The Human Factor 2021 Report from Proofpoint can help organizations understand the threat landscape in 2021 to better prepare for future sources of attacks. Notably different in this year’s report is how it covers facets of user risk:
- Vulnerability: The likelihood of users becoming victims based on how they behave or interact with threats.
- Attacks: The probability of users being targeted by cyber attackers or receiving severe threats.
- Privilege: The impact of the damage a successful attack would cause.
Earlier this year, Proofpoint introduced Nexus People Risk Explorer to equip our customers with insight to build a people-centric cybersecurity strategy. The dashboard is a unique tool that can help organizations mitigate risk by providing them a greater understanding of user risk through integrations with various Proofpoint products. Nexus People Risk Explorer goes hand-in-hand with the three facets of user risk covered in The Human Factor 2021 Report.
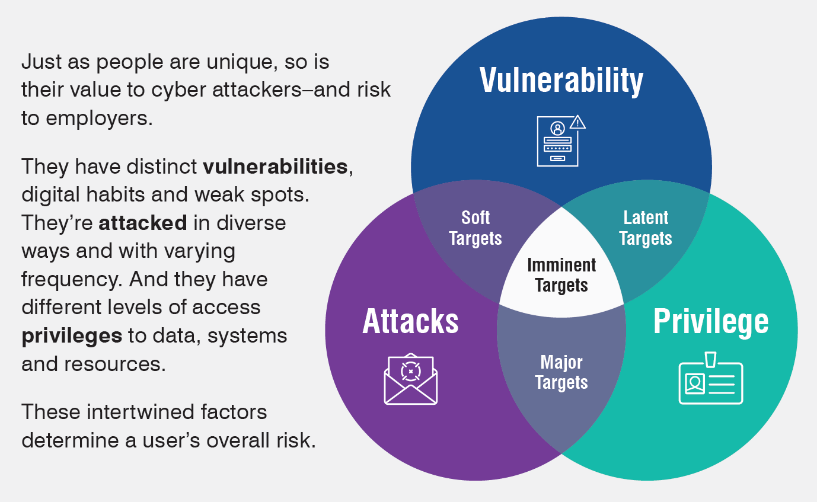
Figure 1. The Human Factor’s categorization of threats in 2021
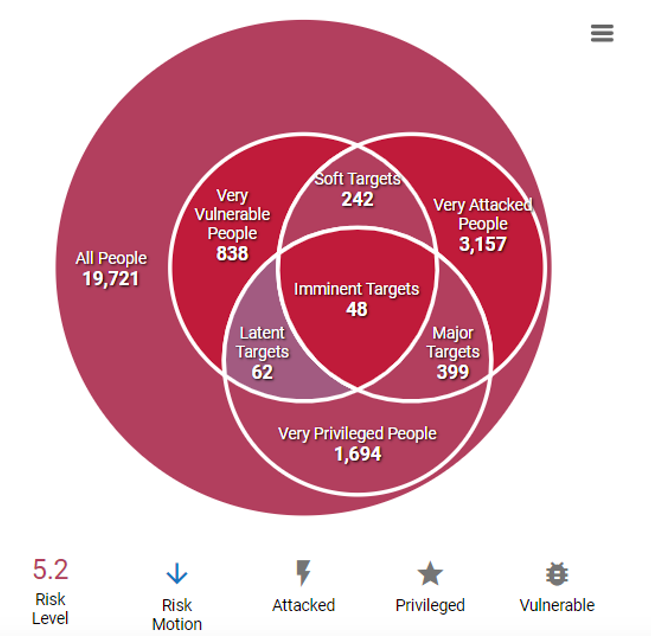
Figure 2. How Nexus People Risk Explorer analyzes user risk in organizations
Social engineering still the go-to technique for many attackers
Cyber attackers have historically sent users widespread attack campaigns with a low click or open rate, only counting on a few users to fall for them. One notable actor (TA407*) averaged one click out of every five emails it sent last year, which is one of the highest attack open rates monitored. This actor was highly selective, sending out only a few dozen emails. It also used advanced social engineering techniques, a strategy many attackers use for targeted campaigns.
Social engineering tactics exploit existing user vulnerabilities such as being “click happy” or unable to readily identify phishing or malware in emails and websites. The report shows that certain departments such as purchasing, research and development, and IT are among the most vulnerable. The types of roles in these departments have access to sensitive personal and financial information that, if stolen or compromised, could have severe consequences.
Did you know? TA407 has targeted universities throughout North America and Europe seeking intellectual property. In 2018 alone, nine members of this group were indicted for stealing data valued at US$3.4 billion.
If organizations don’t know who their most vulnerable users are, they can’t prepare these users to identify and avoid attacks. Nexus People Risk Explorer helps organizations overcome this challenge by providing them a better understanding of their users’ vulnerabilities. Proofpoint helps security teams predict risky users based on behaviors, such as using risky third-party apps (identified via integrations with cloud security solutions such as Proofpoint Cloud Application Security Broker (CASB) and Proofpoint Cloud Account Defense (CAD)) or the propensity to click. Proofpoint can also assess the effectiveness of security awareness training modules.
Security teams can also analyze the most common vulnerability categories that affect their organization by business role, department and VIP groups. Proofpoint doesn’t stop there: Our Nexus People Risk Explorer dashboard provides security control recommendations for security teams to know exactly which customized controls to apply to vulnerable users and departments to help reduce their overall risk score.
Not all attacks are created equal
Ransomware and email fraud, threat types that rely on human interaction and target major industries, are some of the top concerns for chief information security officers (CISOs) today. According to The Human Factor 2021 Report, Proofpoint saw ransomware attacks increase 300% in 2020. And while ransomware operators continue to use email, they’re also turning to more sophisticated strategies to increase their chances of success, such as launching multistage attacks, partnering with “loader” and “trojan” attackers, and using backdoors to target large organizations.
These tactics make it even more challenging for organization to protect their users. Traditional email gateways might miss these complex ransomware attacks, leaving users exposed.
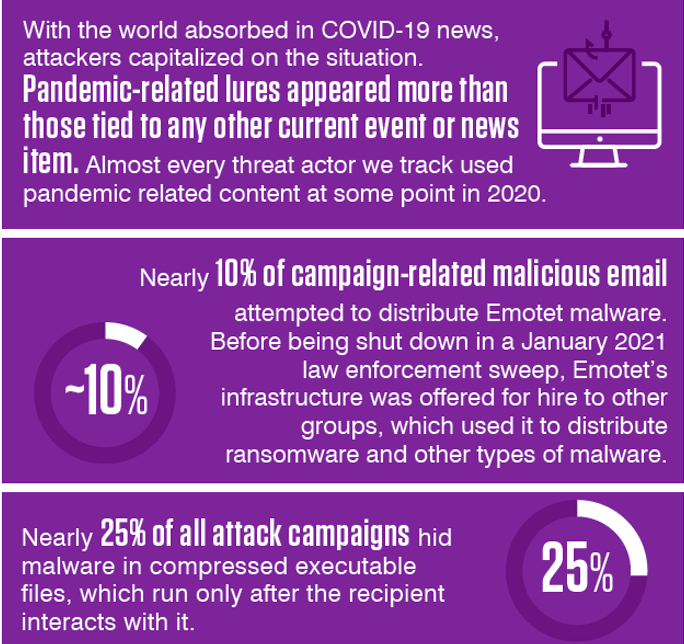
Figure 3. Key findings from The Human Factor 2021 Report
Email fraud that results in compromised accounts is another source of concern for CISOs. Research for The Human Factor 2021 Report shows that in 2020, attackers gained access to user accounts by tricking users into clicking on malicious links and attachments sent in emails on the topics of COVID-19 restrictions and vaccines. These tactics likely succeeded due to the tone and attachments that appealed to emotional current events. And once attackers gain access to a user’s credentials, it’s only a matter of time before they start to move laterally in the organization.
Nexus People Risk Explorer, through the integration with Proofpoint Targeted Attack Protection (TAP) and its Attack Index score, provides insight into which users are most attacked. Nexus People Risk Explorer can also list all attacks that users have received ranked by threat severity score to better identify which users represent the most risk.
Malware and Business Email Compromise (BEC) attacks may be challenging to prevent because of the ever-changing strategies actors use. Proofpoint recommends integrating security controls with security awareness training to empower users to be the last line of defense.
The more privileged the user, the more damaging the attack
The Human Factor 2021 Report notes that “the more privileged the victim, the more access attackers have—and the more damage they can do.” And the top three insider threat management alerts now on the rise, according to the report, relate to connecting unlisted USB devices, performing a large file or folder copy, and opening a clear text file that stores passwords.
Nexus People Risk Explorer synchronizes with Active Directory (AD) to display information on user privilege based on the user’s role and business function. Because AD doesn’t always represent system and data access accurately, Nexus People Risk Explorer includes a feature to create custom groups and track them over time.
Our integration with CyberArk adds an extra layer of information to the privilege data provided by AD, using their Privilege Access Management solution. This integration allows security teams to assign a risk score to the CyberArk group within Nexus People Risk Explorer and get a clearer picture of privilege risk. Using this additional privilege score, security teams can apply stricter controls to certain individuals who are highly privileged based on the systems they access for their role.
Gain a unified view of security risks to better protect users
Learning about past threats is an important step toward strengthening existing security measures. However, attackers constantly adapt their tactics. Also, users attacked in the past could potentially be compromised in the future. So, it’s important to consider the following questions when taking steps to protect your users and organization:
-
How do we know which users are most at risk for future compromise?
-
What makes certain users risky?
- What is the impact to the rest of our organization if a user is compromised?
Download The Human Factor 2021 Report and follow the Proofpoint Threat Insight blog to learn more about the threats in the cybersecurity landscape that Proofpoint analyzed in 2020.
Also, find out whether your organization is entitled to access Nexus People Risk Explorer. The dashboard lets you tie vulnerability, attack and privilege data, so you can save time in identifying and applying the right security controls to protect your riskiest users.










