The risk of data loss increases as your business embraces digital transformation, remote work and cloud computing. Legacy data loss prevention (DLP) solutions weren’t developed with these new dynamics in mind.
In today’s world, your DLP platform must provide visibility across multiple channels for data loss—email, cloud services, endpoint and web. It must scale with your needs while protecting data without interruption. And since data doesn’t lose itself, it should be people centric. Part of that means providing insight into user behaviour.
The Gartner Market Guide for Data Loss Prevention explains that “DLP technology is mature, but today, organisations look for comprehensive solutions that go beyond traditional DLP measures”. It also notes that “Security and risk management leaders should focus on risk-based adaptive data protection techniques to strengthen the data security of their organisation”.
Let’s take a look at some other insights from the report.
Adaptive DLP: Enhanced with classification and converged with insider threat management
The Gartner Market Guide states that “DLP vendors are increasingly converging with insider risk management platforms. This convergence enables better detection of data exfiltration as it enriches DLP events with anomalous user behaviours, improved risk scoring and real-time monitoring capabilities”. This, the report notes, enables an adaptive, risk based DLP approach.
It also shares important insights such as:
- Enterprise DLP (EDLP) solutions offer centralised policy management and reporting functionality
- Enterprise DLP (EDLP) solutions generally incorporate advanced content inspection techniques to identify complex content and apply remediation
- Content inspection within IDLP solutions has improved considerably, and many of these solutions can recognise classification tags from more sophisticated classification tools
- DLP solutions use data classification labels and tags, content inspection techniques and contextual analysis to identify sensitive content and analyse actions related to the use of that content
Gartner sees that DLP vendors are increasingly converging with insider risk management platforms. This convergence enables better detection of data exfiltration as it enriches DLP events with anomalous user behaviours, improved risk scoring and real-time monitoring capabilities.
Gartner recommends in its Market Guide that a business use enterprise DLP if it has limited resources and its “users are transacting sensitive information through multiple channels”. The report also mentions that consulting and managed services can help “shorten the time to value and augment lean IT and security departments”.
Proofpoint delivers adaptive DLP
As a key player in the space, we think Proofpoint Enterprise DLP expands on the capabilities that Gartner shares in its report. The following is an overview of how we do that.
People-centric insights and risk-based adaptive DLP
Proofpoint Enterprise DLP protects against data loss across email, cloud, endpoint and web. Our solution combines content, behaviour and threat telemetry from all these channels to address the full spectrum of people-centric data loss scenarios such as:
- Leavers who feel entitled to take intellectual property with them
- Compromised users whose data is stolen by threat actors
- Careless users who accidentally email sensitive documents to your partners
People-centric information protection is an adaptive, risk-based approach to DLP. Our Enterprise DLP solution uses people and application risk scoring and modelling for dynamic policies.
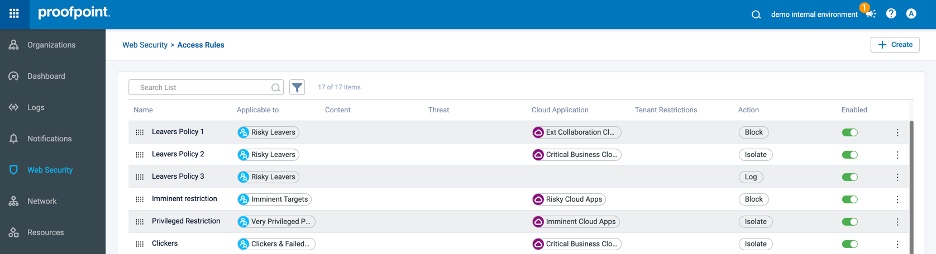
Figure 1. Web security risk-based access rule.
In Figure 1, “Leavers Policy 2” applies isolation as a data control when “Risky Leavers” access “Critical Business Cloud Apps”.
One console, one agent, one cloud-native platform
Proofpoint provides what administrators and analysts need to accurately detect DLP and insider threats:
- Policy management
- Workflows
- Alert management
- Threat-hunting capabilities
- Classification sophistication
- Reporting
- Dashboards
And it does all this in a single console and using a single lightweight agent. Our DLP platform is quick to deploy. It is scalable, multichannel, API-driven and cloud-native.
It includes data lineage tools such as a file timeline for visibility, and a user timeline for context on user intent. User and file timelines show alerts and activities before, during and after an incident. They provide insight as to whether the user might be careless, compromised or malicious.
Intelligent classification
Our DLP platform integrates with our Intelligent Data Classification solution. Powered by artificial intelligence (AI), it helps classify your business-critical data. And it suggests actions based on risk to help you prioritise which of your assets you should protect first.
This integration can expand and accelerate DLP for your security teams. Thanks to AI-generated detectors, dictionaries and automated labelling, your data will be better protected against the threat of careless, compromised and malicious users.
Right people and processes
Proofpoint Managed Services and specialised partners can help you design, implement and manage your information protection program. You can also get advice from data security experts to augment your core team if needed.
Key channels and solutions for DLP
In the Market Guide for Data Loss Prevention, Gartner mentions that DLP is included as a capability in a variety of products, such as email security solutions, security service edge (SSE) and endpoint protection platforms (EPPs). We believe that Proofpoint has products for each solution. We integrate them all on our Proofpoint Sigma information protection platform.
Email security solutions
Proofpoint Email Data Loss Prevention and Proofpoint Email Encryption protect sensitive data sent via email. They are both part of our email security platform.
With data detectors that we have honed over the last 15 years, we help you identify regulated data and intellectual property in email. Proofpoint helps you enforce company policies through services such as email encryption, revocation, quarantine and more.
Endpoint DLP solutions
We integrate Proofpoint Endpoint DLP with our insider risk management solution to enrich DLP events with user behaviour telemetry.
You can use Endpoint DLP to monitor file activity and scan content to determine if users are handling sensitive data in line with your corporate policy. You can also ask a user to justify actions they take with data.
We also offer a library of rules that can help your business to prevent data loss via USB, web browser, cloud sync folder, print and more.
Insider risk management solutions
Proofpoint Insider Threat Management monitors user activity. This includes their use of applications, input and output, website access, and file movement across Windows and Mac systems. We track and alert you about risky user behaviours. And we provide sophisticated threat-hunting tools and visual evidence to accelerate your threat insider investigations.
In other words, our single lightweight dual-purpose agent helps you both prevent data loss and manage insider threats.
Plus, Proofpoint Cloud App Security Broker (CASB) monitors for anomalous file exfiltration by departing employees or employees who share files with their personal cloud storage accounts.
Cloud security solutions
Proofpoint cloud security solutions secure access to the web, cloud services and private apps. We combine CASB, Proofpoint Web Security, secure access and browser isolation to enable people-centric visibility and controls across your business.
We deliver a broad range of capabilities, including:
- Rich, cross-vector threat intelligence on user and cloud services risk
- Advanced threat protection against compromised cloud accounts, malicious OAuth apps, malicious files and malicious websites
- Granular controls, such as step-up authentication, read-only access via browser isolation and micro-segmented application access
- Proxy and API-based DLP to prevent unauthorised access to sensitive data in the web and in cloud services, and to ensure compliance
- Visibility into shadow IT, acceptable use controls, application governance for software-as-a-service and third-party OAuth apps
- Cloud security posture management for infrastructure-as-a-service
You can enforce stricter controls for risky users and cloud services, too. Risky users can be highly targeted or vulnerable users. Or they can be privileged groups like admins and VIPs.
Risky cloud services can be very privileged apps, abused public services and questionable gaming sites—to name a few.
Learn more
Download the Market Guide for Data Loss Prevention from Gartner to learn more about market direction and what to look for in a DLP solution. We also encourage you to take a look at Proofpoint Enterprise DLP to see how we deliver on the recommendations and key findings that are shared in the report.
Gartner, Market Guide for Data Loss Prevention, by Ravisha Chugh and Andrew Bales, published September 4, 2023.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organisation and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.










