If your business is a Microsoft 365 customer, you may think you’re well-protected against cyber attacks. Why wouldn’t that be your assumption? After all, Microsoft’s cloud-based email and collaboration platform come with a host of native cybersecurity capabilities. And if you need to add more coverage, you can always subscribe to more tools.
But experts agree that built-in cybersecurity tools for cloud-based email can’t keep you safe from every threat. In Gartner’s February 2023 Market Guide for Email Security, the analysts advised: “[Microsoft and Google’s capabilities] are decent but insufficient for some sophisticated attacks. … Evaluate built-in email security capabilities provided by cloud email systems and augment it with third-party solutions for handling sophisticated attacks.”
What are some of the key risks that you can’t afford to ignore? Let’s look at the top three reasons you may not want to rely on Microsoft 365 native email security alone.
1. Microsoft 365 is a favorite target of cyber criminals
Given the sheer number of successful companies around the world using Microsoft 365, it is hardly surprising that attacking Microsoft 365 is so popular. Many of the world’s largest and most successful companies use Microsoft 365 to get work done.
In March 2023, for example, Microsoft had 300 million monthly active users on its messaging app Teams alone. And Gartner’s Vendor Report: Microsoft notes that Microsoft controlled 88.1% of market share in 2021.
Research for the latest State of the Phish report from Proofpoint helps to highlight just how popular Microsoft is with cyber criminals:
- Out of nearly 1,600 campaigns involving brand abuse in 2022, Microsoft topped the list as the most abused brand.
- More than 30 million messages in 2022 used Microsoft branding or featured a Microsoft product like Office or OneDrive.
Creating your own Microsoft 365 tenant is easy, and even a small business account offers basic default protection. So, when cyber criminals want to test a malicious email, all they need to do is to create their own tenant and send that email to their own mailbox. In this way, attackers learn to pick their own lock, and, in the process, get a universal key to unlock every company that is relying on the same native controls.
2. Cyber criminals keep getting better at what they do
The cybersecurity industry is constantly working to stop cyber crime. Meanwhile, cyber criminals are constantly working to stay one step ahead of defenders. This race to innovate means the threat landscape is evolving at a record pace—and threats are more dangerous than ever.
Stopping sophisticated attacks requires deep cybersecurity expertise and threat intelligence. Take, for example, these sophisticated and difficult to detect attacks:
- Advanced phishing. Most users today are wise to the old-school Nigerian prince-style phishing emails. But today’s advanced phishing attacks are on another level. Attackers use sophisticated tactics to get a hold of multi-factor authentication (MFA) tokens. That puts the company’s entire Microsoft 365 cloud environment at risk. And cyber criminals don’t stop when they gain access to the corporate directory and documents on OneDrive or SharePoint. Once they’re inside, they move laterally across the network. An initial compromise is only the first step in a much larger cyber-attack chain.
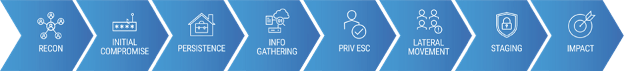
The cyber-attack chain—from initial compromise to privilege escalation and impact.
- Business email compromise (BEC). The motive for most cyber criminals is financial. But they don’t need sophisticated malware to make a profit. Social engineering is a powerful tool. With simple payroll redirect attacks, malicious actors need very little skill other than the ability to spoof an email address. More sophisticated BEC attacks involve hijacking email conversations to divert invoice payments to fraudsters’ accounts. These attacks have no payload; they’re just regular emails. That makes them very difficult for native Microsoft email controls to detect.
- Telephone-Oriented Attack Delivery (TOAD). TOAD attacks are sophisticated and multi-layered. They’re also difficult to combat because they are text-based with no payloads to analyze. There are two distinct types of TOAD attacks, but they usually begin the same way. A victim receives an email directing them to call a customer service representative. Then, depending on the attacker’s objective, the attack path diverges. TOAD attacks take advantage of human vulnerability. And there’s no patch or Microsoft software solution to help with that.
3. Every cybersecurity gap is a liability
Microsoft Exchange Online Protection, which is part of the default Microsoft 365 package, provides basic email hygiene capabilities for inbound messages. But it doesn’t provide any outbound brand protection, for example.
To provide better security coverage, Microsoft offers a wide range of upgrades, like Microsoft Defender for Office 365. Obviously, if you need greater protections, then basic security is not enough.
Microsoft does offer some basic response capabilities if something does get through. But security teams must do some serious heavy lifting to remediate an attack.
And even if you subscribe to every Microsoft 365 security tool, today’s threats require more than just attack detection. Here are three examples of key areas you’d still need to augment Microsoft native security:
- Security awareness. Employees are a company’s last line of defense. Well-trained users are great at spotting fraud—and they can make a big difference. They can be even more effective if they have simplified reporting tools that work on every device that they can use to alert the security team after an attack.
- Automated remediation tools. If your users are very good at reporting threats, you’ll want to make sure that you deal with every report promptly. In a breach, every second counts. This is where automated remediation comes in. Automation ensures that every report can be investigated quickly. And it eliminates the manual tasks that slow security teams down.
- Supplier account compromise. Most security teams lack visibility into the third parties their company interacts with. This means they can react to compromised supplier accounts only after they’re notified. Often, they’re not notified at all. To stay secure, you need to proactively detect the compromised accounts of your third parties and suppliers.
Protect your Microsoft 365 environment
There is no silver bullet to stop the growing threat of cyber attacks. That’s why a layered, integrated approach to Microsoft 365 native email security is so essential for protection in today’s environment.
To learn how Proofpoint can help, see this page.










