WHY PROOFPOINT
Choose the trusted leader in cybersecurity to protect your people, data, and AI
Proofpoint’s human and agent-centric security platform secures how people, data and AI agents connect across email, cloud and collaboration tools.
See the Proofpoint difference
Superior protection for every organization
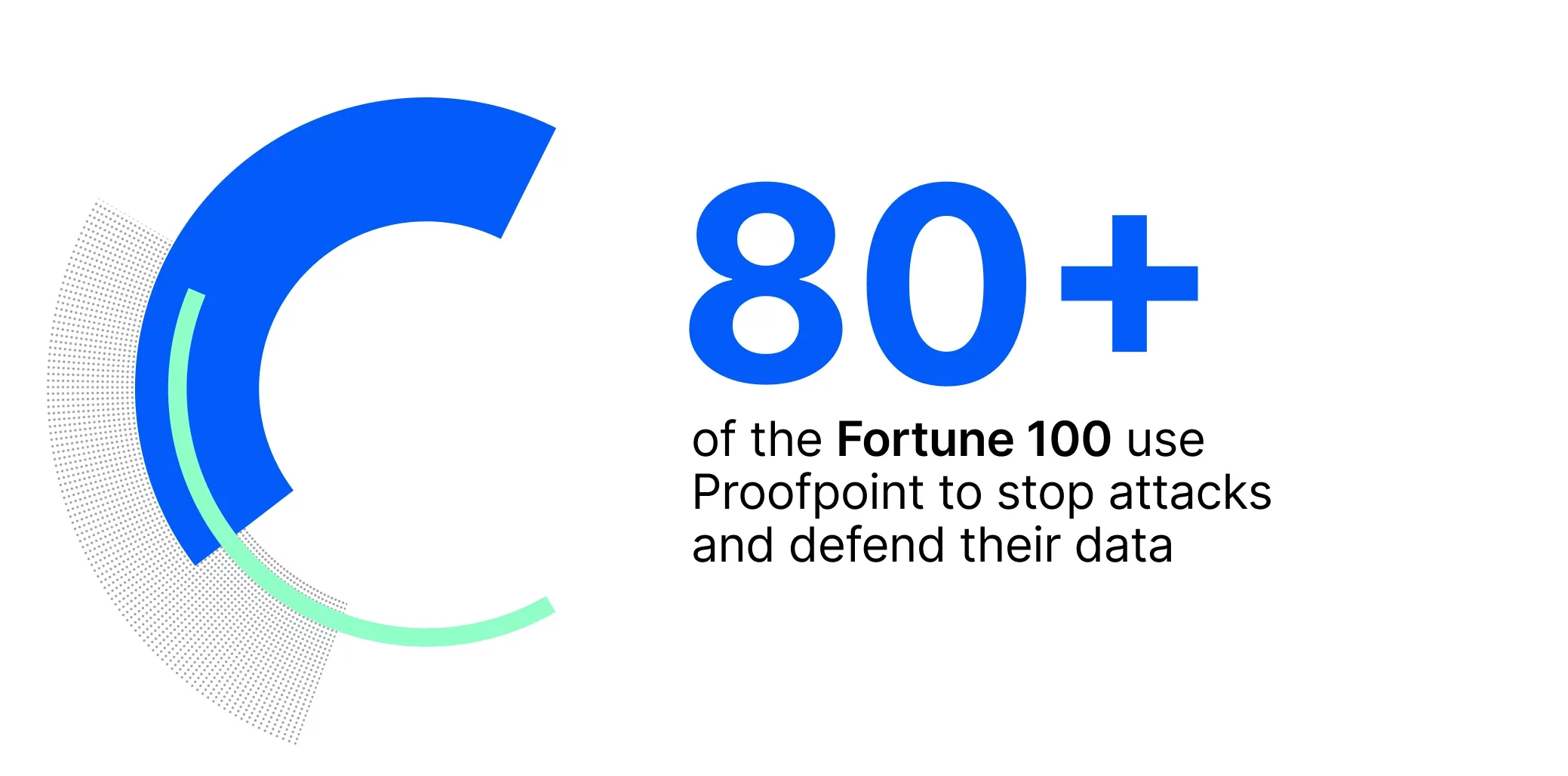
Proofpoint is a trusted partner to 80+ of the Fortune 100, more than 10,000 large enterprises, and millions of smaller organizations, chosen to stop threats, prevent data loss, and build resilience across modern collaboration.
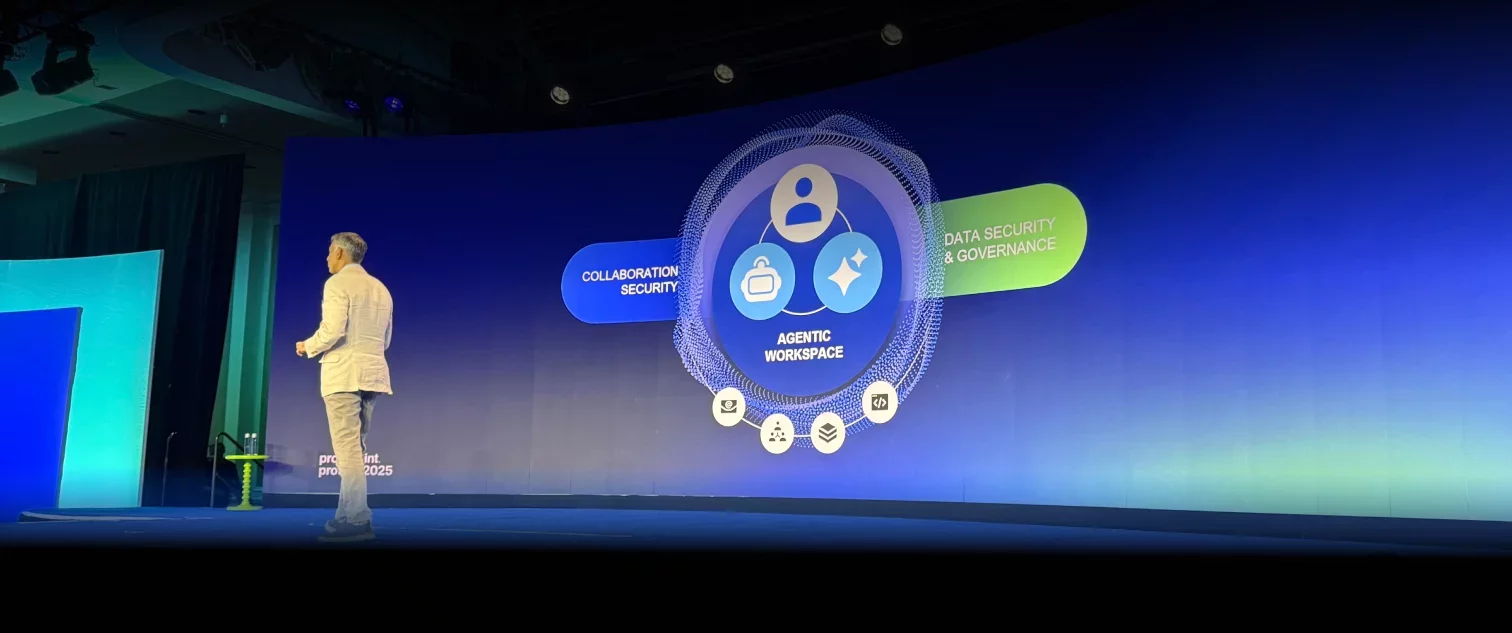
Innovative security to protect the agentic workspace
People remain the leading source of cybersecurity incidents and today, AI agents amplify that risk at machine speed, creating new paths for error, data loss and compliance failures.
Proofpoint always protected people and now, our human and agent-centric security platform extends protection to every interaction across people, data, and AI agents. We deliver control, compliance and the freedom to innovate without compromise. With Proofpoint, security leaders can move fast, and move securely to unleash the full potential for their organization.

Top reasons customers choose Proofpoint
Relentless at stopping threats others miss
Our solutions stop 99.999% of email and cloud threats, and eliminate data leakage by humans, agents and public GenAI sites with precision accuracy.
Innovation that never stops
Decades of leadership in AI-based detection and automation, now made even more powerful with Proofpoint Satori™.
Unmatched visibility backed by global intelligence
No other vendor has a global intelligence platform that spans email, cloud and collaboration tools. We analyze more than 100 billion data points every day and 3.4 trillion emails every year—giving you crucial visibility and insights to stop advanced threats.
Trusted everywhere and loved by customers
Trusted by thousands of reviewers worldwide, earning leadership status on Gartner, G2 and TrustRadius for security excellence.
Seamless integration
Integrate with leading ecosystem partners including Microsoft, Google, CrowdStrike, SentinelOne and more.
Maximum ROI
Reduce complexity and cost with an integrated solution that achieves 237% ROI and more than $6.1M in risk alleviation.
Proven outcomes and recognized leadership
Consistently top-rated in email security, data security and compliance, earning leadership in nearly every major analyst ranking.
What our customers say
LEADER
|
CUSTOMER'S CHOICE
|
LEADER
|
|
LEADER, OUTPERFORMER
|
LEADER, FAST MOVER
|
TOP PLAYER
|
|
Leader
|
|
What comes next? Unleash the full potential of your organization
Request a demo
Learn how our integrated platform helps you:
-
Stop cyberattacks
-
Prevent data loss
-
Reduce human risk across your environment
















