Security incidents involving a cloud account takeover can be very costly for today’s enterprises. A recent Ponemon Institute study found that companies lose $6.2 million annually from cloud account compromises. Things are getting worse, too: 50% of respondents in the same Ponemon study said the volume or frequency of cloud account compromise incidents has increased over the past 12 months.
The growth of cloud storage, the rise of remote work and greater use of cloud applications for anytime-anywhere workforce collaboration are all helping to increase attackers’ interest in targeting cloud accounts. Malicious actors know that sensitive data is there for the taking, resting in cloud storage applications or moving between cloud and web applications.
There is additional upside for attackers who succeed at cloud account compromise. Following a cloud account takeover, attackers can potentially use the account (and often do) for data exfiltration, business email compromise, and lateral movement (including sophisticated social engineering). These extended campaigns can lead to more account compromises and greater data and financial loss for organisations.
A powerful gateway: the enterprise Okta or Office 365 account
Active Directory, across on-premise and in the cloud, is ubiquitous as the identity provision technology in any large enterprise. This is a gateway to Office 365 apps and more, which are core to how work gets done in many organisations. Okta Identity Cloud is a very popular secure cloud single sign-on (SSO) solution for users to access the IT-approved applications they need to be productive, including when they are working remotely. These enterprise applications are known as federated applications.
While this method of user authentication is convenient, it also makes a user’s credentials for an enterprise Office 365 or Okta account a top prize for attackers. Account compromise in this case means gaining the keys to a very powerful gateway. If a malicious actor has access to an enterprise user’s cloud account credentials for Office 365 or in Okta, they can also then access all the other enterprise applications using those same credentials.
And, if the enterprise doesn’t enforce multifactor authentication (MFA) to increase the security of user accounts, getting to those apps and data is even easier for an attacker following an account takeover.
Protect almost any modern cloud app from account compromise with our integrated approach
Organisations can better protect their users from the risk of an account compromise in thousands of applications in the Office 365 and Okta environments.
Proofpoint CASB detects and remediates suspicious logins in near-real time based on our integrations with Proofpoint Emerging Threat (ET) Intelligence, Proofpoint Targeted Attack Protection (TAP) and CASB proprietary threat intelligence and user behaviour analytics.
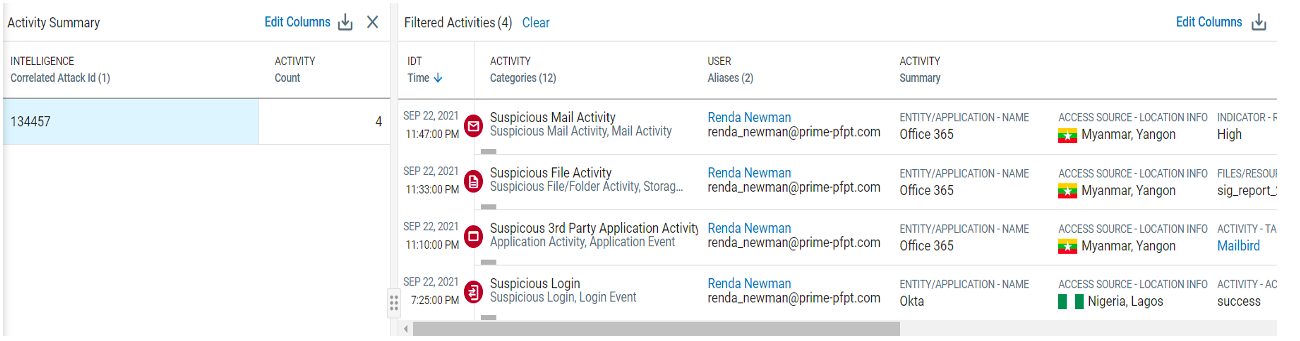
Figure 1: Attack sequences within Proofpoint CASB simplifies hunting for threats by correlating initial access with post-access malicious activity with high confidence.
This unique threat context comes from:
- Visibility into the recently phished users and the most attacked users in your organisation (“Very Attacked People” or VAPs) from Proofpoint TAP
- Intelligence on latest cloud, email and web from our proprietary security research and Proofpoint Emerging Threats (ET) Intelligence
- Visibility into recent or active cloud threat infrastructures (such as IP addresses, hostnames and OAuth apps associated with threat actors) from Proofpoint CASB
This means that we can protect your users when they log in via the Okta SSO, even if the identity provider isn’t Okta. This is most commonly the case with customers using Okta for SSO and Microsoft Active Director as their identity provider.
Best practices if your organisation relies on Microsoft Active Directory or Okta
General cloud security guidance:
- First and foremost, require multi-factor authentication for access to all enterprise applications
- Update the single sign on (SAML SSO) certificate between Okta and the federated applications
- Recreate secrets and certificates for any newly created or authorised OAuth applications within your Office 365 and Okta environments
Now, let’s move onto our recommendations if you use a CASB, especially Proofpoint CASB:
- Identify successful suspicious login alerts and failed login events using your users’ Office 365 or Okta credentials
- If any successful account compromise, build timelines of compromised user’s activity. Within Proofpoint CASB, that comes
- automatically with attack sequences
- Otherwise, review any risky activity around user creations, files, third-party app authorisations and other settings related to those users
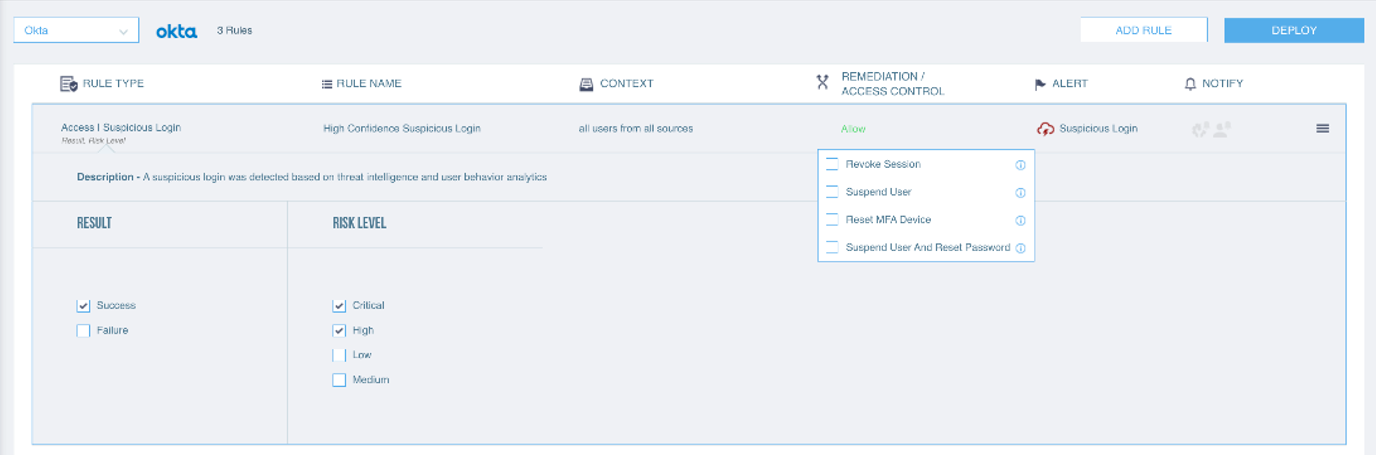
Figure 2: CASB detection and remediation rules for Okta-federated applications to protect from account takeovers
Threat hunting scenarios based on potentially risky user administrative and risky single sign-on activity:
- User creations, especially ones that don't match expected new employee onboarding
- “Password Reset” and “Device MFA Setting” activity that can be leveraged to takeover authentication factors
- Unexpected access to business applications by Active Directory (AD) and Okta admins
- Escalation to privileged AD and Okta groups such as groups that allow access to critical cloud resources or ones that exempt from authentication factors
- Look for anomalous user behaviour within Office 365 and Okta federated applications
More detailed instructions are available to Proofpoint customers on our Communities portal.
Multi-mode suspicious login detection with Proofpoint CASB
Proofpoint CASB supports dynamic and policy-based detection, remediation and real-time access prevention of suspicious logins into cloud apps using the breadth of our deployment models—CASB API, adaptive access controls and forward proxy.
With our comprehensive and adaptive controls, Proofpoint can protect any application used in modern enterprises today from account compromise and takeover attempts.
To learn more about how Proofpoint CASB can protect your cloud accounts from account compromise and other threats, read more here.










