画一的なセキュリティ意識向上プログラムの時代はもはや過去のものです。プルーフポイントのState of the Phishレポートによると、組織の98%以上がセキュリティ意識向上プログラムを導入しています。しかしながら、ユーザーの68%が、リスクがあることを知りながらもリスクのある行動を取っていると回答しています。
まだプルーフポイントをご利用でない方々から日々耳にするフラストレーションを思えば、このような数字もうなずけます。こうした組織は、継続的な教育プログラムを実施しているものの、ユーザーの行動を望ましい方向へと改善するのに苦労しているようです。組織が直面している主な課題のいくつかは以下のとおりです。
- 組織に最大のリスクをもたらしているのが誰なのかがわからない
- どのようなポリシー、脅威、脆弱性についてユーザーを教育すべきなのか、臨機応変に決められない
- プログラムを維持するのに、ユーザーグループの更新やカリキュラムの調整が継続的に必要であり、リソースに大きな負担がかかる
これらの問題は、従来のセキュリティ意識向上の枠を超えた、包括的な人的リスク管理プログラム構築の必要性を浮かび上がらせています。
最初に取り組むべきは、頻繁に標的にされているユーザーグループにフォーカスすることです。組織内のほとんどのセキュリティ問題の要因となっているのは、多くの場合こうしたユーザーです。こうしたユーザー固有のニーズに合わせて教育プログラムを調整することができれば、個々の脆弱性を緩和することができます。また、今後ありうる攻撃に対して全体の防御を強化することもできます。
プルーフポイントが提供する新しいワークフローは、こうしたユーザーにフォーカスし、全体的なリスクを大幅に低減させるものです。この記事では、人的リスク管理にフォーカスすることがなぜ重要なのかを見ていきます。また、組織がこれを実現するためにプルーフポイントがどうお役に立つかをお伝えします。
人的リスク管理とは
人的リスク管理は、サイバー攻撃の防止と対応を自動化する既存のセキュリティ ベストプラクティスを基盤として構築される、「人」を中心に据えた管理手法です。人的リスク管理ソリューションの基本は、特定の環境内において、複数のセキュリティツールにまたがってユーザーイベントやアイデンティティ アクティビティを取り込むことができる機能です。このソリューションが追跡するものは以下のとおりです。
- 攻撃リスク:ユーザーが攻撃される可能性
- 脆弱性リスク:攻撃が成功する可能性
- 権限リスク:攻撃が組織にもたらしうる損害
続いて、このソリューションは個人の総合リスクスコアを定量化します。こうした知見により、企業やセキュリティチームは以下のことが可能になります。
- 主な標的にされている個人またはグループを可視化し、最善の保護を提供するための戦略を優先化
- リスクのある行動を即座に防ぐために技術的な制御を介入させるか、ユーザーにリスクとその回避方法を助言する文脈的な気づきを提供する
- リスクのあるユーザーを、ユーザーに合わせて調整された教育カリキュラムに自動的に参加させ、ユーザー自身と企業を今後のサイバー攻撃から守れるようサポート
- ユーザーの行動改善状況を簡単に追跡し、ポジティブなセキュリティ文化を育成
Proofpoint Security Awareness 内の新しい Adaptive Threat and User-Risk Response Workflow(脅威&ユーザーリスク適応型対応ワークフロー)は、こうした問題に対処するために設計されています。一言で言うと、この新しいワークフローには、プルーフポイントのあらゆる長所がつまっています。
Adaptive Threat and User-Risk Response Workflow
この新しいワークフローには3つの主要機能が統合されています。これにより、以下が可能になります。
- アダプティブグループを使用し、Proofpoint NPRE (Nexus People Risk Explorer)とProofpoint TAP (Targeted Attack Protection)から作成されたユーザーリスク プロファイルとグループに基づいて、ユーザーグループを動的に作成および管理
- プルーフポイント独自の脅威調査により追跡され、TAPにより報告された、定義済み脅威ファミリーに基づく脅威ベースの教育カリキュラムを作成
- 事前に作成されたアダプティブグループの対象となるユーザーが確認されたら、その新しいユーザーをカリキュラムに自動的に参加させる、適応型課題を構築
この適応型学習アプローチにより、頻繁に標的にされているグループに対する教育が優先的に行われます。ここでは、管理者は、こうしたユーザーに最も関連性の高い脅威やリスクに合わせてカリキュラムを調整できるため、ユーザー エンゲージメントを最大化することもできます。
これは、脅威やユーザーリスクを定量化し、詳細に可視化することで実現されます。これらの知見を使用して、頻繁に標的にされているグループ向けの教育を調整することができます。
脅威とユーザーリスクを定量化する
プルーフポイントのユーザーリスク グループとプロファイルは、この新しいワークフローの中核にあるものです。これには、NPREとTAPで提供されている、Imminent Target(緊急の標的)とVery Attacked People™のグループが含まれます。
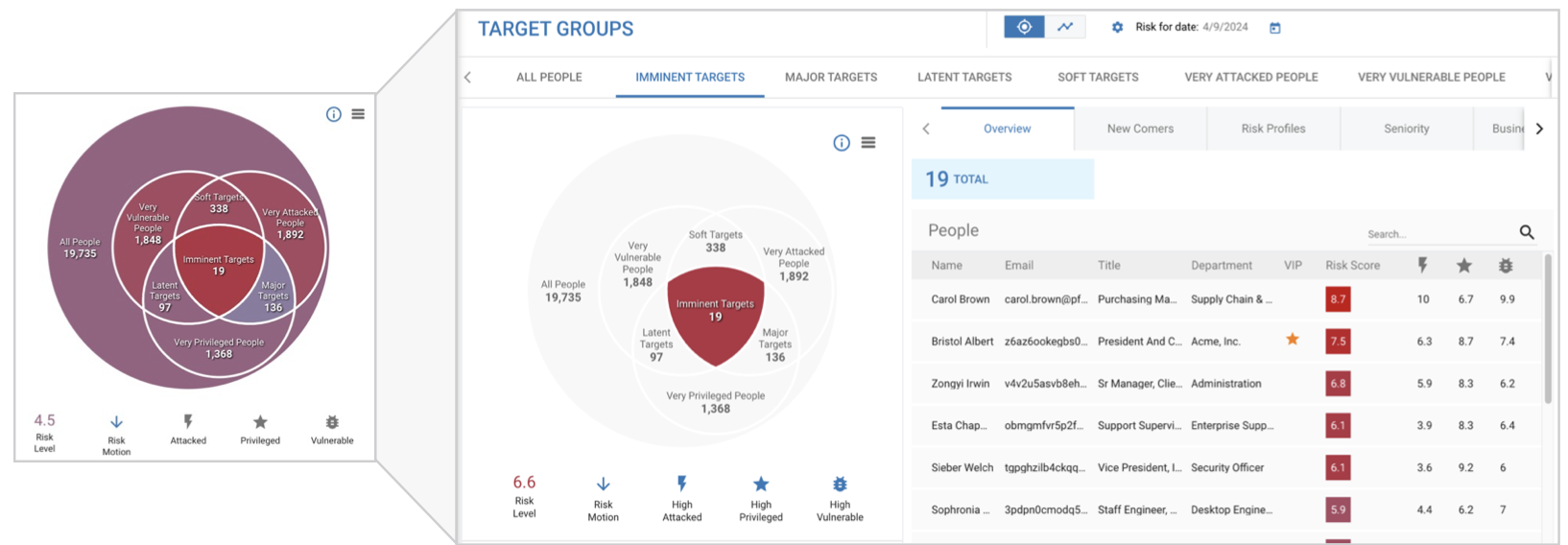
NPREユーザーリスク グループの例
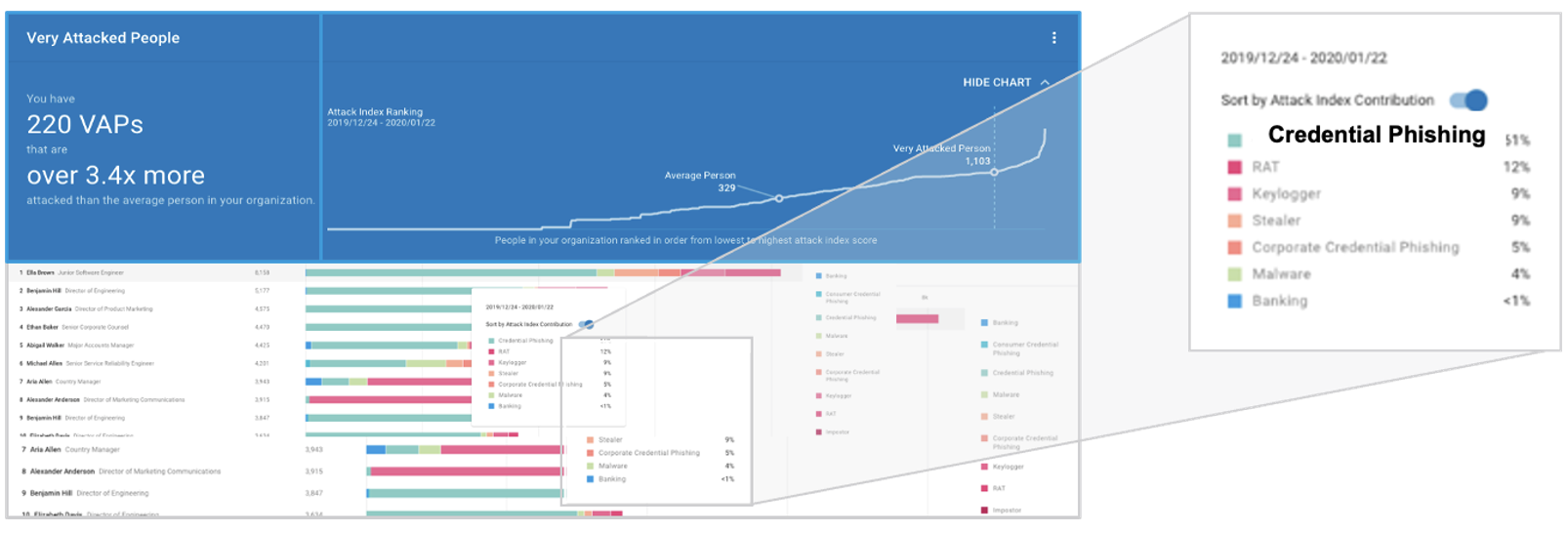
Very Attacked People™と脅威ファミリーの例
NPREとTAPは、以下のような複数の要素を組み合わせています。
Attack RiskとAttack Index
これらの指標は、ユーザーグループがサイバー攻撃によって標的にされる可能性を評価するものです。リスクプロファイルを構成する要素には、以下などが含まれます。
- メッセージ攻撃件数
- 攻撃のタイプ
- 攻撃者の巧妙さ
- 攻撃の多様性
- 攻撃標的の拡散と集中
脆弱性リスク
この指標は、ユーザーへの攻撃が成功する可能性を評価するものです。これは、ユーザーとグループに関する以下の情報を考慮します。
- セキュリティ教育への参加
- フィッシング テスト パフォーマンス
- サードパーティ アプリ認証要求
- シャドーITの使用
- 一貫性のないユーザー位置情報
- URLクリック操作
- 配布リストのメンバー属性
- クラウドアカウント侵害
- 内部リスクアラート
- リスクのあるデータの取り扱い
権限リスク
この指標は、攻撃がもたらしうる潜在的な損害を評価するものです。これは、以下のようなユーザーの特性を考慮します。
- ユーザーディレクトリ/部門/グループ/個人のアイデンティティ権限
- カスタマー定義の特権グループ
- 高度な権限をもつアイデンティティ(例:ドメイン管理者)
- Tier-Zeroエンタイトルメント(重要資産)への高リスク攻撃パスをもつユーザー
これらの要素を分析することにより、企業は、最もリスクの高い個人とグループに対し、教育面とセキュリティ制御面での戦略を優先化することができます。
高リスクグループに向けて教育を調整する
NPREとTAPが提供する可視性により、管理者は、対象のグループ向けに教育を調整することができます。管理者は、グループが最も受けやすい脆弱性または脅威を中心としたカリキュラムを提供できます。
例えば、「最もクリック数の多いユーザー」リスクグループとして、リスクの高いグループ向けに教育を調整することができます。このようなグループ内で、管理者は、「広告詐欺」や「バンキング型トロイの木馬」といった、グループを標的にするために広く使用されている脅威を可視化できます。
こうした情報とProofpoint Security Awareness統合を使用して、管理者は以下のことが可能です。
1. Proofpoint Security Awareness内でアダプティブ グループを構築:このグループは、「最もクリック数の多いユーザー」ユーザーリスク グループや、標的にされるユーザーに対し用いられている「広告詐欺」、「バンキング」、「バックドア」などの上位の脅威に直接関連するものです。
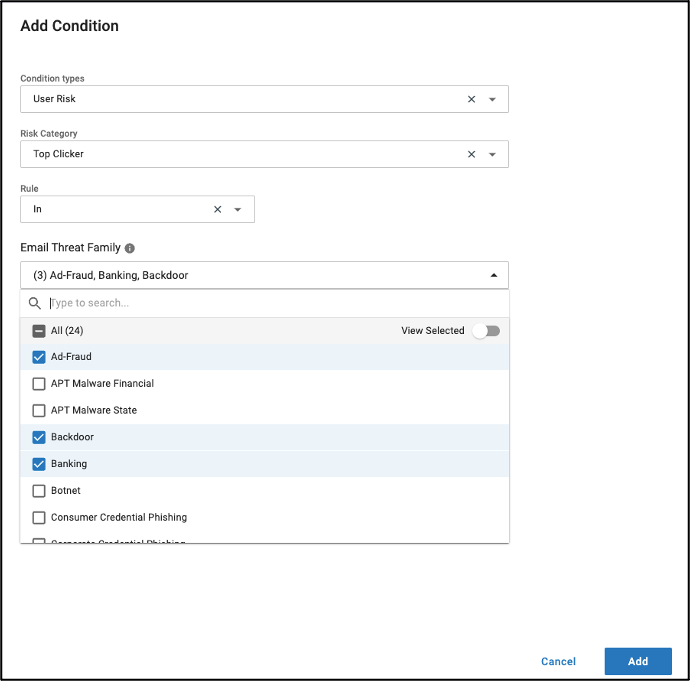
「ユーザーリスク」と「脅威ファミリー」の条件を指定したアダプティブグループの構成
2. コンテンツ検索が簡単:コンテンツライブラリには、TAPが追跡する脅威ファミリーに基づいて、事前に作成された検索フィルタが含まれます。
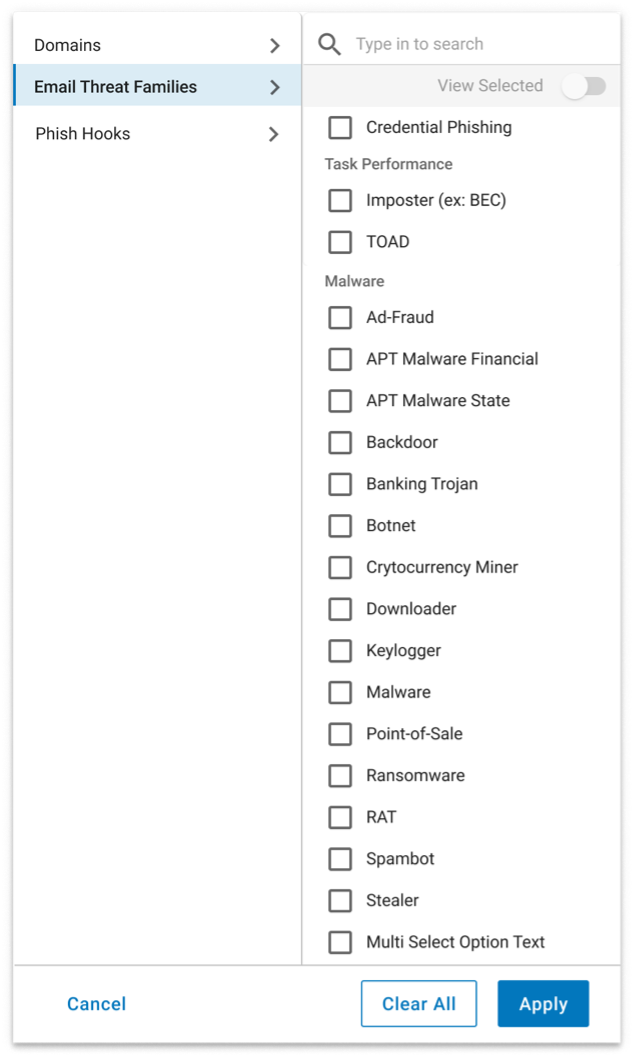
「脅威ファミリー」のコンテンツライブラリ検索フィルタの例
3. 課題を迅速に作成:ボタンのクリック操作で、特定の教育モジュールや前述の脅威に関連した課題を調整することができます。
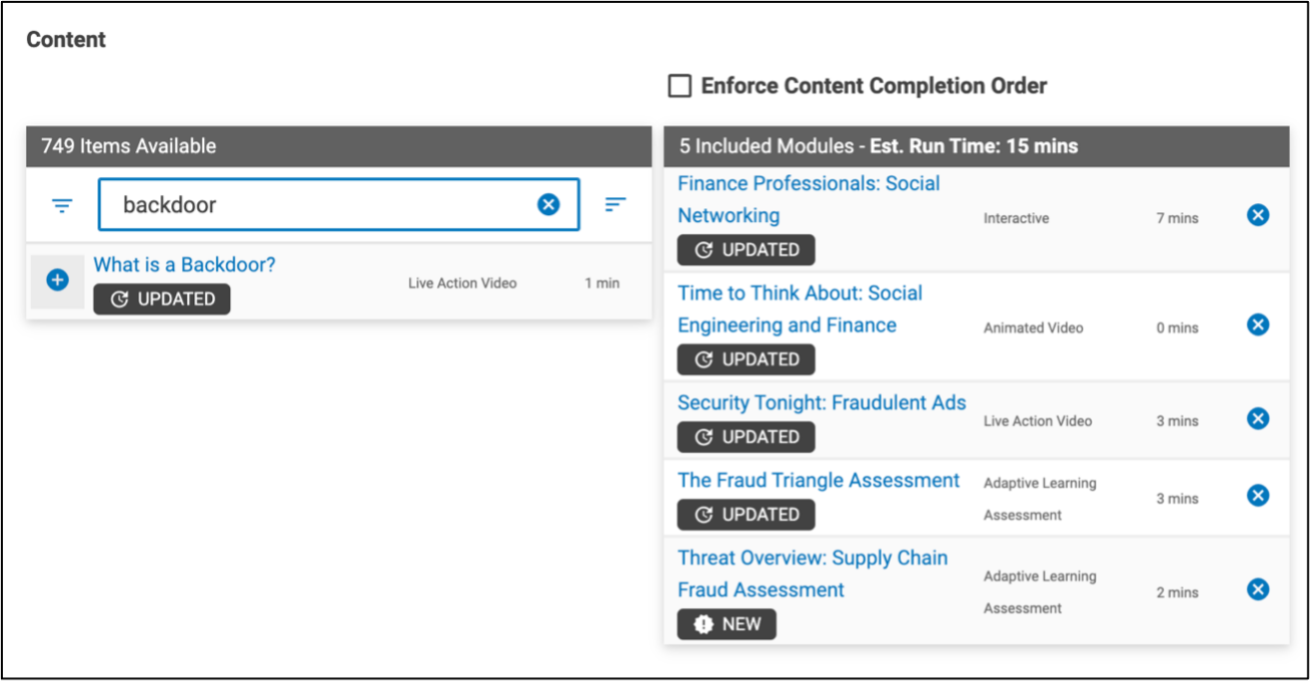
課題作成の概要
4. 新たなグループメンバーとして自動的に参加:この機能により、「最もクリック数の多いユーザー」になったユーザーや、「広告詐欺」、「バンキング」、「バックドア」の脅威によって標的にされたユーザーは、事前作成済みの課題に自動的に追加されます。
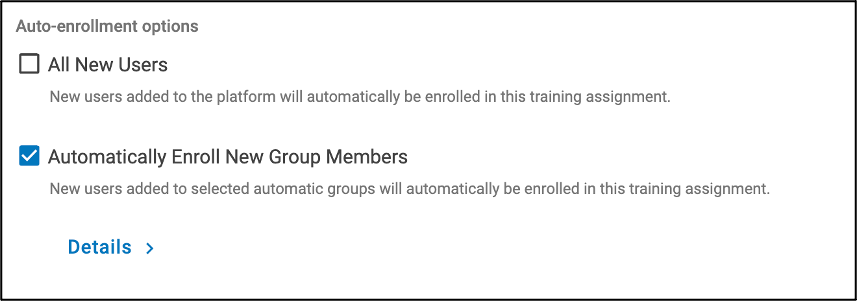
課題に新しいユーザーを自動追加するオプション
的を絞ったアプローチのメリット
Adaptive Threat and User-Risk Response Workflowは画期的なワークフローです。これにより、以下が可能となります。
- リソースに優先順位をつける:最も脆弱性の高いグループに最初にフォーカスすることで、トレーニング リソースをより効果的に割り当てることができます。
- エンゲージメントと能力の最大化する:最も関連性の高い教育をユーザーに提供できれば、ユーザーは脅威の特定に役立つ知識と能力を身につけることができます。
- プロアクティブな防御の考え方を促進する:教育によって向上したユーザーは、不審なメールやアクティビティをただ無視するのではなく報告する可能性が高くなります。
- 測定可能なリスク低減を実現する:高リスクグループに的を絞ることで、組織は、攻撃が発生する可能性を大幅に低減することができます。
人的リスクに対する戦いにおける大きな進歩
Proofpoint Security AwarenessのAdaptive Threat and User-Risk Response Workflowにより、企業内の頻繁に標的にされているユーザーグループを詳細に可視化することができます。さらに、包括的なリスクスコアと、ユーザーを標的にしている脅威の種類に基づいて調整された教育を提供することができます。これにより、画一的なセキュリティ意識向上モデルから抜け出し、機能する人的リスク管理プログラムを構築する機会が得られます。
Proofpoint Security Awarenessにより、脅威の一歩先を行き、人のファイアウォールを強化することができます。プルーフポイントのソリューションについて詳しくはぜひお問い合わせください。










