Key takeaways
- Email addresses remain the dominant digital identifier across the web.
- Compromised credentials frequently lead to compromised identities.
- Modern agentic AI systems increasingly read, interpret, and send email, which further expands the attack surface.
In 1637, René Descartes asserted “I think, therefore I am.” With that statement, he grounded human existence in cognition. Today, identity is more broadly defined as your unique identifier.
In the physical world, it’s established through tangible, authoritative attributes such as biometric data, government-issued documents, or personal records. In the digital world it’s anchored in practical markers that systems can verify. And because global systems require universal, consistent, and easily validated identifiers, the email address has become the de-facto digital identity.
The email address as the universal digital identifier
Research shows that between 64.9% and 92.4% of web applications use email addresses as the primary identifier for critical functions, such as creating new accounts and recovering passwords. This is driven by several practical advantages. Not only is there a global uniqueness, but verification can also be automated. Plus, it’s convenient for users. And it can be used as a default recovery channel across platforms.
Obviously, there other methods, such as usernames and customer identification numbers. However, these methods are often reserved for high value access to online bank accounts, financial records, medical records, and so on. The drawback of these methods is that it can be a real challenge for users to maintain and remember a wide variety of different identifiers. And even when an email address is not used, recovery is often through an email address.
Email also allows users to differentiate between their corporate and personal identities (or, in some cases, multiple personal identities). You wouldn’t use your corporate email address for online transactions because you won’t always work for the same company, so you won’t always have access to that email.
Why email remains the primary attack vector
Although a “username” alone is not enough (at a minimum a password is required to form credentials), this reliance on email as a de facto identity means that it remains the most valuable attack vector for threat actors. The primary goal for most attacks is using social engineering, malware, keyloggers and exploits to obtain credentials so that threat actors can access systems and data.
Additional layers of security and multifactor (MFA) authentication have raised the bar for securing identities. For example, identity access management (IAM) and privilege access management (PAM) add more controls on what information an “identity” can access. (However, they don’t prevent an identity from being compromised.) Meanwhile, identity threat detection and response (ITDR) can detect when credentials have been compromised and take actions to mitigate that compromise. ITDR might force the use of a new password or require additional authentication steps. All these components and controls should be part of a comprehensive security strategy.
Attackers continue to adapt to these extra controls and use new, innovative methods to get around them. Whether it’s a man-in-the-middle (MITM) attack to steal authentication tokens or MFA bombing (where the user constantly gets requests to authorize a login), Proofpoint has found that 59% of compromised accounts had MFA enabled. According to the Verizon 2025 Data Breach Investigations Report (DBIR), 54% of ransomware victims had credentials stolen prior to the ransomware attack. And stolen credentials are the starting point for roughly a third of human-related breaches.
The evolution of email security
The theft of email-based credentials is not new. The first phishing attacks targeted AOL in the 1990s. Since then, attacks have evolved dramatically. While threat actors once sent generic phishing blasts, today they send highly targeted spearphishing and whaling campaigns that use research about individuals to maximize their success. Deepfake voice and video add new layer of deception. The security conversation has changed dramatically. It’s no longer just about protecting email; it’s about protecting the person behind the inbox.
The introduction of agentic AI—which can make decisions and take actions automatically—has meant that protecting email is growing in importance. Agentic AI can automatically summarize emails, suggest responses, and even take action. As such, it has become part of the attack surface for threat actors.
In the same way that users can fall for social engineering attacks, AI tools can fall victim to prompt engineering attacks. Human users may reveal password credentials, but AI tools and agents can also store and reveal sensitive data. And just like humans that can be tricked into downloading and executing malicious code, there will be malicious AI agents that can execute code at lightning speed.
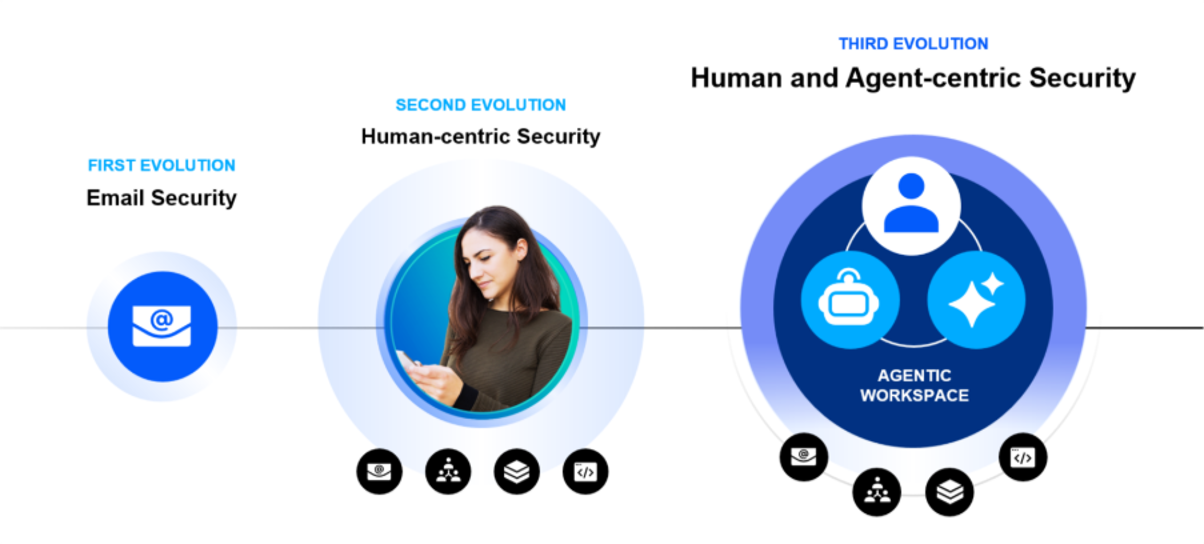
Figure 1. Three evolutions in security.
Proofpoint has already seen email attacks that embed AI prompts as hidden text to attempt to steal data. Other agentic AI tools directly monitor—or are even assigned—an email address to automatically process documents, such as purchase orders or payment processing.
Proofpoint is addressing this transition from email security to human and agent-centric security. It’s doing so by extending protection to include the agentic workspace. We are building on our foundations of human-centric security to include agentic AI. This means detecting and preventing inbound AI inject prompts as well as monitoring and blocking data exfiltration whether it is malicious or accidental.
Conclusion
In the digital world, email is still identity. It connects human users to systems, links authentication across services, and now anchors the workflows of intelligent agents.
As threats evolve from credential phishing to AI prompt manipulation, organizations must shift to a comprehensive human and agent-centric security architecture. If you want to secure email, you must also secure humans as well as the AI systems that act on their behalf.
Learn more about how Proofpoint is securing both AI and humans with intent-based protection here










