Key takeaways
- Proofpoint’s Data Risk Map provides a unified view of how sensitive data moves, who can access it, and how it might leave the organization.
- The Data Risk Map helps highlight risky sharing settings and policy gaps across endpoints, cloud, and collaboration platforms.
- Data lineage enables analysts to follow data from its origin, through every change, copy, or transfer until it leaves the organization.
- One-click remediation actions embedded in the investigation workflow enable teams to quickly contain exposure before data loss occurs.
You can’t secure enterprise data at scale without clear visibility. And today, sensitive data is continuously created, shared, and moved across collaboration platforms, cloud storage, endpoints, and on-premises systems.
Without a clear and complete view of where data resides and how it flows, security teams struggle to understand data risk. Their data security is reactive, not proactive.
Proofpoint’s Data Risk Map solves this problem by turning visibility into action. It provides a unified view of how sensitive data moves, who can access it, and how it might leave the organization.
The Data Risk Map helps teams identify and reduce risk before breaches occur. For data security analysts and data loss prevention (DLP) administrators, fragmented telemetry is replaced by prioritized, actionable insight. Rather than reviewing isolated alerts, teams can track sensitive data and prevent its loss.
From visibility to actionable intelligence
At its core, the Data Risk Map answers three key questions:
- Where is your sensitive data?
- How does it move?
- Who can access it?
The Data Risk Map is a single intuitive interface within the Data Security Workbench. It brings together insights from multiple sources. These include cloud and endpoint DLP, as well as Data Security Posture Management (DSPM), Insider Threat Management, and AI Data Governance.
Teams can see where sensitive data lives, how it’s accessed, and where it’s moving. This helps them move from reactive investigations to proactive governance.
Security teams can identify high-risk repositories, track data flows, and see which users or agents use sensitive information. For data security administrators managing policies across multiple channels, this unified view is particularly valuable. Instead of reviewing logs across multiple tools, analysts can see cross-channel data activity in one place. This makes it clear whether existing policies provide adequate coverage.
Identifying exfiltration risk across channels
While access risk exposes sensitive data inside the organization, exfiltration risk occurs when data leaves through unsanctioned or uncontrolled channels.
The Data Risk Map shows how sensitive information moves across systems and where it exits. Security teams can quickly decide if data activity is normal or potentially risky.
For example, the Data Risk Map highlights patterns such as:
- Sensitive files uploaded through web applications
- Data copied from corporate repositories to personal cloud storage
- Files shared through collaboration tools outside approved workflows
These insights help analysts spot weak points and apply stronger controls where needed.
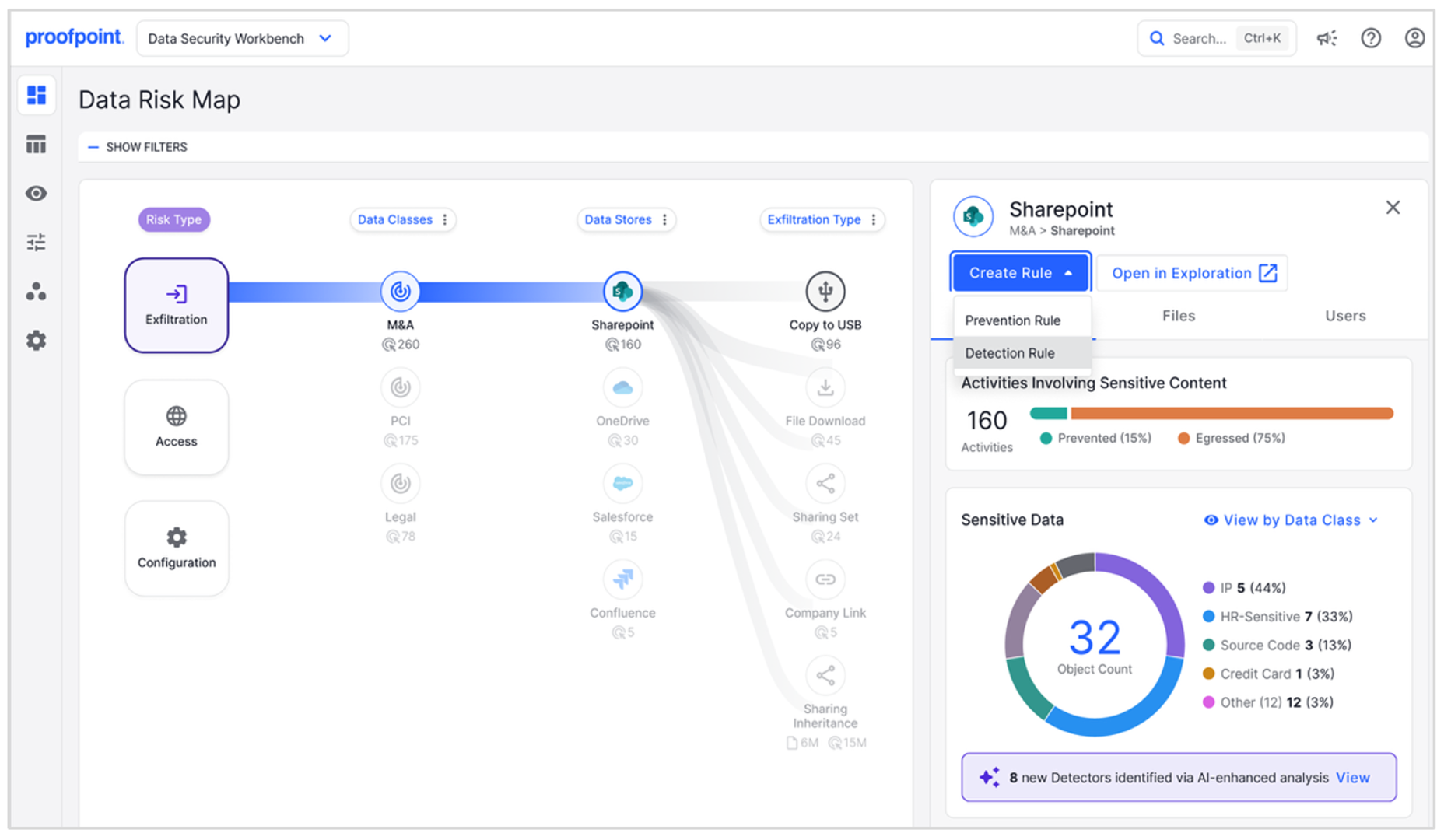
Figure 1: In the Data Risk Map, analysts can see how data flows between repositories and exit channels.
Teams can filter the view by time range, repository, activity type, or data classification. For DLP administrators, this makes it easier to find policy gaps. For example, if sensitive files repeatedly move through a channel without controls, it’s clear that extra detection or prevention policies are needed.
By linking data movement to specific data classes and locations, analysts get a clear view of how data leaves the environment.
Understanding data movement with data lineage
A key capability of the Data Risk Map is data lineage. This traces sensitive files from their origin through every change, copy, and transfer until they leave the organization.
Data lineage enables analysts to see the full history of a file:
- Where the file originated
- How it was modified or transferred
- Where it left the environment
For incident response teams, this traceability speeds up investigations. Instead of manually connecting events, analysts can quickly see how a file moved across cloud services, endpoints, and external destinations.
Proofpoint links events across all channels where users interact with data. Every file is assigned a persistent identity that stays the same even when the file is downloaded, copied, or shared. This enables continuous tracking of data across environments.
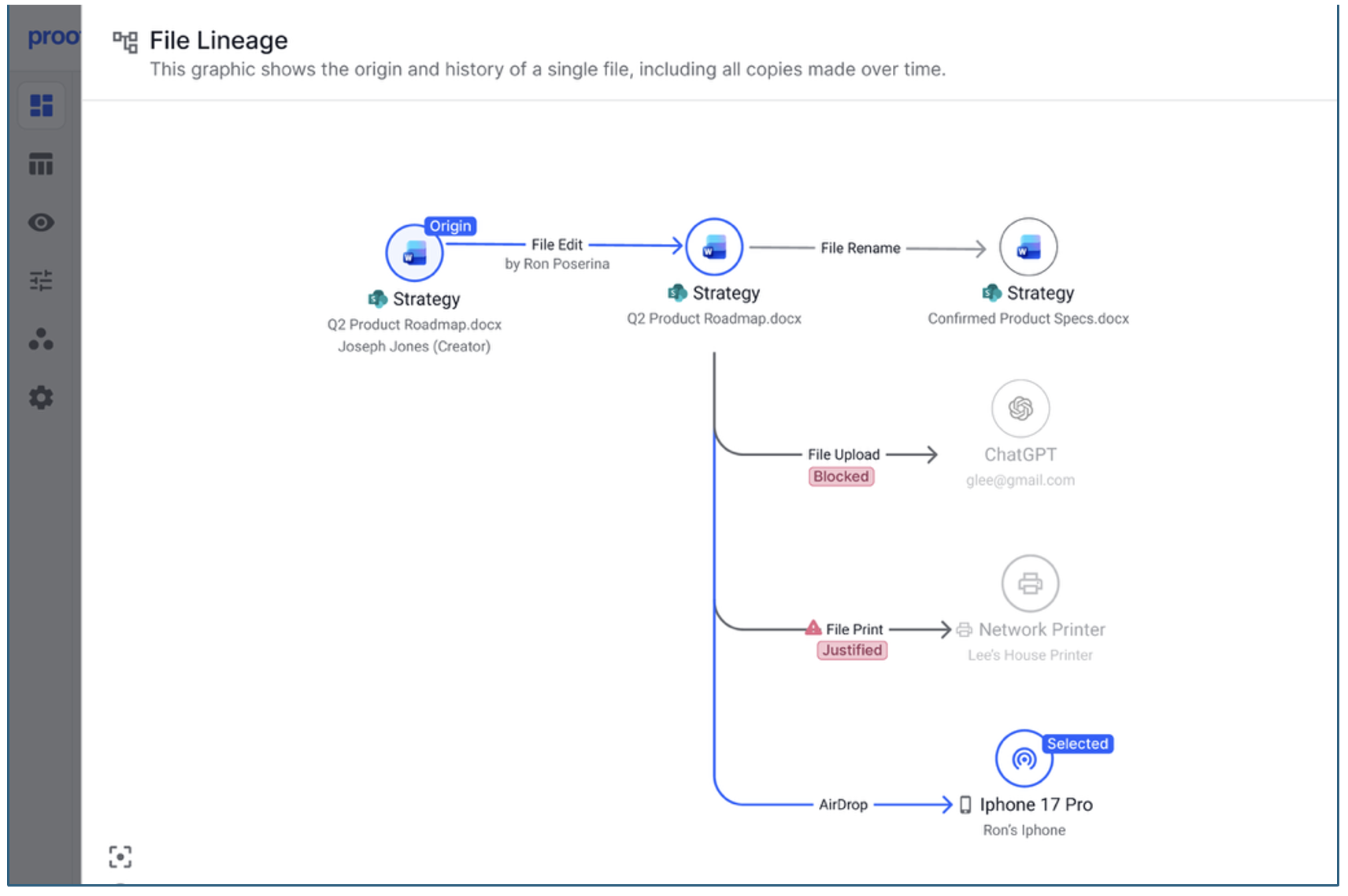
Figure 2: With data lineage modeling in the Data Risk Map, sensitive files can be traced from their origin through every transformation, copy, and transfer until they reach an exit channel.
For example, say a file is stored in SharePoint and shared with an external collaborator. Later, it’s downloaded to an endpoint and uploaded to a personal email account. The Data Risk Map connects all these actions in a single file lineage.
The Data Risk Map supports major collaboration platforms such as Microsoft SharePoint, Microsoft OneDrive, Google Drive, and Salesforce. By linking cloud activity with endpoint telemetry, Proofpoint ensures unbroken visibility across the data lifecycle.
Understanding and reducing access risk
A common cause of data exposure is overly broad access. Often, sensitive files are stored in locations that allow access across large groups or entire organizations.
For example, a SharePoint folder might contain regulated data but allow access to everyone in the company. This greatly increases the chance of misuse or accidental exposure.
The Data Risk Map highlights these risks. Analysts can see:
- Which repositories contain sensitive data
- How widely data is shared
- Which users, applications, or AI tools are accessing it
The access risk view also correlates exfiltration activity on those same files. This helps analysts answer key questions:
- Is widely shared data exfiltrated more often?
- Is frequently exfiltrated data also overexposed?
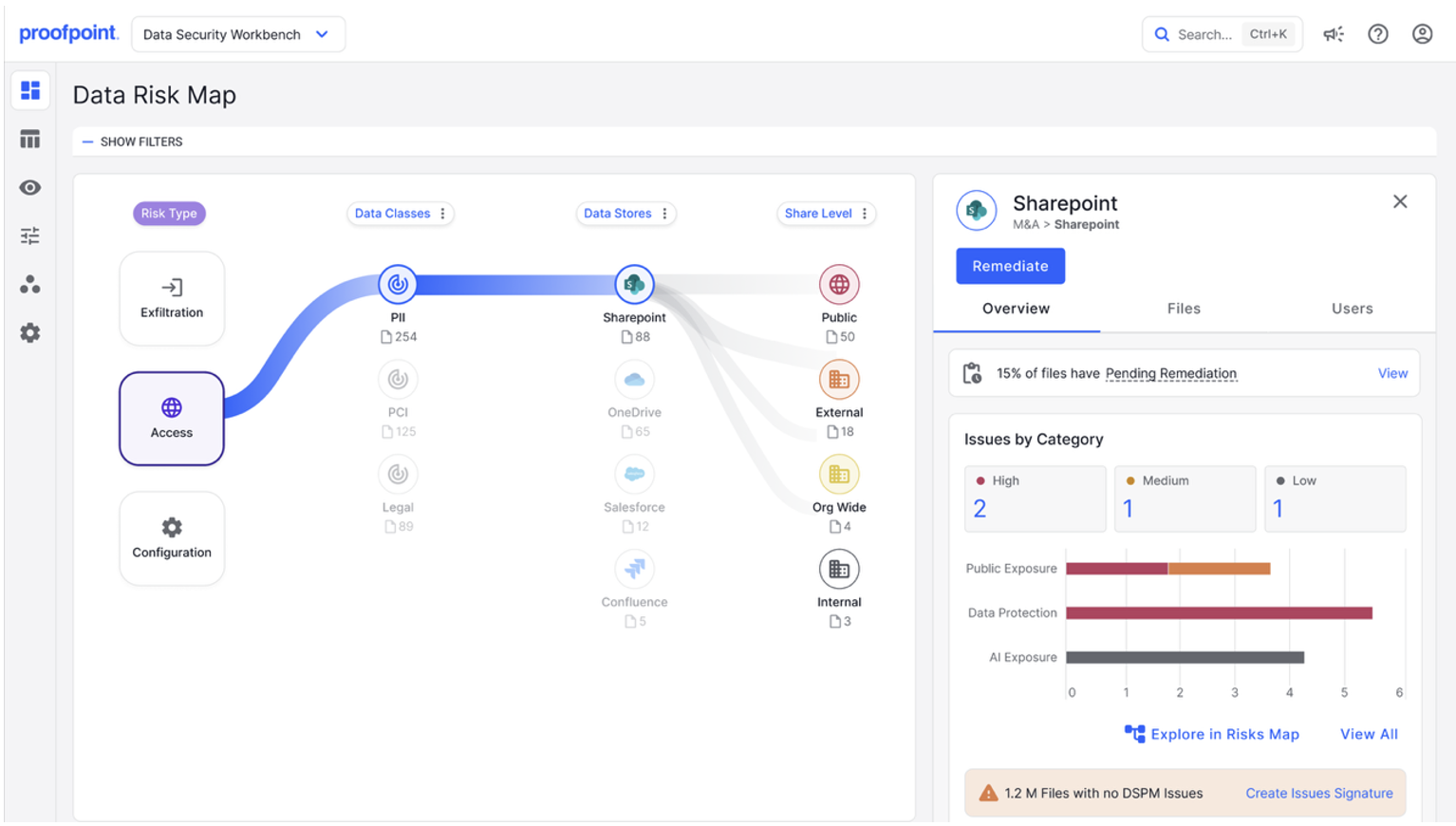
Figure 3: The Data Risk Map helps analysts identify risky situations by showing which repositories contain sensitive data, how widely that data is shared, and which users, applications, or AI tools are accessing it.
These insights help teams focus on the highest-risk issues first. As access permissions are tightened, the Data Risk Map shows the resulting drop in risk.
This visibility is even more valuable as companies adopt generative AI tools and automation agents. Teams can monitor how AI interacts with sensitive data and ensure it follows policy.
By linking data classification with access controls, the Data Risk Map provides a clear view of who can access sensitive data and whether that access is appropriate.
Accelerating response with one-click remediation
Visibility matters only if teams can act quickly. Therefore, the Data Risk Map also includes capabilities to speed up response.
Teams can perform one-click remediation actions for platforms such as Microsoft 365 and Google Workspace directly from the interface. These actions include:
- Revoking unauthorized file access
- Fixing risky sharing settings
- Quarantining exposed files
Because teams perform these actions directly in the investigation workflow, they can contain exposure of sensitive data more quickly.
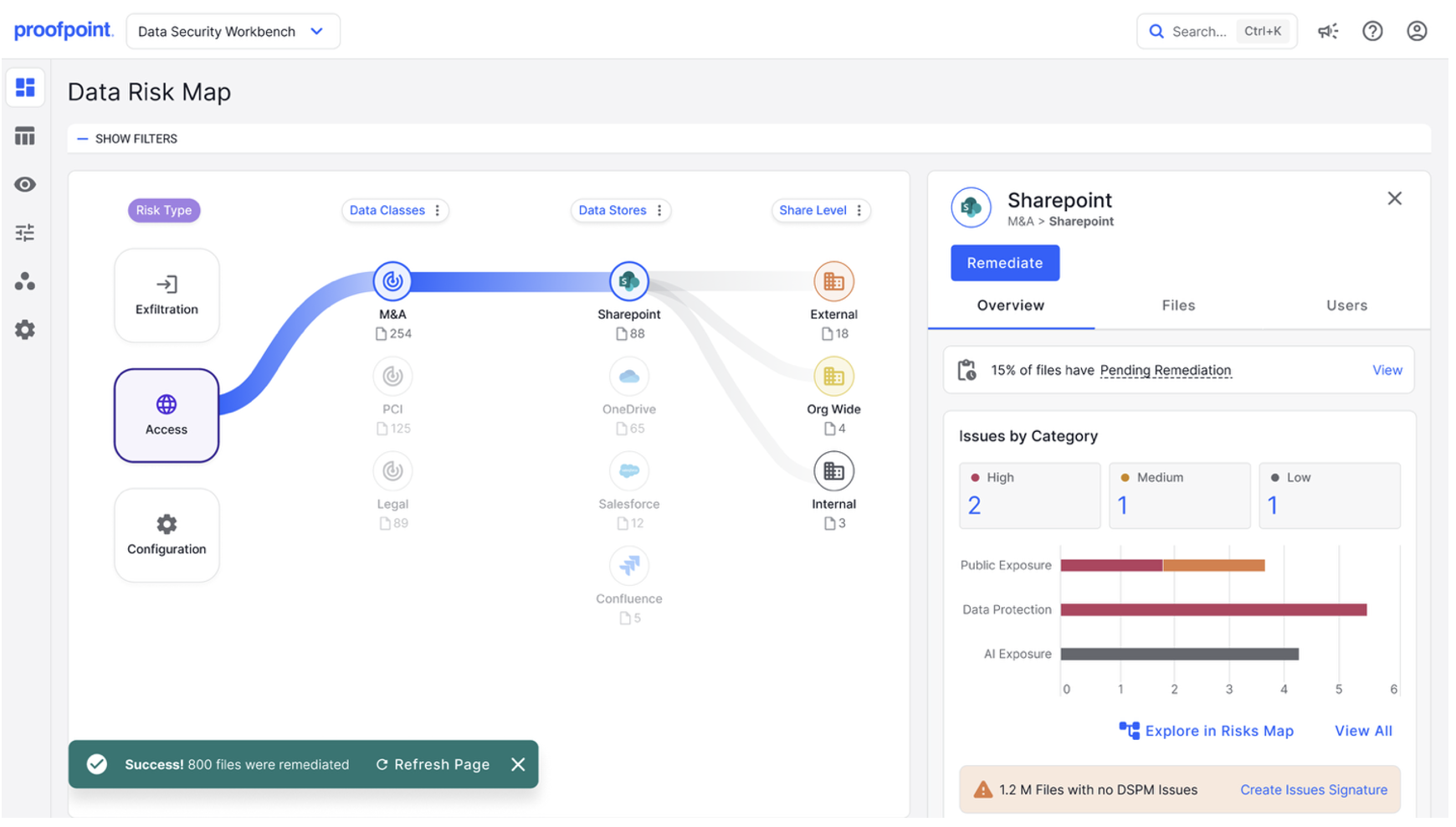
Figure 4: The Data Risk Map includes built-in remediation capabilities designed to reduce response time. In this figure, access to 800 files was remediated with a few clicks, helping the organization to quickly contain data exposure.
Closing the gap between insight and protection
In modern environments, managing data risk can be overwhelming. Users and AI generate large volumes of data activity across collaboration platforms, cloud storage, endpoints, and on-premises systems that are hard to connect.
The Data Risk Map simplifies this by bringing everything together in one place:
- Visibility
- Lineage
- Investigation tools
- Remediation actions
This enables a more proactive approach to data security. Teams can see risk as it develops, understand data movement, and act before sensitive information is lost.
Today, data flows constantly across systems and platforms. Clear visibility is no longer optional. It is essential for protecting your organization’s most valuable information.
Find out more
To learn more about Proofpoint's unified data security solution for the AI era, visit https://www.proofpoint.com/us/products/data-security-governance.










