Table of Contents
Remote Access Trojan Definition
Like legitimate software developers, malware developers code their software for a specific purpose. A remote access Trojan (RAT) is a tool used by cybercriminals to gain full access and remote control on a user’s system, including mouse and keyboard control, file access, and network resource access. Instead of destroying files or stealing data, a RAT gives attackers full control of a desktop or mobile device so that they can silently browse applications and files and bypass common security such as firewalls, intrusion detection systems, and authentication controls.
Cybersecurity Education and Training Begins Here
Here’s how your free trial works:
- Meet with our cybersecurity experts to assess your environment and identify your threat risk exposure
- Within 24 hours and minimal configuration, we’ll deploy our solutions for 30 days
- Experience our technology in action!
- Receive report outlining your security vulnerabilities to help you take immediate action against cybersecurity attacks
Fill out this form to request a meeting with our cybersecurity experts.
Thank you for your submission.
How Are Remote Access Trojans Useful to Hackers?
A 2015 incident in Ukraine illustrates the widespread and nefarious nature of RAT programs. Attackers using remote control malware cut power to 80,000 people by remotely accessing a computer authenticated into SCADA (supervisory control and data acquisition) machines that controlled the country’s utility infrastructure. RAT software made it possible for the attacker to access sensitive resources through bypassing the authenticated user’s elevated privileges on the network. Having access to critical machines that control city resources and infrastructure is one of the biggest dangers of RAT malware.
Legitimate remote-control software exists to enable an administrator to control a device remotely. For example, administrators use Remote Desktop Protocol (RDP) configured on a Windows server to remotely manage a system physically located at another site such as a data center. Physical access to the data center isn’t available to administrators, so RDP gives them access to configure the server and manage it for corporate productivity.
RATs have the same remote-control functionality as RDPs, but are used for malicious purposes. Attackers typically code software to avoid detection, but attackers who use a RAT risk being caught if the user is in front of the device and the mouse moves across the screen. Therefore, RAT authors must create a hidden program and use it when the user is not in front of the device. To avoid detection, a RAT author will hide the program from view in Task Manager, a Windows tool that lists all the programs and processes running in memory. Attackers aim to stay hidden for as long as possible, so that they have more time to extract data and explore network resources for critical components that could be used in future attacks.
In addition to accessing network resources and files, any local hardware installed on the device is accessible to the attacker. An attacker using RAT software can access cameras, microphones, and connected USB devices, and an attacker can exploit these hardware resources to their advantage. For example, an attacker can use the camera to take pictures of the user or their surrounding environment. These photos can be used to find out more about the targeted user or organization. They can also be used to blackmail the targeted user into sending payment to an attacker.
Launching a distributed denial-of-service (DDoS) is another popular use for RATs. By controlling potentially thousands of devices, an attacker can instruct the devices to flood a targeted server with requests. What makes these attacks difficult to avoid is that there are no warning signs of an attack, and the flood of traffic comes from hundreds or thousands of devices from around the globe. Users with devices controlled by RATs are likely to be unaware of the installed malware and don’t know that their devices are being used for malicious purposes. Network performance is often affected when a user’s device is used in a DDoS, but users are often unaware that performance degradation is a warning sign for malware infection.
As Bitcoin and cryptocurrency continue to become more popular, attackers use RATs to configure infected devices for mining digital currency. Digital currency requires large quantities of computer resources pooled together to perform calculations. The electricity to power pools of computer resources is often more expensive than the returns on creating cryptocurrency. By hijacking third-party computing power, attackers can generate digital currency while never paying for electricity costs.
Finally, using a remote device for file storage is common with attackers that want to host illegal content. Instead of storing the content on their own servers and cloud devices, attackers use targeted stolen devices so that they can avoid having accounts and servers shut down for illegal content.
Email Security and Protection
Understand the risks you face and respond to threats faster
How Does a Remote Access Trojan Work?
To discover the way RATs work, users can remotely access a device in their home or on a work-related network. RATs work just like standard remote-control software, but a RAT is programmed to stay hidden to avoid detection either from anti-malware software or the device owner.
RATs often come packaged with other malware to help attackers with their goals. For example, it’s not uncommon for a RAT program to include a keylogger. A keylogger silently runs in the background collecting user keystrokes. With a keylogger, an attacker can obtain credentials for personal user accounts or for corporate productivity. With the right credentials, an attacker can obtain financial data, intellectual property or elevate privileges across the network to remotely control other devices on a corporate network.
An attacker must convince the user to install a RAT either by downloading malicious software from the web or running an executable from a malicious email attachment or message. RATs can also be installed using macros in Microsoft Word or Excel documents. When a user allows the macro to run on a device, the macro silently downloads RAT malware and installs it. With the RAT installed, an attacker can now remotely control the desktop, including mouse movement, mouse clicks, camera controls, keyboard actions, and any configured peripherals.
Since an attacker remotely accesses the computer, authenticated accounts such as email are at risk. Attackers can use email, for example, to send malicious messages to other potential victims using the authenticated email account on the remotely controlled device. Using a trusted email account gives attackers a better chance of tricking an email recipient into installing malware or running a malicious attachment.
How to Detect a Remote Access Trojan
Because RATs are designed to avoid detection, they can be difficult for the average user to identify. Depending on the RAT, users can take several steps to determine if they have one installed on their system. These steps can be used to identify most malware on a system so that steps can be taken to remove it. Any malware installed on a device should be removed immediately. Long-term access to a system gives an attacker more time to install additional malware, download large amounts of data, transfer important files to a third-party server, or collect more account credentials.
Typically, RAT authors avoid showing up in Task Manager, but not every program is written well for stealth. Open Task Manager and look at all applications and processes running on the machine.
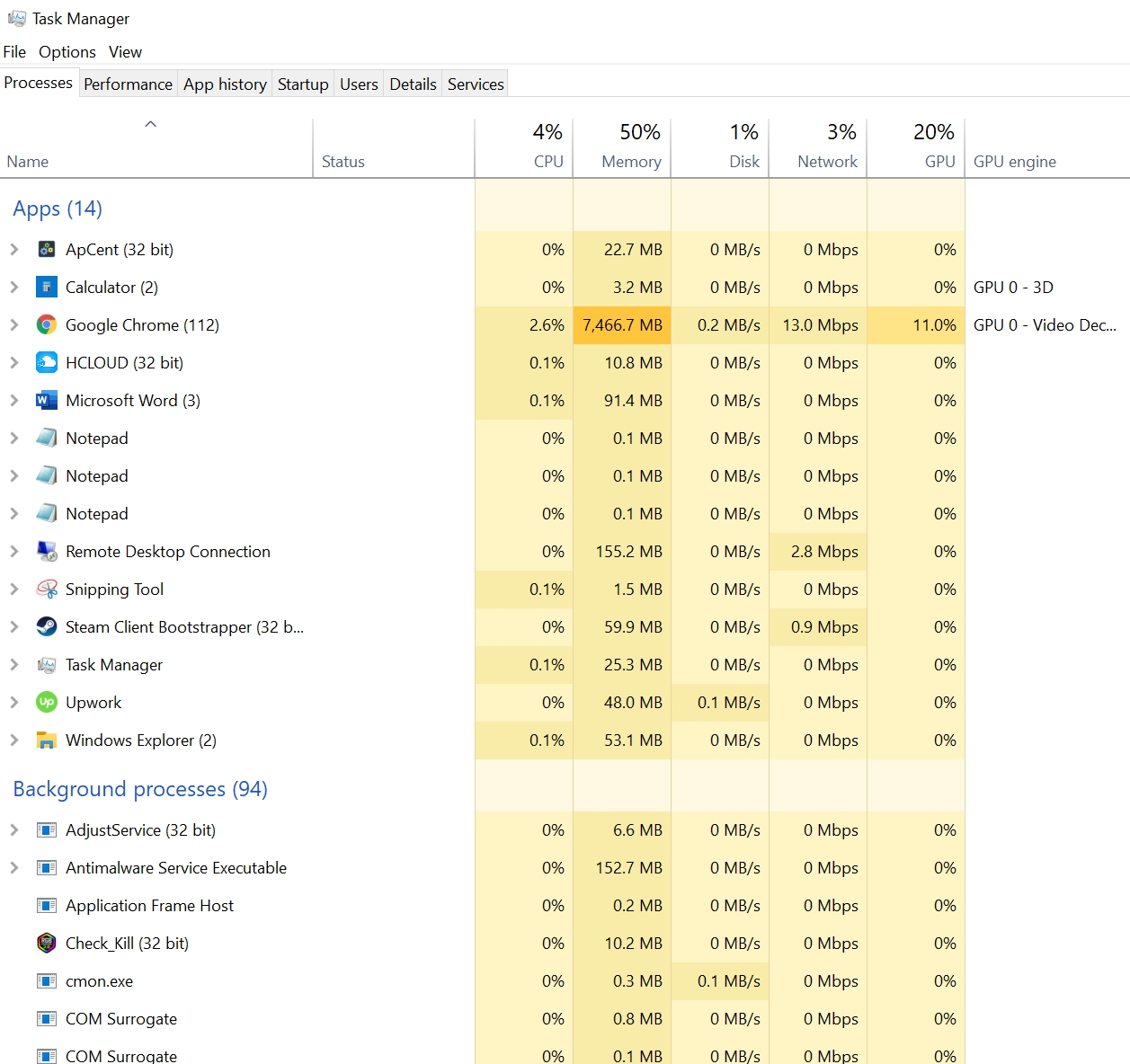
For most applications and processes, you can identify any suspicious content in this window, but malware writers name processes to make them look official. If you find any suspicious executables and processes, search online to determine if the process could be a RAT or other type of malware.
If you don’t see any potential malware in Task Manager, you could still have a RAT that an author designed to avoid detection. Good antimalware applications detect most of the common RATs in the wild. Any zero-day malware remains undetected until the user updates their anti-malware software, so it’s important to keep your anti-malware and antivirus software updated. Vendors for these programs publish updates frequently as new malware is found in the wild.
Always have anti-malware running on your computers, especially if it’s used to install programs or browse the web. Antimalware programs block RATs from being installed and loaded into memory, so they stop malware from persisting on the device. If you already have a RAT on your computer, anti-malware software can be used to remove it from your system.
Removing the Internet connection from the device disables remote access to your system by an attacker. After the device can no longer connect to the Internet, use your installed antimalware program to remove it from local storage and memory. Unless you have monitoring configured on your computer, you won’t know which data and files transferred to an attacker. You should always change passwords across all accounts, especially financial accounts, after removing malware from your system.
Get Ahead of Tomorrow’s Threats with Proofpoint
Anticipating the nature of certain cyber threats helps organizations identify where their defenses are weak and which protective measures to prioritize. Most organizations are more resilient through layered strategies that leverage detection and prevention technologies, real-time threat intelligence, and user-focused training programs to reduce the risk of attacks via email and cloud environments. As threats like phishing, BEC, ransomware, and credential theft evolve, it’s important to have the right mix of tools and processes to keep your data and your people protected. Take ownership to protect against threats and make strides to improve your cybersecurity effectiveness.
Leverage the capabilities trusted by 83 of the Fortune 100 companies. Contact Proofpoint to learn more.
Related Resources
The latest news and updates from Proofpoint, delivered to your inbox.
Sign up to receive news and other stories from Proofpoint. Your information will be used in accordance with Proofpoint’s privacy policy. You may opt out at any time.













