Threat actors target victims across multiple attack vectors, counting on uncoordinated defensive security technology that’s ineffective against advanced attacks. URLs have emerged as one of these critical threat vectors for phishing.
According to the “2022 State of the Phish” report from Proofpoint, attackers easily create new URLs and use them to target specific users in the supply chain to steal their credentials. The shift to a hybrid workforce compounds the problem, pushing traditional networking and security infrastructures to a breaking point, as employees access applications and data from everywhere.
As enterprises seek to reduce the risk of web-based and URL attacks, businesses strive to implement a combination of products that can protect and address these threats and enable highly flexible monitoring and high-availability capabilities. (Learn more by reading this year’s “Human Factor” report from Proofpoint.)
That’s why Proofpoint and Palo Alto Networks have expanded their strategic partnership, integrating automated browser isolation to help give their shared customers an enhanced security posture—from email to the network and the cloud.
Keeping threats out of the corporate environment
Since 2016, the combination of Proofpoint Targeted Attack Protection™ (TAP), Proofpoint Digital Risk Protection™ and Palo Alto Networks Wildfire™ has provided customers with integrated threat analysis across email, web and social media.
With the partnership’s latest integration, Palo Alto Networks Prisma® Access can be configured to redirect risky users to Proofpoint Browser Isolation™. Cloud-based Browser Isolation helps stop targeted phishing and malware attacks without the productivity-impacting effects of blocking broad website categories and similar intrusive controls. When integrated with Prisma Access, websites are safely rendered in a managed and isolated browsing session to keep threats out of the corporate environment.
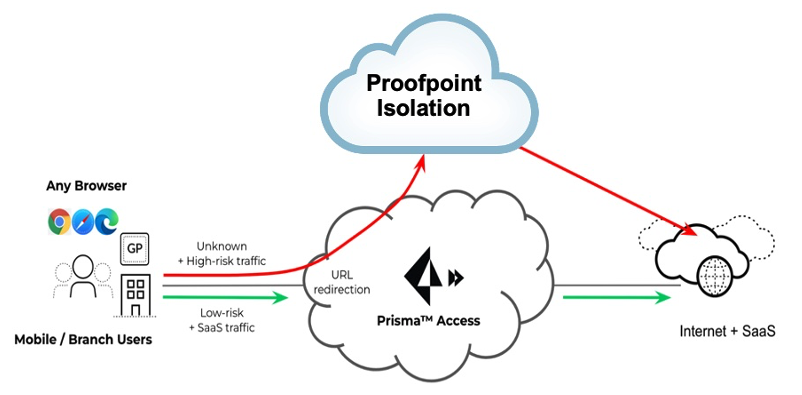
Figure 1. Overview of Palo Alto Networks Prisma Access URL redirection to Proofpoint Browser Isolation.
To automate URL redirection into Browser Isolation, Prisma Access will detect when a user goes to a website that should be opened in isolation. It then redirects that user based on specific URLs or categories, such as webmail or uncategorized sites.
Browser Isolation uses a remote cloud-based browser to manage users’ activity in a secure container. High-risk content, including executable code, is stripped out. A sanitized version of the page is sent to users’ browsers. Any unsafe content that users may encounter will never impact the endpoint—or the enterprise. (Download the Proofpoint Browser Isolation data sheet to learn more.)
Palo Alto Networks Prisma® Access is a complete cloud-delivered platform, allowing organizations to enable secure remote workforces. All users, whether they’re working at corporate headquarters, branch offices or on the road, connect to Prisma Access to access cloud and data center applications and the internet safely. Prisma Access inspects all traffic across all ports and provides bidirectional networking to enable branch-to-branch and branch-to-HQ traffic.
Protecting against threats from high-risk sites and webmail
Employee productivity depends on users safely clicking and viewing potentially risky URLs without putting their organization at risk. To enable this, security products must seamlessly integrate with a cloud-based service that provides secure, isolated browsing that protects against phishing and malware attacks. With Palo Alto Prisma Access and Proofpoint Browser Isolation, enterprises can seamlessly integrate these solutions to deliver best-in-class protection capabilities.
The new integration solves two use cases:
- Isolating high-risk or uncategorized URLs
- Isolating webmail
Customers face the binary choice of either allowing access to web categories that pose a high risk for malicious content, or just outright blocking access. It becomes a trade-off between usability and risk that impacts user productivity.
With the integration of Prisma Access and Proofpoint Browser Isolation, an isolated version of the high-risk website is delivered. Rather than just the binary choice of allow or block, customers can now have the additional flexibility of creating policies to redirect users to Proofpoint Browser Isolation to control viewing pages, keyboard inputs, and file upload and download actions.
Similarly, webmail and the associated clicks and attachments that come with it are a significant risk for organizations. Customers are faced with a choice of either accepting the risk that webmail creates, or blocking it, which creates work-life friction with employees and contractors.
With the integration of Palo Alto Networks Prisma Access and Proofpoint Browser Isolation, users can access webmail while also protecting the enterprise by keeping any opened URL contained in the email body in isolation or restricting downloads of email attachments. A balance between usability and risk can be achieved using Browser Isolation and Prisma Access.
Explore how Proofpoint and Palo Alto Networks work together to keep your web journey safe.










