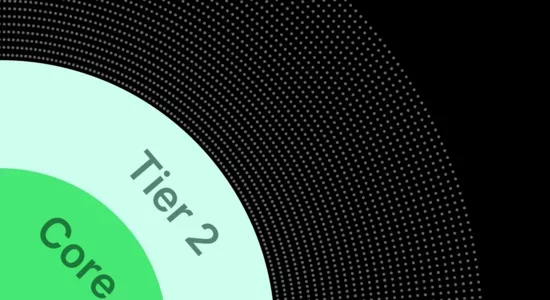
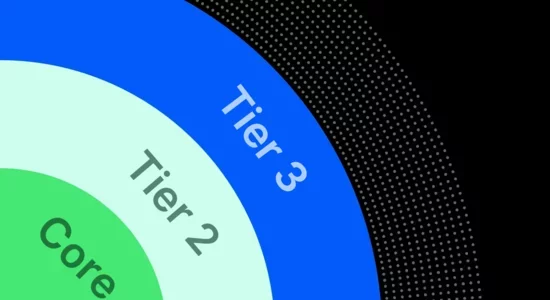
Core
Industry-leading Email Security
Core Email Protection
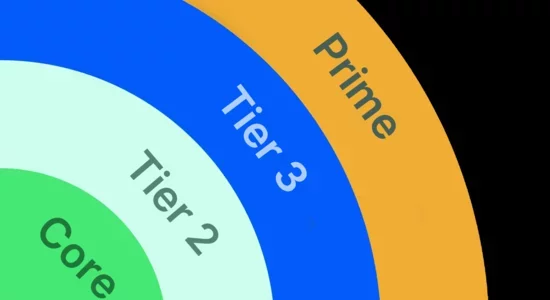
Complete collaboration security for the agentic workspace with Collaboration Security Prime
Compare our solutions to find the right fit for your team
Looking for Email Security? Check out our Core Email Protection.
| Key Features & Capabilities | Core | Tier 2 | Tier 3 | Prime |
|---|---|---|---|---|
| Industry-leading Email Security |
Yes
|
Yes
|
Yes
|
Yes
|
| Defend against account takeovers |
Yes
|
Yes
|
Yes
|
|
| Defend against compromised supplier accounts |
Yes
|
Yes
|
Yes
|
|
| Secure messaging tools like Teams, Slack |
Yes
|
Yes
|
Yes
|
|
| Deliver automated threat-guided training |
Yes
|
Yes
|
||
| Convert threats into instant simulations |
Yes
|
Yes
|
||
| Prevent domain fraud and spoofing |
Yes
|
|||
| Simplify authentication with hosted services (DMARC, DKIM, SPF) |
Yes
|
|||
| Detect and remediate lookalike domains |
Yes
|
|||
| Secure application-generated email |
Yes
|
Complete collaboration security with Prime
FAQs
I am an existing customer, how will my existing plan factor into the new solutions?
Proofpoint will honor renewals of current solutions for existing customers. There are special discounts and added functionality built into these solutions that may be financially beneficial for you to consider. Work with your Proofpoint account team to determine the best value for your organization’s needs.
How are the solutions priced?
Proofpoint Solutions are designed to optimize value for our customers. This means providing the most effective and comprehensive solution possible at a sustainable price. Budgetary pricing can be determined based on the number of user licenses and contract term (single or multi-year). There are exceptions that depend on consumption, so be sure to discuss your requirements with your Proofpoint account team.
How do I know which solution is right for my organization?
Please contact us. We would love to have a conversation to learn more about your organization’s criteria, challenges, culture, and budget.










