Cybercriminals are increasingly targeting mobile users with free mobile apps in order to steal data – and nothing is sacred. Like a social media account with a large following, popular mobile apps give scammers a low-cost way to cast a very wide net. Free apps mimicking popular games, for example, are often ‘riskware’ that can steal user information, track browsing, access contacts and calendar, and make unauthorized calls: a steep price to pay for a ‘free’ app.
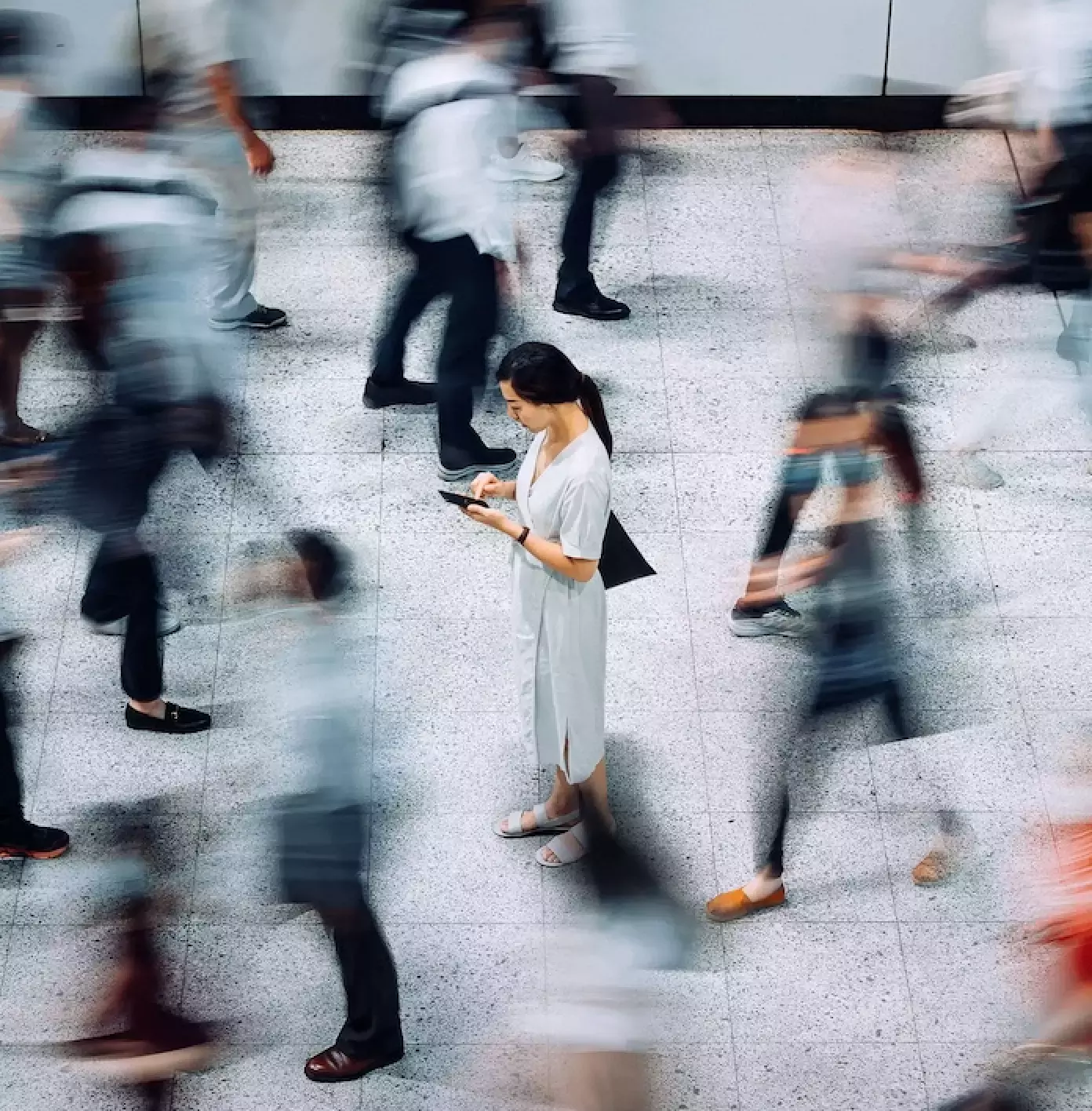
Yet cybercriminals are being inadvertently assisted in their efforts by a human failure. From end users to security managers, people often make mobile app security decisions based on assumptions around the type of app, rather than a real, data-driven assessment of its behavior and risk to personal data and to organizations. Judging apps based on preconceived notions can lead to serious security issues: Proofpoint research has found that differentiating risky apps from harmless ones based solely on their initial appearance can lead to the wrong security conclusions.
For example, free gambling apps offer a prime example of the threat posed by risky apps. In a Proofpoint sample of 23,000 card game apps (15,013 for Android; 7,991 for iOS; includes poker, blackjack, bingo, solitaire, and miscellaneous card games) with 5.6 billion total downloads, 52 apps were found to contain known malicious code and another 379 can be classified as ”dangerous” or high risk, and over 3,200 behaved in a manner that Proofpoint deems a ”moderate risk.”[i] In total, nearly fourteen percent of gambling apps demonstrate some form risky behavior. Even assuming that a gaming app might need to communicate with a server for some functions, a number of the analyzed gambling apps displayed an alarming amount of communication with external servers, as a category sending data to over 1,800 servers across 41 countries.

While some may not be surprised to learn that mobile users who download free poker apps are gambling with their personal data, Proofpoint researchers found that more innocuous apps can also behave this way. Shining a light on flashlight apps, we found that of over 5,600 apps analyzed (all for Android), 26 contain known malicious code and another 36 can be classified as high risk. Users can be forgiven for not expecting a flashlight app to need to communicate externally, yet the flashlight apps as a whole communicated with 678 servers across 28 countries.
If we needed further evidence that any legitimate-looking app has the potential to be mimicked, scammers have even created malicious and riskware versions of holy books. Proofpoint researchers analyzed holy book apps available on iOS and Android app stores and quantified the extent of the risk to users… and their personal and company data.
A Proofpoint sample of apps available on major app stores found that the Bible is the most popular of the holy book apps: a single Bible app has over 50 million downloads, three registered over five million downloads, and seventeen Bible apps have been each downloaded over one million times.
Looking more closely at the apps themselves, Proofpoint analyzed over 5,600 unique Bible apps (4,154 for Android; 1,500 for iOS), including 208 that contain known malicious code and 140 classified as high risk based on their behavior, all for the Android platform. Many Bible apps do not have privacy policies, which is fitting since many apps send data about the user to a variety of countries, with some apps communicating to over fifty servers. Some have added a wide variety of advertising and social networking capabilities, dramatically increasing the risk exposure of users. All told, Bible apps communicate data to over 2,500 servers across forty-two countries.

These behaviors are not limited to the less-downloaded apps: Proofpoint analysis found that one of the most popular Bible apps sends data to sixteen servers in three different countries; reads the user’s SMS messages, address book, and device and phone information; tries to exploit cross-app interaction if the device is rooted; and can even make phone calls on your behalf.
Nor was the Bible alone in this regard: analysis revealed similar prevalence for malicious and high-risk Quran apps. At almost 4,500 unique Quran apps (3,804 for Android; 646 for iOS), the holy book of the world’s second most populous religion rivaled the Bible in terms of the number of apps. Two have over 10 million downloads, seven over 5 million downloads, and 13 Quran apps that have each been downloaded at least one million times. Sixteen of the scanned Quran apps contain known malicious code and another thirty-eight were classified as high risk (again, all for the Android platform), and a number of them communicate with as many as thirty-five servers. One of the ten most-downloaded apps is clearly riskware: installing itself as a boot-time app it communicates to thirty-one different servers; reads the user’s SMS messages; can send SMS messages from the user; and can look up the user’s GPS location. As a whole, the scanned Quran apps communicate data to 1,440 servers across thirty-six countries.
By contrast, the Torah offers users a relatively low-risk reading experience, albeit with a smaller range of choices. Less than two hundred unique Torah apps were discovered and the most-downloaded had a half-million downloads, with only two of the scanned apps containing known malicious code. That said, Torah apps were not entirely without risk, as some were found to communicate with as many as fifty different servers, and Torah apps as a group still communicated data to 332 servers in sixteen different countries.
Defending against riskware
The existence – and surprising prevalence – of riskware in apps from gambling programs to the holy books is a valuable reminder of the importance of a mobile app security strategy for your organization. Clearly, one cannot ”judge a book by its cover” – that is, assess security risk by preconceived notions of legitimacy based on what an app claims it is or does. In order to protect employees and users from unscrupulous scammers and cybercriminals targeting their employees, organizations should:
- Use data-driven tools that ascertain exactly what types of data apps are accessing and transmitting, and to where.
- Inform employees and users about what data their apps are harvesting and where that data is being sent, so that they can make informed decisions; this includes religious and other seemingly innocent apps.
- Remove malware-infected apps from employee devices, including religious, gaming, utility and other apps that are infected.
- Review the privacy policy of all apps that harvest user or company data, especially address book and calendar information, and ensure that these meet with compliance guidelines. Consider restricting apps that harvest company data that do not have privacy policies, or whose privacy policies do not promise protection of this information.
[i]Proofpoint researchers analyzed several categories of free apps available on the Android and iOS apps stores and found malicious and ‘high risk’ apps in all. In Proofpoint’s definition, “malicious” apps have malware in them: that is, these apps attempt to exploit the OS in order to access things for which they don’t have permission. “High risk” apps – again, in Proofpoint’s definition – have known security vulnerabilities (SSL, cert), communicate personal info (contacts, calendar), or leak location and activity information.
Subscribe to the Proofpoint Blog