Multi-layered email security
Email security trusted by 87 of the Fortune 100 to block human-targeted attacks, stop account takeover and safeguard privileged identities.
People activate today’s integrated attacks.
Email remains the #1 threat vector to target organizations. What makes cyber-attacks like business email compromise (BEC), credential phishing, ransomware and account takeover so successful is how effectively they target your users using a personalized, multi-layered approach. Traditional email security solutions focused on siloed controls aren’t enough. To stop these modern attacks, you need integrated defense.
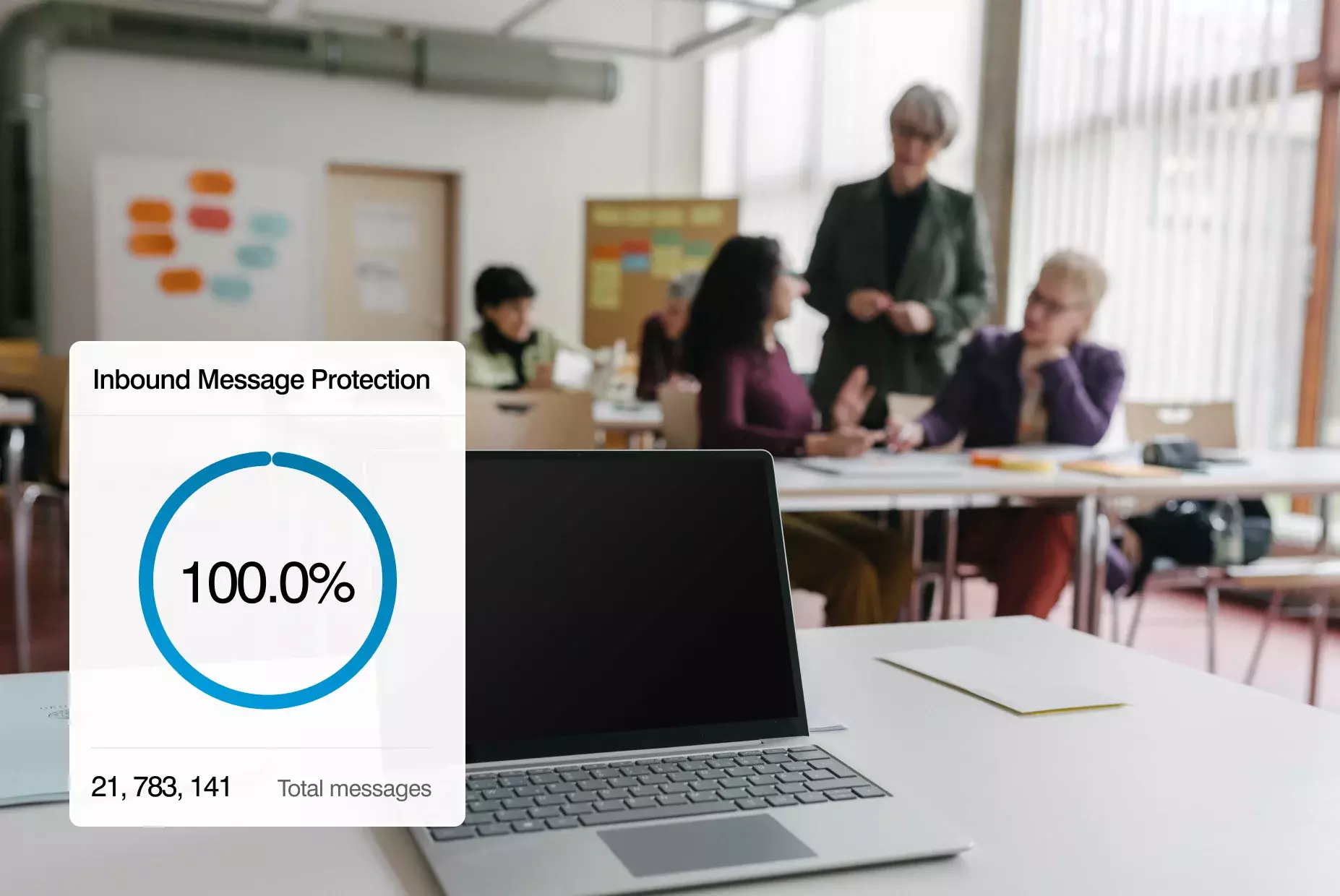
We protect against every type of threat, every time, every way a user may encounter it.
Our multi-layered, adaptive email security service stops 99.99% of all email threats, including business email compromise, ransomware, credential phishing and other forms of social engineering.
Our detection ensemble, with threat intelligence, static analysis, sandboxing, click-time protection, and Nexus AI models, is the industry’s most effective. In addition, we've now introduced the first-ever pre-delivery protections against social engineering and malicious URLs, plus new post-delivery behavioral AI capabilities: Proofpoint Adaptive Email Security.

Experience the benefits of our core email security offering
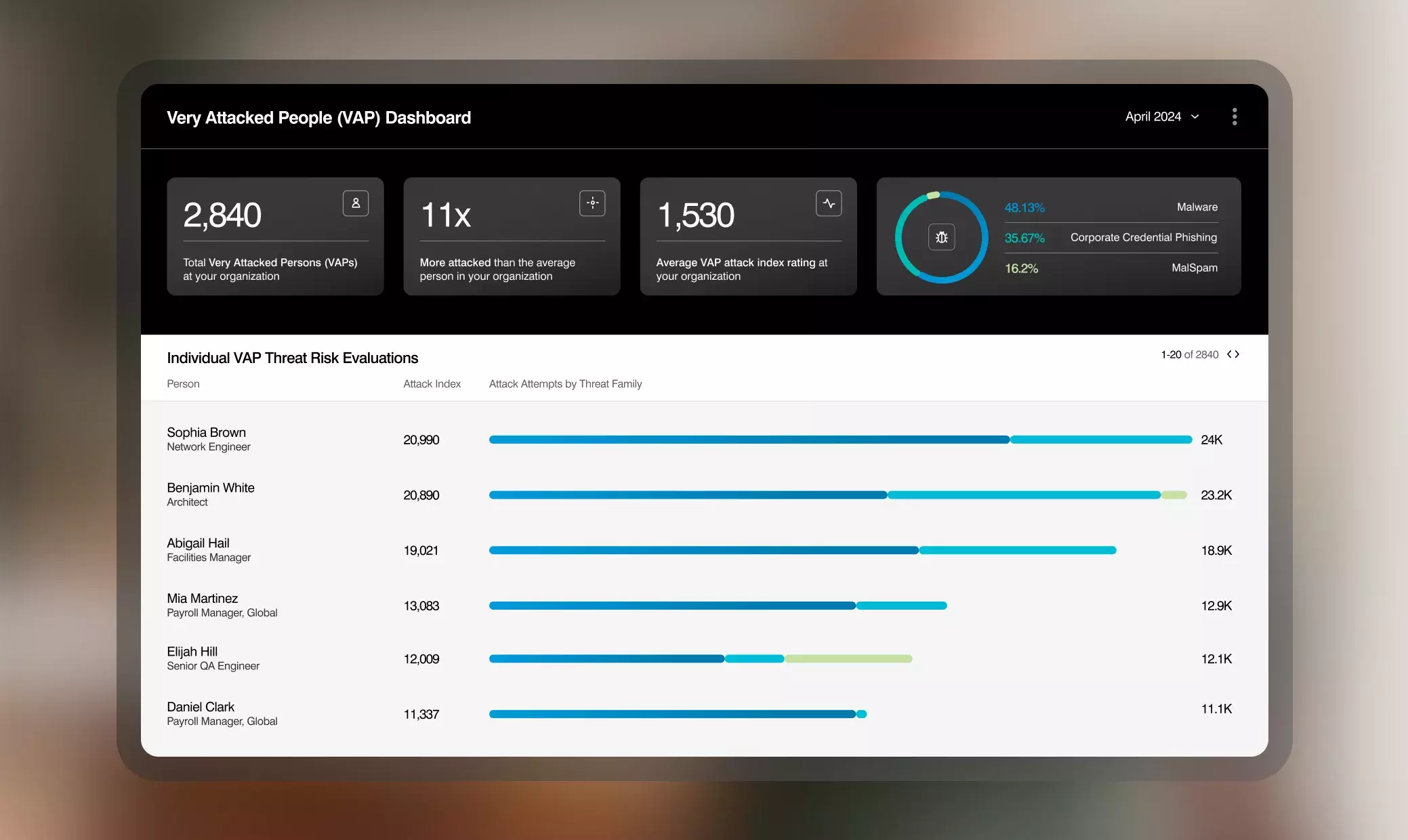
Get total visibility
We offer total visibility into who your Very Attacked People (VAPs) are, what threats are targeting them, and how. And we offer a risk score for each person at your organization based on their unique vulnerability, attack and IT privileges.

Superior defense starts with world-class data
Our AI/ML models are trained with the richest data set in the world, providing superior accuracy. We analyze three trillion messages per year across 230,000+ organizations globally. The value of our proprietary data is enhanced by contextual insights and in-depth classification from our leading team of threat researchers and data scientists.
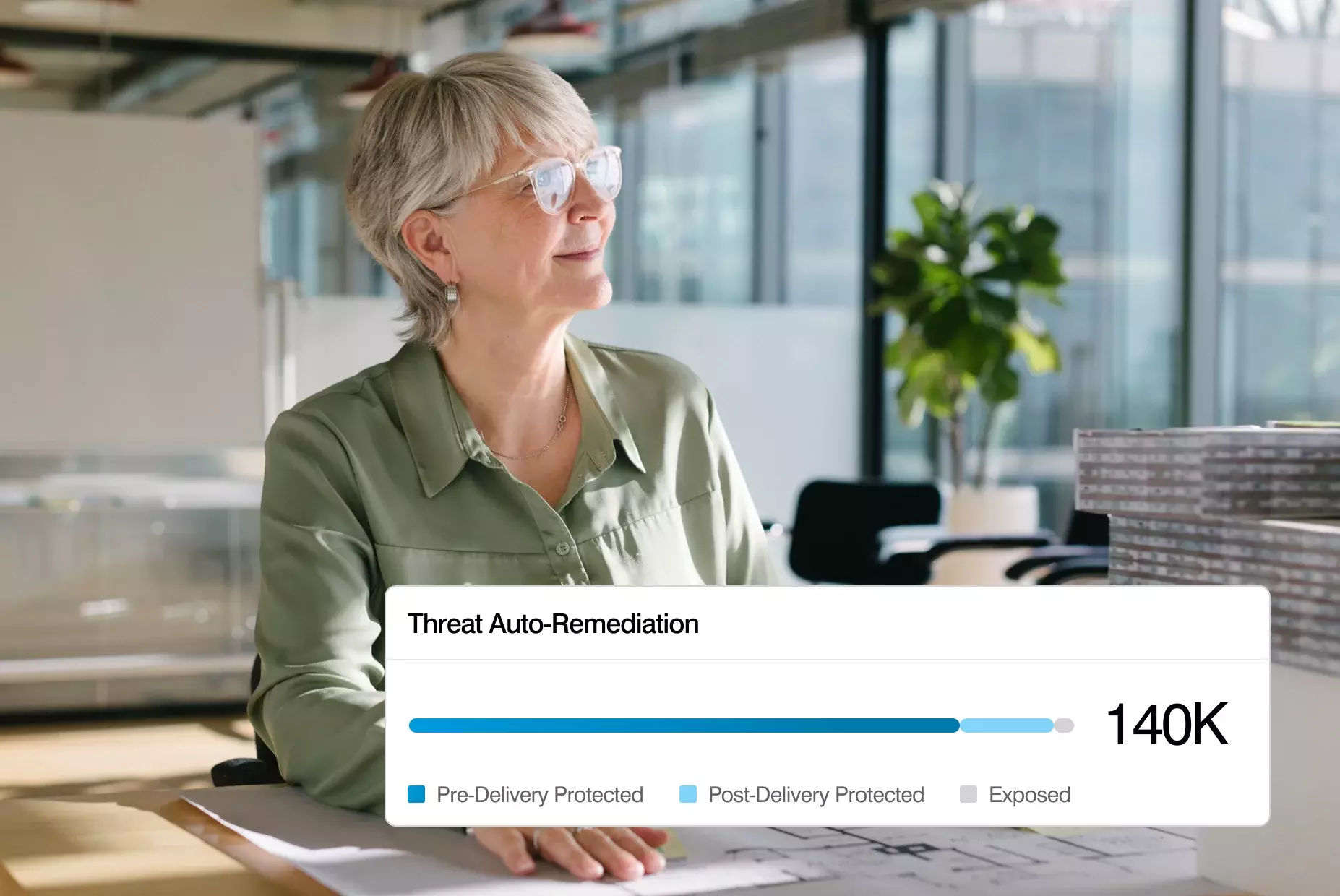
Work smarter
Proofpoint email security solutions boost the efficiency and effectiveness of your team. We stop threats before they reach your organization, reducing your workload. We also automate the remediation of malicious and unwanted emails post-delivery, limiting exposure time and accelerating incident response.
Defend better before and after delivery
Pre-delivery, we detect and stop email threats with and without payloads—including BEC, TOAD attacks, and credential phishing—before they reach your inbox.
Post-delivery, our comprehensive protection rewrites suspicious URLs, applies contextual warning tags to emails, and conducts in-depth analysis of messages via behavioral AI and content examination. And it remediates threats, ensuring total protection.
Prevent account takeover, safeguard identities
Our identity defenses detect account takeover and stop lateral movement. We find and fix your risky identities and available attack paths before your adversaries do.
Key features that stop human-targeted attacks
Nexus People Risk Explorer identifies your riskiest users
We provide insights into who your "Very Attacked People" (VAP) are and what specific threats are targeting them, so you can implement customized controls including browser isolation, focused security awareness training, identity vulnerability remediation, and step-up authentication to reduce risk.
Early warning telemetry into risks targeting your people
Our team of threat researchers investigates email security threats, identifies new campaigns and tracks threat actor activity. We provide detailed reports of attack trends and insights into specific threat actors targeting your organization.

Enhanced end user experience
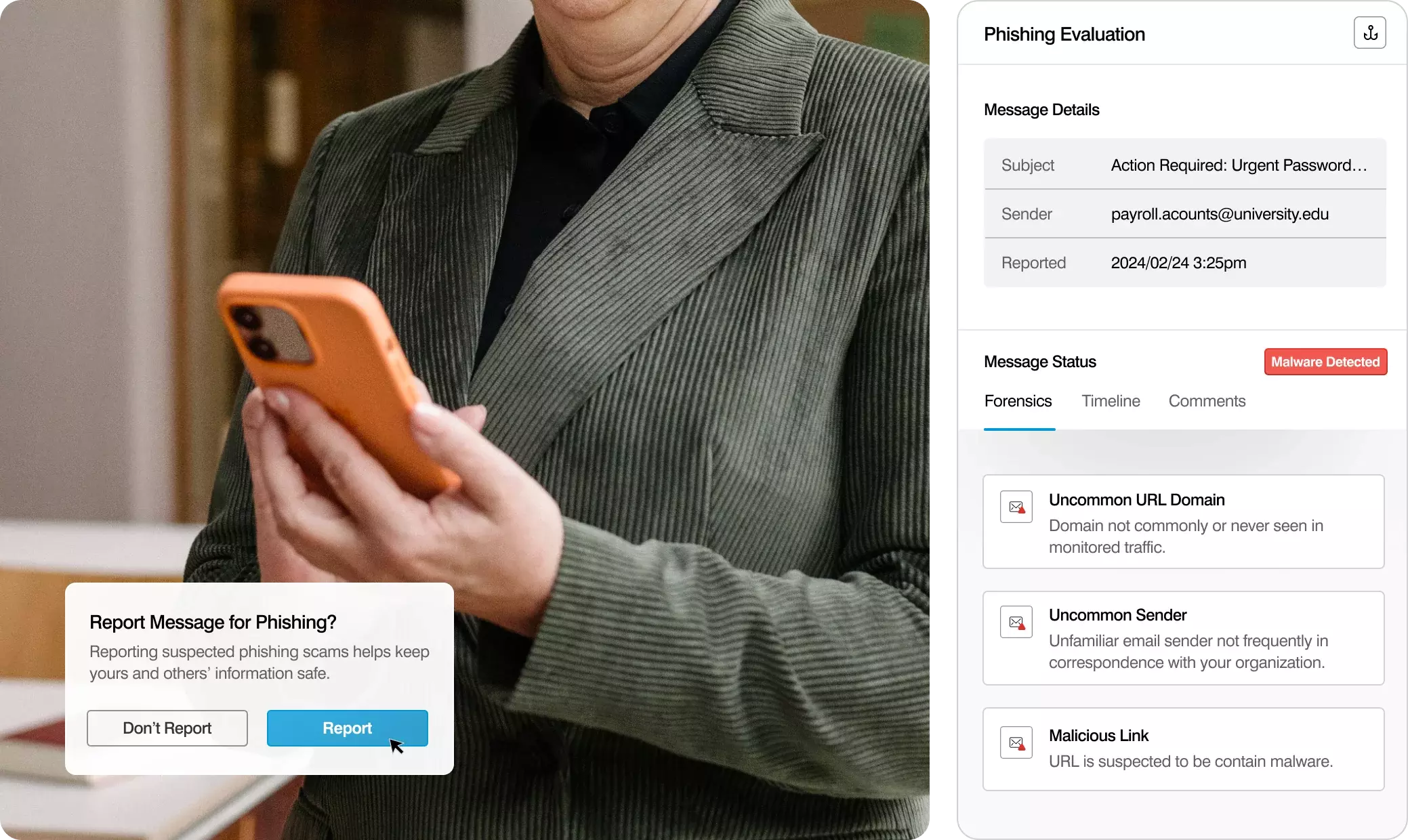
Seamless classification of user-reported messages
We make it easy for users to report suspicious messages across all devices and automatically classify reported emails. If we discover that a user-reported message is malicious, we’ll automatically remove all instances of it from all user inboxes—including forwards and distribution lists. And we communicate that activity back to the submitting user, helping them understand the positive impact of their actions.
Email warning tags to help your users
We empower your users to make informed decisions in the moment with email warning tags that flag potentially malicious messages. And our warning banners include an integrated “report suspicious” button, making it easy to report suspicious messages even on a mobile device.
Pre-delivery sandboxing and behavioral analysis
We analyze messages, links and attachments before they reach the inbox. And we provide inline, pre-delivery sandboxing and behavioral analysis of suspicious QR codes, reducing the burden on your security teams. Our sandbox technology provides exhaustive analysis via static, dynamic and analyst-assisted execution, to maximize detection and intelligence extraction. We use ML-driven intelligence to determine whether a URL should be sent to the sandbox for further analysis.
Continuous analysis of the inbox with Adaptive Email Security
We analyze messages in employee inboxes using over 200 behavioral AI signals, providing email security defense-in-depth. Augment pre-delivery protection with an API integration to M365 or Google Workspace. And we stop internal phishing by detecting anomalous sending behaviors such as spikes in email volume and unusual recipients.
Personalized security protection
In combination with our email security solution, our personalized threat-driven security education enables you to deliver targeted learning and simulations for better outcomes, reinforcing behavior with contextual nudges via email tags and custom feedback on user-reported messages.

Automated protection
Click-time protection
We re-write URLs to protect users on any network and device to detect if a message has been weaponized post-delivery. When users click on re-written URLs, automated browser isolation and real-time sandboxing protect against malware and credential theft.
Automated Quarantine Post-Delivery
If a malicious message is detected post-delivery, we automatically move it to quarantine. And we follow forwarded mail and distribution lists.
Powerful integrations
API-based SIEM/SOAR integration
We enable you to automatically enrich and correlate existing security event data with email threat data, so your security team can leverage context-aware threat intelligence and to proactively alert on and quickly respond to suspicious email-based threats.
API-based endpoint integration
We automatically feed threat intelligence information to your endpoint protection solution. With insight into endpoint behavior, file activity information, and detailed threat forensic evidence, your security team can quickly identify and enable endpoint isolation to remediate compromised devices. And we provide API-enabled, bi-directional workflows and integrations with third-party security vendors like Palo Alto, Crowdstrike, Microsoft Defender, Okta and more.
We’re recognized as an industry leader by leading analyst firms and customers alike.

Proofpoint Recognized as Overall Market Leader Frost Radar™: Email Security, 2024

Proofpoint Tops KuppingerCole Leadership Compass for Email Security

Proofpoint Named a Leader in The Forrester Wave™: Enterprise Email Security, Q2 2023
“Proofpoint is the only vendor that delivers on all five areas for email security as an integrated platform.” — Gartner
Threat Detection: Included in our Core product package
Core
Threat Protection with Optional Security Awareness
The only package that includes Proofpoint’s award-winning Threat Protection technology with the ability to add on optional Security Awareness.
Learn more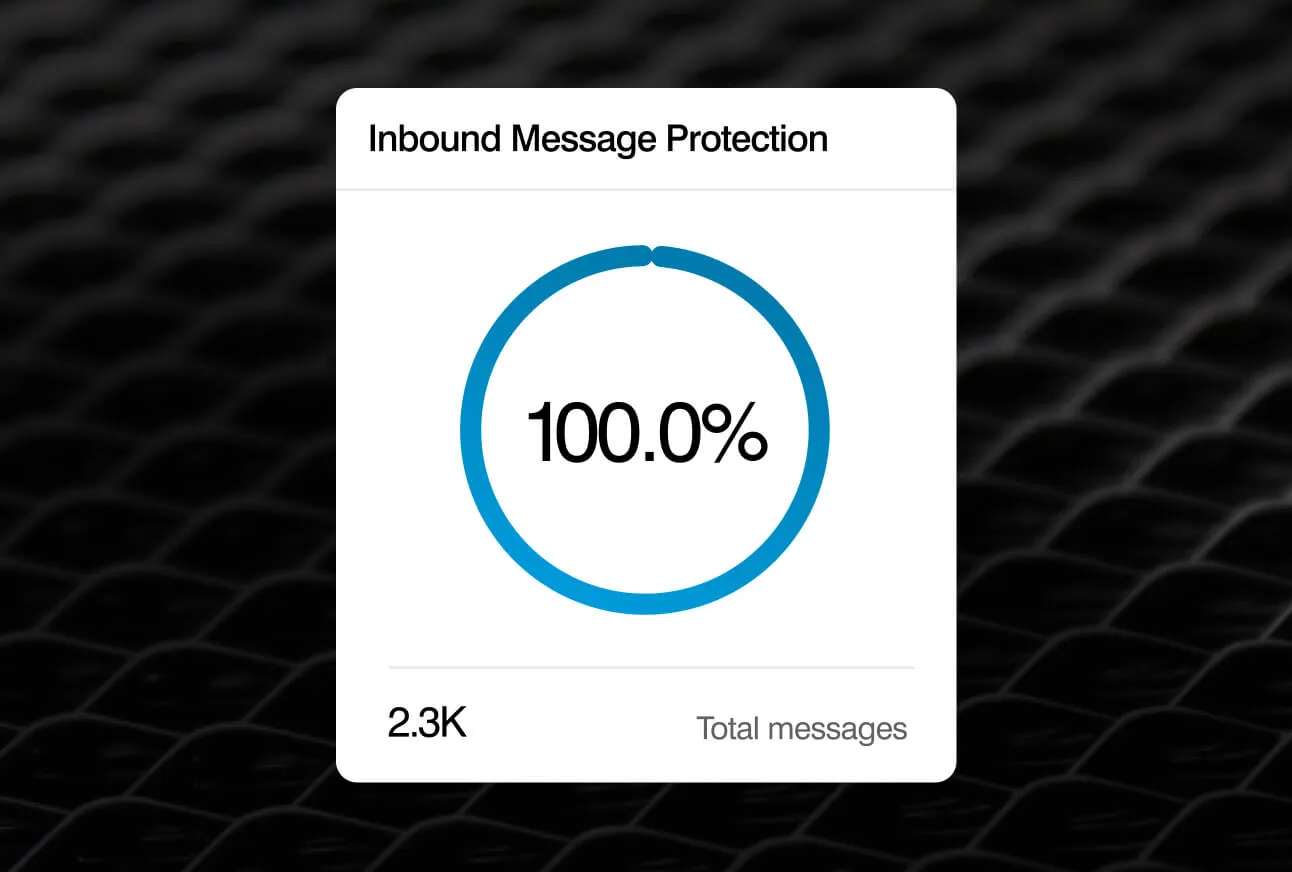
Packages Core
Core
Threat Protection With Optional Security Awareness
Includes:
Powerful Products
Learn more about the products powering our package solutions
Adaptive Email Security
Stop more threats, including internal phishing, with a fully integrated layer of behavioral AI.
Learn moreImpersonation Protection
Holistic brand and supplier defense that stops 100% of domain spoofing.
Learn moreIdentity Threat and Account Takeover Protection
Secure vulnerable identities, stop lateral movement and privilege escalation.
Learn moreMitigate Human Risk
Unlock full user risk visibility and drive behavior change with security awareness training.
Learn moreThe latest developments in Threat Protection
The Definitive Email Cybersecurity Strategy Guide - Protect Your People From Email Attacks and Threats
Read More
Proofpoint Named a Leader in The Forrester Wave™: Enterprise Email Security, Q2 2023
Threat Protection Solution Brief
Turn people into your best defense
Free Rapid Risk Assessment