It’s been clear for a long time that attackers will leverage any means necessary to infiltrate a targeted organization. Unfortunately, attackers often benefit because many of the technologies that protect the most critical attack vectors do not share threat intelligence, which leaves organizations to try and patch together their own integrations. At Proofpoint, we feel that to best protect our customers, we must collaborate with other leading next-generation cybersecurity companies to share threat intelligence and enable better protection across an organizations’ key security controls.
In that spirit, today we announced that we are making it easier for joint Proofpoint and Palo Alto Networks customers to detect and stop cyberattacks. Our companies have partnered to integrate best-in-class security intelligence from Proofpoint Targeted Attack Protection (TAP) email security and Proofpoint SocialPatrol social media security with Palo Alto Networks WildFire for automated protection across the network, endpoint and cloud.
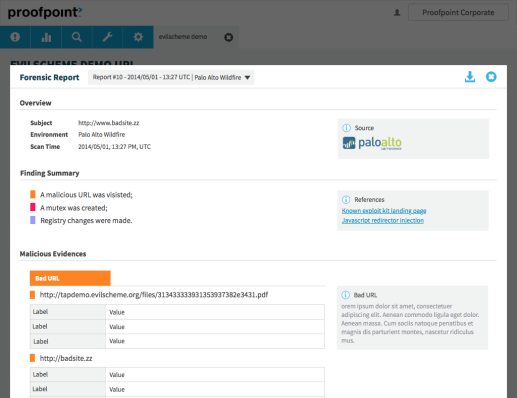
The first integration ensures that both TAP and Wildfire receive potentially malicious email attachments for automated threat protection across Proofpoint’s email gateway and Palo Alto Networks’ next-generation firewalls and Traps Advanced Endpoint Protection. An example is shown below.
The second integration combines Wildfire’s ability to analyze potentially malicious links in a cloud sandbox with Proofpoint SocialPatrol’s ability to scan and, if necessary, remove links throughout an organization’s social presence. This includes Facebook, Twitter, LinkedIn and Instagram. Please see the image below.
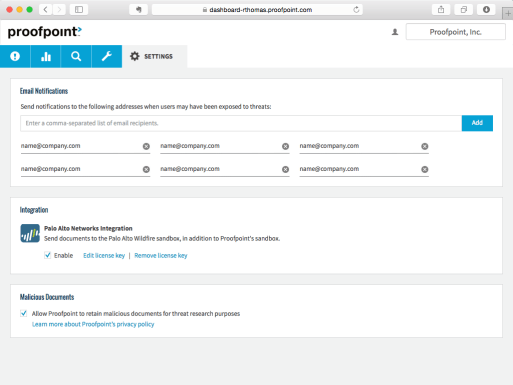
The even better news is that this is a one-step integration. Joint customers can turn it by entering their Wildfire API key on the TAP or SocialPatrol integration settings tab.
For more information, please visit proofpoint.com/proofpoint-palo-alto-networks. View today’s press release.
Do you have any questions on this partnership? Feel free to ask below in the comments, or reach out on Twitter (@rkalember).










