: Enterprise Email Security, Q2 2023
Featured | Analyst Report
Proofpoint Named a Leader in The Forrester Wave™: Enterprise Email Security, Q2 2023
Learn moreCybersecurity’s most advanced detection stack
Detect a wider range of threats. Block attacks more quickly. Contend with fewer false positives. Four layers of detection give you unmatched protection that evolves at the speed of today’s threats.
Start protecting your people today