As cyber attacks grow more scalable and creative, user awareness hasn’t kept pace, leaving organizations vulnerable to ransomware, phishing, insider threats—and the financial risks that stem from them. That’s just one of the major themes of the 2023 State of the Phish report, our yearly in-depth look at user awareness, vulnerability, resilience and risk.
Covering more countries and more threat types than ever, this ninth annual study from Proofpoint analyzes global survey responses, simulated phishing exercises and real-world attacks. The 2023 State of the Phish highlights how today’s cyber threats are evolving. And it uncovers critical gaps in people’s security knowledge and behavior.
The report compiles data from multiple sources, including:
- A commissioned survey of 7,500 working adults across 15 countries. (That’s more than double the countries surveyed in past years.)
- A commissioned survey of 1,050 infosec and IT professionals across those 15 countries.
- 135 million simulated phishing attacks sent by our customers over a one-year period.
- More than 18 million suspicious emails reported by our customers’ end users.
Download your copy of the 2023 State of the Phish report now to get full access to global and regional findings, including country-level breakdowns of the survey results.
Also, be sure to register now for our 2023 State of the Phish webinar on March 2. Our experts will detail the report’s findings, provide more insight and answer your questions in a live session.
In the meantime, let’s take a sneak peak at the data.
Global findings
Here are some key findings from this year’s report:
Survey of infosecs and IT
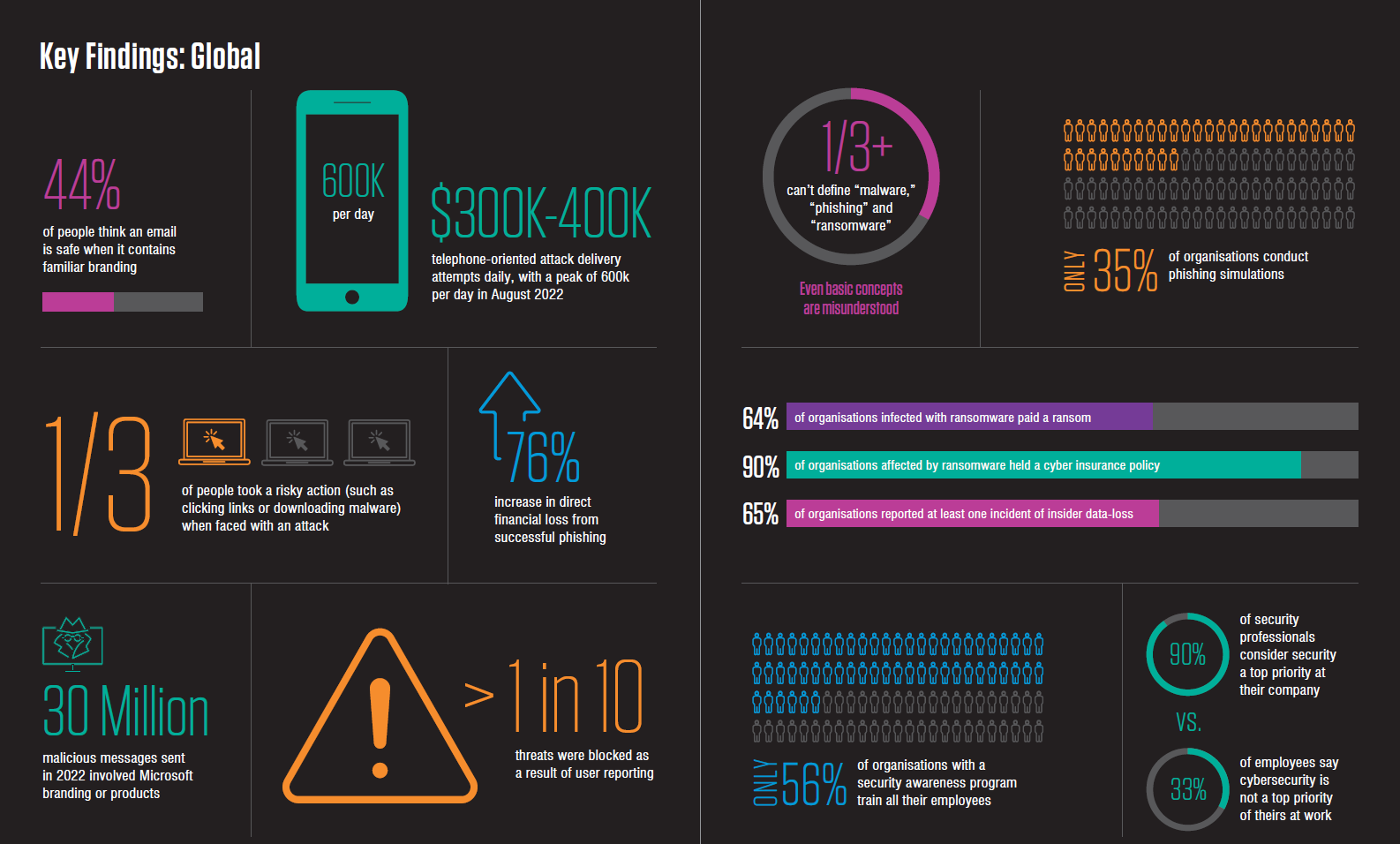
- 84% of those surveyed said their organization suffered at least one successful email-based phishing attack in 2022. Yet only 35% said they conduct phishing simulation. That’s down from 41% in 2021.
- Direct financial loss from successful phishing attacks soared 76%.
- 64% of organizations infected by ransomware agreed to pay ransom. Of those, 90% got help from cyber insurance.
- 65% of respondents said their organization lost data because of an insider. It’s no wonder insider threats were a top concern of CISOs surveyed in our global 2022 Voice of the CISO report.
Survey of working adults
- Users still struggle with basic security concepts. More than a third of those surveyed couldn’t define “malware,” “phishing” or “ransomware.”
- 44% of users think email is safe when it contains familiar branding. (Brand abuse remains one of the most common attack tactics.)
- Among users who changed jobs within the past two years, nearly half admitted to taking data with them when they left. That’s a major insider risk.
- There is a disconnect between infosec pros and other workers. For instance, 83% of infosec pros said they think security is a top priority for users. Just 67% of users agreed.
Proofpoint observations and security awareness data
- Microsoft was the most abused brand in 2022. Our researchers saw more than 30 million malicious messages that involved Microsoft branding or products.
- Attackers made 300,000 to 400,000 telephone-based phishing attempts on average per day. These attacks peaked at 600,000 per day in August 2022.
- More than 75 million malicious messages—roughly 12% of the messages we blocked—were first reported by end users at organizations that deployed PhishAlarm (our in-client email reporting button).
- Attackers’ COVID-19 lures still work. Among the 10 most-used template themes in 2022, the failure rate for a COVID-19 lure was more than 50% higher than the next closest theme.
Regional findings
For the first time this year, we’re releasing regional summaries of our data. Here’s a look at some of the key findings:
North America
(Note: These data points are not featured in the global 2023 State of the Phish report. But they are still worth noting, so we’re highlighting them here.)
- Among the 15 countries in our survey, U.S. organizations were most likely to suffer a successful phishing attack (98%). They’re also the most likely to suffer ransomware attacks (89%). Among infected U.S. organizations, 99% had cyber insurance.
- Canadian organizations were least likely (24%) of all 15 countries to file a cyber insurance claim. Many said their policy didn’t cover ransomware attacks.
- U.S. organizations were most likely (63%) to discipline users for unsafe behavior. About 9% of infosec respondents said a consequence model is not a culture fit for their organization.
Europe and the Middle East
- 71% of European and Middle Eastern employers lost data to insiders in 2022. German organizations were the most likely within the region to face frequent insider attacks (18%). Those in the UAE were the least likely (4%).
- Swedish organizations were the most likely within the region to face successful phishing attacks (94%). They also had the highest rate of ransomware infection (82%).
- Italians were the least likely to face successful phishing attacks. Italy was the only country with a ransomware incidence rate below 50%.
- Users in the Netherlands were the least likely to give out personal information (5%) or passwords (4%).
Asia-Pacific
- Japanese organizations were the least likely in in the region to suffer a successful phishing attack (64%). Australians were the most likely (94%). The prevalence of English in phishing emails might be a factor.
- South Korean organizations faced the lowest infection rates among those in the region attacked by ransomware.
- 95% of Singapore organizations infected by ransomware said their cyber insurance paid some or all of the ransom amount. That’s the highest in the Asia-Pacific region.
Brazil
- Brazilians reported fewer successful cyber attacks versus global averages in every category tracked in our study. Still, 70% suffered at least one successful phishing attack in 2022.
- 71% of organizations in Brazil provided security awareness education to every user. That’s the highest percentage of any country in our study and well above the 56% global average.
About the report
The 2023 State of the Phish provides data, insight and actionable advice. We cover:
- How threat actors are upping their game. We explore complex attacks such as multi-factor authentication (MFA) phishing and telephone-oriented attack delivery (TOAD). We also explore new phishing and social engineering tactics.
- Knowledge gaps and security habits in end users. We dive into risky behavior—both in and out of the office.
- Benchmark data for a range of metrics. See failure rates, reporting rates and resilience across industries, departments and phishing simulation campaigns.
- Key insights into building security culture. Find out the discrepancy in perception between security teams and end users.
Read the report for more global and regional insights
Across the globe, organizations faced both new and longstanding cybersecurity challenges in 2022. More than ever, a people-centric security approach is the most effective defense against these risks.
Download your copy of the 2023 State of the Phish report now for more key findings into:
- The impact of common tactics used by attackers
- How users' security habits both at home and work may affect an organization's security posture
- Industry benchmark data for failure rate, reporting rate and resilience










