Global events often capture the world’s attention with a combination of wide recognition and a sense of urgency, but they are also unfortunately likely candidates for threat actor campaigns. TA542, the group behind Emotet clearly believes in this and is leveraging the recent Coronavirus health scare and climate change discussion to try and secure clicks. Our threat research team is tracking TA542’s use of the Coronavirus-themed email lures and a revival of their Greta Thunberg-themed campaigns, while also examining threat actors who are starting to register Coronavirus-themed websites that could be used for later fraud.
Currently, Proofpoint researchers are seeing Emotet Coronavirus-themed email attacks using Japanese language lures exclusively and in contrast the Greta Thunberg-themed campaigns are broad in their geographic distribution. They are targeting at least a dozen countries worldwide with Greta Thunberg-themed lures, including: Australia, Austria, Barbados, Germany, Hong Kong, Japan, Malaysia, Singapore, Spain, Switzerland, United Arab Emirates, and the United States.
It’s important to note that TA542 is a group that is capable of carrying out multiple campaigns at the same time. Emotet’s infrastructure is also very test and metric-driven, and is built to scale depending on what’s working.
Coronavirus-Themed Lures: Japan
Some of the emails that we’ve observed come with a sender that reads “京都府山城南保健所福祉室” (Translation to English: Kyoto Prefectural Yamashiro Minami Public Health Center Welfare Room) and “京都府共同募金会” (Translation to English: Kyoto Prefectural Fundraiser).
An example of these emails is shown in Figure 1. Figure 2 shows an English translation of the text.
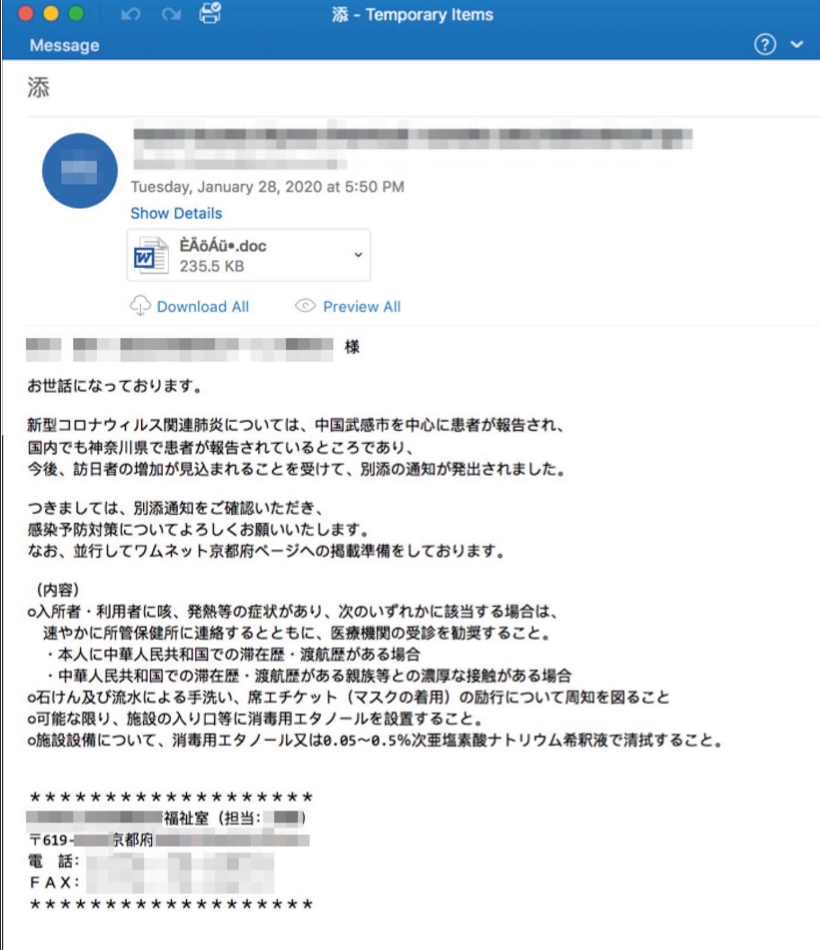
Figure 1 Corona-themed Emotet Lure in Japanese
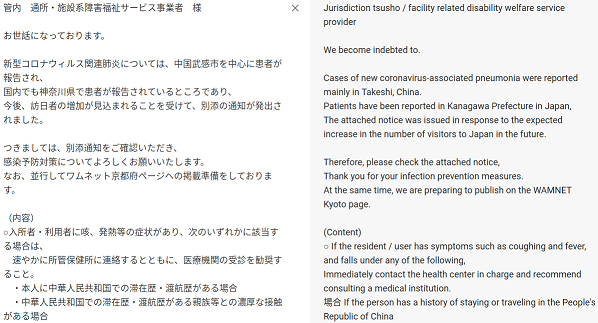
Figure 2 Corona-themed Emotet Lure in Japanese with translation
Interestingly, TA542 has taken the time to include reasonable health guidance in their lure by including information about symptoms and actions to take. This increases the believability of the lure.
As in other Emotet campaigns, many of these emails come with an attached Microsoft Word document with malicious macros. When the document is opened and the user enables the macros, Emotet is installed. We have also seen examples using attached PDF messages and including links to download Microsoft Word documents.
Latest Greta Thunberg-themed Lures
The latest Greta Thunberg-themed lures are very similar to what we saw in December 2019 with much of the same subject lines and attachment names. This time there is no reference to Christmas holidays and a bigger focus on climate change.
One thing that is new: some of these emails are using the offer of free Greta Thunberg-themed t-shirts, pants, pens, posters and mugs as part of the lure. An example of this latest campaign is shown in Figure 3.
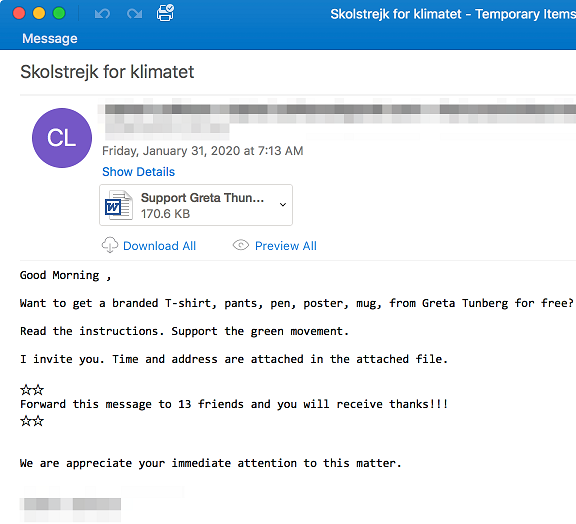
We believe this campaign has been effective for the attackers as very little has changed between the December campaign and this latest effort.
Coronavirus-themed websites
Finally, Proofpoint researchers have been closely watching for other Coronavirus-themed attacks and scams. We’ve observed that attackers are beginning to register Coronavirus-themed URLs and websites. An example of one these is shown in Figure 4.

Figure 4 Recently Registered Coronavirus-themed webpage
While the page we found isn’t active yet, we reasonably believe that it’s possibly an early step in preparation for future coronavirus-related malicious activity.
Protecting Yourself
All of this activity serves as a reminder to exercise caution regarding emails and websites related to current events, particularly ones that appear to ask you to take urgent action surrounding the Coronavirus. Be sure to only visit verified, trusted websites.
It also serves as a reminder that TA542 is a formidable threat actor group with advanced capabilities that enable them to move quickly in response to current events and even smartly, selectively target campaigns based on language and region. It’s important security teams continue to secure their email channel and educate users regarding the increased risks associated with email attachments risks as Emotet is capable of downloading a range of additional malware, spreading across networks, and using infected devices to launch further attacks.










