
Defense-in-Depth: The Missing Layer
Information security has become a game of juggling priorities in the different layers of a defense-in-depth strategy. Information security departments spend millions of dollars every year on software and hardware to battle malware, build firewalls, detect intrusions, analyze threats, and countless other functions.
These technical safeguards have been tasked with creating an impenetrable defense, and we’ve seen that the strategy isn’t working, with countless breaches in the news, along with the slew of others that go unnoticed or unpublished. Hackers are skirting around most organizations’ software defenses with an easy target: end users.
Just consider everything we know about errant end-user behavior contributing to security incidents:
- Human error and malicious insiders represented 59% of security incidents in the last year
- Source: Experian 2015 Data Breach Industry Forecast
- More than 95% of all security incidents investigated recognize “human error” as a contributing factor
- 23% of recipients now open phishing messages and 11% click on attachments
- Source: 2015 Verizon Data Breach Investigations Report (DBIR)
A Marriage of Human and Technical Safeguards
Evidence is starting to come to the surface that end-user training can reduce risk and build a credible layer of defense:
- 76% less is spent on security events when employees are trained in good cyber security hygiene
- Source: PWC 2014 US State of Cybercrime Survey
- Employee training cuts the cost of phishing attacks by over $1.8M for an average 10,000-person company
Information security departments should be asking themselves how they can reduce end-user error in a meaningful way and start thinking of their end users as a layer to work with, not work around. Just like every other layer, there should be time and investment — even though a security awareness and training program may not seem to fit within traditional information security skill-sets or protection plans.
There is also a way to tackle end-user issues using existing security infrastructure. Wombat’s new partnership with endpoint protection provider Carbon Black marries endpoint remediation with end-user remediation, creating a blend of technical and human safeguards to create a stronger layer of human defense.
By engaging and educating end users at a relevant time and place, organizations are tackling the human error problem head-on. Is this a silver bullet for perfect security? Of course not. But it’s an important step in bridging the gap between technical and human solutions.
Just-in-Time, Not Hours of Your Time
There’s no reason to over-train and bore employees with hours of presentations or unnecessary in-person training that’s inconvenient and detracts from productivity. Training should be just-in-time, focused, and relevant. Just like you’d be annoyed if your anti-malware software kept flagging non-malware as malicious, a security awareness and training program should be looking for its weakest links.
It’s possible to do simulated phishing attacks or knowledge assessments to find out weaknesses. But what about dealing with real threats like end users who click real phishing emails, download malicious attachments, and visit unsafe links? Wombat’s partnership with Carbon Black will connect Wombat’s leading Security Awareness and Training solution with Carbon Black Enterprise Response, an advanced endpoint threat detection and response solution. This technology partnership will enable companies to sense and interrupt risky employee behavior with helpful “just-in-time” training to lower their overall cyber security risk.
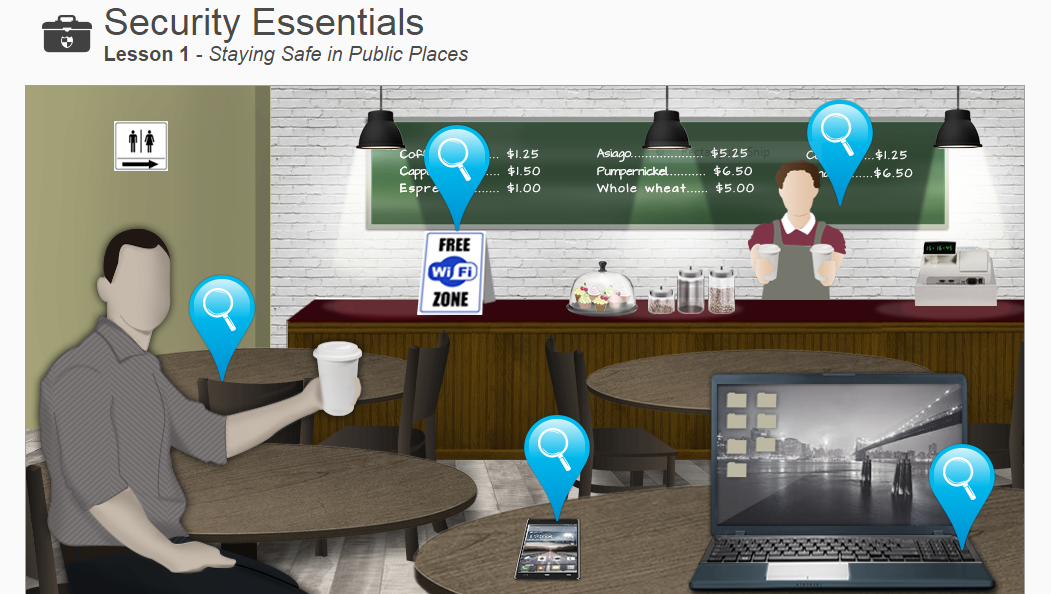
When Carbon Black Enterprise Response identifies end users who have received emails with, or downloaded, potentially dangerous files, the joint solution can trigger user enrollment in Wombat’s interactive training modules such as Email Security or Security Essentials. This raises the effectiveness of both endpoint security and security education with “just-in-time” training to change employee behavior and strengthen their defense against cyber attacks.










