Definition
A component of the Software Development Life Cycle (SDLC) is maintaining it, and patch management strategies handle the way updates and hotfixes are deployed among a network of devices. Software versioning can be difficult to manage when several developers release frequent updates, and these updates are consistently released every month. The process of patch management presents considerable overhead for IT staff, but it’s a necessary part of device maintenance to avoid conflicts, cybersecurity issues, bugs, and other vulnerabilities in installed software. Several patch management solutions are available to help automate the process and reduce overhead for IT staff.
How Patch Management Works
Patch management is often automated using third-party software, but some human intervention is also necessary to determine the frequency at which updates are deployed, who oversees the process, and what happens when patches must be rolled back. Automation software saves time for IT staff that must review and test patches before they are installed, but the strategies surrounding the way software is deployed still requires human intervention.
The first step in patch management is scanning devices for outdated software. Devices could be on the local network or cloud-connected and controlled by the organisation. The devices scanned must give the scanner permission to access the targeted software to identify if it’s outdated. If any scanner can access the device’s software version, it may be a cybersecurity issue. In some cases, the software itself can poll a central server to determine if the currently installed version is the latest or if an update is available.
If a device contains outdated software, the next step is to upload the latest update to the target. If the software polls a central server, the software might trigger a download of the latest updates and hotfixes. Patch management must apply the right updates and hotfixes in the correct order. If a user has not run previous updates, patch management ensures that all earlier updates are installed before applying the latest one.
One patch management strategy is to send files to a central server where the developer’s software can poll for any updates. That would enable users to manually download files instead of allowing the software to update automatically. Some users prefer to manually install files instead of using automation tools, so developers need to give users that option.
Finally, IT staff must have a way to know if patches were successfully installed. A good patch management solution provides reports that can be reviewed by developers or other IT staff to ensure that the installation was successful. This component is crucial for internal IT staff that must keep track of dozens of devices on the network to ensure that they are not vulnerable to crashes and cybersecurity threats.
Best Practices With Patch Management
To ensure the update process is smooth across all devices, software developers, and the businesses that manage updates should create a strategy. The strategy created depends on the network environment and the type of devices that must be patched. Software developers can release software to the public, but the updates must be handled in a way that allows users to freely update software even if they are behind a few versions. Businesses must create a patch management strategy that ensures all users have the latest updates to protect corporate assets and prevent data loss.
Before coming up with a strategy, it’s also important to understand the SDLC that controls the way developers release updates. Software developers release updates, but organisations must check for them frequently. Patch management software can do most of the work for the IT staff, but staff must still check reports to ensure updates didn’t fail.
Common best practices to devise a patch management strategy:
- IT staff and software developers should understand the importance of patch management. Any software that must be updated frequently should have patches available for download, and IT staff should use automation tools to ensure software is updated as these patches are made available. Any vulnerabilities found in software either from pen-testers or whitehat hackers should be patched immediately.
- Severe vulnerabilities should be patched immediately using hotfixes if the software is out of date. An example of the seriousness of outdated software is the WannaCry ransomware outbreak. Outdated Windows versions allowed the ransomware to spread even though Microsoft released updates to its SMB vulnerability.
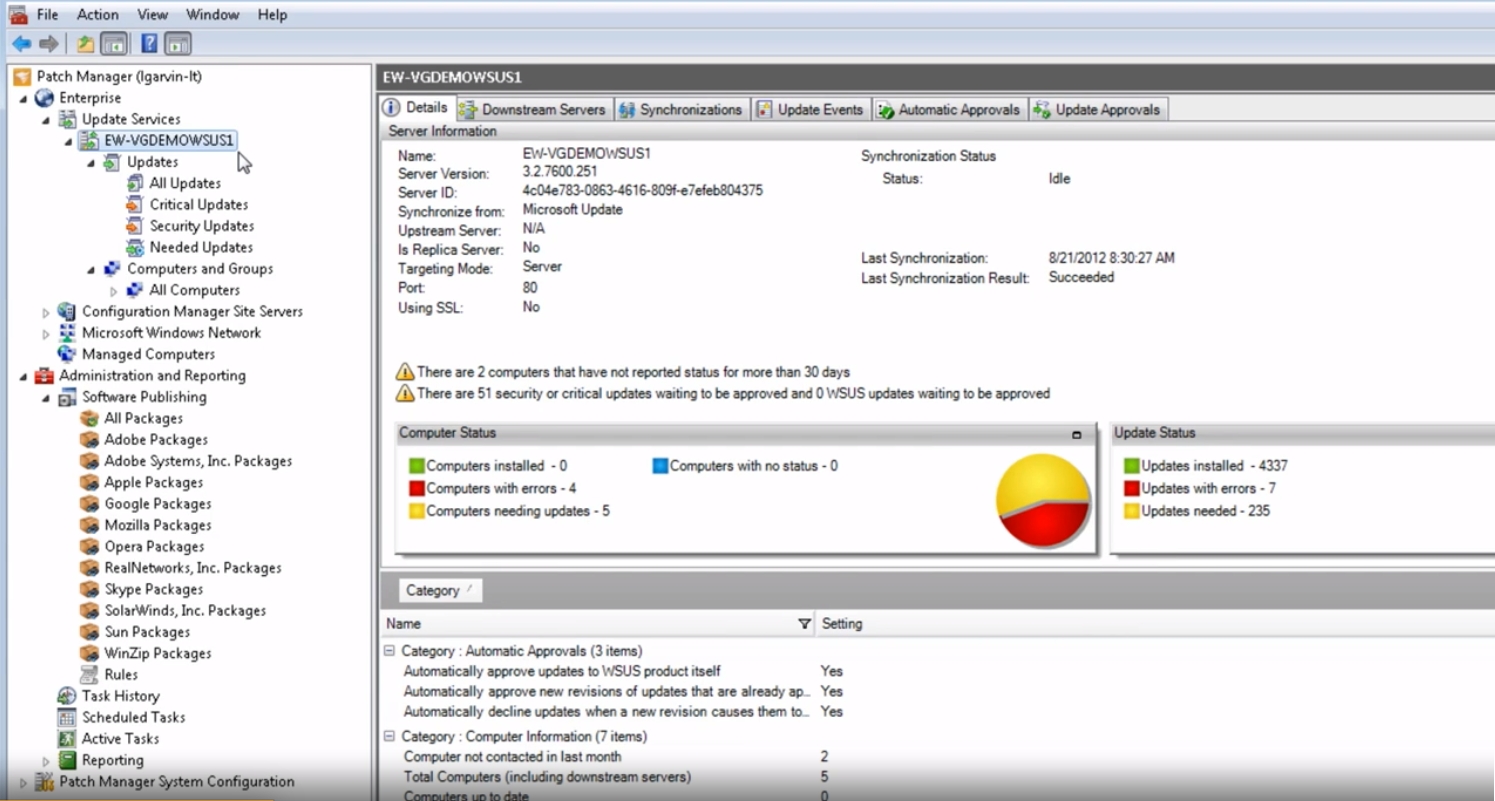
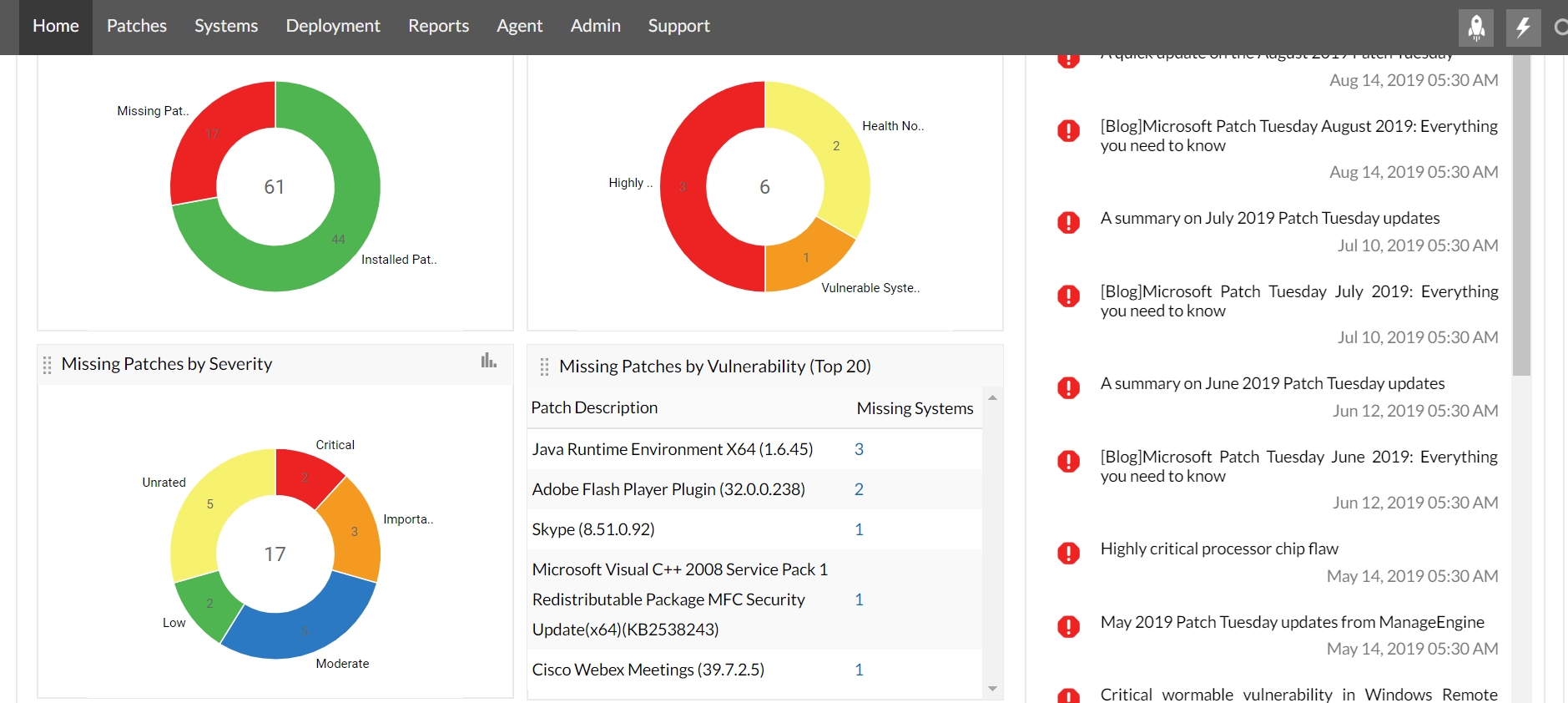
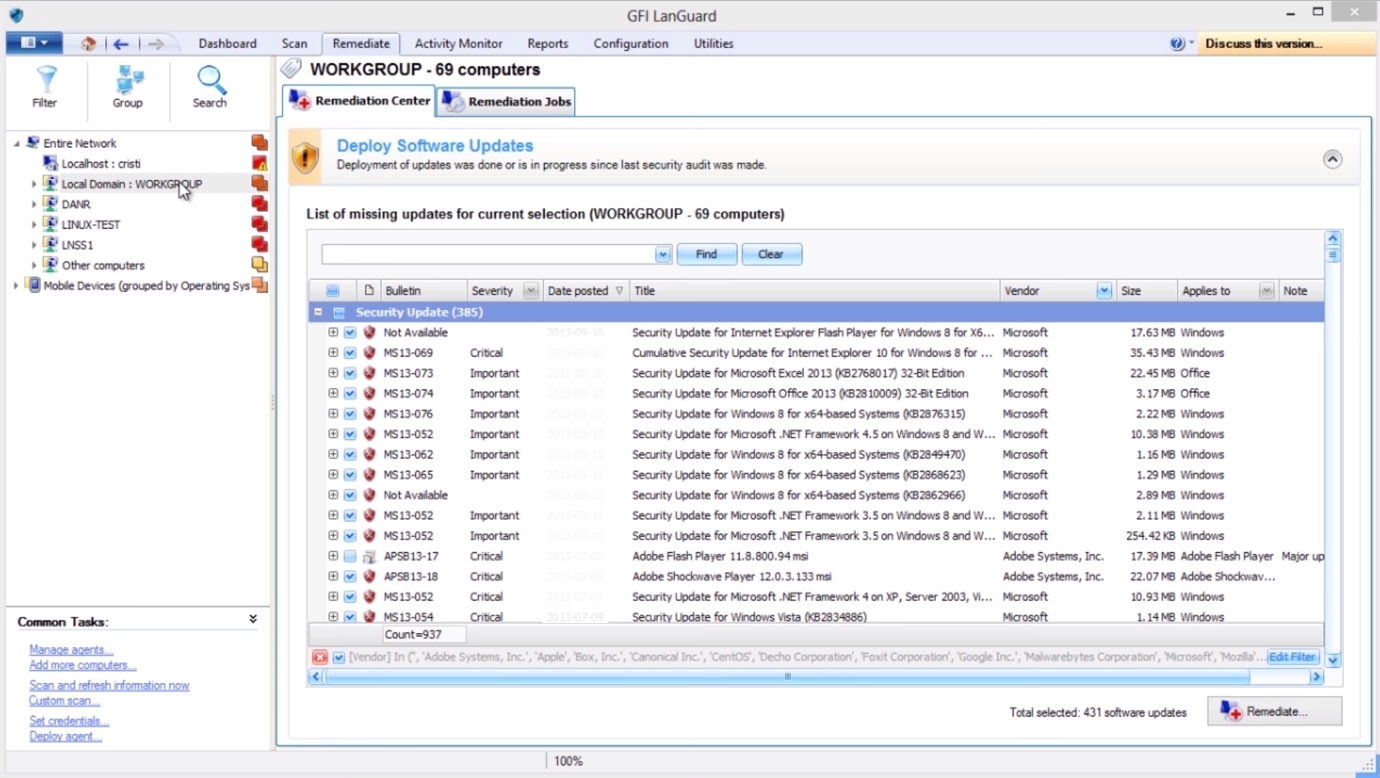
- For businesses, an automation tool can help reduce the overhead of patch management. Some developers offer enterprise versions of their applications, which have automation tools that can be installed on a central server. These automation tools will scan devices for outdated software and update them where appropriate.
- Test updates on devices before applying patches. Developers should test their patches before deploying them to the public, while businesses that send updates across multiple devices should test it on one testing device before automatically updating dozens of machines.
Choosing a Patch Management Solution
If a developer does not offer an automation solution, several tools exist that help IT staff deal with patch management. These tools are generally for enterprise businesses, as individuals can download updates manually at home. Several software developers offer tools that run on home user machines that will poll a central server and download updates automatically. The Windows 10 operating system is an example of software that automatically downloads and updates without user interaction.
The following list contains a few patch management tools that can be used to automate updates:
E-book: Ransomware Detection & Survival Guide
Ransomware is an old threat that won’t go away. Download the Proofpoint 2022 Ransomware Survival Guide to learn what to do before, during, and after an attack.
Proofpoint Threat Response Solutions
Find out how Proofpoint Threat Response solutions enables security teams to respond to threats that are targeting people in their organisation.