プルーフポイントのCybersecurity Stop of the Monthにようこそ。この新しいブログシリーズでは、現在のサイバー犯罪者の進化し続ける戦術を探っていきます。また、特にメール脅威の分野における偵察活動と最初の侵害といった、攻撃チェーンにおける重要な最初の段階にも焦点を当てます。
このシリーズの目的は、防御を強化する方法を理解できるようサポートすることです。これにより、今日のダイナミックなデジタル世界において新しい脅威に対し保護することができます。

攻撃チェーンの最初の2つの段階:偵察と最初の侵害
前回の記事では、BECとサプライチェーン攻撃について説明しました。今回の記事では、EvilProxyとして知られる陰湿な脅威について見ていきます。
シナリオ
プルーフポイントが最近行ったメール脅威アセスメントにおいて、1,500社の顧客を抱えるテクノロジー企業が、EvilProxyに侵害されていることを発見しました。既存のメールセキュリティ ソリューションでは、この脅威を検知できていませんでした。
EvilProxyとは何でしょうか?EvilProxyは、認証情報と多要素認証(MFA)トークンを盗む能力をもつフィッシング ツールキットです。ターゲットと正規のWebページの間に入り込んで攻撃を仕掛けます。
被害者がフィッシングページに接続すると、実際のログインポータルと同じ外観で、同じように動作する、偽のログインページが表示されます。EvilProxyはユーザーの認証情報と認証セッショントークンを盗みます。攻撃者は続いてMFA保護を回避しながら、ユーザーの代わりにログインします。
脅威:攻撃はどのように起こったのか?
この攻撃がどのように展開されたか詳しく見ていきましょう。
1. 偽のメッセージ:攻撃は、文書の署名を求める正規のDocuSignによる通知のように見えるメールで始まりました。この一見無害なメッセージは、実は巧妙なサイバー攻撃への入口でした。
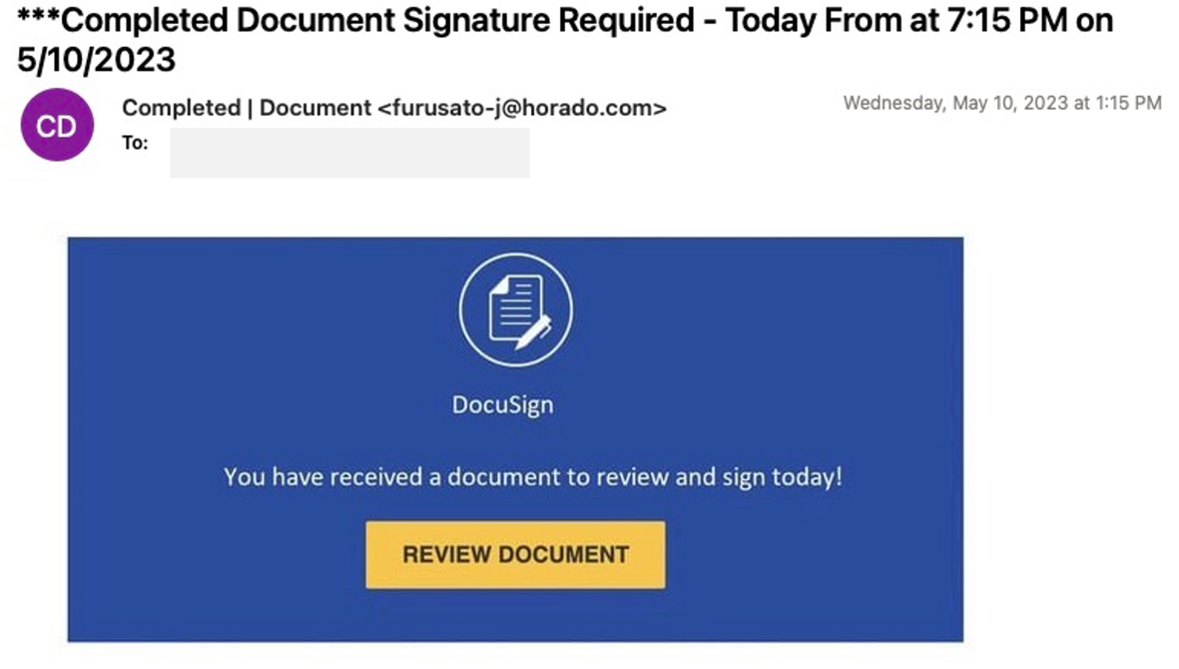
顧客が受け取った最初の偽メール
2. 悪意のあるURL:被害者がメールに記載されたURLをクリックすると、被害者のMicrosoftログインページに誘導されますが、その背後には攻撃者のプロキシが設定されていました。このページで攻撃者は、ユーザーが騙されて自ら認証情報を入力してしまうことをねらっていました。
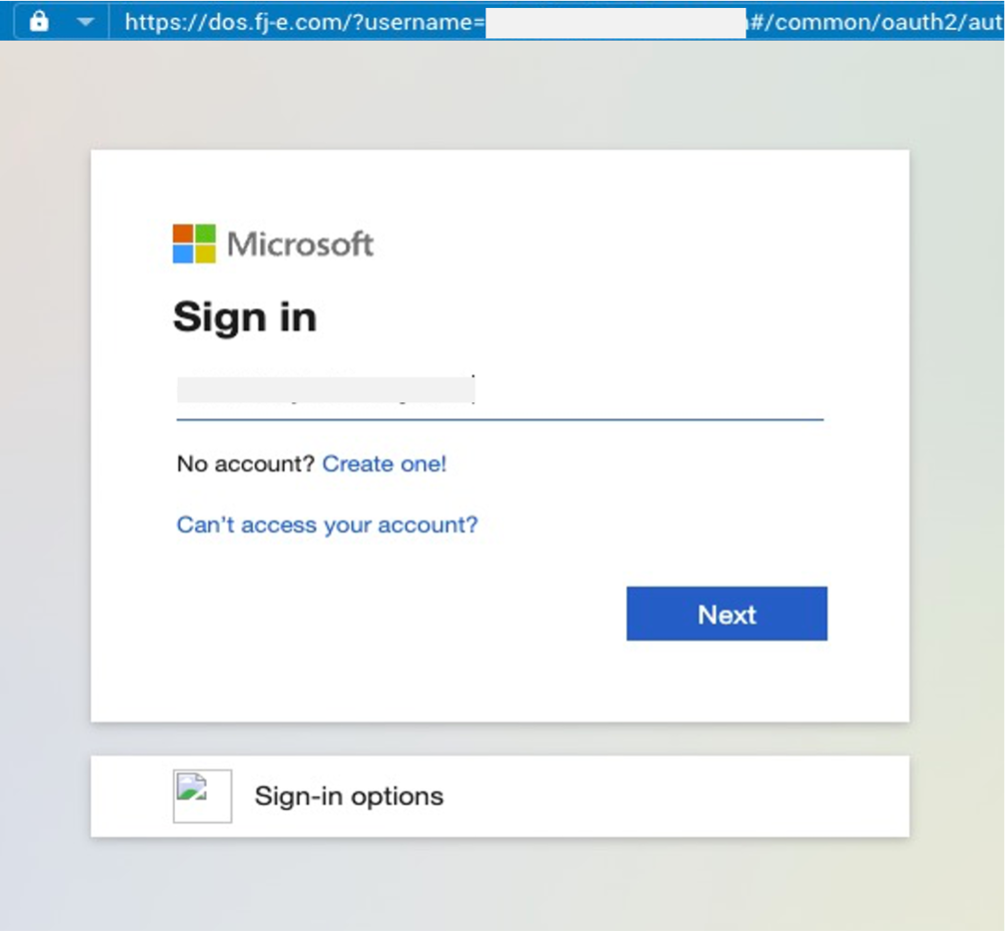
悪意のあるMicrosoftサインインページ
3. EvilProxyフィッシング フレームワーク:この攻撃の原動力はEvilProxyフィッシング フレームワークでした。攻撃者はリバースプロキシの手法を使用し、本物のMicrosoftサインインページでのユーザーのログイン試行を傍受しました。このようにしてひそかにMFAコードとユーザー認証情報を抜き取ったのです。
4. MFAによる認証の弱体化:MFAコードとログイン認証情報を手に入れた攻撃者は、その侵害したアカウントに自由にアクセスできるようになりました。MFAによる確認を回避することで完全にコントロールすることができます。つまり、このテクノロジー企業と1,500社のエンドユーザーにとって重大な脅威となったのです。
検知:プルーフポイントのソリューションでどのように攻撃を検知できたか?
攻撃者が強化されたセキュリティ制御にも対応できるようになっていることから、EvilProxyや、MFAを回避するその他の脅威はますます使用されるようになっています。IPアドレスまたはURLのレピュテーションといった従来の方法では、こうした脅威を十分に阻止できません。
プルーフポイントは高度な機械学習を使用し、認証情報のフィッシング攻撃でしばしば見られる行動やメッセージの特性を特定することができます。また、メッセージをサンドボックス解析して詳細に調査することにより、悪意のあるURLリダイレクトパターンやEvilProxyフレームワークに焦点を当てることができます。
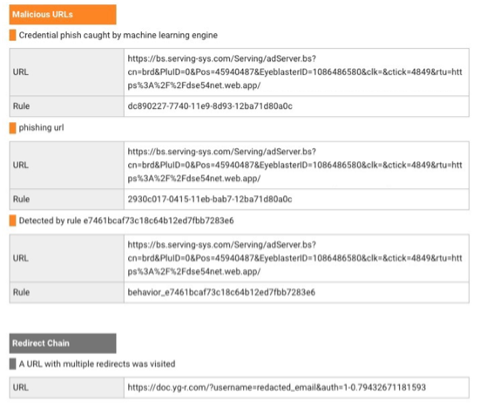
プルーフポイントでの悪意のあるURLの検知とリダイレクトチェーン
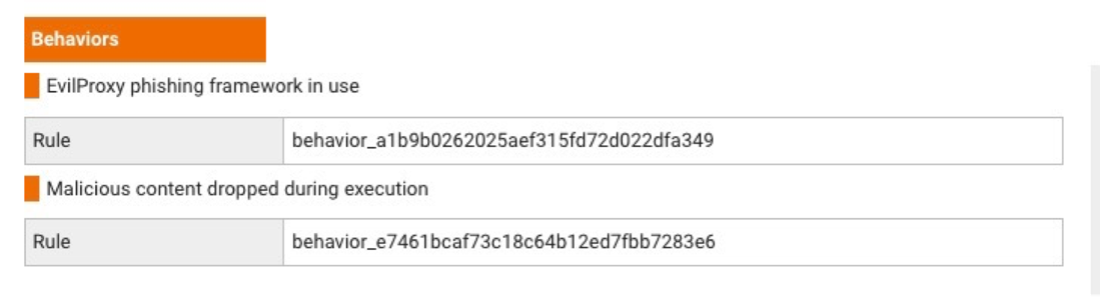
プルーフポイントでのEvilProxyフィッシング フレームワークの検知
対処:教訓は?
EvilProxyなどの脅威から保護するために、以下などのプロアクティブな対策を実装することが重要です。
- ユーザー教育:従業員はサイバー攻撃に対する最後の砦となりえます。偽のメールやログインページなど、あらゆるフィッシング攻撃に関するセキュリティ意識向上トレーニングを提供しましょう。これにより被害にあう可能性を大きく減らすことができます。
- 堅牢なメールセキュリティ:高度なメールセキュリティ ソリューションは、ユーザーの受信箱に届く前にフィッシング攻撃を検知し、阻止することができます。プルーフポイントの脅威検知プラットフォームのような、機械学習を使用してこうした脅威を検知し、阻止するソリューションがおすすめです。
- クラウドセキュリティ:優れたクラウドセキュリティ プラットフォームは、アカウント乗っ取り(ATO)攻撃を特定し、機密のクラウドリソースへの許可されていないアクセスを防止することができます。これは最初の侵害および侵害後の活動にも対応します。また、これによりセキュリティチームは、攻撃者によって悪用されているサービスやアプリケーションについて詳しく確認することができます。対処を自動化するソリューションがおすすめです。これにより攻撃者の滞在時間を減らし、被害を最小限に抑えることができます。
- サプライチェーンの保護:メールに起因する攻撃からサプライチェーンを保護します。Proofpoint Supplier Threat Protectionは高度なAIと最新の脅威インテリジェンスを使用し、侵害されたサプライヤーアカウントを検知し、調査が必要なアカウントを優先させます。
- 多要素認証(MFA):MFAのような強力な認証技術により、セキュリティ体制を大幅に向上させることができます。しかし、先ほど紹介したシナリオのように、従来のMFAソリューションではあまり効果がないことにご注意ください。そのため、このようなインシデントを速やかに修復できる、クラウドのATO自動化ツールを使用することが重要です。
- 継続的な脅威アセスメント:注意を怠らず、新たな脅威の監視を続ける必要があります。定期的な脅威アセスメントにより、企業の脆弱性を特定し、インシデント対応機能を強化することができます。
Proofpoint TAP Account Takeoverによる防護
Proofpoint TAP ATO (Account Takeover)により、プルーフポイントのProofpoint TAP (Targeted Attack Protection)ソリューションの高度な脅威検知機能を拡大しています。人工知能、相関脅威インテリジェンス、振る舞い分析を使用して以下を検知し、自動的に修復します。
- 侵害されたアカウント
- 悪意のあるメールボックスのルール変更
- サードパーティ アプリの承認
- サイバー犯罪者による機密ファイルの過度な共有
Proofpoint TAP ATOは、さまざまな修復オプションで滞在時間を減らすことができます。イベントを関連付け、攻撃シーケンス全体を把握することにより、迅速な対応を行います。攻撃者はユーザーのアカウントにアクセスするためにさまざまな方法を探し続けるため、適時の対応が不可欠です。例をいくつかご紹介します。
- EvilProxyのようなMFAをバイパスする脅威
- パスワード スタッフィング
- データ侵害
- 総当たり攻撃
- 永続的なアクセストークン
Proofpoint TAP ATOなら、チームは悪意のあるアクティビティを調査し、速やかに脅威に対処することができます。これにより企業へのリスクを抑えることができます。
プルーフポイントで攻撃チェーンを断ち切る
EvilProxyの脅威から、堅牢なサイバーセキュリティ対策を備えることが重要であることがわかります。今日の巧妙なサイバー脅威を阻止できるのは、常に注意を払い、企業と顧客を保護するべくプロアクティブな防御を導入する企業だけです。その他の重要なステップとして、最先端の技術を導入し、プルーフポイントのような信頼できるサイバーセキュリティ パートナーと連携することがあげられます。
このブログシリーズでは、継続的に最新脅威の説明や、プルーフポイントの検知方法の紹介などを行っています。プルーフポイントは、攻撃チェーンに焦点を当てることにより、攻撃チェーンを断ち切り、企業がこれらの新しい脅威に対しプロアクティブに防御できるようサポートすることに努めています。
常に最新情報を入手し、保護し、先手を打つ
EvilProxyなどの脅威から保護する方法については、プルーフポイントのe-book、メール セキュリティ戦略ガイドをダウンロードしてください。
●あわせて読みたい











