

Emerging Threats Intelligence
Proofpoint ET Intelligence delivers the most timely and accurate threat intelligence. Our fully verified intelligence provides more in-depth context and integrates seamlessly with your security tools to enhance your decision-making.
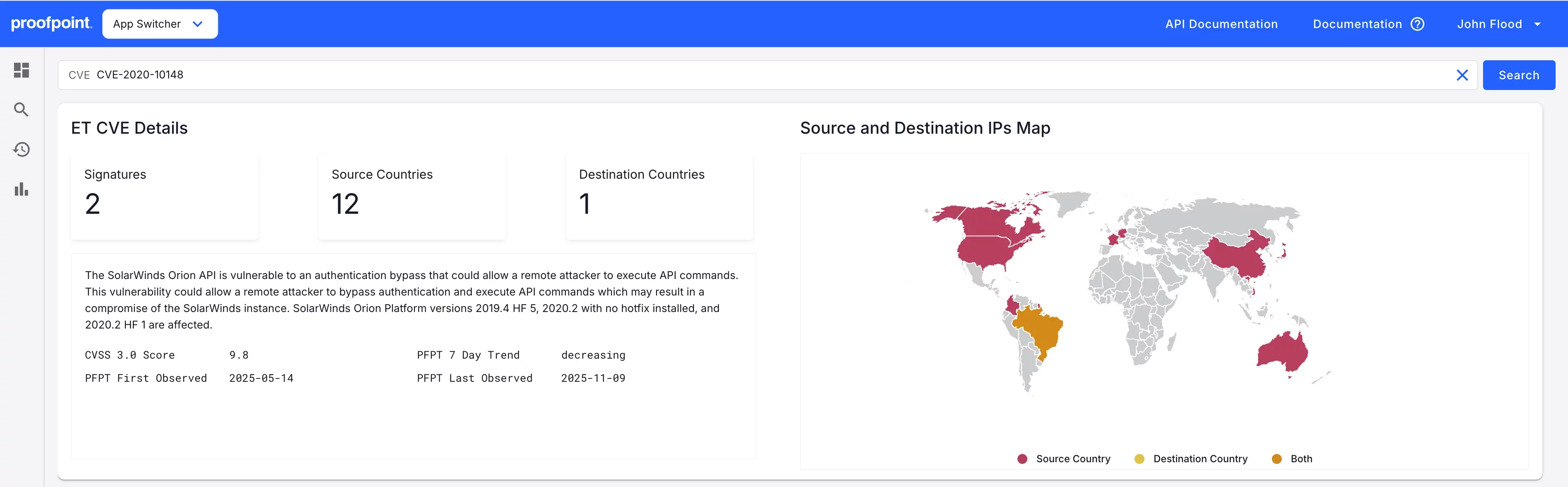
Rich Threat Intelligence and Context Portal
Knowing which types of threat exist no longer suffices to protect your people, data and brand. Emerging Threats (ET) intelligence helps prevent attacks and reduce risk by helping you understand the historical context of where these threats originated, who is behind them, when they have attacked, what methods they used, and what their objectives are. Gain on-demand access to current and historical metadata on IPs, domains and other related threat intelligence to assist in researching threats and investigating incidents.
In addition to reputation intelligence, you receive condemnation evidence, in-depth context, history and detection information. It's all searchable in an easy-to-use threat intelligence portal that includes:
- Trends and timestamps of when a threat was observed and the associated category
- Type of threat and exploit kit names when available
- Related samples used in associated or related attacks.
Actionable IP and Domain Reputation
Emerging Threats (ET) Intelligence provides actionable threat intelligence feeds to identify IPs and domains involved in suspicious and malicious activity. All threat intelligence feeds are based on behaviour observed directly by Proofpoint ET Labs. And they can all be directly fed to SIEMs, firewalls, intrusion detection systems (IDS), intrusion protection systems (IPS) and authentication systems.

Emerging Threats (ET) Intelligence highlights:
Separate lists for IP addresses and domains
IP addresses and domains classified into over 40 different categories
IP addresses and domains are assigned a confidence score for each category
Scores indicate recent activity levels and are aggressively aged to show current conditions
Hourly list updates
Multiple formats supported, including TXT, CSV, JSON and compressed
Easy integration with security tools
Emerging Threats (ET) Intelligence is easily digested by your existing SIEM tools, such as Splunk, QRadar and ArcSight, as well as by threat intelligence platforms (TIPs)

Subscribers receive free use of our Splunk technology add-on (Proofpoint Splunk TA). The add-on integrates Emerging Threats (ET) Intelligence reputation into Splunk to quickly surface log entries appearing on reputation lists, and it’s compatible with existing Splunk reporting. Threat intelligence is directly available for use through Anomali (formerly ThreatStream).
Emerging Threats (ET) Intelligence lists can also be downloaded in the Bro IDS format.
Related Resources
White Paper
Osterman Research: The Value of Threat Intelligence
Datasheet
Emerging Threats Intelligence
Datasheet
ET Pro Ruleset
Datasheet
Emerging Threats Intelligence Features and Usage
Datasheet
Proofpoint Threat Intelligence Services
Explore OEM licensing
Discover fully verified, real-time threat intelligence that integrates seamlessly with your security stack. Speak with a sales expert today









