In October 2017, the Department of Homeland Security announced Binding Operational Directive (BOD) 18-01 to increase security for people who receive email from federal agencies or visit a federal website. As part of this mandate, all civilian federal agencies are required to deploy SPF and DMARC email authentication protocols within 12 months and have been given deadlines to achieve specific milestones along the way. Today, January 16, marks the first major milestone where agencies must have a DMARC record published for their trusted domains in monitor mode, or ‘p=none’.
DMARC prevents email spoofing by validating the true identity of the sender, but fully enforcing the protocol can be difficult to achieve because there is risk of blocking legitimate email. Given the work that goes into a DMARC implementation project, the timelines set by the DHS are aggressive.
After the announcement of BOD 18-01, Proofpoint conducted extensive research regarding the state of email fraud across federal, state, and local government agencies and found that 1 out of every 8 .gov emails was fraudulent. Clearly the mandate set by the DHS is a step in the right direction, but where do the agencies stand at the first deadline, 90 days into BOD 18-01? Our researchers look at DMARC adoption rates for each of the civilian federal agencies under the directive.
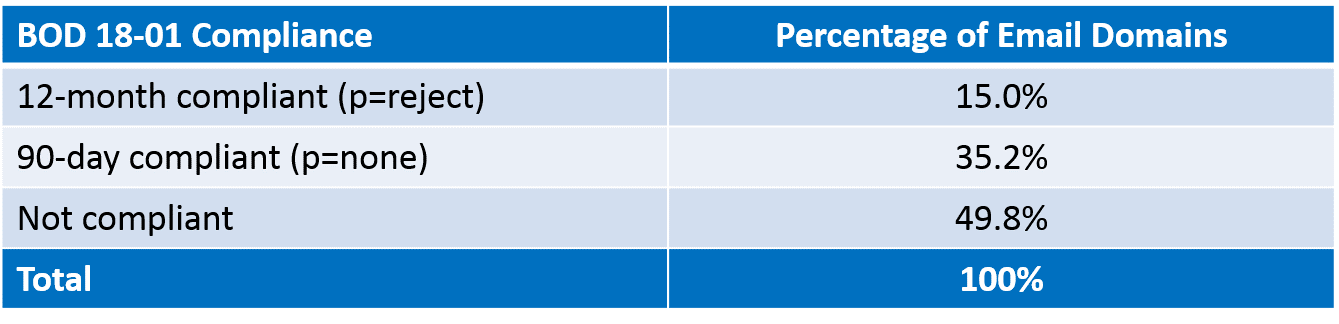
Surprisingly, nearly half of the agencies have not started their compliance journey at the date of the first compliance deadline. Looking across all of the email domains involved, only 47.1% have a DMARC record published. But it is interesting to note that 15% of the domains have already met the 12-month compliance requirement to achieve a DMARC policy of ‘reject’.
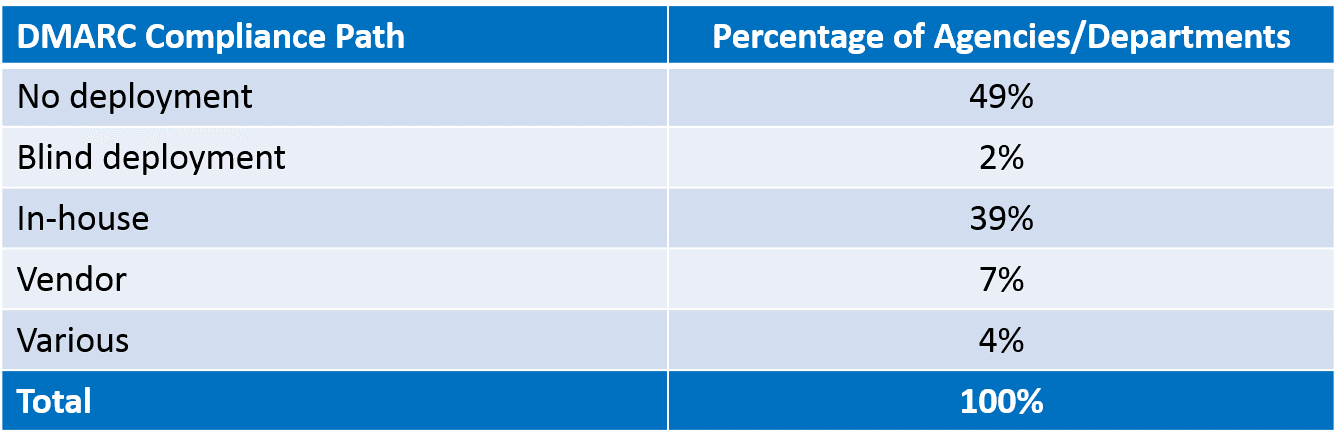
Of the agencies that have met the 90-day requirement to publish a DMARC record in monitor mode, the majority – 39% of all required federal agencies - have started the journey on their own, presumably in an effort to save money. But some agencies (1.7%) have published syntactically incorrect DMARC records, while others (1.8%) are “flying blind” publishing policies without receiving any reporting. Furthermore, because the DHS has insisted that they be included in all agency’s policies, a small number of domains (0.8%) have now exceeded DMARC’s practical limit of two reporting addresses.
The question that will need to be answered is whether or not working to implement DMARC alone compromises the intent of BOD 18-01: “to ensure the integrity and confidentiality of internet-delivered data, minimize spam, and better protect users who might otherwise fall victim to a phishing email that appears to come from a government-owned system”. Given the difficulty and risk associated with deploying DMARC authentication, this group of agencies may seek the help of vendors overtime in order to become compliant.
BOD 18-01 is an important step set by the DHS to restore trust to internet-delivered data from federal agencies. But, implementing DMARC is a significant challenge, as we see that nearly half of the agencies under the mandate have yet to take the first step towards compliance. You don’t have to take this journey alone. Proofpoint provides the visibility, tools, and services to help federal agencies implement DMARC authentication quickly and safely. We encourage organizations to get a free DMARC assessment and receive:
- A DMARC record that can be used to collect data on email using your trusted domains
- Visibility into all suspicious email being sent, including geographic details
- Guidance on steps that can be taken to improve your security










