Key takeaways
- Modern email attacks don’t end at delivery. They evolve across users and systems.
- Legacy SEGs can generate high alert volumes without providing full attack context
- Proofpoint Threat Protection Workbench helps reconstruct attacks end‑to‑end. It surfaces the likely source, path, and impact in a single view.
- By unifying SEG and API-based protection, Proofpoint reduces the tradeoff between modern deployment flexibility and operational clarity.
Most email security tools were built to answer one question: Should this message be blocked or allowed? Yet modern attacks don’t stop at delivery—and neither does the work of a security operations center (SOC) analyst.
Today’s email threats unfold over time. A phishing message leads to a click. A click leads to account access. And that access leads to lateral movement, supplier abuse, or business email compromise (BEC).
By the time there’s an alert, analysts are no longer asking “Was the message malicious?” They’re asking:
- What was the source of the threat?
- What path did it take?
- What exposure did the threat create?
That’s where legacy secure email gateways (SEGs) often struggle. They generate alerts, not understanding; logs, not clarity; more tools, not better outcomes.
Proofpoint Threat Protection Workbench was built for a different reality—one where investigations matter as much as detection.
From filtering messages to understanding attacks
By design, legacy SEGs focus on messages. They excel at inspecting individual emails. But when threats span users, time, and systems, they can struggle. For SOC teams, this often means having to stitch together context across tools. They gather gateway logs to see delivery details, use dashboards to get threat intelligence, and work on separate consoles for remediation. And then, they put everything in spreadsheets to track progress.
Threat Protection Workbench takes a fundamentally different approach. Instead of treating each email as an isolated artifact, it brings message data, threat intelligence, and response actions into a single investigation experience. It’s designed for how analysts actually work. It takes the focus away from handling alerts and puts it on understanding attacks.
Innovation 1: See the full attack, not just the alert
Threat Protection Workbench gives analysts a visual, end-to-end view of how a threat unfolded—connecting messages, users, clicks, and remediation actions into a single investigation. At the center of that experience is the Threat Interaction Map, which shows the source of the threat, the path it took through the organization, and the exposure it created.
Instead of manually piecing together evidence, analysts can immediately see:
- The source of the threat
- The path it took through users and systems
- The scope and exposure it created
If an attack was fully contained, they can move on with confidence. If it wasn’t, they know exactly where to focus next.
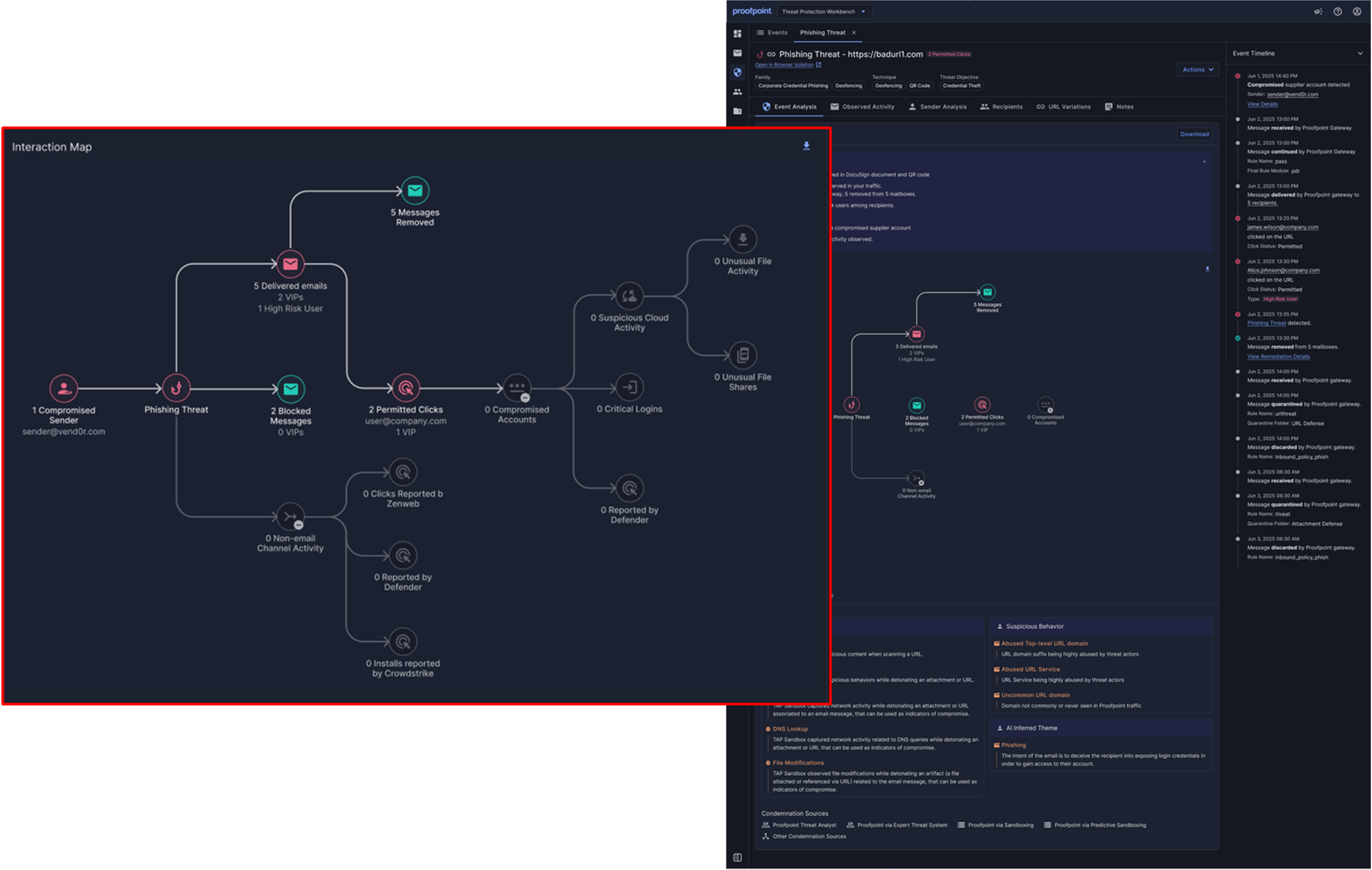
Figure 1. The Threat Interaction Map shows where a threat originated, how it moved through users and systems, and what exposure it created.
Innovation 2: Understand the attack in the order that it happened
Legacy tools often present fragmented snapshots of activity. This leaves analysts to reconstruct what happened and when. Threat Protection Workbench organizes investigations around Security Events, using time as the organizing principle.
Analysts still ask:
- What was the source of the threat?
- What path did it take?
- What exposure did it create?
But instead of using those questions to start an investigation, the answers are presented to them—clearly, sequentially, and in context. This chronological clarity reduces guesswork, accelerates triage, and builds confidence in their response decisions.
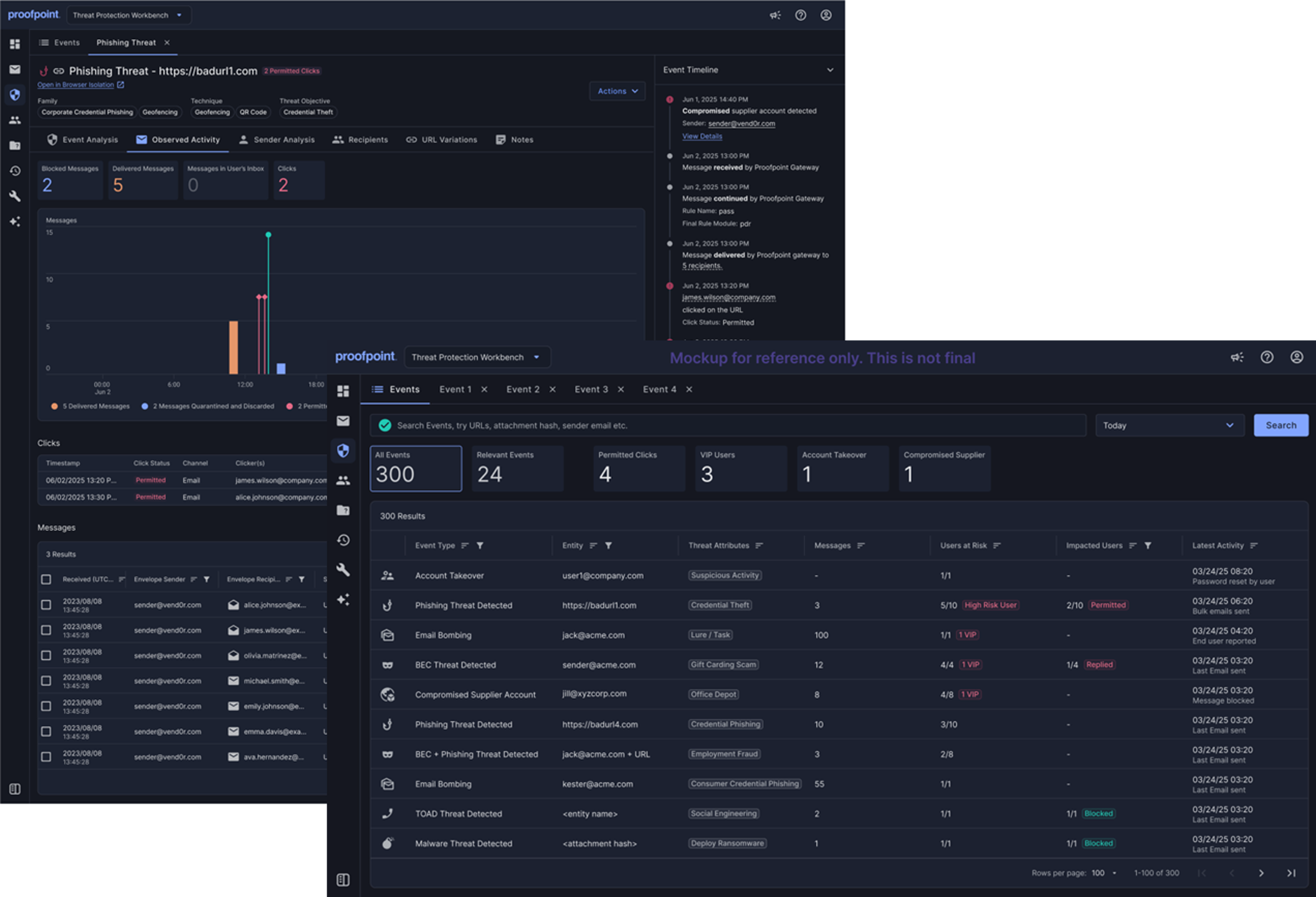
Figure 2. Security Events present every key action—delivery, click, report, and remediation—in the order it actually happened.
Innovation 3: Respond at the speed of understanding
User-reported email is one of the most valuable signals that defenders have. However, traditional abuse mailboxes can quickly turn into backlogs. Analysts must manually sort, prioritize, and investigate reported messages with little context, slowing response and increasing fatigue.
Threat Protection Workbench reimagines the abuse mailbox as part of the investigation workflow, not a separate queue. Reported messages arrive with built-in context, timelines, and response options. And AI agents assist with triage, helping surface what matters most. This enables analysts to focus on judgment instead of sorting.
From there, remediation actions—such as removing messages, blocking senders, or releasing false positives—can be taken directly from the same investigation view.
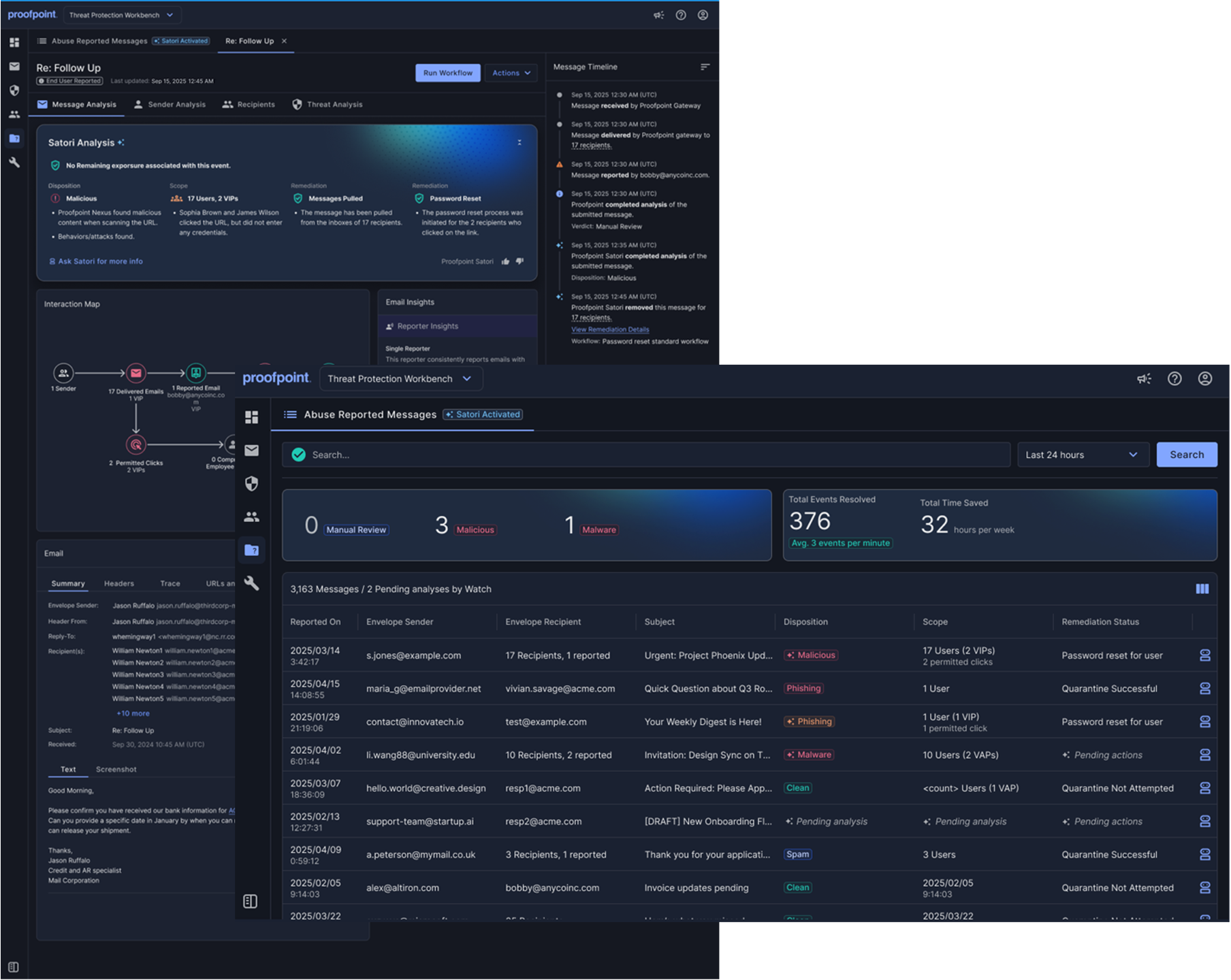
Figure 3. The reimagined abuse mailbox surfaces user-reported messages with built-in context, timelines, and priority.
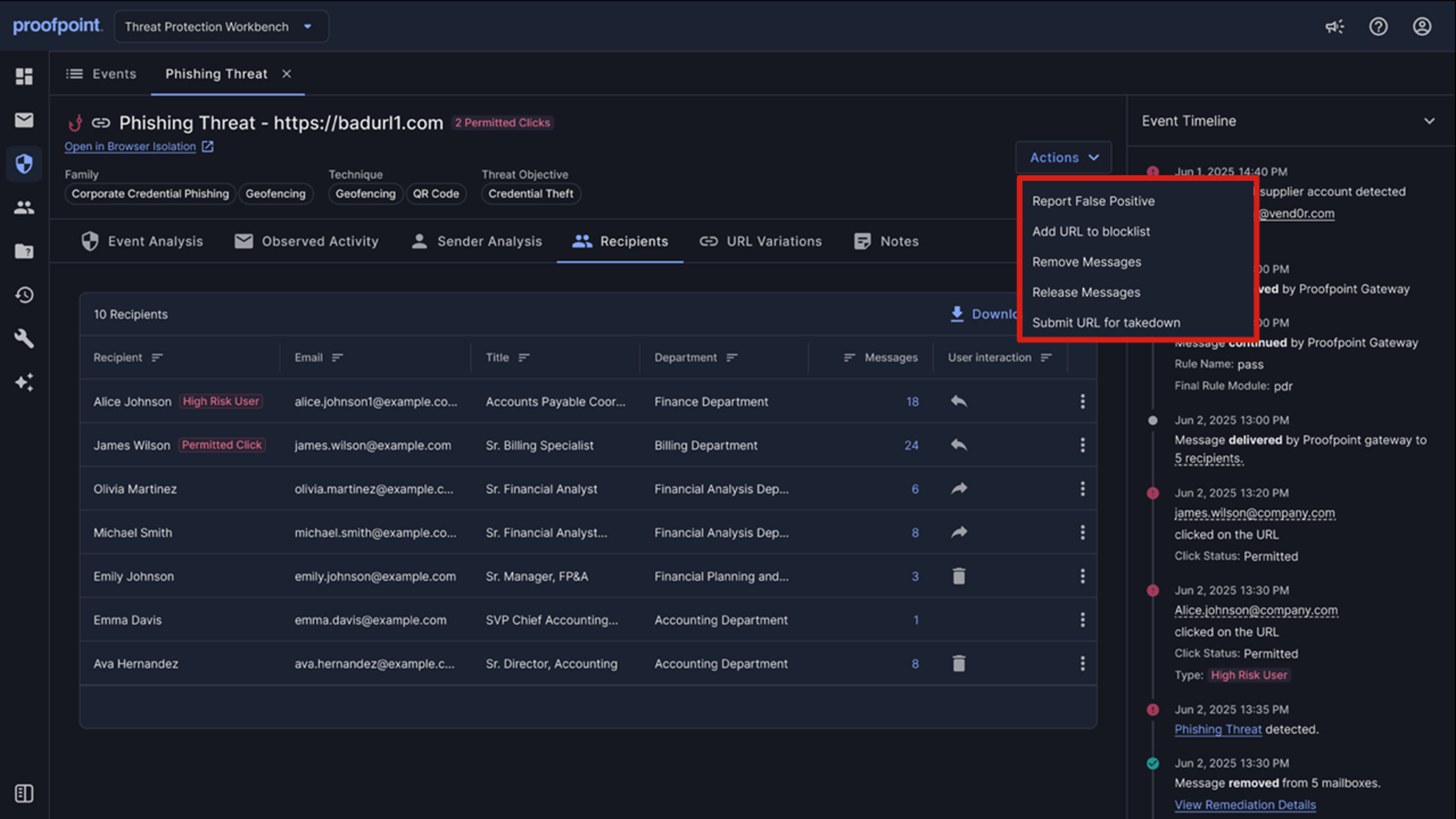
Figure 4. Analysts can remove messages, block senders, or release false positives directly from the same view.
Innovation 4: Turn real attacks into lasting resilience
Modern attacks don’t just expose technical gaps. They reveal human patterns: which lures work, which users are targeted, and which behaviors can be successfully exploited.
Threat Protection Workbench helps capture those lessons through capabilities like AI ThreatFlip Workflow. With ThreatFlip, organizations can turn real-world attacks into realistic training scenarios. Instead of relying solely on generic simulations, security teams can reinforce awareness using the same techniques that adversaries use against their own organization.
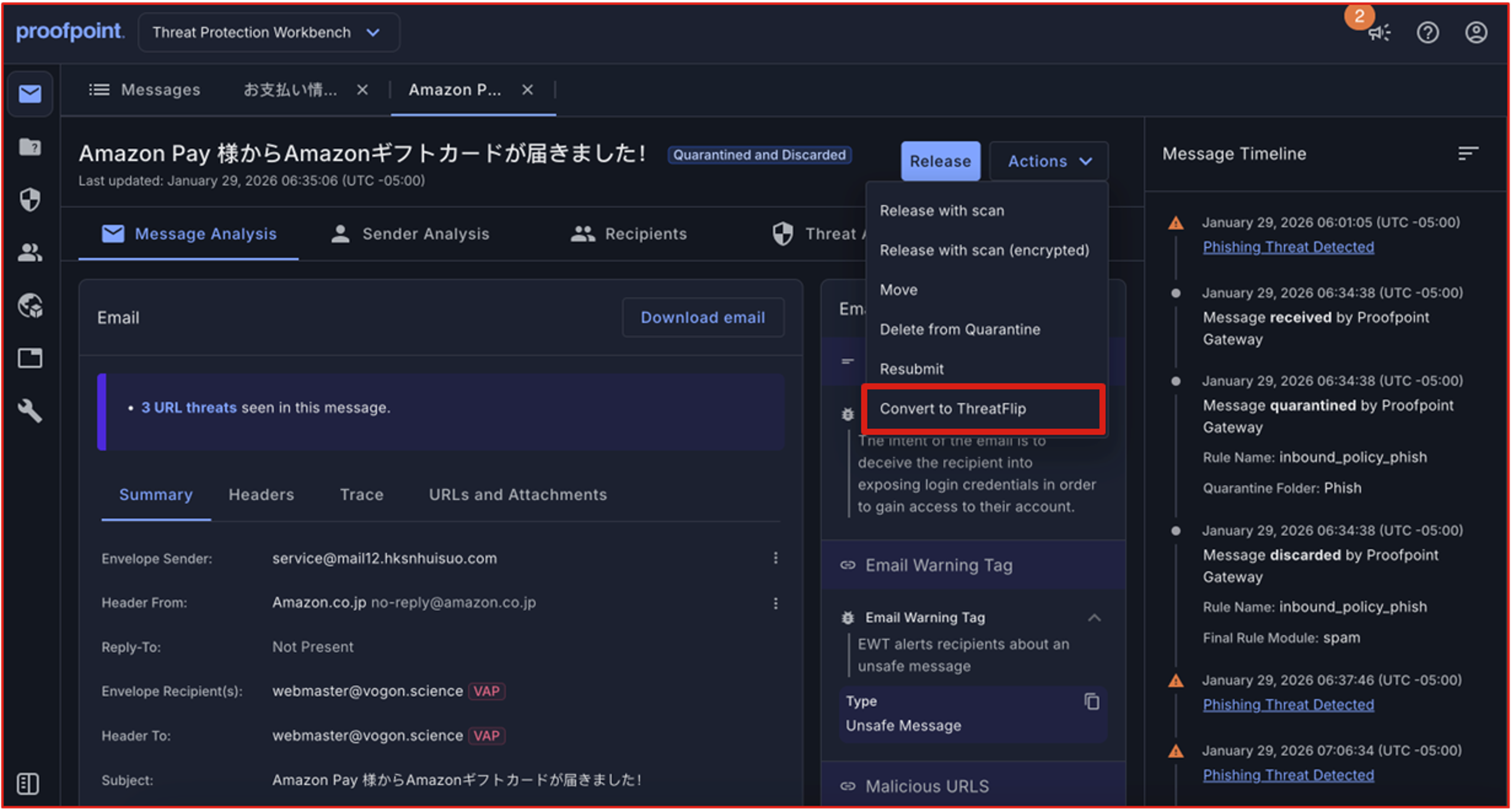
Figure 5. ThreatFlip transforms real-world incidents into realistic simulations.
Innovation 5: Gateway-level visibility and response—now for API-based protection
Historically, this level of visibility and unified response has only been possible with an SEG. And while API-based email security typically delivers strong detection, it often doesn’t provide the same investigation depth, visual context, or response consistency that SOC teams rely on from SEGs.
Proofpoint brings gateway‑level investigation and response into an API‑driven model.
Threat Protection Workbench serves as the common investigation layer across deployment paths—whether organizations replace a legacy SEG, augment Microsoft 365 with API-based protection, or adopt a hybrid approach.
Regardless of how protection is delivered, SOC teams get:
- The same investigation experience
- The same visual understanding of threats
- The same response workflows and confidence
Organizations no longer have to choose between modern deployment flexibility and deep operational clarity. They can have both.
What’s next: fewer decisions under pressure
Threat Protection Workbench continues to evolve. Future innovations will focus on:
- Expanding Security Events across email, identity, supplier, and collaboration threats
- Deepening visual context
- Introducing additional agent-assisted capabilities that remove toil without replacing human judgment.
The goal isn’t more features. It’s reducing the decisions that analysts have to make under pressure and helping ensure better outcomes.
It’s time to rethink email security investigations
Legacy SEGs were built for a simpler threat landscape. But Threat Protection Workbench is built for the reality that SOC teams face today: multistage attacks, human-targeted threats, and investigations that demand clarity and speed.
Part of Proofpoint Core Email Protection and the broader Collaboration Security Prime platform, it delivers modern, visual investigation and unified response across deployment models. Whether you protect your email through a secure email gateway or API-based protection for Microsoft 365, or you take a hybrid approach, it’s designed to evolve to meet what’s coming next.
Request a demo to see how Proofpoint Core Email Protection and Threat Protection Workbench can help your organization take a fundamentally different approach.
Explore More
- Learn more about Proofpoint Core Email Protection (SEG and API)
- Download the Core Email Protection solution brief
- Explore how Proofpoint Collaboration Security Prime unifies human-centric security











