Proofpoint researchers have been tracking a low-volume, email-based ransomware campaign targeting organizations in Austria, Switzerland, and Germany. The campaign leverages Hakbit, a variant of Thanos ransomware as a service (RaaS). The attack employs malicious Microsoft Excel attachments delivered from a free email provider (GMX) that primarily serves a European client base. The attachments contain false billing and tax repayment subjects to entice users to enable macros that execute GuLoader, which downloads the ransomware to encrypt files and lock the system.
To help ensure success because Microsoft Office VBA macros do not execute on mobile devices, these emails direct recipients to open attachments on their computer and not their mobile device.
Users targeted were employed in mid-level positions across the pharmaceutical, legal, financial, business service, retail, and healthcare sector. The largest volume of messages we observed were sent to the information technology, manufacturing, insurance, and technology verticals. Proofpoint researchers have observed that the majority of roles targeted in the Hakbit campaigns are customer-facing with individuals’ business contact information revealed publicly on company websites, and/or advertisements. These roles include attorneys, client advisors, directors, insurance advisors, managing directors, and project managers.
Below is an example of the lure, many messages arrived with subject lines such as “"Fwd: Steuerrückzahlung" (Translated: Tax Repayment)” and “Ihre Rechnung (Translated: Your Bill)”.
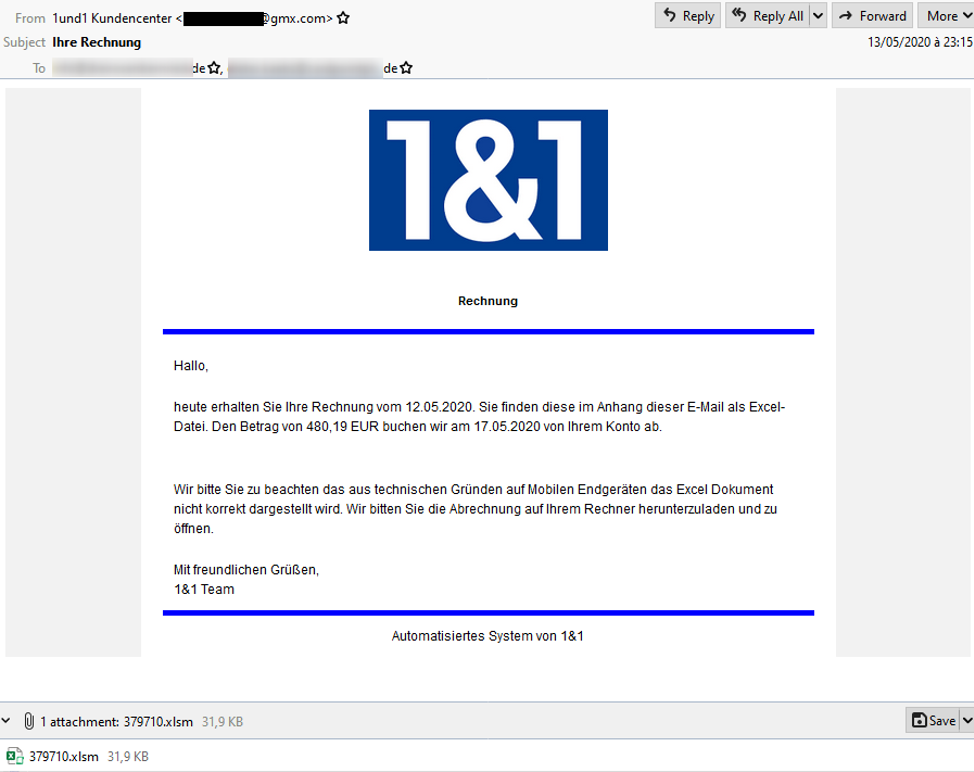
Figure 1 Hakbit Lure Email Message in German
This lure is in German and abuses the logo and branding of 1&1, a German telecommunications company. According to Google Translate, the body of the message states:
Today you will receive your invoice dated 12.05.2020. You will find it in the attachment to this e-mail as an Excel file. We will debit the amount of EUR 480.19 from your account on May 17th, 2020.
Please note that due to technical reasons the Excel document is not displayed correctly on mobile devices. We ask you to download the invoice on your computer and open it.
Best regards,
The message contains a Microsoft Excel attachment named 379710.xlsm which leverages malicious macros. Because the macros and malware won’t work on a mobile device, the message instructs the recipient to use a computer to read the attachment. Once opened, the spreadsheet directs the recipient in German and English to enable macros as shown in Figure 2.
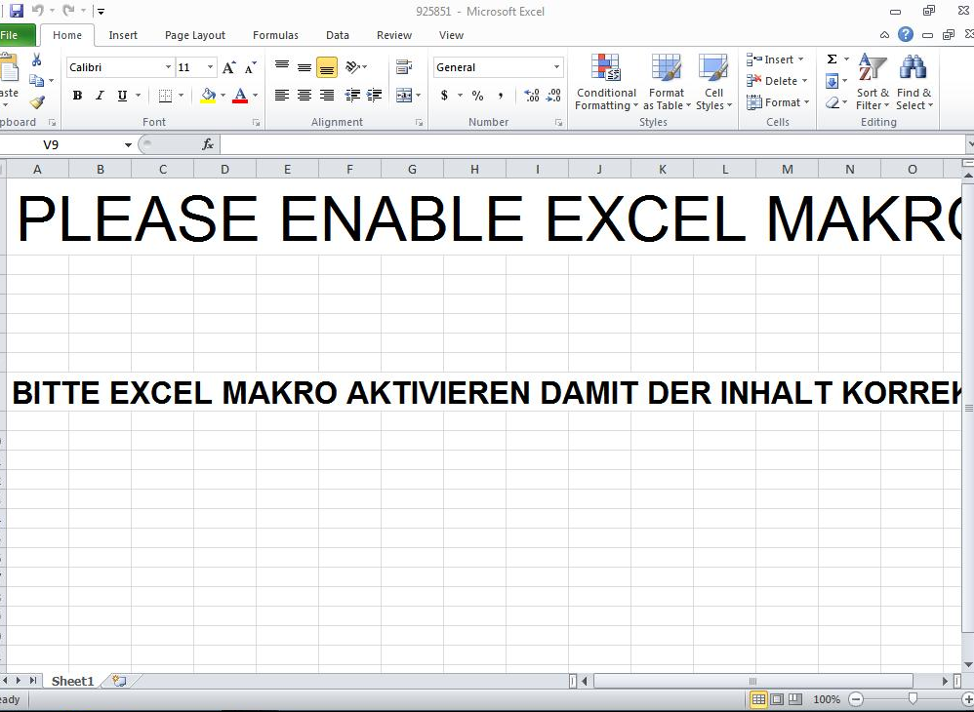
Figure 2 Microsoft Excel Attachment with Enable Macros Message
Once macros are enabled in the spreadsheet, it downloads and executes GuLoader, a relatively new downloader written in VB 6.0 that we wrote about in March 2020. When GuLoader runs, it downloads and executes Hakbit, a ransomware that encrypts files using AES-256 encryption.
Below is the image that appears when Hakbit executes (Figure 3) and the ransom note in both English and German (Figure 4).
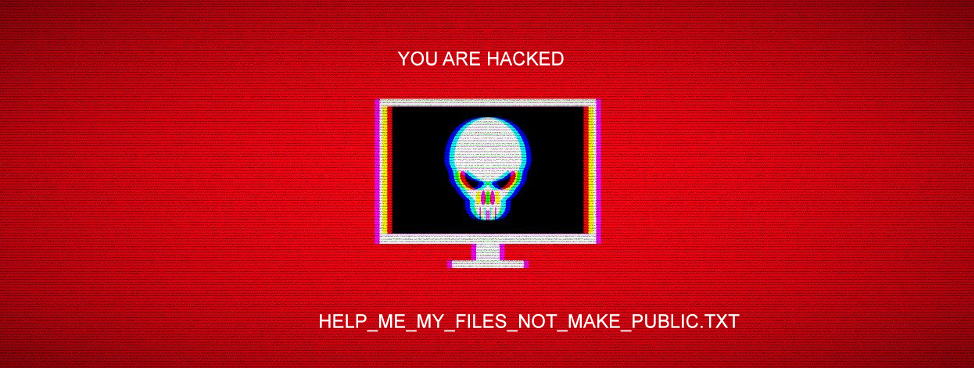
Figure 3 Hakbit Ransom Screen
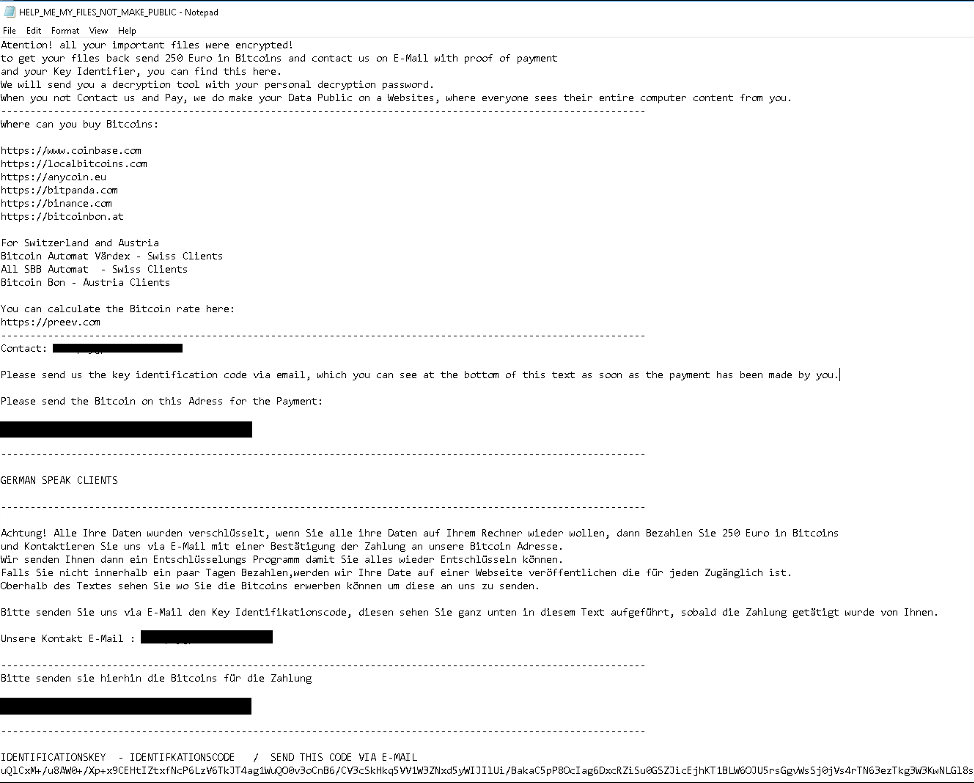
Figure 4 Hakbit Ransom Note
The note demands a payment of 250 Euros in bitcoin to unlock the encrypted files and provides instructions on how to pay the ransom. As of June 16, 2020, our researchers have found no transactions showing payment of the ransom to the bitcoin wallet in the examples here.
Conclusion
Proofpoint researchers have observed consistent low-volume and often boutique ransomware campaigns since January 2020. Proofpoint researchers recently identified a shift in the threat landscape with a large-scale Avaddon ransomware campaign consistent with recent open source vendor reporting. Hakbit exemplifies a people-centric ransomware campaign tailored to a specific audience, role, organization, and in the user’s native language.
Indicators of Compromise (IOCs)
|
Hakbit |
SHA256 |
34b93f1989b272866f023c34a2243978565fcfd23869cacc58ce592c1c545d8e |










