Key findings
- Tycoon 2FA is one of the most popular phishing-as-a-service (PhaaS) platforms currently used by threat actors, and highest volume adversary-in-the-middle (AiTM) phishing threat in Proofpoint data.
- Tycoon 2FA infrastructure was disrupted by public and private partners, including Proofpoint, Microsoft, Europol, Cloudflare, Coinbase, Crowell, eSentire, Health-ISAC, Intel 471, Resecurity, The Shadowserver Foundation, SpyCloud, and TrendAI, and additional European law enforcement partners.
- The Tycoon 2FA disruption and associated lawsuit naming the creator will have a significant impact on Tycoon 2FA, related infrastructure, and threat actor activity.
- Proofpoint was proud to assist in the law enforcement and private sector investigations into Tycoon 2FA activity and supported Microsoft’s action with data, including malicious domains and information related to Tycoon 2FA campaigns.
Overview
Tycoon 2FA operates as an AitM phishing kit. Its primary function is to harvest usernames, passwords, and Microsoft 365 and Gmail session cookies. Attackers use these cookies to circumvent multifactor authentication (MFA) access controls during subsequent authentication. That allows them to achieve full account takeover (ATO) and gain unauthorized access to a user’s accounts, systems and cloud services—even those that have MFA as an additional security measure.
According to Proofpoint threat data, in 2025, 99% of organizations experienced account takeover attempts, and 67% experienced a successful account takeover. Of these, 59% of taken over accounts had MFA enabled. While not all MFA bypassing ATO campaigns are attributable to Tycoon 2FA, Tycoon 2FA is the highest volume AiTM phishing threat in Proofpoint visibility. Tycoon 2FA threat volumes vary based on actor activity, and in February 2026, Proofpoint observed over three million messages associated with Tycoon 2FA.
Tycoon 2FA infrastructure, including domains and servers, was disrupted in collaboration with private and public partners including Proofpoint, Microsoft, Europol, Cloudflare, Coinbase, Crowell, eSentire, Health-ISAC, Intel 471, Resecurity, The Shadowserver Foundation, SpyCloud, and TrendAI. In coordination with Europol, law enforcement in Latvia, Lithuania, Portugal, Poland, Spain and the United Kingdom carried out a seizure of infrastructure and other operational measures. Microsoft and co-plaintiff Health-ISAC also filed a lawsuit against the alleged Tycoon 2FA creator, Saad Fridi, and unnamed associates. The disruption and associated civil filing in the United States Southern District of New York will have a significant impact on Tycoon 2FA operations and overall threat activity.
Proofpoint supported Microsoft’s action with threat data from our visibility, including malicious domains and information related to Tycoon 2FA campaigns, and provided a declaration for the suit.
In addition to the disruption, the following splash page was displayed on the seized Tycoon 2FA domains:

Figure 1. Tycoon 2FA splash page.
Tycoon 2FA campaign details
Tycoon 2FA relies on attacker-controlled infrastructure to host the phishing webpages. Using a synchronous proxy the platform allows the interception of victims’ entered credentials. The credentials are then relayed to the legitimate service for a transparent, successful login, prompting MFA requests. The resulting session cookies are relayed back to the threat actors.
Tycoon 2FA is sold as a phishing-as-a-service (PhaaS), meaning that threat actors purchase access to the phishing tool and then they can customize it to suit their specific needs. The kit can be used multiple times through the duration of the subscription. Tycoon 2FA is used by multiple different threat actors, and sold by one main individual. It has been sold on Telegram since 2023 and was initially distributed via the “Saad Tycoon Group” channel.
Some Tycoon 2FA users are leveraging “ATO Jumping” whereby the actor compromises an initial email account, uses the compromised sender to broadly distribute Tycoon 2FA URLs, and attempts further account takeover (ATO) activities. Using this technique enables emails to look like they are authentically coming from a victim’s trusted contact, increasing the likelihood of a successful compromise.
Tycoon 2FA infections can lead to a variety of malicious activities including theft of private data including financial information, personally identifiable information, proprietary business information; full account takeover and access to M365 hosts that can be sold to additional threat actors; and potentially lead to follow-on malware compromises including ransomware.
Proofpoint has regularly tracked actors using the Tycoon 2FA phishing kit since 2024. We observe Tycoon 2FA distributed via email campaigns. A campaign is a time-bound set of related activity that is clustered by indicators of compromise (IOCs) such as senders, URLs, attachments, Tycoon 2FA configuration, etc. Tycoon 2FA campaigns vary in terms of scale; some include just a handful of messages; some include millions of messages. Campaign timelines can range from one day to one week.
Tycoon 2FA distribution depends on the criminals’ preferred method of email spam. Emails may contain malicious links, QR codes, SVGs, or attachments with URLs. In all cases, a user is redirected to an actor-controlled URL that displays a unique CAPTCHA resolution that, if solved, will direct to an attacker-controlled site impersonating a Microsoft or Google login portal. In many cases, the threat actor will display a target organization’s Azure Active Directory branding to further the social engineering component and trick a user into thinking they are entering their credentials into a real corporate site.
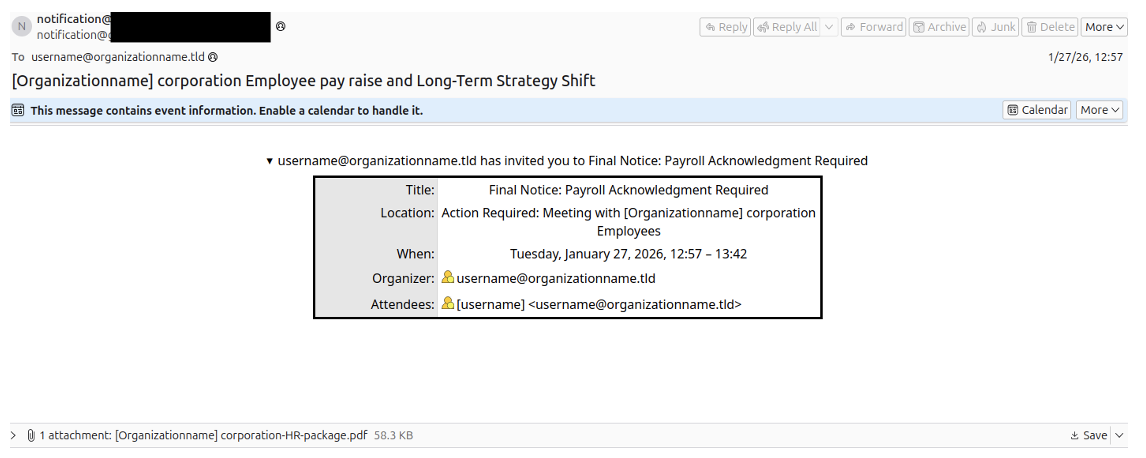
Figure 2. Email lure observed in late January 2026 with a PDF attachment containing a QR code leading to Tycoon 2FA.
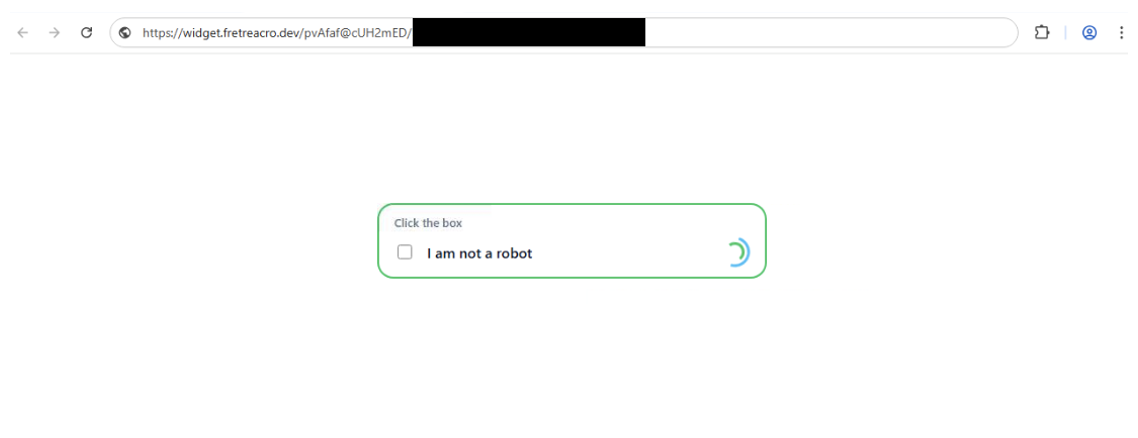
Figure 3. Example CAPTCHA used by Tycoon 2FA, January 2026.
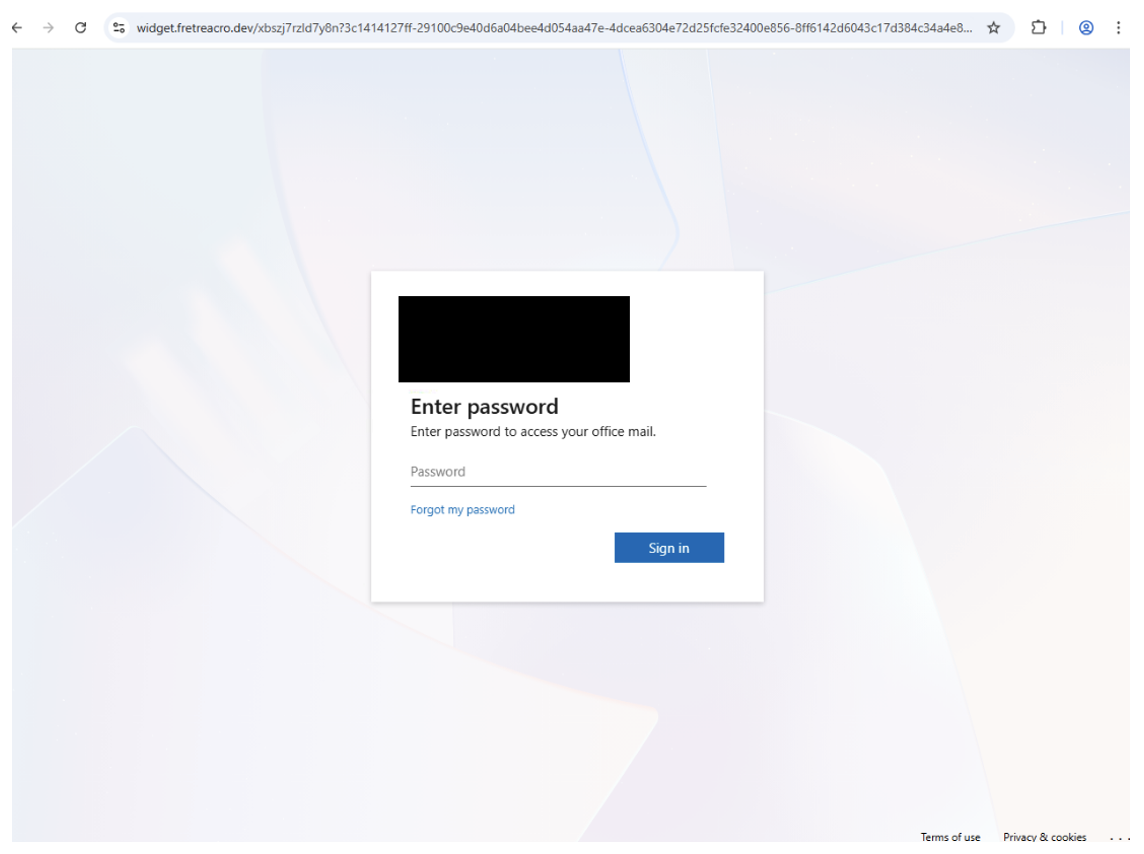
Figure 4. Tycoon 2FA landing page with the target organization’s logo redacted, January 2026.
Tycoon 2FA campaigns are typically opportunistic and target a broad range of organizations and often leverage compromised accounts to spread their phishing kits. Proofpoint has observed Tycoon 2FA distributed via compromised accounts from various industries including legal, real estate, healthcare, government, education, construction, and technology, as well as personal emails such as Gmail addresses.
Tycoon 2FA customers manage their campaigns via a panel provided by the Tycoon 2FA creator. The panel landing pages have changed slightly since 2023, but overall, the general URL structure and landing page functionality has remained the same.
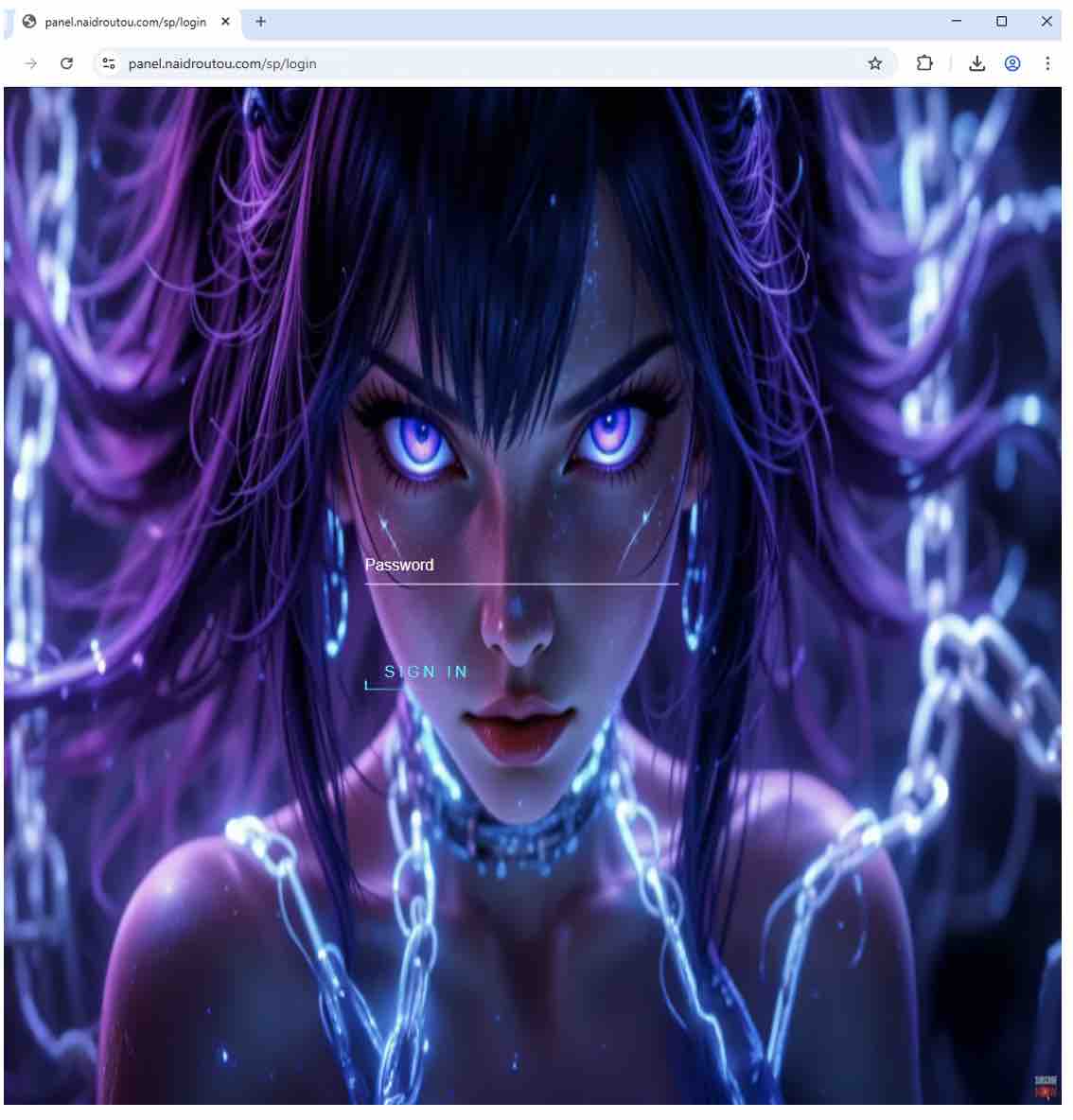
Figure 5. Tycoon panel login screen, February 2026.
The current panel (as of February 2026) also requires a CAPTCHA.
Impact
The majority of tracked Tycoon 2FA campaigns impact North America, mainly the U.S. and Canada, with additional activities targeting many European countries including Germany, Spain, France, and the UK. According to Microsoft, Tycoon 2FA enabled cybercriminals to access almost 100,000 organizations, including schools, hospitals, non-profits, and public institutions.
Based on Proofpoint’s visibility, the following is an example of industries that were targeted in observed Tycoon 2FA campaigns in our threat data, and the percent of campaigns in which they appeared. (Individual campaigns impact multiple different targets).
|
Vertical |
Percent of Tycoon 2FA Campaigns |
|
Aerospace |
73% |
|
Business Services |
82% |
|
Defense |
64% |
|
Education |
75% |
|
Energy |
78% |
|
Financial Services |
84% |
|
Government |
79% |
|
Healthcare |
83% |
|
Hospitality |
76% |
|
Manufacturing |
83% |
|
Real Estate |
77% |
|
Technology |
85% |
|
Utilities |
76% |
Disruption
On 4 March 2026, Microsoft announced a lawsuit and disruption action against the Tycoon 2FA creator and multiple unnamed associates. Proofpoint supported the civil filing by providing a declaration regarding Tycoon activity, including infrastructure and campaign details. Microsoft seized 330 control panel domains associated with Tycoon 2FA. This action will have a significant impact on operations, disrupting ongoing criminal activity.
Successful account takeovers can cause significant harm to compromised organizations including financial and reputational damage, loss of proprietary data, and potentially lead to follow-on attacks like ransomware that can have destructive and potentially organizational damaging consequences.
Proofpoint’s mission is to provide the best human-centric protection for our customers against advanced threats. Whenever it is possible and appropriate to do so, and as is the case with the Tycoon 2FA disruption, Proofpoint uses its team’s knowledge and skills to help protect a wider audience against widespread malware and phishing threats. Proofpoint was proud to assist in the law enforcement and private sector investigations into Tycoon 2FA activity.
Through its unique vantage point, Proofpoint is able to identify the largest and most consequential malware distribution campaigns, providing the authorities with much-needed insight into the biggest threats to society, affecting the greatest number of people around the world.










