Since March 27, 2020, Proofpoint researchers have observed an increase in video conferencing company-themed attacks seeking to steal credentials and distribute malware. These lures capitalize on the global workforce’s shift to remote work and consequential increased demand for video conferencing services during the COVID-19 pandemic.
To note, these attacks do not leverage or attack video conferencing software directly. Threat actors are using the names and brands of these video conferencing companies as themes in their social engineering lures, which lead to the theft of various account credentials, malware distribution, or credential harvesting for these spoofed video conferencing accounts.
Credential Phish: Cisco WebEx “Alert!" "Your account access will be limited!”
Key Points: This small campaign in the United States attempted to harvest WebEx users’ credentials with emails claiming that recipients need to take immediate action to address a WebEx security vulnerability. Industries targeted include technology, accounting, aerospace, energy, healthcare, telecommunications, transportation, government, and manufacturing companies.
Figure 1 Lure with Spoofed Cisco WebEx Branding Claiming Critical Vulnerability
Summary:
This is a small campaign with messages intended for technology, accounting, aerospace, energy, healthcare, telecommunications, transportation, government, and manufacturing companies in the United States.
This campaign claims to come from addresses such as:
- “cisco@webex[.]com”
- “meetings@webex[.]com”
and uses subject lines such as:
- “Critical Update!”
- “Alert!”
- “Critical Update!”, “Your account access will be limited!”
- “Your account access will be limited in 24h.”
- “Your account access will be limited!”.
The emails claim that the recipient needs to update their WebEx client to “fix” a security vulnerability in the Docker Engine Configuration in Cisco CloudCenter Orchestrator, CVE-2016-9923. The messages very prominently abuse the Cisco WebEx logo and spoof the format of Cisco’s security advisories. They also appear to draw text and images from the legitimate Cisco advisory cisco-sa-20161221-cco which was released in December 2016 and does address CVE-2016-9923.
If the recipient clicks on the link, they are taken to the page shown in Figure 2 which asks for the user’s WebEx credentials.
Figure 2 WebEx Credential Phishing Page
Credential Phish: Zoom Account
Key Points: This medium-sized campaign has targeted energy, manufacturing, and business services in the United States and is designed to steal user credentials. The message body includes a lure that claims to welcome users to their new Zoom account.
Figure 3 False Zoom Activation Lure
Summary:
Emails in this campaign arrive with a subject line of “Zoom Account” and purport to be from an admin account. In the sample in Figure 3, the message claims to come from “Rouncube Admin”. Other email lures claim to be from “admin@servewebteam[.]gq”.
The message body includes a lure that welcomes users to their new Zoom account and contains a link, which the recipient is urged to click in order to activate their Zoom account. When clicked, users are taken to a generic webmail landing page and asked to enter their credentials as shown in Figure 4.
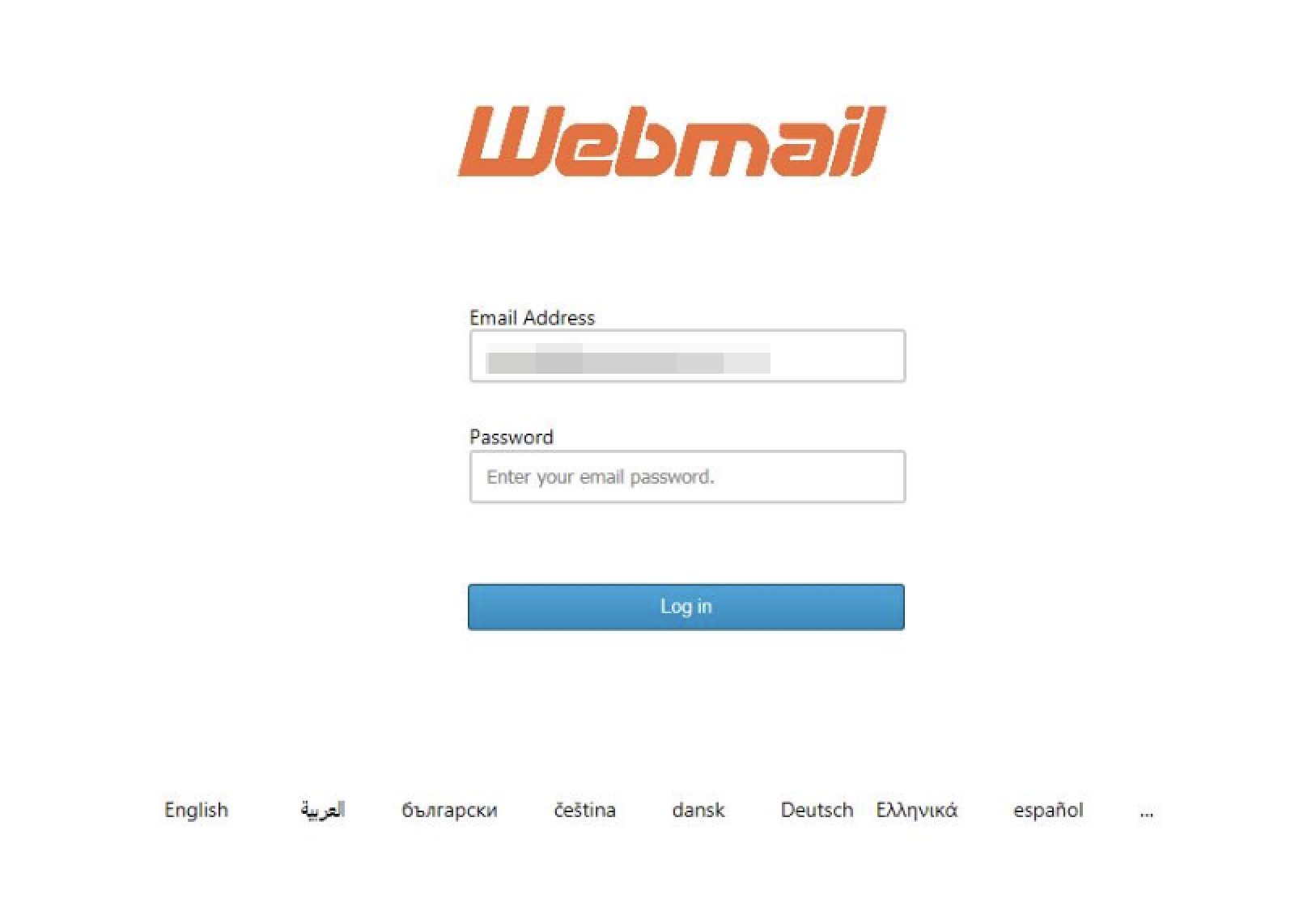
Figure 4 Generic Webmail Login for Zoom Credentials
Credential Phish: Missed Zoom Meeting
Key Points: This small campaign targets transportation, manufacturing, technology, business services, and aerospace companies in the United States and seeks to steal to user credentials using a lure around a missed meeting.
Figure 5 Missed Zoom Meeting Lure
Summary:
This small campaign targets transportation, manufacturing, technology, business services and aerospace companies in the United States. The emails arrive claiming that the recipient missed a Zoom meeting and includes a link the recipient can use to “Check your missed conference”.
If the recipient clicks on the link, they are taken to a spoofed Zoom page and asked for their Zoom credentials as shown in Figure 6
Figure 6 Missed Zoom Meeting Credential Phish Page
Malware: ServLoader/NetSupport with “[Company] Meeting cancelled - Could we do a Zoom call?”
Key Points: This small campaign targeted energy, manufacturing industrial, marketing/advertising, technology, IT and construction companies with ServLoader and the NetSupport remote access Trojans (RATs).
Figure 7 Malware Distribution Using "Zoom Call" in Message Body
Summary:
This is a malware campaign that was carried out over several days by TA4562 and seeks to distribute the ServLoader/NetSupport remote access Trojans. TA4562 has been behind ServLoader/NetSupport and Trick campaigns in the past.
The message thanks the recipient for their response to a fake RFQ (Request for Quotation), includes an attachment that purports to be about that discussion, and offers to have a call via Zoom.
This campaign uses subject lines that include:
- “[Company] Meeting cancelled - Could we do a Zoom call”
- “[Company] - I won't make it to Arizona - Could we talk over Zoom?”
- “The [Company] - I won't make it to Tennessee - Can we talk over Zoom?”
- “The [Company] Meeting cancelled - Should we talk over Zoom?” where the subject line includes the correct name of the recipient’s company.
Of particular, note, we observed one sample sent to the help desk of a large agricultural firm.
If the recipient opens the attachment, they are prompted to enable macros as shown in Figure 8.
Figure 8 Prompt to Enable Macros
Once enabled, those macros execute a ServLoader PowerShell script which in turn will install the NetSupport a legitimate remote-control application that threat actors abuse. If installed, NetSupport can access any files and information on the compromised system that the user can, including usernames, passwords, and credit card information.
Conclusion
As video teleconferencing has become more important than ever to the global workforce, it’s not surprising that attackers are moving to adapt their themes and lures to include prominent video conferencing providers like WebEx and Zoom. With more and more organizations shifting to remote work, we can expect these video teleconferencing brands to continue to be used as themes in social engineering lures for the foreseeable future.











