Although Dridex continues to crush other email-borne malware in terms of sheer volume (Proofpoint researchers are tracking what appears to be the largest Dridex campaign ever today), the actors behind Dridex are exploring new means of distribution and further expanding their geographic footprints. Just this week, Proofpoint researchers observed Dridex being dropped via the Bedep Trojan which in turn was dropped by Angler. Figure 1 below shows the stream with this infection chain in action.
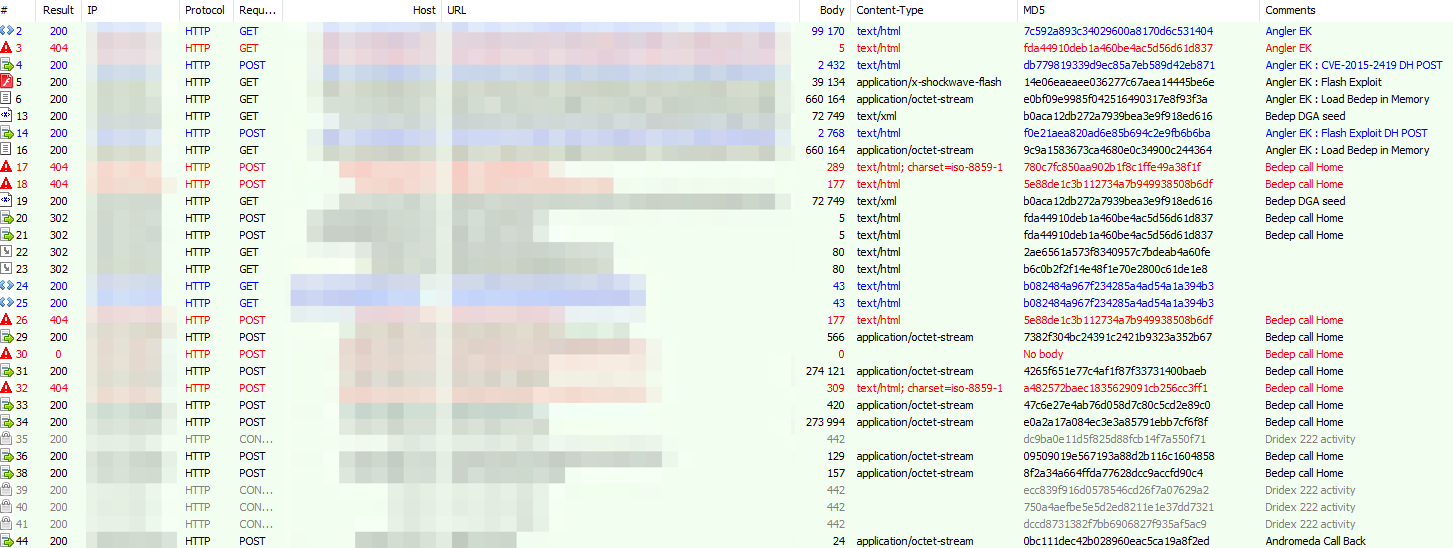
Figure 1: Stream showing novel Dridex infection chain (Angler EK -> Bedep -> Dridex)
This kind of variation is reminiscent of a blip we observed in November when both Dridex and Shifu were being distributed exclusively by Angler and RIG exploit kits rather than spam bots (normal for Shifu, but far less common for Dridex), although in the current case, spam volumes didn't drop off. Dridex distribution was simply augmented by the EK and Bedep.
Figure 2 below shows Dridex spam volume over the last month, reflecting the holiday dip we described last week as well as the return to exceptionally high volumes over the last week.

Figure 2: Record Dridex volumes following an extended holiday break
Perhaps just as significant, though, is the use of new botnets, wider international distribution, and new spammers distributing Dridex. For example, while the record-setting volumes observed today were primarily directed at US targets, Dridex spammers have recently turned much of their attention to the UK and Germany.
One particular actor, for example, launched a Dridex campaign recently that used a relatively new botnet (while reusing the old botnet 125 ID) for spam distribution of Dridex via two different message attachments. As the campaign progressed, the actor switched from dropping Dridex directly to dropping Betabot, which in turn was being used to drop Dridex and other payloads throughout the week. While this actor is not new to Betabot (or a variety of malware for that matter), this appears to be the first time distributing Dridex. Figure 3 below shows all message activity for this actor over the last 6 months. The final spike is Dridex.

Figure 3: A midrange actor who uses a variety of malware, recently distributing Dridex via Betabot
In another recent campaign, Proofpoint researchers observed the Bedep Trojan dropping a Dridex botnet that didn't share command and control infrastructure as expected but instead worked with c2 infrastructure in geographies that reinforced this notion of an increasing Dridex footprint and a growing backend that can deliver the sorts of volumes and diverse targets we're currently observing.
As we noted at the end of October, Dridex is not dead yet - Far from it, in fact. Actors are using new botnets, resurrecting old botnets, employing exploit kits, expanding command and control infrastructure, and employing malware that previously hadn't been used for distributing Dridex. They are targeting new geographies and launching spam campaigns with previously unseen volumes that use sophisticated techniques to evade traditional defenses. The volume, variety, and velocity associated with campaigns like today's, with customers seeing as much as 10% of their inbound mail volume as Dridex, makes the point very clear: the year may be new and the mechanisms may be evolving, but we certainly didn't see the end of Dridex in 2015.










