For years, CISOs have struggled to protect their users and identify if unknown URLs are malicious. Even today, organizations still deploy a myriad of security tools to help solve these challenges.
Stopping a threat before the first point of infection is critical to prevent attackers from compromising an organization's most important asset, the people. To properly defend against phishing attacks and targeted attacks requires a multi-layered solution that allows users to maintain continuity of their day-to-day operations, all while keeping the organization secure.
Applying Isolation controls to your Very Attacked People (VAPs)
Modern email threats continue to exploit human nature because it's simple and effective. We continue to see unique malicious URLs on the rise and a relentless focus on credential phish by bad actors. These attackers rely on users to activate the attack or provide their credentials for bad actors to gain access to their systems and launch their attacks from within.
We are excited to announce TAP URL Isolation for VAPs. This enables users to confidently browse unknown websites while still protecting them from URL and web-based attacks and is a critical component to basic email security. This new feature helps protect organizations from URL and web-based attacks for your Very Attacked Persons (VAPs). With this new integration, any URL that is clicked on within corporate email by your VAP users will be analyzed and isolated per configured policy. This will enable them to confidently access websites from their corporate email, knowing that the organization is secure.
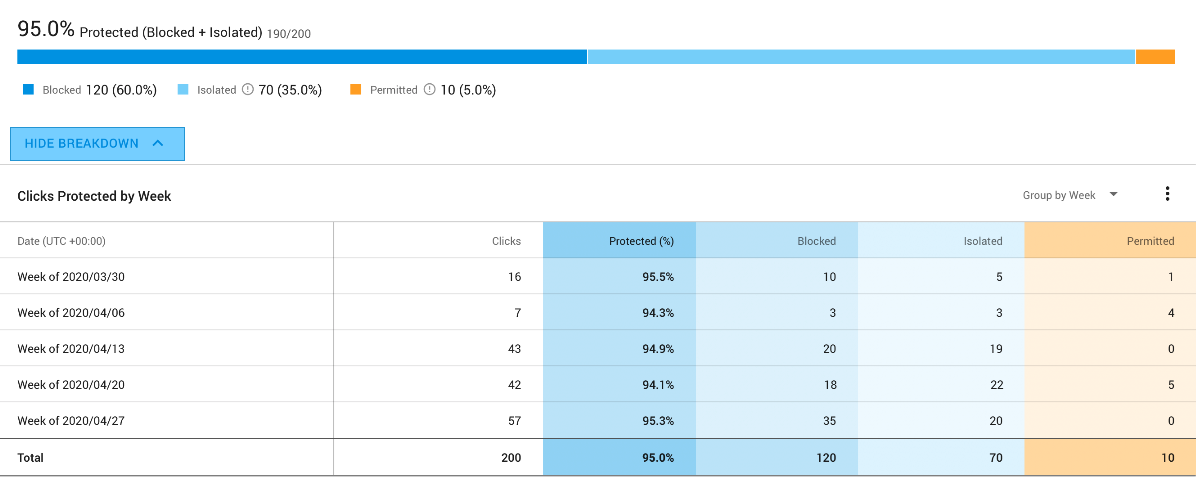
Visibility into isolated clicks through the TAP Dashboard
Visibility into who your VAPs are, how they are being targeted and when they are interacting with potentially malicious URLs is key to protecting your organization today. In the Threat Detail page, you can now view the number of clicks isolated. If your organization has enabled TAP URL Isolation for VAPs, you can understand how many clicks are being protected through TAP's Isolation integration and update your policies within the Proofpoint Isolation console to ensure protection against high-risk categories and activities like isolated user clicks on unknown or malicious URLs within corporate email.
How do these adaptive Isolation controls protect my users?
These adaptive isolation capabilities draw on our expansive threat intelligence. We automatically isolate suspicious URLs based on two predictive scanning methods. First is a reputation check, in which Proofpoint's Nexus Threat Graph helps determine whether a specific URL is subject to our condemned list or not by using a combination of NexusAI machine learning, advanced detection and human expertise. The second is our threat scan in which the html is sent to our static engine check to determine whether the page is malicious. During this time, all keyboard entry is disabled.
This adaptive control mechanism complements Proofpoint Email Protection and Targeted Attack Protection. Users can fully access and interact with most websites. For sites deemed suspicious by initial scans, they can view the site in read-only mode while a full threat analysis is performed behind the scenes. If anything comes back malicious then we would flag this browsing session and block the users from accessing this page.
How to enable TAP URL Isolation for VAPs
All new and existing customers using our P-bundles (P0 and up) will be able to take advantage of this offering at no additional charge. For anyone that is interested in adding isolation for their VAPs, simply reach out to your Proofpoint account teams and they will be able to help you get enabled.
Learn More
Want to apply adaptive isolation controls to your VAPs? Learn more about the Proofpoint Targeted Attack Protection offering here.










