Verizon Data Breach Investigations Report (年 Verizon データ侵害調査レポート)によると、侵害の 85% には何らかのヒューマンエラーが関係しています。E メールは依然として、「人」の脆弱性を狙うPeople-Centric な攻撃において最上位の脅威ベクトルとなっています。また、ランサムウェア、ビジネスメール詐欺 (BEC)、メール詐欺は、組織に何百万ドルもの損害を与えています。
では、このように急速に高度化しつつある危険な脅威に対して、どのような最善策があるでしょうか?その答えは、Gartner が最近公開した「2021 Market Guide for Email Security」レポートで取り上げた内容にあります。このガイドで、Gartner は、セキュリティにかかわるリーダーがメール セキュリティ ソリューションを選定する際に検討すべき機能の包括的なリストを提供しています。
プルーフポイントのメール セキュリティソリューションを利用して、充実した対策がどのように可能になるのか、以下で説明します。
プルーフポイントは、Gartner が言及している機能に対応できると自負しています。
メール セキュリティは、ケーキのように何重もの層で構成する必要があります
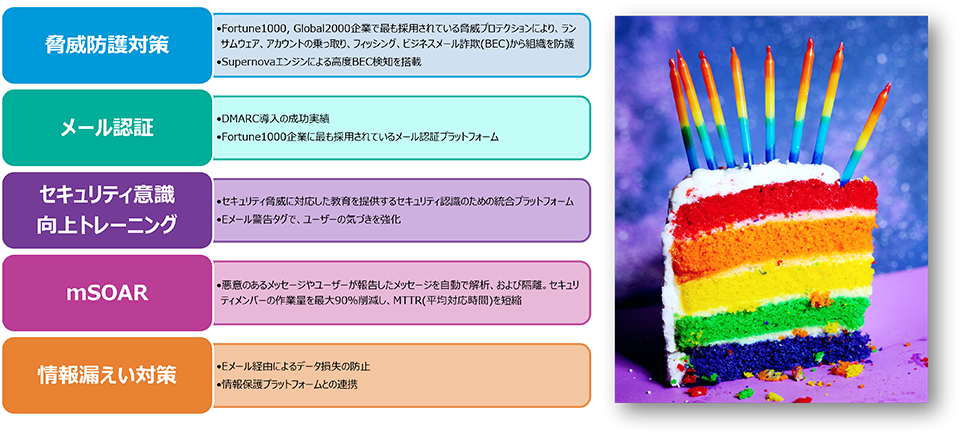
図 1:最新の「Gartner Market Guide for Email Security」で概説されている 5 つのおもな要件
メール セキュリティにおいてもっとも重要な第 1 の側面は、効果を発揮するために複数の層が必要であるということです。現在の脅威状況を 1 つの層や 1 つの製品で解決できると期待する時代は終わりました。以下は、現在の市場におけるメール セキュリティの定義について、Gartner が言及した内容です。
「メール セキュリティは、ゲートウェイ、メールシステム、ユーザー行動、コンテンツ セキュリティに加え、サポートのためのさまざまなプロセス、サービス、およびその周辺のセキュリティ アーキテクチャにまで及びます。効果的なメール セキュリティを実現するには、必要な機能や構成を備えた適格な製品を選択するだけでなく、適切な運用手順を導入することも求められます。」
プルーフポイントもこの考え方に同意しています。だからこそ、運用上の成果を改善し、リスクを低減するとともに、People-Centric な脅威に対する高い可視性をお客様に提供するための統合的な多層アプローチを構築してきたのです。
Gartner の「マーケット・ガイド」で述べられたメール セキュリティに関する要件を詳しく考察し、プルーフポイントがどのようにして Gartner の推奨事項を実現しているのかを確認しましょう。
その 1:BEC および従来の脅威に対抗する高度な保護策
実行が容易で、かつ、悪意のあるペイロードが埋め込まれないため一般的に検知が難しいという理由から、ビジネスメール詐欺(BEC) 攻撃が急増しています。毎月、 プルーフポイントは数百万もの BEC 攻撃が顧客に届くのを阻止しています。
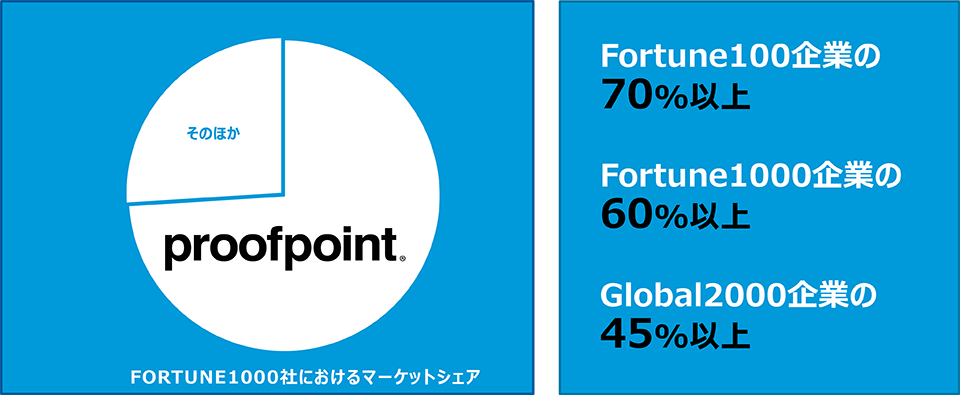
図 2:プルーフポイントはもっとも信頼されているベンダーであり、Fortune 100、Fortune 1000、および Global 2000 にランクインする多くの企業で採用されているマーケットリーダーです。
メール セキュリティ向けの高度な脅威対策において、プルーフポイントを信頼する Fortune 100、Fortune 1000、および Global 2000 企業が増加しているのには理由があります。Proofpoint Nexus Threat Graph は、E メール、クラウド、ネットワーク、ドメイン、ソーシャルメディア、ユーザー、および、総勢 100 名を超える脅威インテリジェンス チームからの 1 兆を超えるデータポイントを組み合わせたもので、プルーフポイントの実績ある効果と能力を引き出すことにより、新たな脅威に迅速に対処します。
Gartner は、各組織に以下のように呼びかけています。
「会話履歴を分析して異常を検知する BEC 対策や、E メール内の不審なリンクを分析するコンピュータビジョンでは、マシンラーニング および AI ベースのフィッシング対策技術を駆使したメール セキュリティ ソリューションを探す必要があります。」
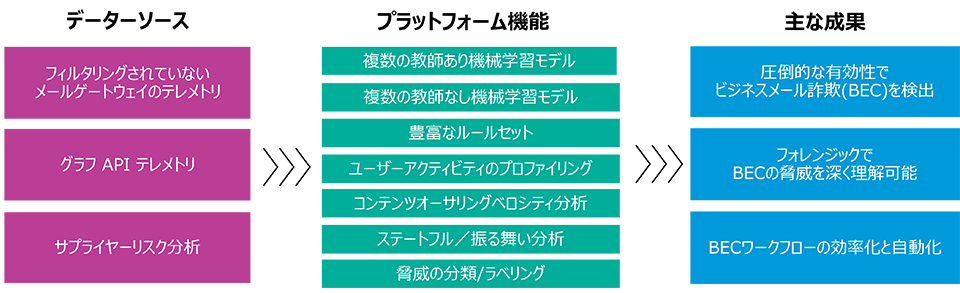
図 3:BEC 攻撃の阻止に有用なプルーフポイントのプラットフォーム機能
プルーフポイントは、大規模なNexusAI 検知エンジンの一部として、20 年以上にわたり、機械学習 (ML) アルゴリズムの改良を続けています。2021 年の早い段階で、Supernova と名づけたまったく新しい検知プラットフォームを用いた Advanced BEC Defense を立ち上げました。送受信ゲートウェイ テレメトリ、サプライチェーン リスク分析、そして Microsoft 365 や Google Workspace をはじめとするクラウド生産性プラットフォームからの API データを活用するこの機能なら、非常に高度なメール詐欺の攻撃も的確に発見できます。なお、この機能はプルーフポイントの高度なメール セキュリティのライセンスすべてに含まれています。
機械学習や人工知能 (AI) が業界の流行語的存在である一方で、本当に重要なのは言葉によるマーケティングよりも効果を示す結果の方です。メール セキュリティのマーケットリーダーであるプルーフポイントの比類なき分析により、より多くのデータが得られ、より高い効果につながります。多くのメール セキュリティ ソリューションとは異なり、プルーフポイントは、BEC の検知で低い誤検知率を実現しており、チームがメッセージを選別し、そのメッセージが実際に悪意のあるものであるかどうかを判断するのに余計な時間を費やさないようにしています。
しかし、プルーフポイントが阻止する攻撃は BEC だけではありません。高度なサンドボックスを用いて、未知の添付ファイルや URL を検査します。攻撃者はよく知られたサービスを利用して検知を回避する手法を使うようになってきており、中でも正規のファイル共有サービスの悪用が増加していることが確認されているため、すべてのファイル共有 URL を予測的にサンドボックス解析を実施しています。プルーフポイントの調査によると、配信された悪意のある URL のうち、半数以上が Microsoft (OneDrive、SharePoint など) からのものでした。
プルーフポイントは、単に添付ファイル (その中の URL を含む) だけでなく、パスワードで保護されている添付ファイルも検査します。また、URL の書き換えや、クリック時に分析をおこなうことにより、あらゆるネットワークやデバイス上のユーザーを保護します。これにより、配信後に悪意をもって起動するコンテンツによるリスクを低減することができます。
その 2:世界中の多くの組織が信頼する DMARC 認証
重要な防御層である認証は、BEC 攻撃を阻止し、組織のブランドを保護し、さらには、一見して見分けのつかない類似ドメインなどからの攻撃を阻止するための情報を提供できるようサポートします。
Gartner は、各組織に次の必要性を訴えています。「DMARC を実装し、ドメインのなりすまし攻撃に対抗できる必要があります。」また、次の指摘もしています。
「DMARC により、従業員、パートナー、顧客を標的とするまったく同じ名前のドメインのなりすましを阻止することはできますが、組織内のドメインのサイズや数によっては難しくなる可能性があります。DMARC の実装や継続的監視の支援には、プロフェッショナル サービスが必要となることが少なくありません。」
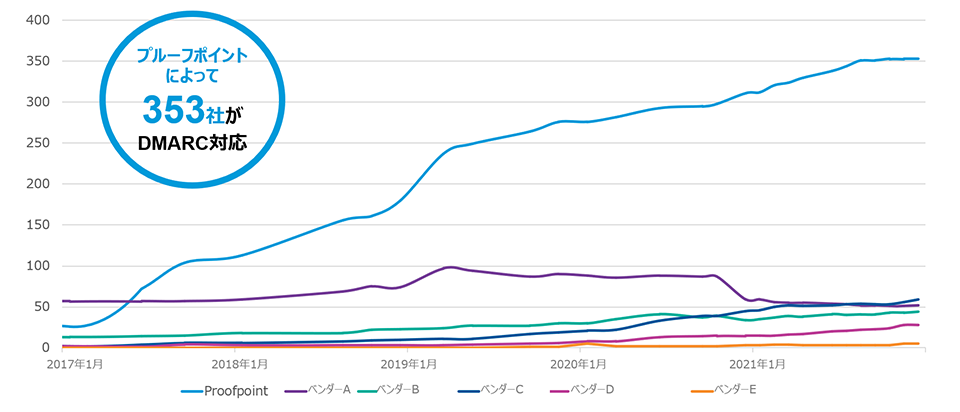
図 4:さまざまなベンダーによる DMARC の実装を示すグラフ
プルーフポイントは、他のどのベンダーよりも多くの Fortune 1000 企業に DMARC を実装しており、高度な構成を実現するのに必要な専門知識を備えています。
しかしながら、組織が DMARC を実装したからといって、これで終わりというわけではありません。
その 3:統合されたセキュリティ意識向上トレーニング
またGartner は、「マーケット・ガイド」の中で、統合されたセキュリティ意識向上トレーニングの概念について、次のように説明しています。
「セキュリティ意識向上トレーニングの強化に役立つ、コンテキスト認識バナーも含んだ製品を検討してください。また、ユーザー教育に投資するとともに、一般的になりすまし攻撃の標的となる財務および機密データ トランザクションに関する標準的な運用手順を導入しましょう。」
プルーフポイントは、標的型攻撃に対抗するためのユーザー教育に関して、業界の最先端を行きます。プルーフポイントのメール セキュリティ ソリューションは、セキュリティ意識向上トレーニングと密接に関連づけられており、次のように、標的を絞った効果的な教育を提供することができます。
- Proofpoint TAP (Targeted Attack Protection) Guided Training の統合により、その組織で最も狙われている重要人物であるVery Attacked People™ や実際に悪意あるメールの影響を受けているユーザーを、関連のある教育に自動登録することができます。
- プルーフポイントのコンテンツは、プルーフポイントの脅威インテリジェンスに基づいており、幅広いコンテンツ ライブラリの中で、標準的な運用手順に対するおとりや攻撃、そして本格的な攻撃キャンペーンの傾向を把握できます。
- プルーフポイントのセキュリティ意識向上トレーニング ソリューションでは、Proofpoint Nexus Threat Graph と自社の脅威検知スタックが使用され、ユーザーから報告されたメッセージを得点化し、ユーザーによる報告の正確性に関する情報を確認できます。
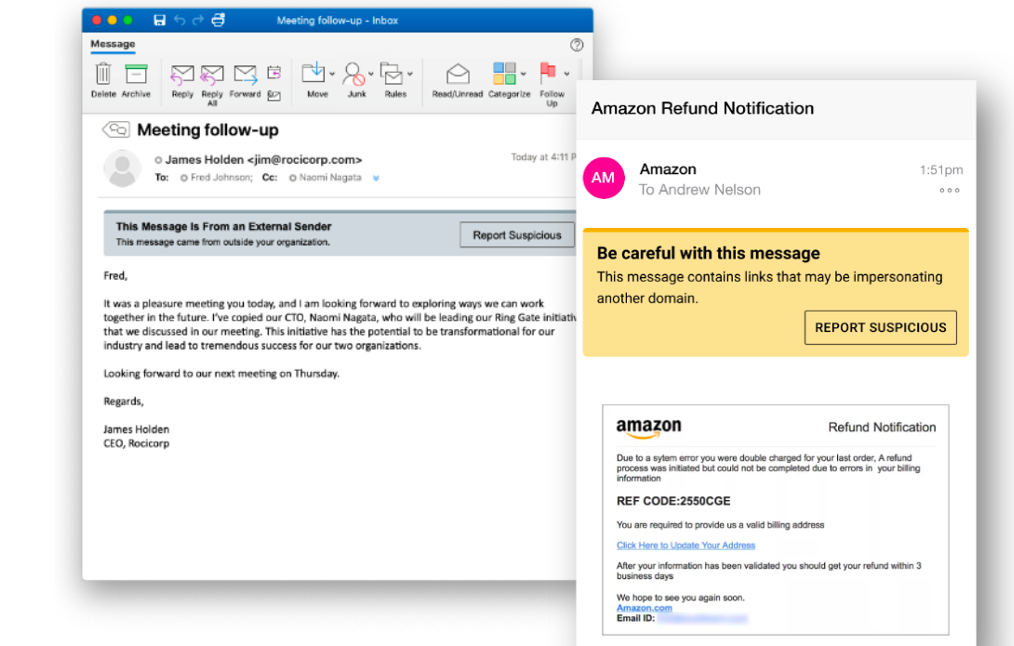
図 5:不審なメールであることを報告できる機能を備えた、HTML ベースのプルーフポイント メール警告タグにより、組織の意識を向上させるとともに、メール セキュリティ体制を改善することが可能
また、メール セキュリティ サービスをご利用のすべてのお客様の E メールには、不審なメールであることを報告できる機能を備えた、コンテキスト、および HTML ベースのメール警告タグが表示されるようになるため、ユーザーはデバイスに関係なく、危険性の高い E メールに関するコンテキストを入手し、簡単に報告することができます。ユーザーがメッセージを報告すると、プルーフポイントは、チームに与える運用上の影響を低減するための強力なメール セキュリティ オーケストレーションおよび対応をおこなう一方、ユーザーにフィードバックをおこなうことにより、「正しく報告されたことを確認」し、報告されたメッセージの種類を通知します。
その 4:業務を劇的に改善する強力な自動化機能を備えた mSOAR
プルーフポイントの mSOAR ソリューションである Proofpoint TRAP (Threat Response Auto-Pull) には、主に以下の 2 つのユースケースがあります。
- 受信後に特定された E メールや武器化された E メールを自動的に削除
- ユーザーから報告されたメッセージを修復
Gartner は「マーケット・ガイド」の中で、mSOAR ツールについて以下のように述べています。
「E メールを自動的に再分類し、受信トレイから削除するのをサポートする mSOAR ツールにより、ユーザーから報告された E メールが処理されるようになります。これにより、報告された E メールの処理は簡素化されますが、修復は依然として、ただでさえ忙殺されている IT セキュリティ チームへの負担となる可能性があります。」
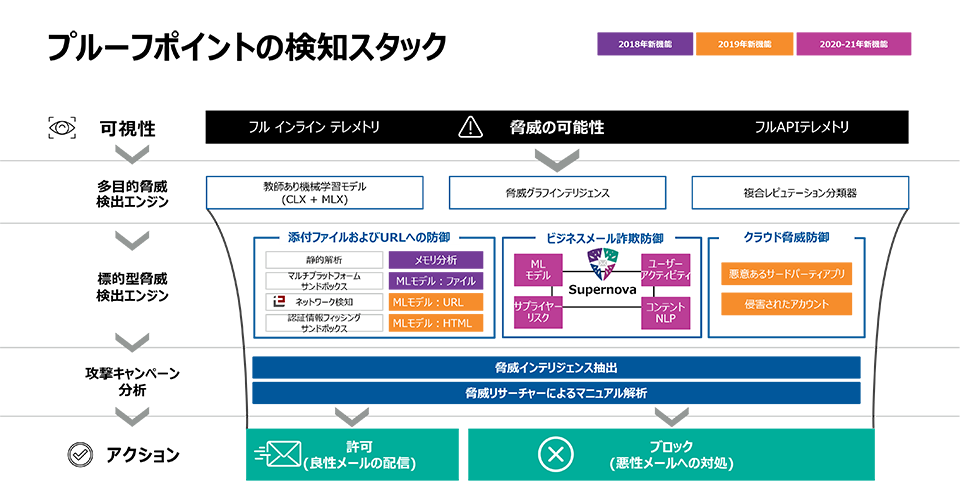
図 6: インシデント レスポンス時間の大幅カットを実現する、プルーフポイントによるメール セキュリティ向け検知アンサンブルの概要
IT セキュリティ チームの負担を軽減するため、プルーフポイントでは、Proofpoint Nexus Threat Graph において業界をリードするデータベースと、自社の高度な検知スタックを活用しており、上記のユースケースでは、最大 90% 負担を軽減しています。
メッセージがこの検知アンサンブルをすべて通過したあとは、隔離 (転送されたメールや類似のメッセージを含む)、ケースクローズ、さらには、Okta、SailPoint、CrowdStrike、Palo Alto Networks、VMware Carbon Black といったテクノロジー パートナーと統合されたワークフローなど、次のアクションがアクティブ化され、業務を効率化できます。
この自動化により、内部リソースためのコストを数千ドル削減することができます。それを実現した、ある医療機関における例を このホワイトペーパーでぜひご覧ください。
その 5:Proofpoint Information Protection プラットフォームの一部である Proofpoint Email DLP
プルーフポイントではよく、次のような表現を使っています。「データがひとりで勝手に流出したりはしない」。メールデータの保護が、メール セキュリティや情報保護の決定的な要素であるといくら強調してもしすぎることはありません。
今日では、メールデータの保護はかつてないほど重要になっています。Gartner は「マーケット・ガイド」で以下のように述べています。
「パートナーや顧客と E メールで共有した機密データを保護、追跡できることに加え、編集できる可能性もあることは、とくに制定が相次ぐ規制やプライバシー法などを踏まえると、きわめて重要になっていると言えます。また、E メールも、とくに偶発的なデータ損失のように、データ侵害のもっとも一般的な原因であり続けています。」
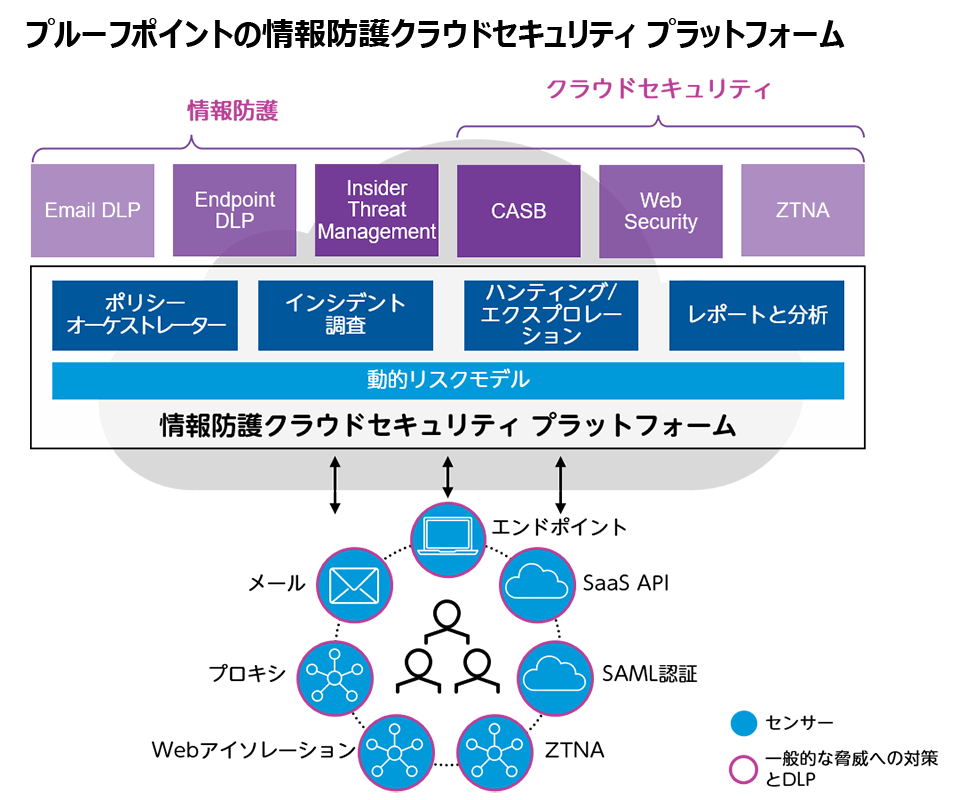
図 7:Proofpoint Information and Cloud Security プラットフォームの完全版では、組織の People-Centric なリスクを低減する強力な機能を提供します。
プルーフポイントの情報セキュリティ プラットフォームの完全版である Proofpoint Email DLP (Data Loss Prevention) および Email Encryption ソリューションは、おもなユースケースとしてきわめて有益であり、情報保護を向上するための最初のステップとなっています。プルーフポイントのサービスは、以下を可能にします。
- メール セキュリティ プラットフォームでメール DLP と暗号化を一元的に管理し実行
- さらに一歩踏み込んでProofpoint Information Protection プラットフォームの完全版に統合すれば、最新アーキテクチャにより、内部脅威、クラウド セキュリティ、コンテンツの検査などに対応でき、コンテキストに基づく People-Centric な可視化が可能になります。
5 つの主要なユースケースを取り上げたところで、どうすればお客様のチームがセキュリティ体制におけるこの重要な要素を管理できるのか、簡単に取り上げることにしましょう。
プルーフポイントのメール セキュリティ向けマネージド サービスを導入すれば、さらに充実した対策が可能に
世界中の情報セキュリティ部門は、人員の不足と確保の問題を抱えています。Proofpoint Managed Services for Email Securityを利用すれば、最高のサービスと、メール セキュリティ ソリューションの組み合わせにより、防御システムを最適化できるだけでなく、優先サポートを受けることができます。まさにビジネスの成功を保証するものです。
プルーフポイントが継続して関与することにより、組織はリスクを低減できるとともに、比類なき可視性を手に入れることができます。また、スタッフは業務にもっとも関連する脅威やその他の重要なプロジェクトだけに集中することができます。
ぜひGartner のレポートをダウンロードし、メール セキュリティ ソリューションを選定する際に検討すべきことについて詳しくご覧ください。
Gartner, Market Guide for Email Security (E メールセキュリティに関するマーケットガイド), Mark Harris, Peter Firstbrook, 2021 年 10 月 7 日
Gartner は、調査報告で特定のベンダー、製品やサービスについて特別に言及することはありません。また、もっとも評価の高いベンダーを選択するように推奨することもありません。Gartner の調査報告は Gartner の調査部門の見解をまとめたものであり、必ずしも客観的な事実を反映しているとは限りません。Gartner は、本調査の内容に対して、明示または黙示を問わず、特定の状況あるいは環境に対する正確性および適合性を一切保証いたしません。
以下の免責事項を追加してください。GARTNER は、米国および全世界における Gartner, Inc. および/またはその関連会社の登録商標およびサービスマークであり、Gartner, Inc. の許可を得て使用されています。All rights reserved.
※本ブログの情報は、英語による原文「2021 Gartner® Market Guide for Email Security: Proofpoint Lets You Have Your Cake and Eat It, Too」の翻訳です。英語原文との間で内容の齟齬がある場合には、英語原文が優先します。