

人に依存するサイバーセキュリティ・リスクを特定、評価、低減
従業員向けのサイバーセキュリティ意識向上トレーニングで、人的リスクを意識したセキュリティを構築し、ユーザーをレジリエンスを高めます。
ユーザーのリスクを理解しなければ、セキュリティ管理も意識向上プログラムも意味がない
サイバーセキュリティの問題の多くは、ヒューマンエラーに起因します。多くの組織では、この問題を低減するためにセキュリティ管理策や何らかのセキュリティ意識教育が実施されていますが、人的リスクがどこにあるのかを可視化できていません。最も脆弱なユーザを知らなければ、組織はそのユーザを適切に保護することも、攻撃を認識し防御するための準備を整えることもできません。
ユーザーのリスクを完全に可視化し、行動変容を促進
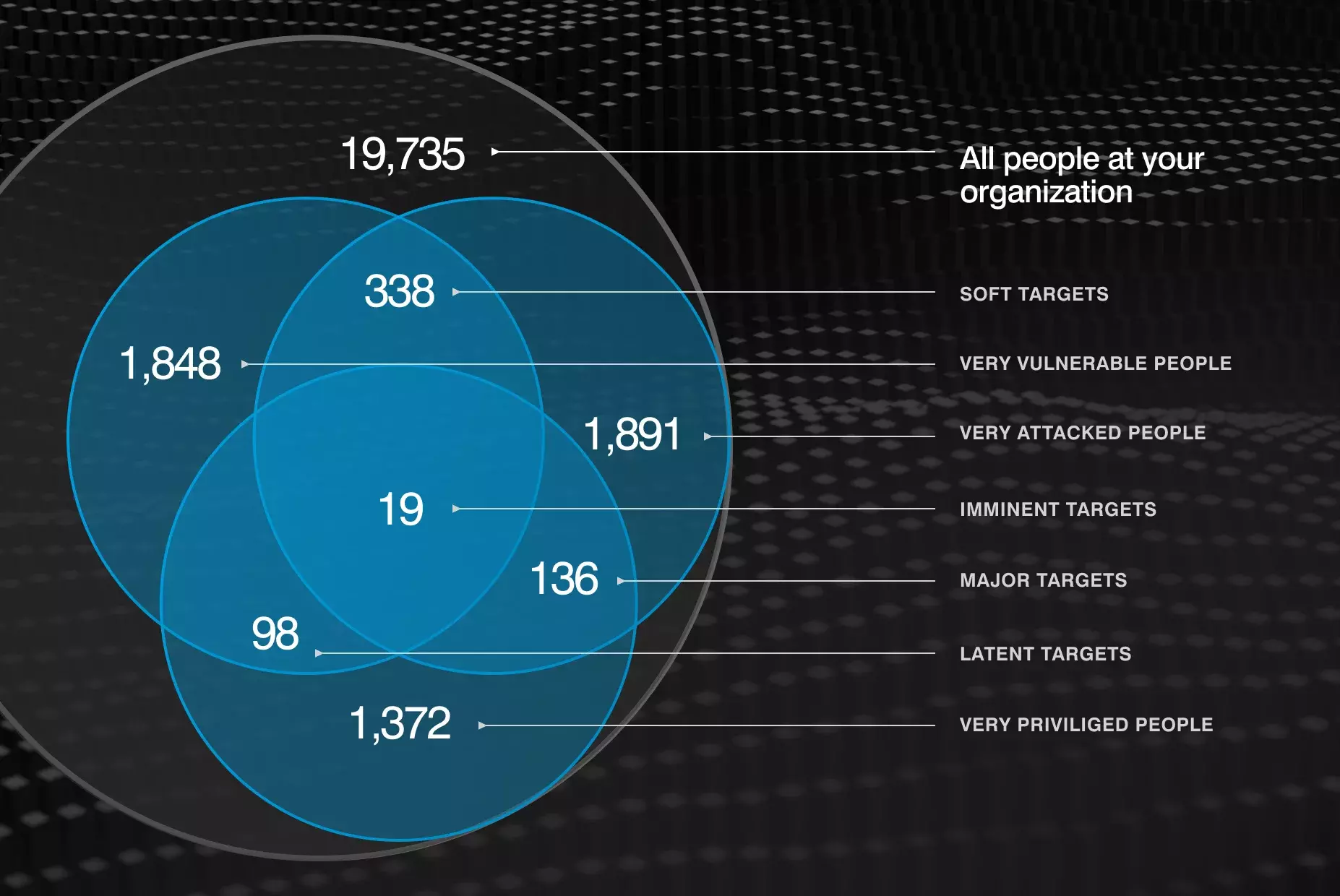
プルーフポイントのヒューマン・セントリック・インテリジェンスは、組織内の脆弱な個人、特権を持つ個人、標的となる個人に関する貴重な洞察を提供し、侵害される可能性が最も高い個人をピンポイントで特定します。
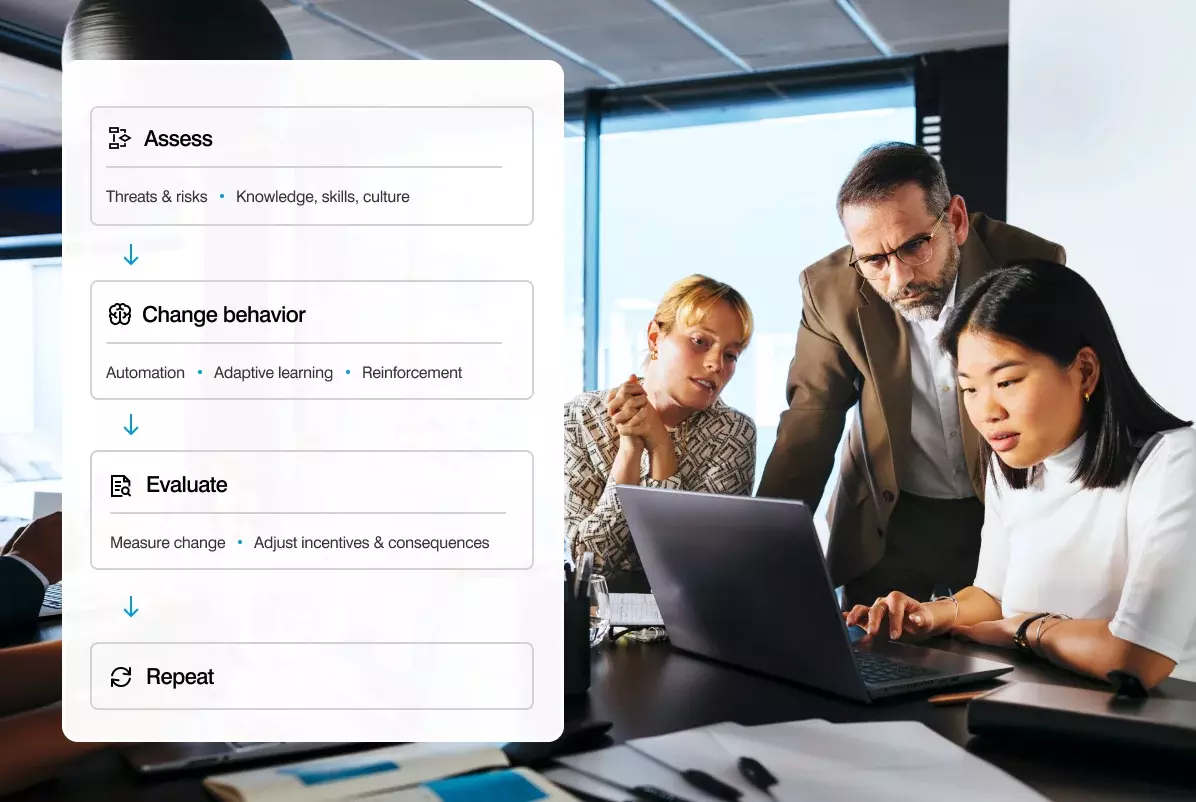
Proofpoint SAT は、ユーザー中心の脅威主導型プログラムで従業員の行動変容を促し、持続可能なセキュリティ習慣を構築します。

プルーフポイントのアプローチは、行動科学で実証された知見、カスタマイズされたマイクロラーニング、従業員が実際に直面する脅威を取り入れたプログラムを統合し、行動変容を促し、時間の経過とともに測定可能なほど改善される持続可能なセキュリティ文化を構築します。
Identify Risk
Identify vulnerable, attacked, and privileged (VAPs) individuals within the organization and who are most likely to be compromised.
Adaptive Protection
Protect your most risky and privileged used with specific security controls.
Change Unsafe Behavior
Create sustainable security habits by using personalized content for each user’s needs.
Evaluate and Scale
Measure performance and make group wide decisions with multitenant administration.
Report Back
We measure behavioral metrics that matter to your executive leadership.
従業員を砦の一つに
Focus on true risk within your organization
Proofpoint identifies vulnerable users using multiple methods— we identify what users know with adaptive learning assessments; what users do when faced with threats with phishing simulations that mimic real-world attacks; and what users believe with short and concise assessments.

Powerful integrations
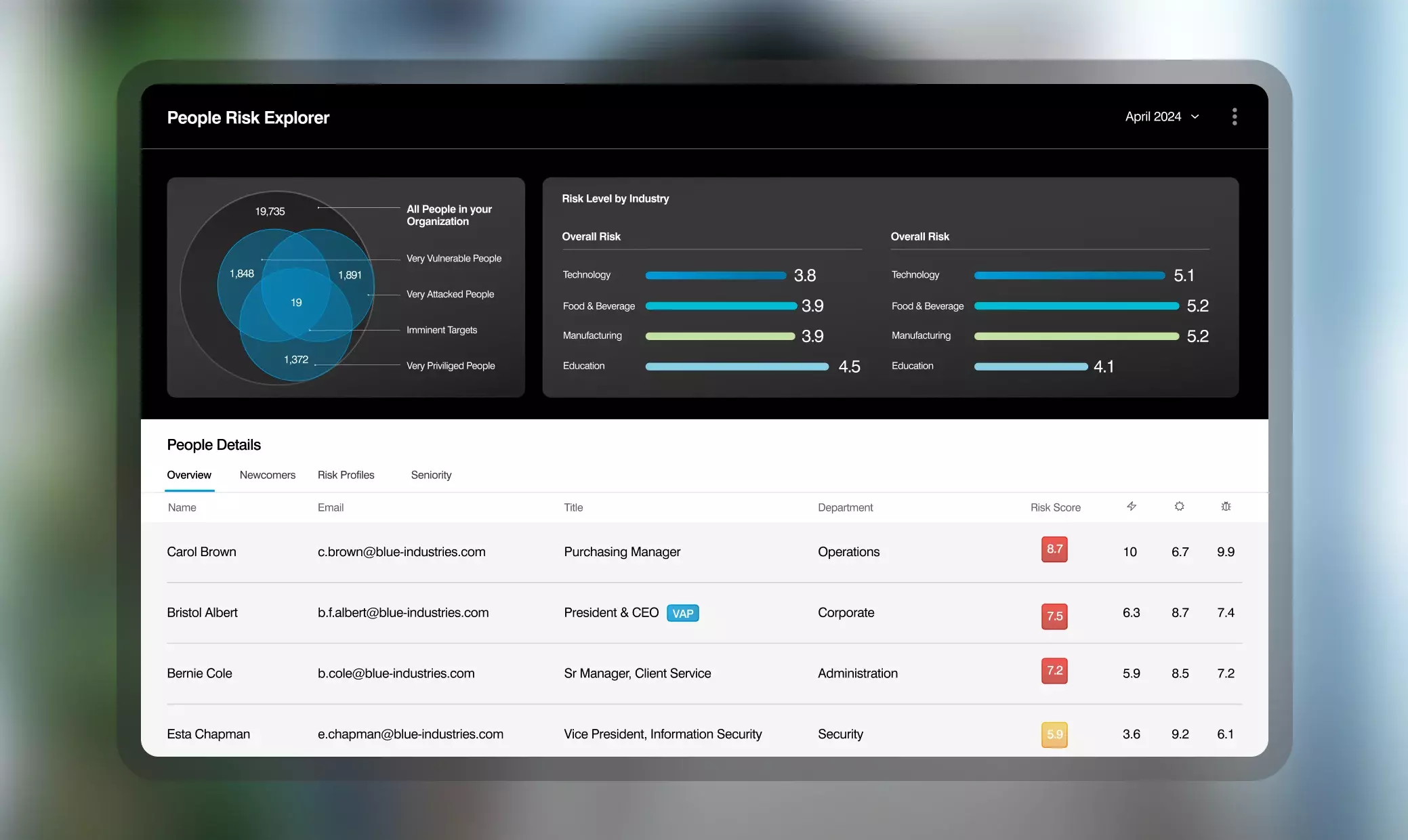
Integrated with Proofpoint Threat Protection, we unveil Very Attacked People and top clickers. Nexus People Risk Explorer (NPRE) quantifies people risk by considering user vulnerability, attack index, and business privilege, revealing the riskiest users.
Drive true change and sustainable habits
Proofpoint provides users with a personalized learning experience that aligns with their role, vulnerabilities, competencies, and language. We keep users resilient against today’s threat landscape by educating them on trending threats with our threat-driven content. Proofpoint creates a security awareness culture that results in many customers seeing a 40% decrease in clicks on real world threats and a 90% reduction in malware infections.

Better Communicate people risk and program impact
Proofpoint Nexus People Risk Explorer gives security executives a comprehensive but simple report summarizing the risk people pose to the rest of the organization. Proofpoint Security Awareness provides behavioral metrics that matter to your executive leadership.
Accelerate threat investigation and response
Proofpoint Security Awareness makes it easy for end users to report suspicious messages. When integrated with Threat Response Auto-Pull, Proofpoint can automate the analysis and remediation of end-user reported emails, thus reducing manual work for the incident
response team.
Key features of our Security Awareness Training
Assess user risk through a whole new lens
Proofpoint helps you identify your most vulnerable users, including top clickers and users that are being targeted with a significant volume of attacks. With this, you get a data-driven security awareness program that goes beyond phishing simulation.
We provide you with:
- Phishing/USB simulations based on real-world threats
- Knowledge assessments
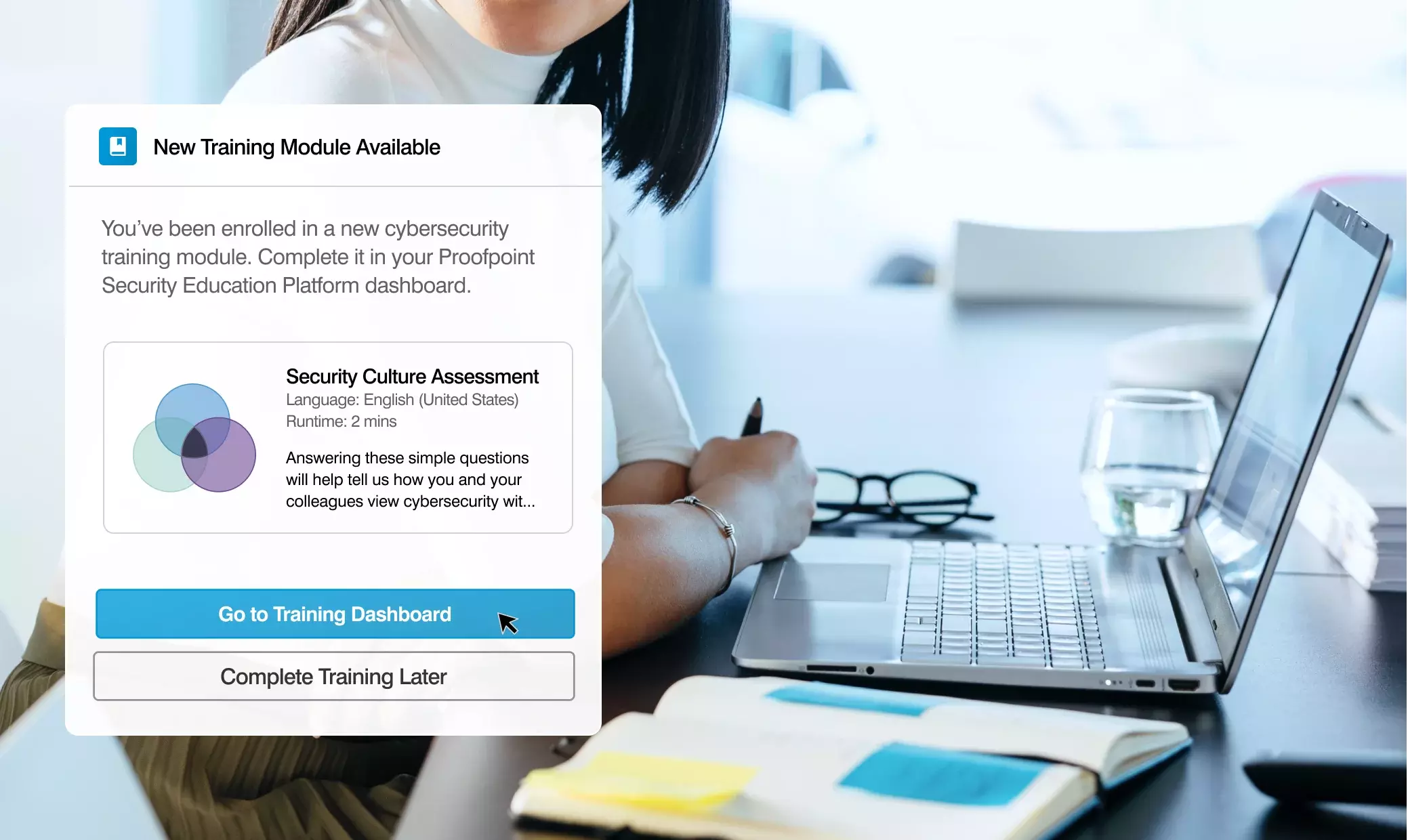
- Security culture assessments
- Reports that identify your Very Attacked People (VAPs) and top clickers
A personalized learning experience
The Proofpoint content library provides you with a wide range of educational topics, formats, and support materials. With our rich threat intelligence, our solution helps users understand real-world security risks, privacy threats and compliance rules. You can now create a truly global training program that users across different functions, regions and languages will understand.
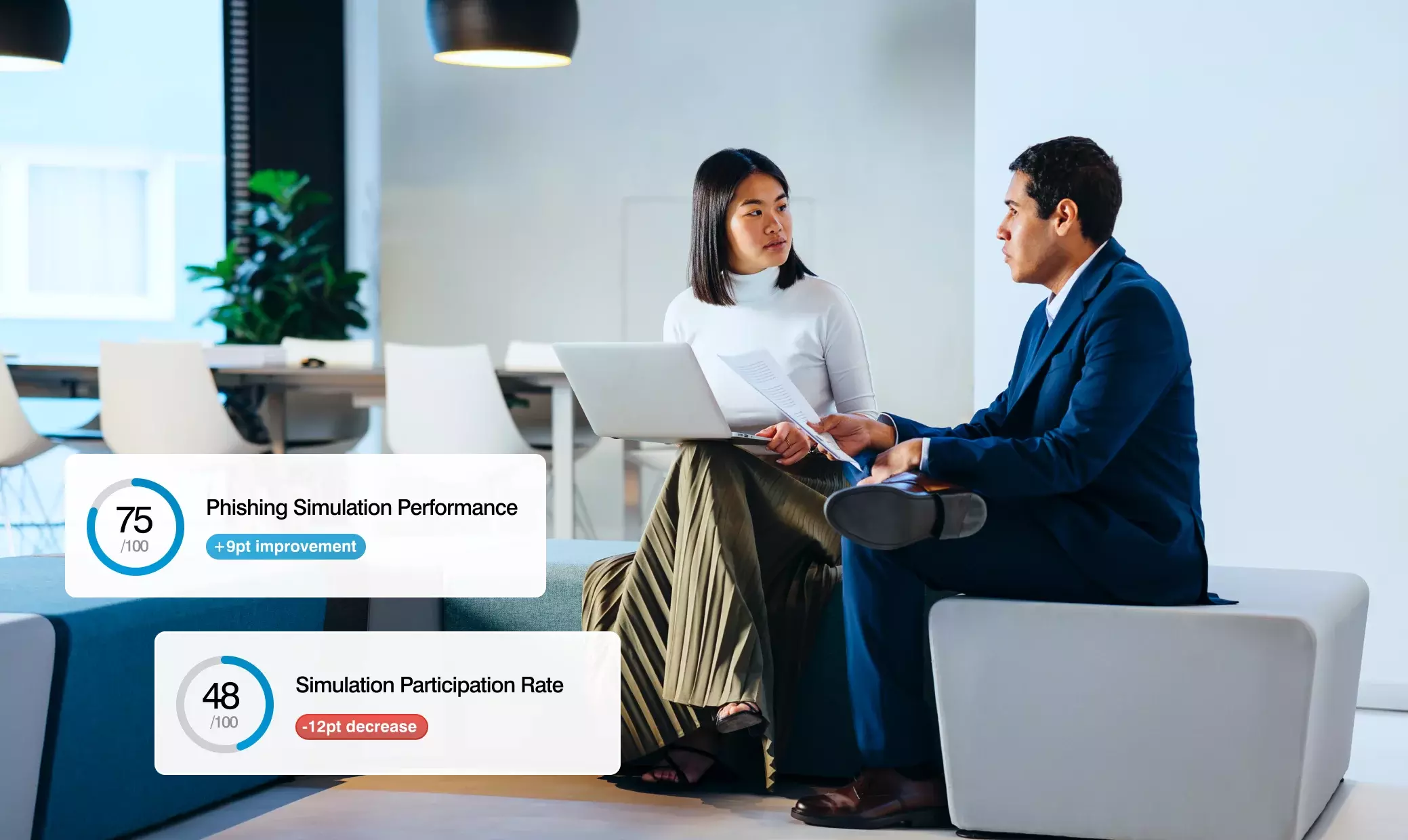
Measure program success and user vulnerability
Proofpoint allows you to effectively measure your program’s progress over time with metrics. With Proofpoint Security Awareness Training, you can:
- Can track behavior for both simulations and real emails (even in real time)
- View a single dashboard that captures behavior change and reveals user vulnerability.
- Get benchmarks against industry peers.
Real time coaching
Reinforce positive user behavior with just-in-time training like Teachable Moment and Phish Hooks.
CISO Dashboard
Our CISO dashboard provides C-level visibility, making it easier to gather and communicate program performance and impact to the board.
Phish Alarm
Proofpoint accelerates threat response by automatically analyzing user-reported messages. We make it easier for end users to report suspicious messages, even when they’re accessing email via mobile devices.
Easily expand and scale your program
Proofpoint Security Awareness Enterprise gives you the power of automation and scalability. With our multitenant administration capabilities, you can group-wide decisions, while also branding your security awareness content in 40+ different languages.
Related mitigating human risk products from Proofpoint
Stop Human-Targeted Attacks
Stop the full range of attacks targeting your people, including threats, impersonation attempts and supplier fraud.
Learn MoreImpersonation Protection
Holistic brand and supplier defense that stops 100% of domain spoofing.
Learn MoreAdaptive Email Security
Stop more threats, including internal phishing, with a fully integrated layer of behavioral AI.
Learn MoreIdentity Protection
Secure vulnerable identities, stop lateral movement and privilege escalation.
Learn MoreThe latest developments in mitigating human risk

State of the Phish
詳細Proofpoint SAT (Security Awareness Training) | 従業員向けセキュリティ意識向上トレーニング エンタープライズ版
Phish in a Barrel: Real-World Cyber Attack Examples | サイバー攻撃最大の侵入経路フィッシング:従業員トレーニングで防ぐことができるサイバー脅威の実態と損害
Turn people into your best defense
Get Started
Product Packages
Comprehensive protection against today's risks — tailored to your organization's needs.
Learn MoreGet Up to Speed
Explore the latest in cybersecurity news, insights, and innovations.
Resource LibraryTake an Assessment
Get a security audit and custom report of your corporate environment
GET AN ASSESSMENT