Whether you’re just getting started with DMARC or have reached p=reject, it’s important to remember that DMARC is a journey and getting your policy in place doesn’t mean your journey is over.
But before we get into that, let’s take a moment to reflect on the path of getting to reject.
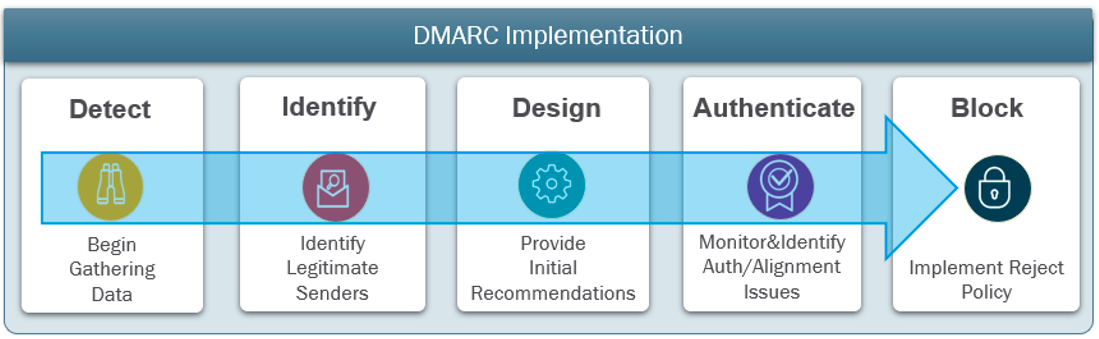
Figure 1. Overview of the DMARC implementation process.
Key aspects of the DMARC process
Your DMARC to-do list should include the following activities:
- Identifying all your domains: Starting the DMARC journey can be daunting, especially if you have many domains or if it’s unclear which domains you’re trying to protect.
- Identifying all legitimate senders: Another key activity during the discovery phase is to identify all your legitimate senders to ensure they’re not blocked later in the process.
- Identify applications and devices sending email: A potentially overlooked source of messages are multifunction printers and software applications, whether they’re internal (on-premises or in the cloud) or from your third-party software-as-as-service (SaaS) partners sending on your behalf. These transactional messages may require special consideration and enhanced support such as adding DKIM signing and security controls.
- Fix the authentication of legitimate senders: Getting your house in order is critical. Find and validate all the good senders and make decisions on the rest. Hosted authentication can help expedite the authentication process and simplify maintenance.
- Publish DMARC policy: Part of the validation process, stepping through the levels from None to Quarantine to Reject, with the goal of being at p=reject.
Maintenance and optimization
Once reject is achieved, part of your DMARC journey shifts to maintaining an optimized system. That means having visibility into changes that occur over time—for example, due to business growth or events like mergers and acquisitions.
Maintenance also includes keeping your SPF record clean and up to date. Manually adding IP addresses to a DNS record is ripe for human error, especially if you support SaaS providers in your framework. Breaking an SPF record could lead DMARC-enabled recipients rejecting legitimate emails.
Another important aspect is the proper rotation of DKIM keys. Regular key rotation can reduce the risk of compromise and help ensure your domain isn’t vulnerable. Much like maintaining your SPF record, it’s best to avoid manual copying and pasting into DNS to avoid errors.
Hosted authentication services can help simplify both tasks above.
Once your policy is in place, ensuring security compliance and governance are ongoing activities required to keep your solution operating as intended.
Expansion
Expand your DMARC journey by building out the layers of your overall identity protection:
Strengthen your gateway: Updating your own DMARC policies and enforcing them at your email gateway helps protect against impostors.
- Proactive monitoring for lookalikes: Proactive monitoring for lookalike domains helps identify them quickly. And using tools like Virtual Takedown from Proofpoint can help block them.
- Reduce your supplier risk: An increasingly frequent tactic in business email compromise (BEC) attacks is the use of supplier identities, via spoofed or compromised supplier accounts. Your DMARC journey should therefore include a strategy for evaluating and monitoring your suppliers’ risk profiles.
- Increase protection and open rates: Once your DMARC policy is in place, you can authenticate your marketing email to build trust with your customers though BIMI (Brand Indicators for Message Identification). With BIMI enabled, customers will see your logo next to emails sent by you. That, in turn, increases open rates by clearly marking your email as legitimate.
DMARC is a great step toward protecting your brand—and reaching a policy of reject is a major milestone. But keep in mind that maintaining and expanding your protection is equally important.
Learn more about how Proofpoint Email Fraud Defense can help and visit our DMARC Creation Wizard to check your DMARC, SPF and BIMI status.










