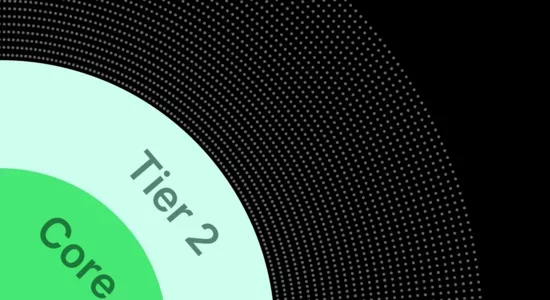
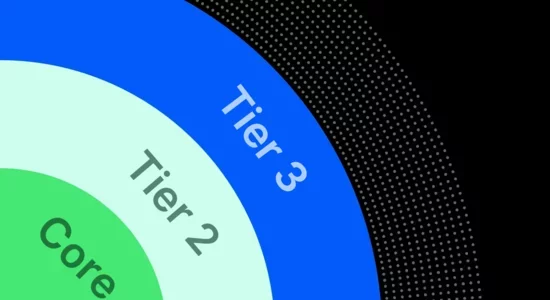
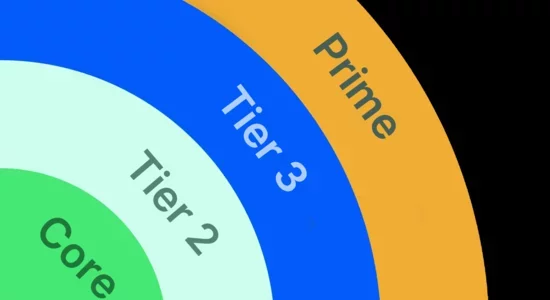
Core
업계 최고 수준의 이메일 보안
Proofpoint Core Email Protection
비교
솔루션을 비교하여 팀에 적합한 솔루션 찾기
이메일 보안 솔루션을 찾고 계십니까? Proofpoint Core Email Protection을 확인해 보십시오.
| 주요 특징 및 기능 | Core | Tier 2 | Tier 3 | Prime |
|---|---|---|---|---|
| 업계 최고 수준의 이메일 보안 |
Yes
|
Yes
|
Yes
|
Yes
|
| 계정 탈취로부터 방어 |
Yes
|
Yes
|
Yes
|
|
| 손상된 공급업체 계정으로부터 방어 |
Yes
|
Yes
|
Yes
|
|
| 보안 메시징 도구(예: Teams, Slack) |
Yes
|
Yes
|
Yes
|
|
| 자동화된 위협 안내 교육 제공 |
Yes
|
Yes
|
||
| 위협을 즉각적 시뮬레이션으로 변환 |
Yes
|
Yes
|
||
| 도메인 사기 및 스푸핑 방지 |
Yes
|
|||
| 호스팅된 서비스(DMARC, DKIM, SPF)로 인증 간소화 |
Yes
|
|||
| 유사 도메인 탐지 및 수정 |
Yes
|
|||
| 보안 응용 프로그램 생성 이메일 |
Yes
|
견적 요청
Proofpoint Prime을 통해 완벽한 협업 보안
FAQ
FAQ
저는 기존 고객입니다. 기존 요금제가 새 솔루션에 어떻게 반영되나요?
Proofpoint는 기존 고객이 사용 중인 솔루션을 갱신하는 것을 존중합니다. 이러한 솔루션에는 재정적으로 도움이 될 수 있는 특별 할인과 추가 기능이 내장되어 있습니다. Proofpoint 계정 팀과 상의하여 조직의 요구 사항에 가장 적합한 솔루션을 결정하십시오.
솔루션 가격은 어떻게 책정되나요?
Proofpoint 솔루션은 고객에 맞게 가치를 최적화하도록 설계되었습니다. 즉, 가능한 가장 효과적이고 포괄적인 솔루션을 지속 가능한 가격으로 제공합니다. 예산 가격은 사용자 라이선스 수와 계약 기간(1년 또는 다년 계약)에 따라 달라질 수 있습니다. 사용량에 따른 예외가 있으므로 Proofpoint 계정 팀과 요구 사항에 대해 논의하십시오.
조직에 어떤 솔루션이 적합한지 어떻게 알 수 있나요?
Proofpoint에 문의하십시오. 대화를 통해 조직의 기준, 과제, 문화, 예산에 대해 자세히 알아보고 결정을 도와드리겠습니다.