What is Proofpoint Nexus AI Threat Intelligence Platform?
Proofpoint Nexus® is an ensemble of AI models—that protects people and data by detecting and preventing advanced threats like phishing, BEC, malware, account takeovers, and data breaches across email, collaboration, web, and cloud environments.
Watch now Nexus overview
media:remote_video:f76e9195-803b-426e-8fdc-9c4c617bf009
AI Threat Intelligence at Proofpoint
Decades of precision. Unmatched AI threat intelligence.
The raw processing power of our AI models is only part of the story—true precision comes from the rich, diverse data that fine tunes performance. Fed by daily email analysis, active campaign tracking, threat actor monitoring, and user reported incidents, our models operate within a living, self learning AI threat intelligence ecosystem. This continuous feedback loop makes our detection engines sharper, more powerful, and increasingly effective at stopping threats over time.
“Proofpoint Nexus’s AI models process 2.3T emails yearly, supported by a threat intelligence team that tracks 100+ unique threat actor groups and more than 8,400 active threat campaigns.”
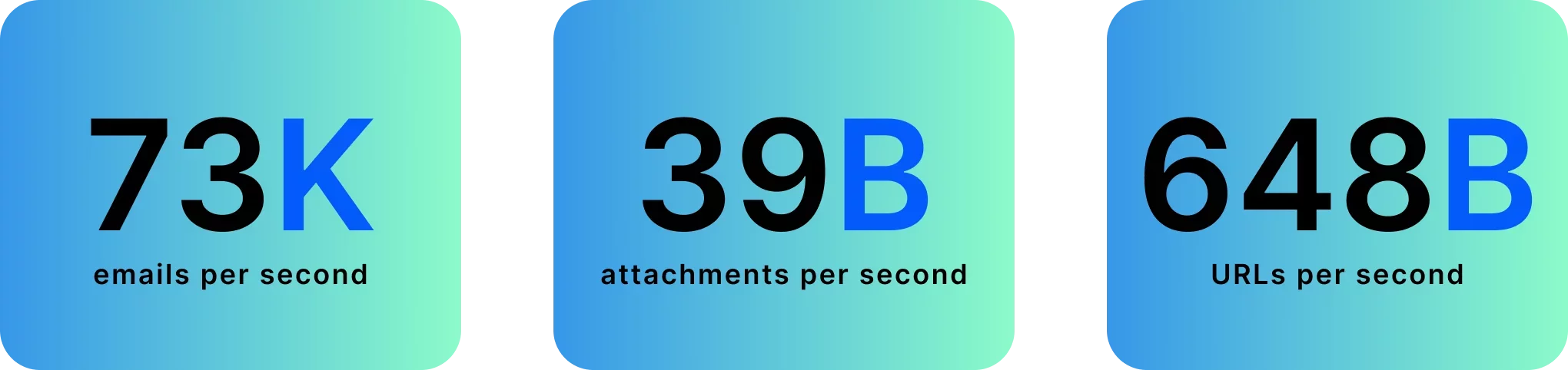
Every Second Delivers New Threat Insights—Nonstop

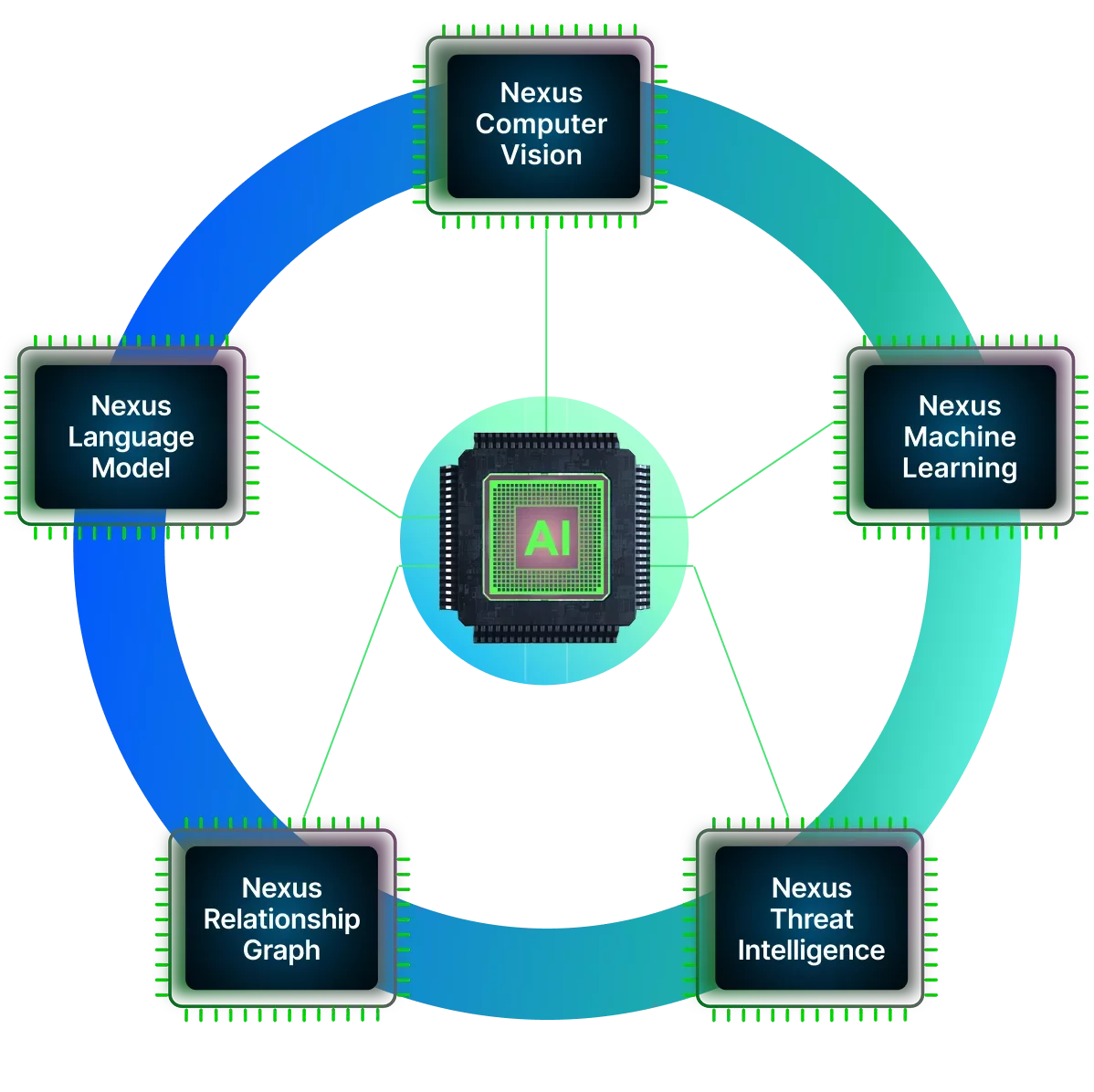
Nexus Language Model (LM)
Detects BEC and sophisticated phishing threats, leveraging advanced language analysis (including transactional language, urgency, context and intent) to uncover hidden threats and unknown data risks.

Nexus Relationship Graph (RG)
Identifies subtle behavioral changes in your users’ communications, detecting deviations in normal user behavior, volumetric changes, sharing of sensitive company data to reduce risks of data leaks and protects against behavior-driven cyber risks.

Nexus AI Threat Intelligence (TI) Platform
Understands attackers’ tactics and proactively protects against new cyberthreats by using real-time intelligence to identify emerging, attacker tactics and system vulnerabilities and triggering sandbox emulation for suspicious URLs and attachments.

Nexus Computer Vision (CV)
Identifies and neutralize vision-based threats. Through advanced computer vision technology, Nexus CV detects threats hidden in visual elements, such as phishing sites, QR codes, malicious attachments and spoofed emails.

Nexus Machine Learning Model (ML)
Dynamic and adaptive learning techniques – like supervised learning, unsupervised learning and ensemble methods – along with predictive threat detection capabilities to map known attack behaviors and unsupervised techniques to detect unknown abnormalities.
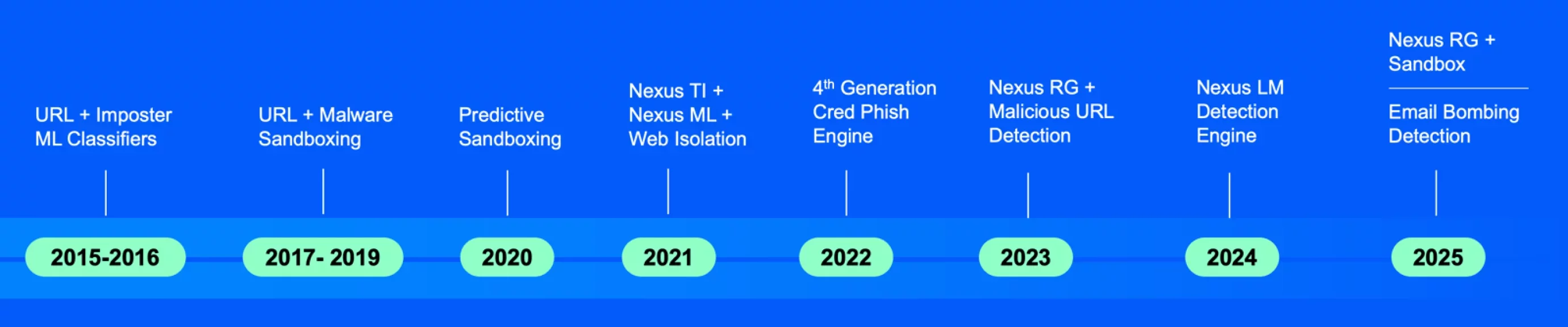
Nexus timeline
Highlighting Proofpoint’s AI threat intelligence platform’s innovation from 2015 to today
-
2015 - 2020 | Groundbreaking Foundations in Predictive Defense
During this era, we pioneered machine-learning-driven imposter classifiers, advanced URL and malware sandboxing, and some of the industry's earliest predictive sandboxing techniques.During this era, we pioneered machine-learning-driven imposter classifiers, advanced URL and malware sandboxing, and some of the industry's earliest predictive sandboxing techniques. These groundbreaking investments laid the technical foundation for today’s speed, efficiency, and rapid model development, giving us a multi-year head start in stopping evolving email attacks.
-
2021 - 2024 | AI Threat Intelligence and Behavior-Aware Detection
From 2021 to 2024, we pushed innovation further with next-generation threat intelligence, ML models that surfaced never-before-seen attack patterns, and web isolation that acted as predictive sandboxing at scale.From 2021 to 2024, we pushed innovation further with next-generation threat intelligence, ML models that surfaced never-before-seen attack patterns, and web isolation that acted as predictive sandboxing at scale. This period delivered a fourth-generation credential phishing engine, a relationship graph fused with malicious URL detection, and a range of language models.
-
2025 and Beyond | Breakthrough Multi-Channel, Multi-Stage Defense for a New Threat Era
Looking ahead, we’re creating stronger defenses against complex, multi-stage attacks.Looking ahead, we’re creating stronger defenses against complex, multi-stage attacks. We’re delivering breakthroughs in email bombing detection, prompt-injection defense, and protection across channels—preparing customers for a rapidly evolving threat landscape that demands AI-driven resilience.
Nexus extends protection beyond inbound email to stop account takeover, supplier-based threats, and attacks initiated through application and third-party messaging channels such as Teams, Slack, and LinkedIn.
In addition to advanced threat detection for inbound email and messages, Nexus supports protection that extends beyond the inbox:
- Messaging Protection automates condemnation and response actions when malicious URLs are identified, including initiating browser isolation for targeted users.
- Supplier Threat Protection identifies known supplier relationships and establishes a baseline of communication patterns to detect anomalous or high-risk activity.
- Account Takeover Protection detects evasion techniques and suspicious mailbox activity, delivers click-time protection through URL rewriting and browser isolation, extracts and analyses URLs, and helps defend against multi-factor authentication (MFA) bypass attempts.
Architected for Flexibility
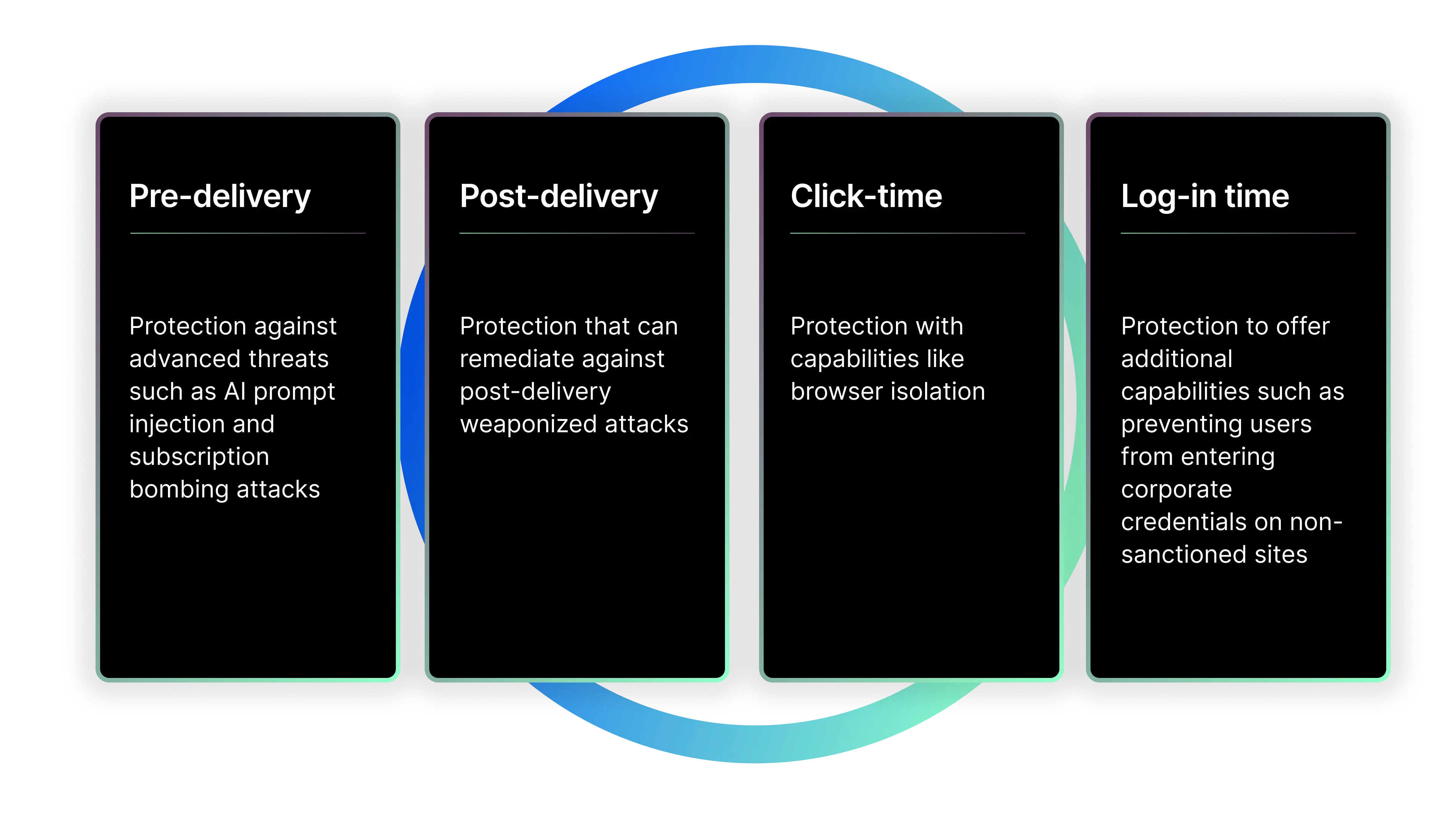
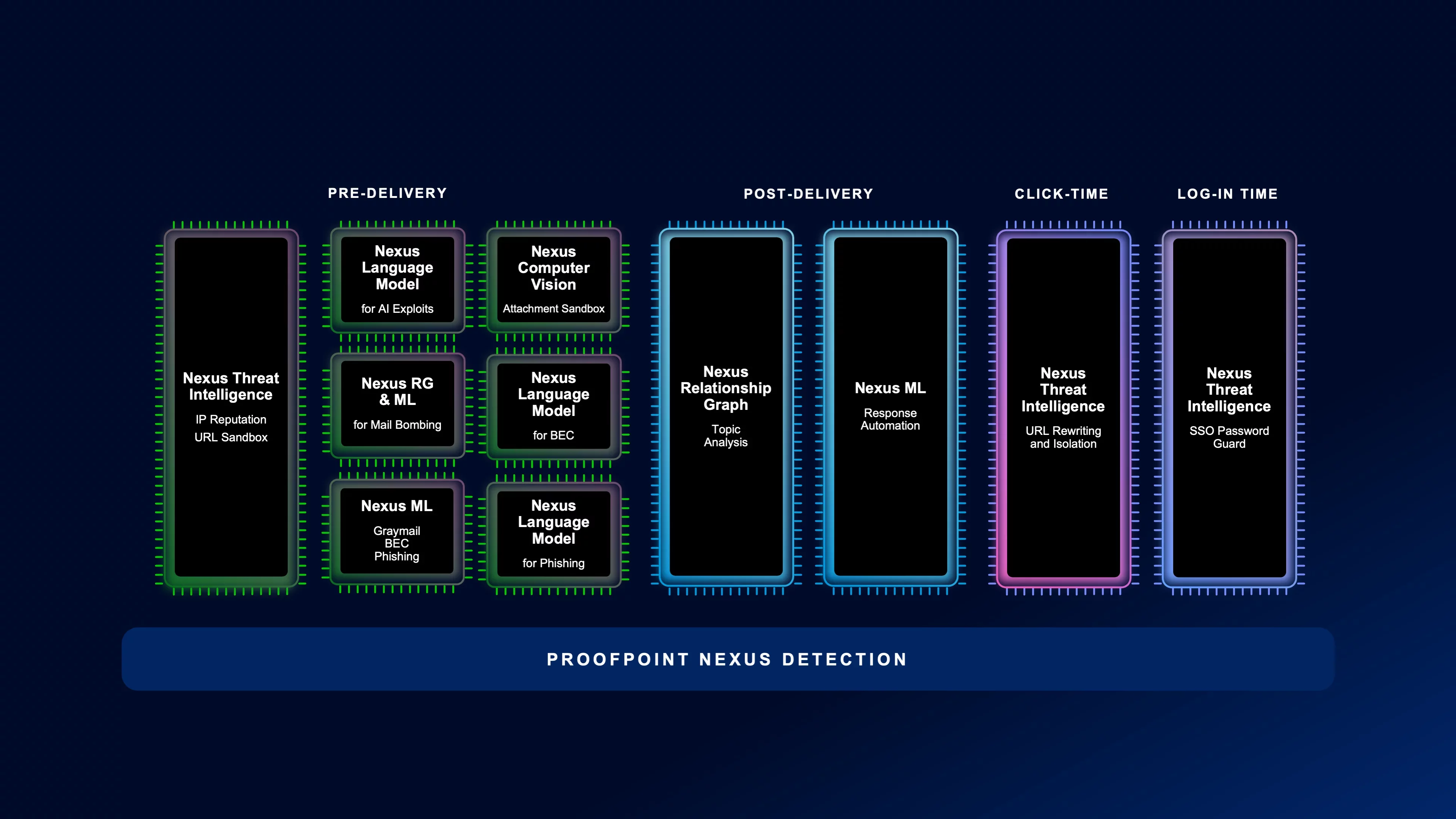
Nexus AI threat intelligence platform protections are embedded across the collaboration threat lifecycle, from pre-delivery to post-delivery, from time of click to login.
Nexus powers Data Security and Governance solutions.
Nexus AI prevents data leaks by categorizing and tracking the path of data and where it flows – both within and outside your organization.
Nexus LM™ (Language Model) learns your organization’s real business document types—like deal materials, forecasts, or product designs. It turns those learned classes into actionable policy context, to quickly discover, prioritize, and protect sensitive data without manual tuning.
Nexus RG™ (Relationship Graph) understands relationships to prevent accidental and intentional data loss from misdirected emails and data exfiltration scenarios.
Nexus TI™ (Threat Intelligence) protects against compromised accounts sending phishing emails both internally and externally.
Nexus CV™ (Computer Vision) detects sensitive content in images within emails and documents.
Nexus ML™ (Machine Learning) provides end-to-end visibility into how files are created, copied, renamed, shared, and moved across repositories and destinations. It connects that activity into a traceable provenance timeline that supports faster investigations, origin-based controls, and audit-ready evidence for data protection programs.