Security provider warns of Trojan that steals banking credentials and other personal data.
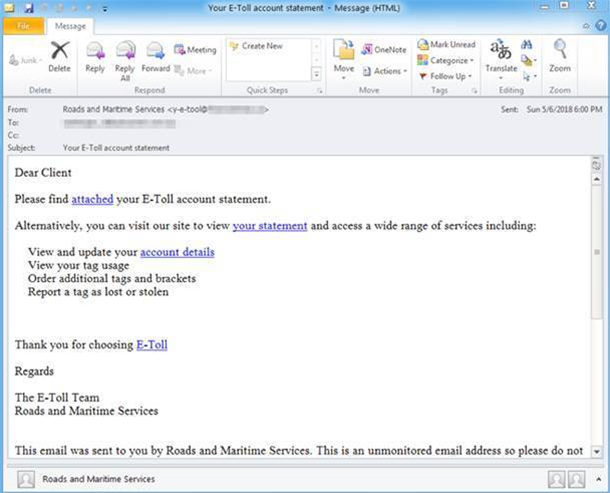
Security provider Proofpoint has warned that the DanaBot banking Trojan is being aimed specifically at Australians through emails purporting to be an E-Toll account statement from NSW Roads and Maritime Services, among others.
DanaBot is able to steal banking credentials, cryptocurrency wallets, browser and email client data, system information and more, according to Proofpoint.
The company first noticed DanaBot being targeted at Australians in early May. Those emails had the subject “Your-E-Toll account statement” and linked indirectly to a malicious Microsoft Word document.
If that document was downloaded and opened (and macros were enabled) it in turn downloaded the DanaBot malware – but only if IP geolocation suggested the victim was in Australia.
Once installed and configured by its command and control server, DanaBot captures a system info report, a screenshot of the desktop, and a list of files, and sends them to the server.
It then proceeds to inject code into internet banking pages (presumably to steal credentials or modify transactions), steal cryptocurrency wallets, take credentials from FTP clients, and extract information from mail clients, web browsers and instant messenger programs.
More recently, DanaBot has been spread via emails with a variety of subjects, including:
Cert "123456789" Doc:-"123456789" Document12345-678 GT123456789 Invoice and Tracking Code 12345678 Invoice from John DoeThese emails link to a JavaScript that downloads DataBot.
“After nearly two years of relentless, high-volume ransomware campaigns, threat actors appear to be favoring less noisy malware such as banking Trojans and information stealers. DanaBot is the latest example of malware focused on persistence and stealing useful information that can later be monetized rather than demanding an immediate ransom from victims,” said Proofpoint.
Banking Trojans now account for almost 60 percent of malicious email payloads, according to the company.
“The social engineering in the low-volume DanaBot campaigns we have observed so far has been well-crafted, again pointing to a renewed focus on 'quality over quantity' in email-based threats.”
Image credit:







.png&h=141&w=208&c=1&s=1)
