We are Proofpoint
We secure how people, data and AI agents connect across email, cloud and collaboration tools
Stopping
BEC attacks per year
Protecting
customers
Of the F100
use Proofpoint to stop attacks and defend their data
Numbers only ever tell part of the story.
See customer stories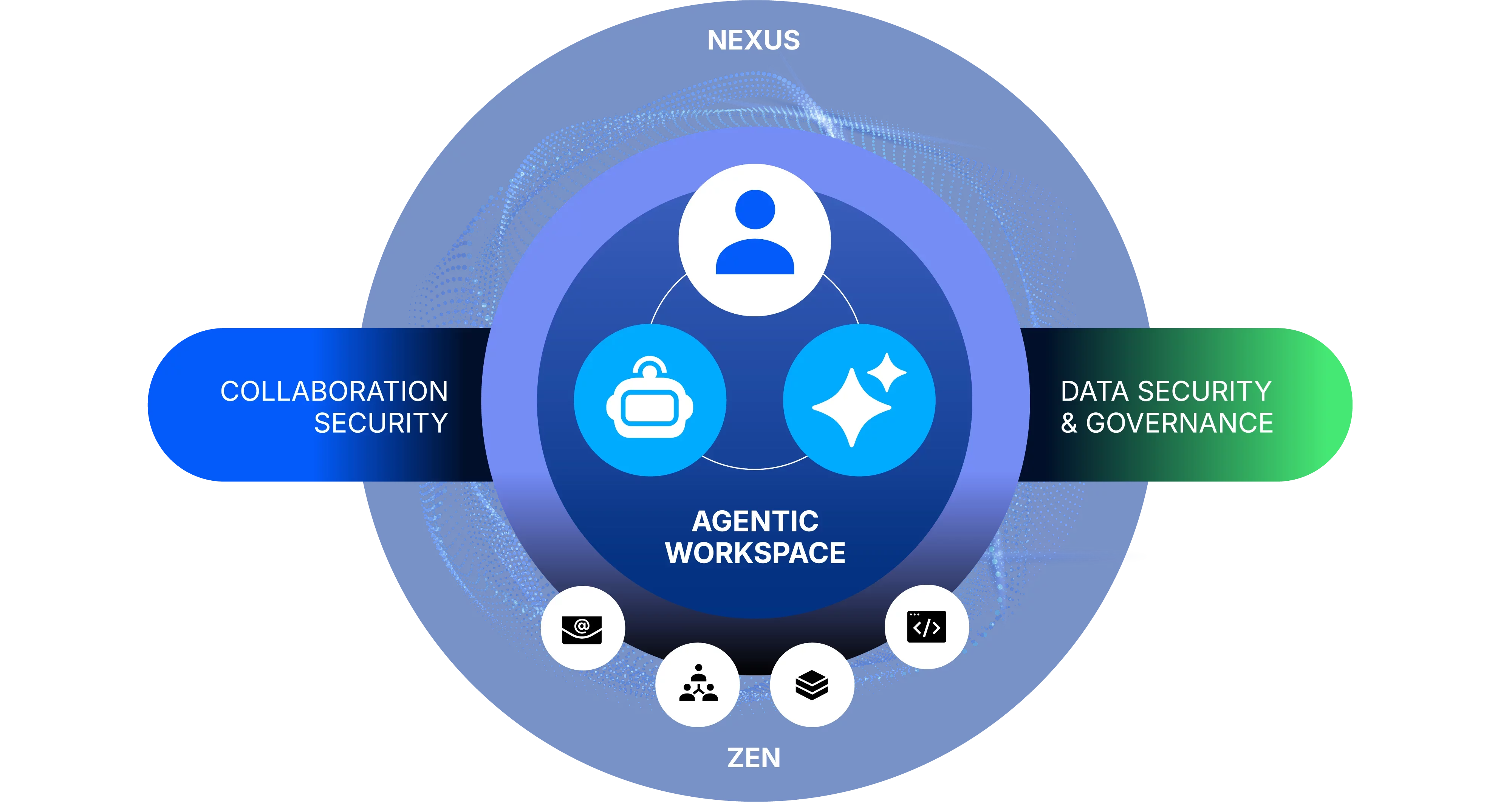
Why Proofpoint
Two million customers including 83 of the Fortune 100 rely on Proofpoint security solutions
AI is transforming the digital workspace and giving rise to the agentic workspace, where every collaboration—whether by a person or an AI agent—introduces new risks.
We give organizations the security solutions they need to protect their people and secure their data while embracing the AI revolution.

Collaboration Security
Stop all human-centric and AI-centric threats
Protect humans and agents from threats targeting them across all points of collaboration—email, messaging tools, social media platforms, cloud apps, and file-sharing services with world leading AI-based detection.

Data Security and Governance
Safeguard information and digital communications
Careless users mishandle it. Malicious users walk out with it. Compromised user accounts are hijacked to steal it. And with the rise of the agentic workspace, non-compliant users, agents or AI tools abuse it. Proofpoint’s unified approach shows you where your data is, who or what has access to it—and helps you protect it.
THE PROOF
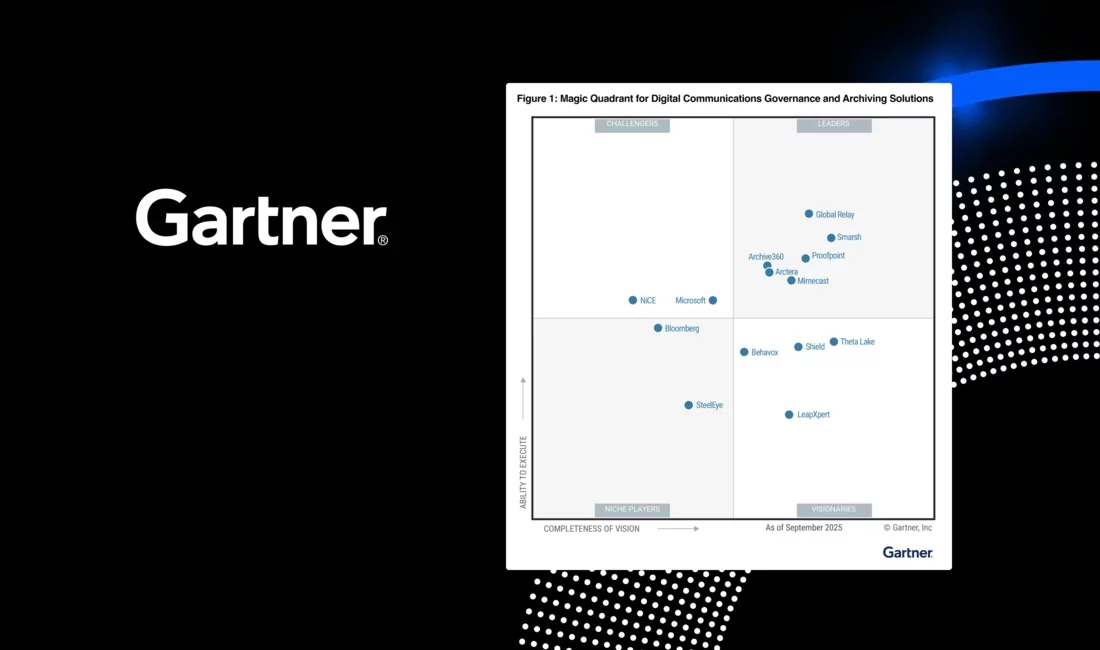
We’re recognized as an industry leader by our peers and customers alike
-
Collaboration Security
-
Data Security and Governance
-
Digital Communications Governance



Proofpoint helps Accenture secure people, data and operations.

Wyndham blocks 99.99% of threats, significantly reducing BEC risks while employees reporting increased phishing awareness with Proofpoint ZenGuideTM.