Most threats today require humans to activate them. That’s why user awareness and knowledge are critical to reducing the risk of breaches and data loss and supporting safe email practices. Well-informed users can recognize, avoid and report suspected malicious content found in emails, texts or web links.
Frost & Sullivan recently published the Frost & Sullivan Frost RadarTM: Security Awareness Training Market, 2021 report, which analyzes the global market for security awareness training in terms of growth and innovation to help organizations select the right solution for their needs. We’re pleased to announce that Frost & Sullivan has recognized Proofpoint as a leader in security awareness training.

Figure 1. Proofpoint recognized on Frost Radar
In a field that included more than 16 global industry participants, Frost & Sullivan’s analysis gave Proofpoint the highest score in the Innovation Index and as a leader in the Growth Index.
Innovation is essential for organizations as they work to reduce risk by positively guiding behavior change, enabling users to identify the deceptive and evolving techniques of threat actors, and developing a security culture that transforms users from targets to defenders.
Innovations to reduce risk, change behavior and build a security culture
Supporting continuous and adaptive behavior change and enabling a resilient security culture requires powerful capabilities in security awareness that can meet the continuing escalation and sophistication of attacks from relentless threat actors.
Let’s review some of the key innovations identified by the Frost & Sullivan Frost Radar: Security Awareness Training Market, 2021 report:
Threat-guided training
From the Frost & Sullivan Frost Radar: “Proofpoint introduced Targeted Attack Protection (TAP) Guided Training to customers in December. This enables Proofpoint customers who utilize its Very Attacked People (VAP) visibility to dynamically train those VAPs on topics related to the threats they are being targeted with. In this way, organizations can focus on their largest exposure and reduce risk as quickly as possible.”
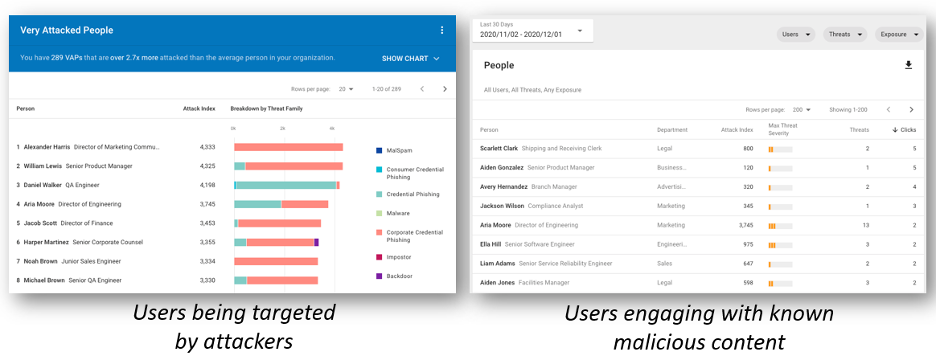
Figure 2. Proofpoint targeted attack protection
With Proofpoint Targeted Attack Protection (TAP), your administrators can focus on the areas of highest risk. And by using the market’s leading threat intelligence from Proofpoint, they can ensure maximum effectiveness. This is achieved by running a precise security awareness program with impact—a program that is based on real risk in the organization’s email environment.
Proofpoint customers with TAP can see which specific attacks their end users are receiving, and which end users are the most attacked. TAP measures volume, severity and targeting to determine the attack index. Armed with that insight, organizations can provide highly prescriptive training that helps users identify and avoid active threats.
One-touch threat reporting
From the Frost & Sullivan Frost Radar: “Similarly, the platform’s Closed-Loop Email Analysis & Response (CLEAR) feature enables end-users to report suspicious emails through the PhishAlarm button. The PhishAlarm Analyzer automatically scores reported messages, classifies messages based on risk level and removes all other malicious email instances across the organization.”
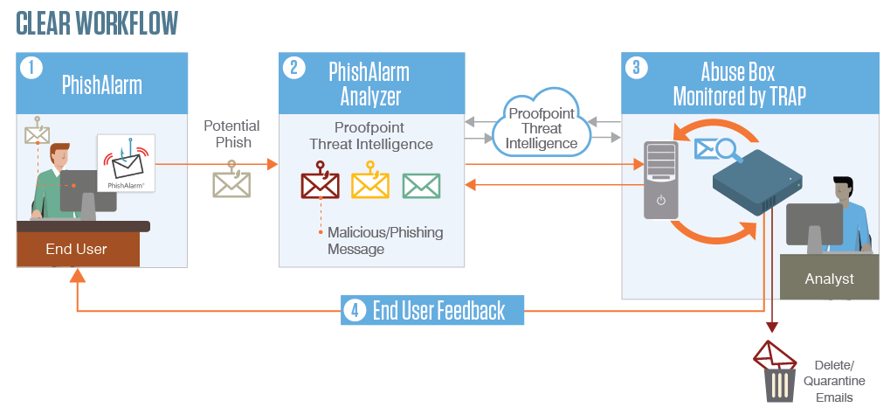
Figure 3. Proofpoint CLEAR Workflow
With the automated Closed-Loop Email Analysis and Response (CLEAR) solution from Proofpoint, reported messages are sent to the Proofpoint Threat Response Auto-Pull (TRAP). In TRAP, these messages can be automatically quarantined or closed. Or they can be sent to the incident response team for further analysis if desired.
Administrators can also set up customized response messages to users based on the message classification. These customized messages are sent back to users to reinforce behavior and help build a security-aware culture. Research shows that organizations can dramatically improve the analysis of reported emails for risk reduction and cut analysis resources by over 90%, dramatically reducing incident-response costs and time.
Continuous measurement and intelligence
From the Frost & Sullivan Frost Radar: “The CISO Dashboard provides metrics on how well an organization’s awareness program is working. And awareness program data is integrated into the Proofpoint Nexus People Risk Explore, helping security teams understand people risk.”

Figure 4. Proofpoint CISO Dashboard
The newest Proofpoint dashboard will provide chief information security officers (CISOs) with visibility into program performance and peer industry comparisons to positively affect people-centric change. The Security Awareness Training CISO Dashboard from Proofpoint allows you to assess and evaluate cultural change quickly and do deeper dives into three key areas:
- Risk intelligence: Identify your riskiest people and tailor your security program based on user behavior. The User Vulnerability Summary provides a more detailed and people-focused view of the score to drive more in-depth discussions about how to target learning. (Key performance indicator (KPI): Who are the riskiest people?)
- Behavior change and cultural scoring: Our security program score summary provides a holistic score that measures the program’s success. The score includes five areas—Training Completion, Knowledge Assessment, Simulated Threat Failure, Simulated Threat Reporting and Reported Threat Accuracy. (KPI: Behavior Change and Security Culture Measurement and Trending.)
- Industry performance: We provide trending and benchmarking information to provide an understanding of performance over time against others in comparative industries. (KPI: How effective is our security culture vs. industry peers?)
Get the report—and more!
To download the Frost & Sullivan Frost RadarTM: Security Awareness Training Market, 2021 report, visit here.
Also, be sure to check out this other content from Proofpoint:
- 2021 State of the Phish report: See our latest research on phishing trends.
- 2021 Voice of the CISO report: Get details on the key concerns of CISOs across the globe.
- Wisdom 2021: View recorded sessions from our Wisdom 2021 customer conference.










