We are Proofpoint
Stop threats at every layer–people, data, and AI–with intent–based protection
Stopping
95M
BEC attacks per year
Protecting
2.7M
customers
Of the F100
83
use Proofpoint to stop attacks and defend their data
Numbers only ever tell part of the story.
See customer storiesHuman- and AI-centric security for the agentic workspace
Proofpoint unifies collaboration, data, and AI security so you can move faster without increasing risk.
#
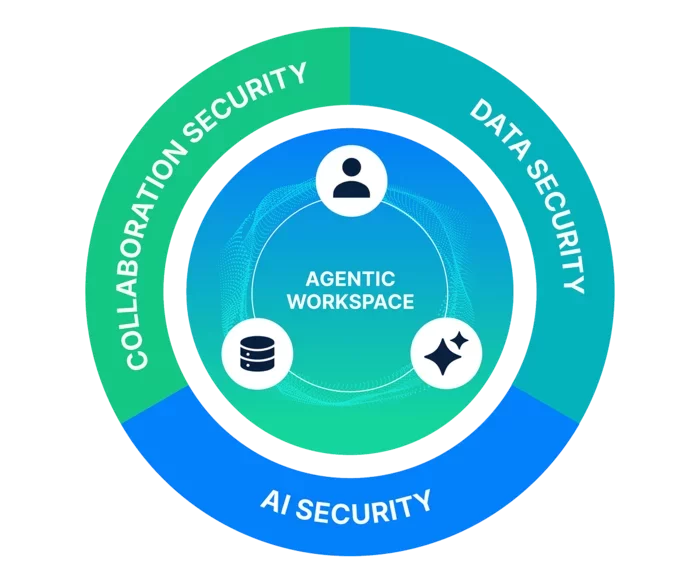
Collaboration Security
Safeguard people and AI agents against targeted threats across email, messaging, social media, cloud apps, and file-sharing services.
Data Security & Governance
Protect sensitive data and communications from loss and misuse with continuous visibility and control over storage, access, and usage.
AI Security
Control how LLMs and AI agents access and share data to prevent leaks, stop prompt-based attacks, and enable safe AI adoption.
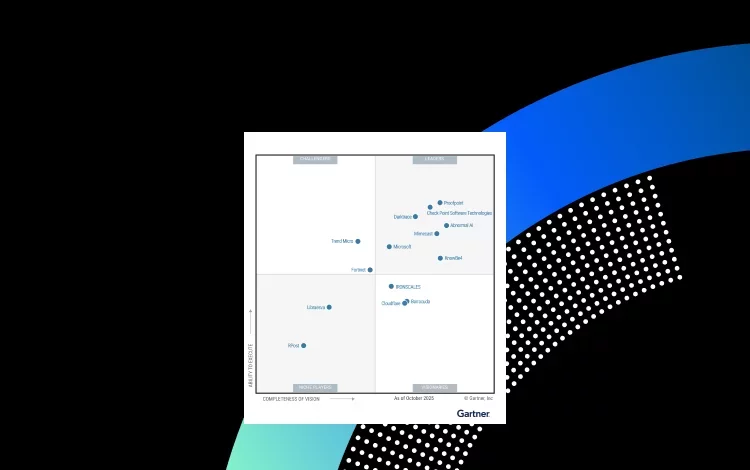
THE PROOF
We’re recognized as an industry leader by our peers and customers alike
-
Collaboration Security
-
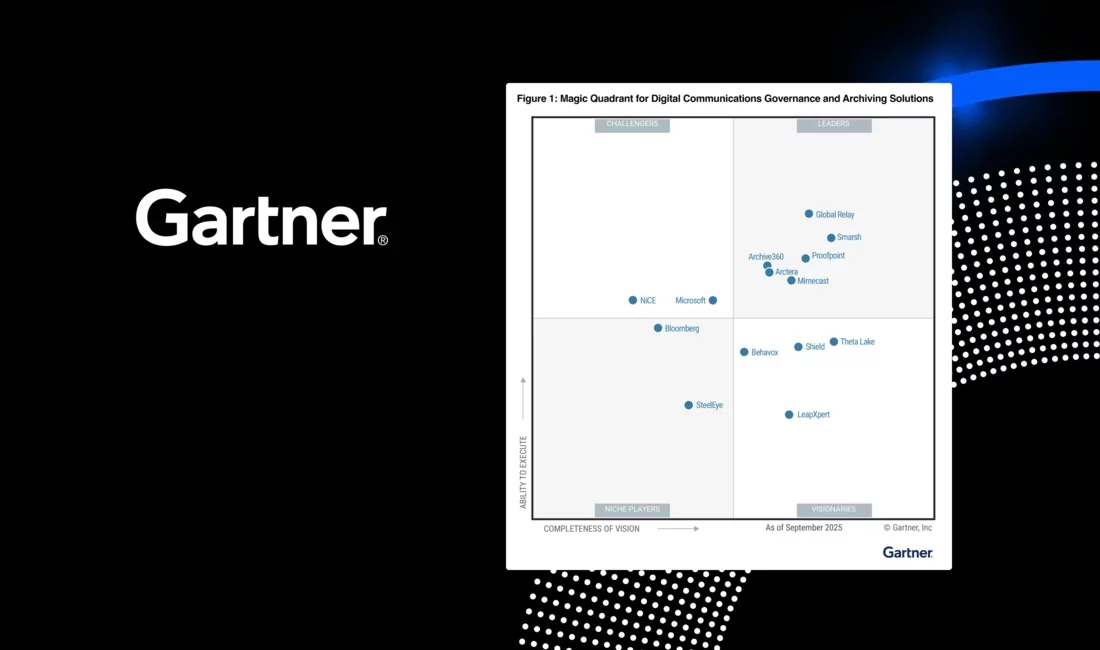
Data Security and Governance
-
Digital Communications Governance



Proofpoint helps Accenture secure people, data and operations.

Wyndham blocks 99.99% of threats, significantly reducing BEC risks while employees reporting increased phishing awareness with Proofpoint ZenGuideTM.