Healthcare concerns drive us to do a lot of things like change our diet, work out more, and take medication. But they should never lead us to fall victim to phishing campaign. Threat actors regularly use purported health information in their phishing lures because it evokes an emotional response that is particularly effective in tricking potential victims to open malicious attachments or click malicious links.
In the latest example, Proofpoint researchers observed cybercriminals impersonating Vanderbilt University Medical Center and sending out fake HIV test result emails that attempted to lure recipients into opening malicious content embedded into the message. This low volume campaign had top targeted industries: global insurance, healthcare, and pharmaceutical organizations, but others were targeted as well. This attack leveraged Koadic RAT, if successful and Koadic is installed, attackers can run programs and access victims’ data, including sensitive personal and financial information.
Campaign Overview
This campaign was a small attack in which the emails claim to come from “Vanderbit [SIC] Medical” and have the subject line “Test result of medical analysis”. The body of the email encourages recipients to open a malicious Microsoft Excel attachment titled “TestResults.xlsb” and claims that the recipient’s HIV results are contained within it. Figure 1 shows a sample below.
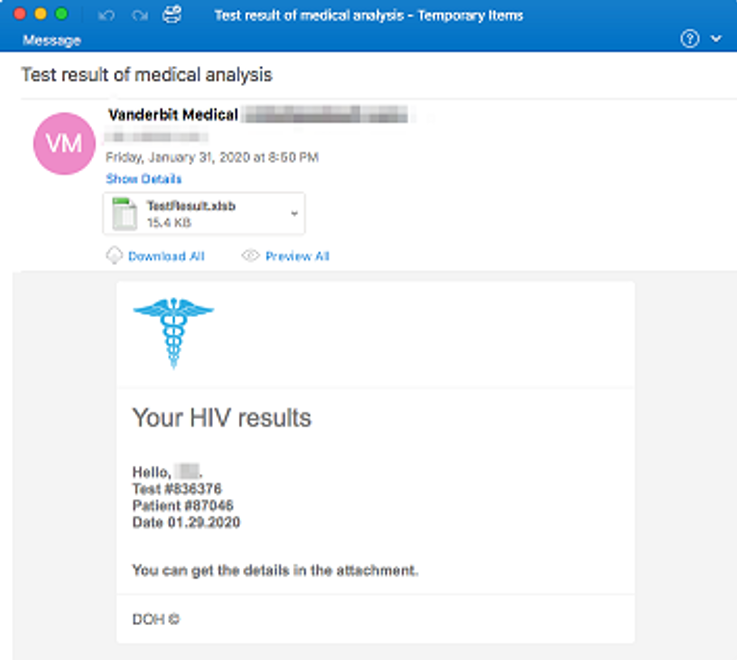
Figure 1 Email with Malicious Excel Attachment Claiming HIV Results
If the recipient opens the attachment, the Excel document opens and prompts the user to enable macros as shown in Figure 2.
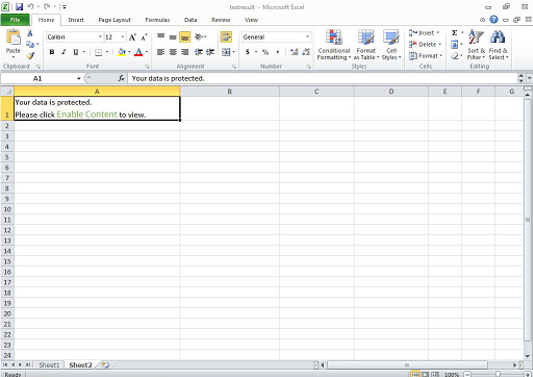
Figure 2 Malicious Excel Document Prompting to Enable Macros
If the recipient enables macros, the document then downloads Koadic. Originally Koadic was intended as a tool for network defenders and allows the actor to take complete control over a user’s system. In recent years it has been used by a variety of nation state actors, including both Chinese and Russian state-sponsored groups, as well as attackers associated with Iran.
This latest campaign serves as a reminder that health-related lures didn’t start and won’t stop with the recent Coronavirus-themed lures we observed. They are a constant tactic as attackers recognize the utility of the health-related “scare factor.” We encourage users to treat health-related emails with caution, especially those that claim to have sensitive health-related information. Sensitive health-related information is typically safely transmitted using secured messaging portals, over the phone, or in-person. If you receive an email that claims to have sensitive health-related information, don’t open the attachments. Instead, visit your medical provider’s patient portal directly, call your doctor, or make an appointment to directly confirm any medical diagnosis or test results.










