There’s real money to be made in real estate. And in 2020, we anticipate the potential for profit will continue to attract cybercriminals as they attack real estate transactions, which are mostly carried out through their favorite channels: emails, websites, and attached documents. To uncover the top cyberattack trends—and detail necessary safety tips—we examined more than 600 U.S. real estate transaction attack attempts and here’s what we uncovered.
Cybercriminals have significantly shifted their attack scope and expanded their net to go after all the players involved in real estate transactions including: agents, buyers, inspectors, insurance agents, and even contractors. Anyone involved in any stage of a real estate transaction needs to know they could potentially be hit with attempts to steal funds and compromise deals. Specifically, bad actors often use fake business email compromise (BEC) messages, spoofed emails, or more recently, they take over the email account of someone in the real estate attack chain to con their victims into acting (this is referred to as email account compromise by the FBI, or EAC). According to the United States Federal Bureau of Instigation (FBI)’s Internet Crime Complaint Center (IC3), over US$26 billion was lost around the world to BEC from June 2016 and July 2019.
While cybercriminals have been going after the big payoffs at the end of real estate transactions for years, the expansion into more targets suggests they are looking to expand their successes. According to our research, attackers varied widely from being very focused and sophisticated to less capable actors using social engineering exclusively. The people behind these attacks run the gamut from known attacker groups to one-off individuals and employ a broad arsenal of tactics and tools, including:
- Social engineering
- Phishing
- Malware, specifically banking Trojans and information stealers
- Compromised personal and business landing pages
- Weaponized attached documents
- Email thread hijacking
- Phishing portals themed around individual agents/agencies
- Financial/wire fraud
Below are six attack attempt examples, including spoofed Office 365 and DocuSign phishing emails to lure victims into clicking. We’ve also provided four ways to stay safe while completing real estate deals in 2020.
A Closer Look at the Threats
Figure 1 is an example of a spoofed Office 365 login page. This page was the destination in a link sent directly to the CEO of a major North American real estate brokerage agency.
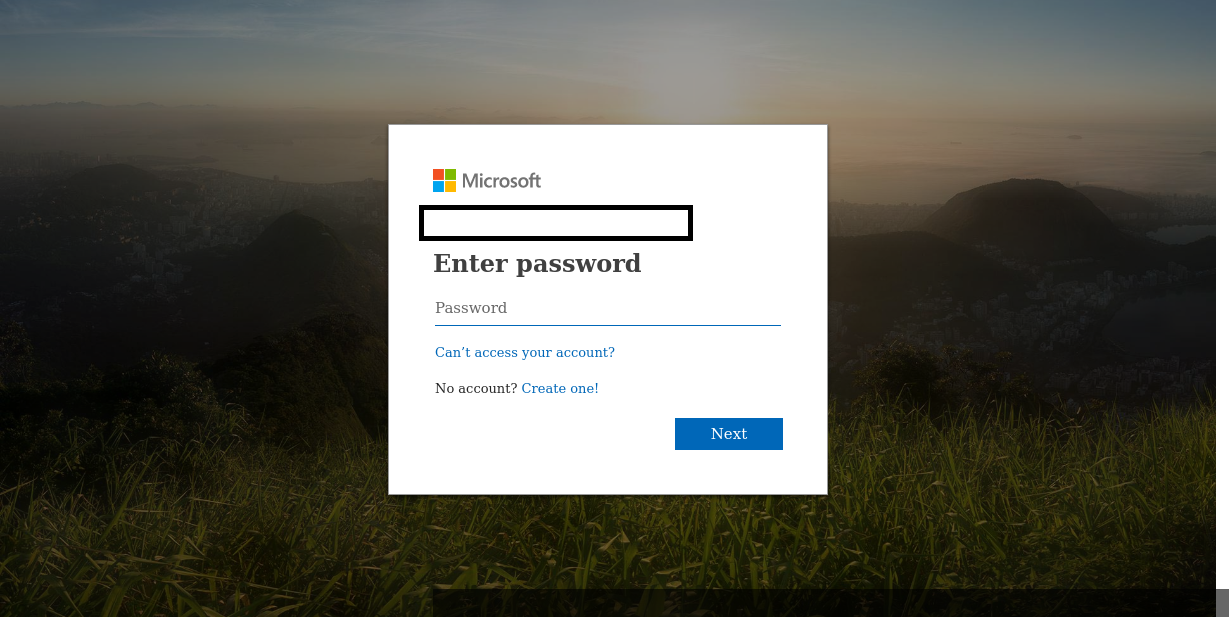
Figure 1 Spoofed Login Page Targeting Real Estate Company CEO
This is a classic example of spearphishing: the attackers did their research and knew exactly who to target. In this case, the attacker’s goal is to get the CEO’s username and password.
Targeting of credentials for later use like this is an increasingly common tactic against players at all points in the real estate transaction chain. In addition to online services like Office 365, our researchers found that document sharing and signing platforms like DocuSign were popular targets for spoofing this type of attack.
Attackers are also using credible spoofed pages in conjunction with the need to view legal paperwork to get credentials. In Figure 2 you can see a spoofed page with the real estate company’s name in the banner (here redacted) meant to collect credentials when recipients wanted to view an attached file that was purported to be part of a real estate transaction.
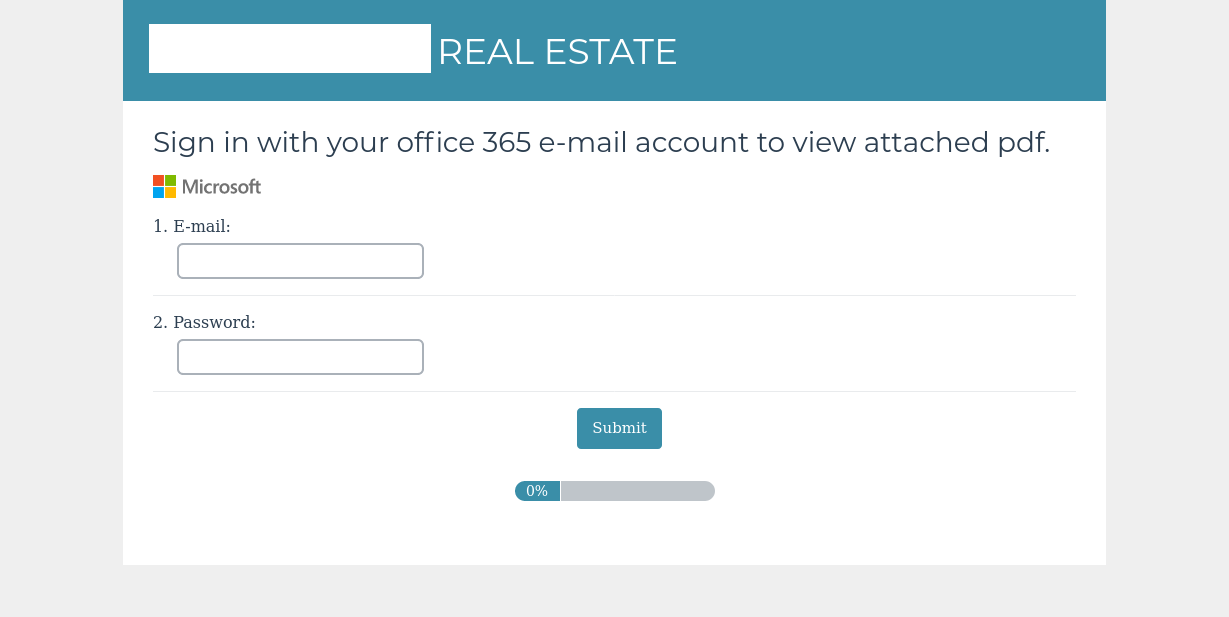
Figure 2 Spoofed Login Page to view attachment
In this case, the emails were sent broadly to brokers at another major real estate company in North America.
Figure 3 shows another example of attackers using the need to view real estate documents as the lure to get user credentials.
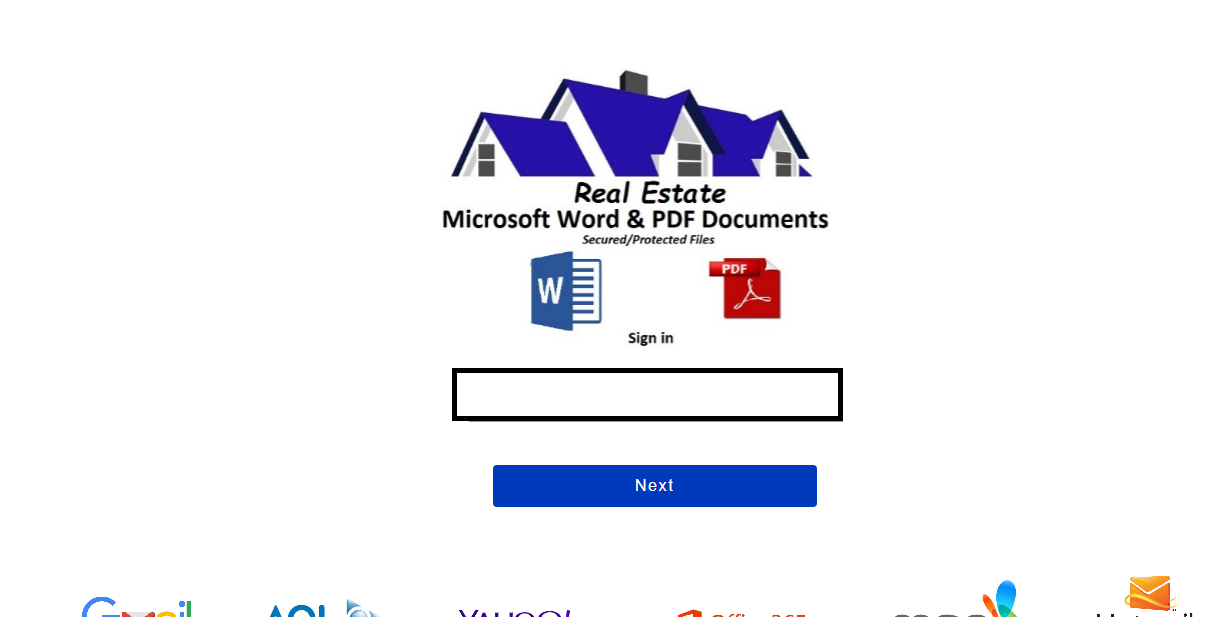
Figure 3 Spoofed Login to Retrieve Documents
In all three cases, the attackers’ goal is to get valid credentials that they can use to access the systems for their later malicious use.
As shown above, attackers know that documents are a key part of real estate transactions and they maximize that fact for their benefit. Another way attackers leverage the use of documents and attachments in real estate is to get malware, like banking Trojans and information stealers, on the system.
In Figure 4 we see a fake document that uses expectation of secured documents as a lure to get the user to click on a download link that will get malware on the system.
Figure 4 Fake Invoice Lure Used to Download Malware
In Figure 5 we can see a variation on this tactic that uses the real estate company’s logo, branding, and even the agent’s name and contact information (redacted here) to increase the credibility of the lure.

Figure 5 Fake Document with Real Estate Company Branding
In these cases, the attackers are trying to get malware on the system that can steal credit card or bank account information. Many types of malware used in these attacks can also steal information like usernames, passwords, email addresses or other information that can be used in follow up attacks.
Another tactic we see is attackers creating fake pages to obtain credit card information from buyers and others involved in the real estate process.
Figure 6 shows a sample our researchers found of a spoofed credit card authorization complete with the logo and name of the real estate company (here redacted).
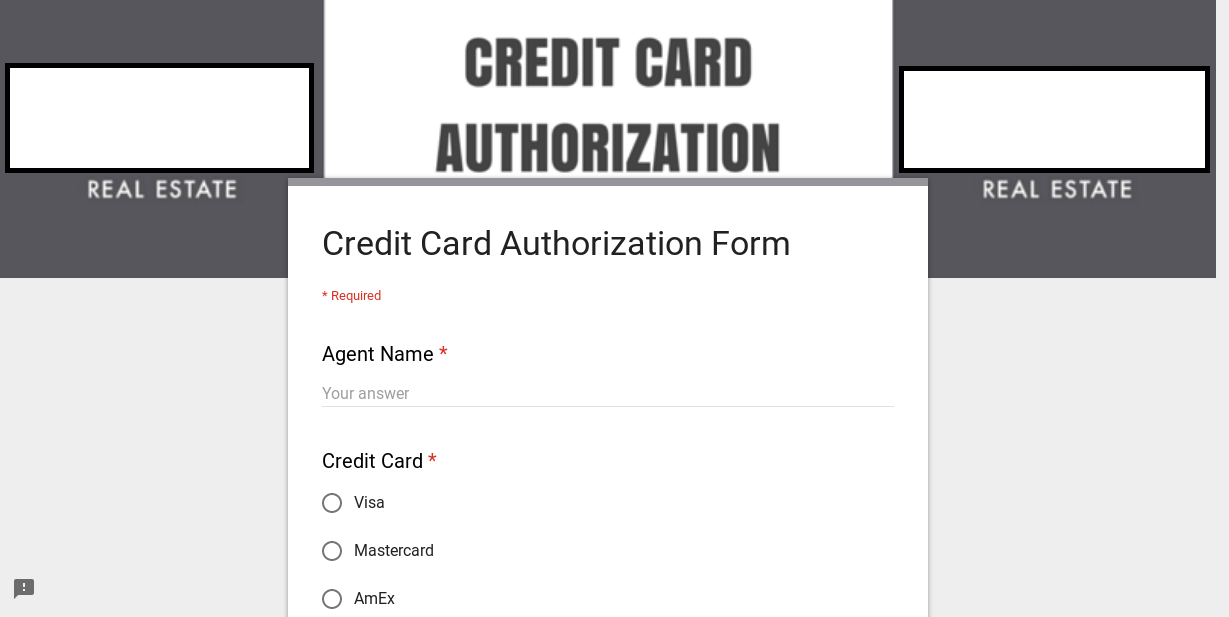
Figure 6 Fake Credit Card Authorization Form
In this case, the attackers’ aims are traditional credit card fraud: using the credibility of the real estate company to convince the recipients to give the attackers their credit card information. The attackers can then use the credit card information themselves or sell it on forums that specialize in the buying and selling of stolen credit card information. And just like with other BEC scams, sometimes the attackers don’t need anything more than an email and a well-meaning employee’s desire to do the right thing. Figure 7 is a sample that shows classic BEC social engineering tactics.
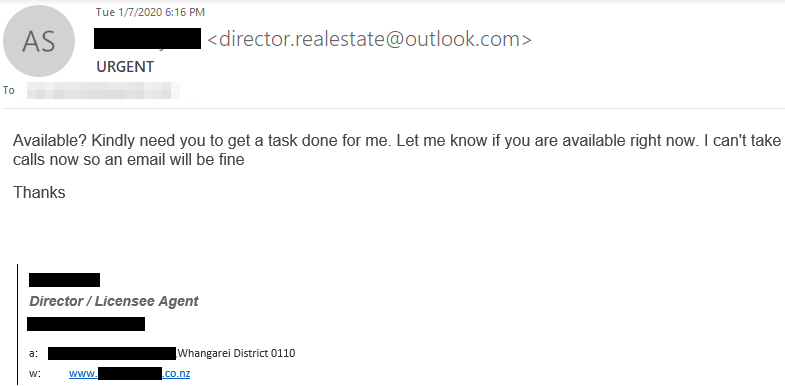
In this case, the attackers are using an email that looks credible with a sense of urgency to try and lure the recipient into an email exchange that the attackers hope will end with the recipient following emailed instructions to transfer money to them.
Steps to Better Protect Yourself
Even with stepped up attacks like this, there are things that you can do that will help you better protect yourself.
Be aware of the greater risks: Everyone involved in real estate transactions should understand that they face greater threats in this process than in other online transactions. Understanding that means you can exercise greater caution throughout the process.
Use two factor authentication: All major web-based email systems like Microsoft Office 365 and Google G Suite support two factor authentication. Many document signing and sharing systems like DocuSign also support two factor authentication. By enabling this, you can protect against attempts to steal credentials and better protect the critical information you’re working with.
Verify the sending and receiving of attachments: Because of the extra risks in real estate around attachments, extra caution makes sense. Take the time to let people know you’re sending attached documents when you do. Take the time to verify with purported senders that they actually sent attached documents when you get them. Remember: a key thing we’re seeing is attackers “hijacking” existing email threads to inject their emails with malicious attachments. Just because you’ve been sending back and forth to someone on an email thread doesn’t mean they actually sent that latest email with an attachment.
Comprehensive security solutions: Real estate firms (and all companies) need to have a comprehensive solution that works to protect all parties (their employees, customers, and business partners) from all forms of email threats and fraud. This solution needs to provide layers of control including email authentication (DMARC) for domain spoofing, dynamic email classification/machine learning technology to detect display name spoofing and lookalike domains at the secure email gateway, and domain monitoring to identify any potentially risky lookalike domains. In addition, cybersecurity awareness training for all employees is encouraged to ensure everyone understands the value of the information they process and how to spot/report email fraud attempts.










