Reducing the risk of a major data breach has become a top priority at most organizations. But executive views of the effectiveness of different security measures vary greatly. Below, we dive into the recent research the Economist Intelligence Unit (EIU) conducted on behalf of Proofpoint to help you make the most informed decision about your cybersecurity solutions.
Preventing Data Breaches Is a Top C-Suite Priority
The EIU research revealed that an overwhelming number (82%) of executives cite preventing data breaches as a high or essential C-suite priority and 73% expect reducing the risk of a major breach to become a higher priority for the C-suite over the next three years. Almost all respondents (96%) said the board and C-suite strongly support efforts to control cybersecurity risks and 93% say the board and C-suite are regularly updated on cyber-security risks.
How Executives Are Addressing Data Breaches
1. Centralize Defense Efforts
Many companies anchor their defense by centralizing the organization’s efforts to help create a cybersecurity culture embracing every employee, every functional area and line of business and the networks that bind them together. Virtually every respondent (94%) agreed that their organization has done so.
2. Move Corporate Infrastructure to the Cloud
Moving corporate infrastructure to the cloud to ensure a more secure data environment was another top security measure. Almost half (46%) of respondents said their organization has moved more than half of its data infrastructure to the cloud and over 69% said they have moved more than 40%. Most respondents also said their organization has undertaken processes to address data breaches. The survey divided these into two groups: processes to ensure responsible cyber-security behavior by employees and processes to avoid and mitigate data breaches.
3. Employee Protection & Security Awareness Training
Between 84% and 95% of respondents said their organization had taken action or plans to implement the following to ensure responsible behavior:
● Conduct pre-employment screening and background checks to avoid hiring individuals who pose a risk (89%)
● Require employees to sign confidentiality agreements (91%)
● Develop and enforce information security policies for employees (93%)
● Conduct regular employee education and security training (94%)
● Limit or block personal web browsing and access to personal email (91%)
● Define and limit employee access to specific data types (95%)
● Offer incentives to motivate upstanding online behavior (84%)
● Stipulate clear consequences for negligence (91%)
● Monitor user accounts for unusual activity or behavior (94%)
Between 86% and 96% said their organization has taken action or plans to implement the following to avoid and mitigate data breaches:
● Require strong credentials and multi-factor authentication (93%)
● Train users to detect and report suspicious email (94%)
● Isolate employees’ personal web browsing and email activity from network traffic (92%)
● Implement a zero-trust network strategy for access security (86%)
● Install security programs (secure email gateways, cloud access security broker/ cloud security tools, firewalls, antimalware and anti-virus software; 96%)
● Roll out systems and software updates and patches as soon as they are available (94%)
● Install upgrades as soon as manufacturer no longer supports software (95%)
● Periodically run tests on data security standards and practices (96%)
● Require use of a virtual private network (VPN; 91%)
What Works Best
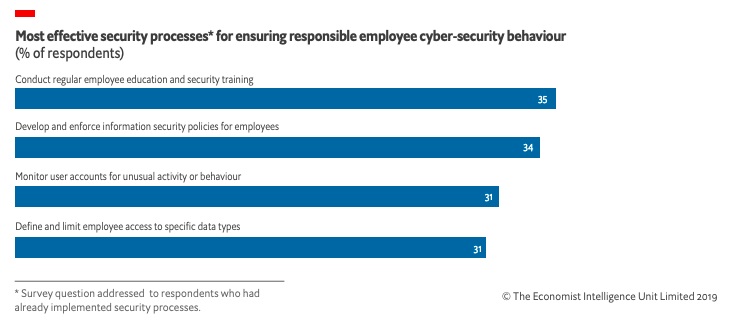
While opinions varied greatly about what the most effective security measures were, the most favored tended to be the most basic, suggesting that as long as employees are educated and informed of the rules, they will assume a measure of responsibility.
Survey respondents who had already implemented security processes found the following to be most effective in ensuring responsible cyber-security employee behavior:
1. Conducting regular employee education and security training (35%) and
2. Developing and enforcing information security policies for employees (34%).
In addition, one out of four respondents mentioned limiting or blocking personal web browsing and access to personal email.
To learn more about this eye-opening research and to hear specific perspectives from executives like Deborah Wheeler, CISO of Delta, Adrian Ludwig, CISO of Atlassian, please read the full report, “Cyber insecurity: Managing threats from within.”










