“Offensive” security awareness and “defensive” security awareness are two learning approaches that you can use to build a robust security culture in your company. They involve applying different strategies to educate your employees about threats and how they can respond to them safely.
You may have heard the terms “offensive cybersecurity” and “defensive cybersecurity.” You use defensive tools and techniques to strengthen security vulnerabilities. And with offensive tools and techniques, you focus on identifying those vulnerabilities before attackers find them first.
How do defensive and offensive approaches apply to security awareness? Here’s a quick overview:
- With a defensive approach, users learn the fundamentals of security.
- With an offensive approach, users learn how to protect themselves and the business against future threats.
Let’s use a sports analogy here. You can actively learn to be a defensive goalie and block threats. Then, you can take your skills up a level and learn to score points with protective techniques.
With Proofpoint Security Awareness, our industry-leading threat intelligence informs both approaches. We help people learn how to defend against current threats. And we give them the tools for taking offensive action against future threats.

Live-action series about Insider Threats. (play video)
Defensive security awareness: set the foundation
We all have to start with the basics, right? With defensive security awareness, you teach people the fundamentals of security and set the stage for safe behavior. This training is often reactive. It enables people to respond to immediate threats and incidents as they arise.
At Proofpoint, we believe in using behavioral science methodologies, like adaptive learning and contextual nudges. We combine this with a threat-driven approach, weaving trend analysis and insights about recent security breaches into our training.
A personalized adaptive framework
The adaptive learning framework is a personalized defensive approach to training. It recognizes that everyone learns differently; it is the opposite of a one-size-fits-all approach. You can teach security fundamentals in a way that is meaningful for each person based on what they know, what they might do and what they believe.
This framework lets you drive behavior change with education that is tailored to each person’s needs. That can include their professional role, industry, content style and native language. The learner can engage with a wide variety of styles and materials. And each training is tied to a specific learning objective.
Adaptive learning recognizes that people learn best in short bursts that are spread over time. Our microlearning video modules are under three minutes, and our nano-learning videos are under one minute. These formats give people the flexibility to learn at their own pace.
For instance, our “You’re Now a Little Wiser” nano series offers bite-size training on topics such as data protection to help users learn about specific threats.

Screenshots from a one-minute nano-learning video.
Contextual nudges and positive reinforcement
Training is essential if you want to build a robust security culture. But it is not enough to change behavior fully. Here is where contextual nudges play a vital role in helping to reinforce positive behavior habits once they are formed. These deliberate interventions are designed to shape how people behave.
Nudges are rooted in a deep understanding of human behavior. They can move people toward making better decisions, often without them realizing it. They are gentle reminders that can guide people toward creating optimal outcomes. That, in turn, helps to foster a defensive security-conscious culture in your company.
It is important to find the respectful balance of nudging people toward secure behaviors without being too intrusive or complex. For example, when a user fails a phishing simulation exercise, Proofpoint Security Awareness offers “Teachable Moment” pop-ups that give helpful examples of why the email was fake. This contextual, timely learning provides fine-grained details that will help people identify a potentially malicious message in the future.
Lately, we have been creating Teachable Moments around Phish Hooks. This is a coding system that calls out the problematic malicious features of an email. The codes are based on the NIST PhishScale, a well-respected academic categorization of the difficulty level for people to understand phishing.
For instance, a Teachable Moment Phish Hook might remind people that a business email should include the signature of the sender and that the signature should display the expected contact information.
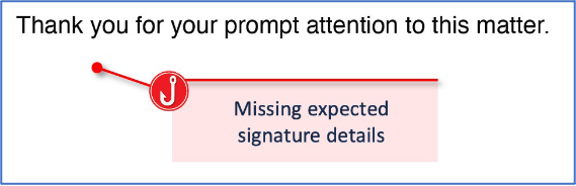
Example of a Phish Hook code.
Offensive security awareness: teach prevention
It is not enough to use phishing simulations to train your people. Once your employees know the fundamentals of security awareness, you can focus on how to enable their offensive security behavior. If a real-world threat slips through detection tools, people must know how to identify and react before the threat can escalate.
At Proofpoint, we release hot security news every week and initiatives each month about upcoming time-specific events. Your program benefits from the threat intelligence we provide about trending attacks. This information helps you keep your people trained on emerging threats.
Weekly Threat Alerts
Threat Alerts are weekly news bulletins that focus on a specific current attack. Each alert explains what the threat is and who it might target in your business. This drives offensive security awareness. Often, these alerts can make you aware of a specific lure that is being used. The alerts are based on trending threats happening now, analyzed by the Proofpoint Threat Intelligence Services team or collected through continuous open-source research.
With each Threat Alert, we recommend applicable training, end-user communication and phishing simulations (if applicable). For instance, our threat team reported artificial intelligence (AI)-themed malware phishing that spoofed corporate IT requiring a system update. The Threat Alert included a visual example of the email lure. It also featured a suggested drive-by phishing campaign and a training module about sophisticated attacks.
Monthly Attack Spotlights
Attack Spotlights are monthly releases that cast a wider lens on a type of attack. They focus on a particular threat attack that is global in nature and growing in prevalence or expected to trend soon. The attack is often related to time-based events such as holidays, travel seasons or shopping. The spotlight is released a month in advance with awareness material, training and a campaign plan, and is available in our 12 core languages.
For example, in anticipation of a busy shopping season, we released an Attack Spotlight about fraudulent shipping notifications in the late fall. And we released an Attack Spotlight on cryptocurrency investment scams as we saw an increased prevalence of conversation-based attacks.

Example of an Attack Spotlight.
Perfect blend: a yearlong, threat-driven campaign
Making campaigns for a whole year is a lot of work. That’s why we’ve curated a yearlong campaign that covers a full calendar year with content, assignments and a flexible communication plan. This comprehensive campaign is an impactful blend of threat-driven training delivered for both defensive and offensive approaches.
Foundational defensive security awareness
From a defensive security approach, the yearlong campaign effort ensures that people gain solid foundational knowledge. It explains what they should do at a basic level to protect themselves and the business.
This modular campaign is designed to fit your company’s time and needs, launched as individual months or continuously for the full 12 months. The continuity of a single theme—“Cybersecurity Heroes”—brings a consistent look and feel to the campaign.
Cybersecurity Heroes covers 12 curated, evergreen topics like insider threats, ransomware, physical security and account security. For instance, the January topic was data security, and that monthlong campaign included an animated video, knowledge assessment, newsletter, interactive game and completion badge.
Future-facing offensive security awareness
For a proactive security approach, the yearlong campaign lets you shift your focus to emerging threats that your business and employees might face. The manual work for baseline training is already in place. That allows you to concentrate on a threat-driven lens.
As part of this initiative, Proofpoint offers varied campaign lengths to give you program choice and flexibility. Admins can choose a time structure that best fits their needs and allows them to move quickly to incorporate trending and timely topics into training.
For instance, to help companies teach their users about data security, we curated a four-week campaign of awareness content and training resources. That information included a campaign guide, newsletter, virtual background, sticker and word search game.
Example of yearlong campaign content.
Take both approaches with Proofpoint
A well-rounded security awareness strategy often combines both defensive and offensive tactics. Going back to our sports analogy: When you combine these approaches, you can enable your people to be the goalies who defensively block incoming threats. You also help them to become offensive point-scorers who can stop the attacks from happening.
With defensive security awareness, your employees can learn from past and recent incidents to improve their current behavior. For instance, education is delivered through an adaptive framework, contextual nudges and yearlong training on security basics.
With offensive security awareness, you can teach and encourage your users to create a security culture that helps minimize future risks. This includes delivering expanded training through weekly Threat Alerts, monthly Attack Spotlights and yearlong campaign flexibility.
Find out more about Proofpoint Security Awareness.










