Today, many companies increasingly rely on software-as-a-service (SaaS) to cut their overhead and costs. SaaS apps are now used for a wide array of critical business functions, including human resources, payroll, IT service management and customer relationship management. This trend accelerated during the pandemic. And it shows no signs of slowing down amid the current economic uncertainty and the rise of remote and hybrid work.
Almost every company today is using at least one SaaS solution with an increasing number operating almost entirely on SaaS. While smaller firms might only work with one or two SaaS partners, enterprises could have hundreds or thousands of SaaS solutions in place.
There’s no doubt that SaaS applications offer tremendous business advantages. Yet they also introduce security risks. This is especially true for apps that send transactional emails on a company’s behalf. Beyond the impact of having an overly permissive SPF record, not all of these solutions have the same level of security your company might have.
You don’t have to look hard to find headlines about security breaches involving vendors sending transactional emails for their clients. These compromised sources are approved to send from your domains. And that creates a risk that your employees could become targets. Even if your company is not impacted directly by these breaches, malicious emails sent from compromised SaaS solutions to your customers and partners could damage your brand reputation.
SaaS providers aren’t security companies
One challenge with SaaS applications is that there’s no centralized control over emails sent from your company’s domain. So if your cybersecurity team discovers any security issues, it can’t stop messages from sending. Instead, it must contact the SaaS vendor—and hope that it acts quickly.
Another problem is that not all SaaS partners support email authentication, such as DKIM signing. Not authenticating your transactional emails limits the effectiveness of your company’s DMARC policies
These challenges point to a greater issue—the fact that SaaS providers aren’t security companies. That’s a key reason these businesses are prime targets for bad actors looking to exploit weaknesses.
To keep your company safe, your security team needs centralized control of all transactional emails, whether they’re being sent on behalf of your employees from internal applications or from third-party SaaS partners. All transactional emails should also be scanned for malicious content and DKIM signed before they’re sent out. Additionally, all emails that contain sensitive information would benefit from data loss prevention (DLP) and encryption.
This is where Proofpoint Secure Email Relay (SER) can help.
A cloud-based relay solution that’s truly different
Proofpoint SER secures transactional email. It stops trusted domains from being abused by bad actors who take advantage of vulnerable apps and compromised email service providers.
SER is a cloud-based solution that provides centralized control for relaying transactional email. Not only does it separate transactional email from other email traffic, it also prevents compromised third parties from sending malicious emails using your domains.
What makes this relay solution stand out from the competition is our proven experience in email security. Proofpoint Secure Email Relay provides:
1. Authentication
Only verified sources can submit emails for sending. It’s also easy to authorize third-party SaaS application senders through the DKIM signing process.
2. Threat protection
Proofpoint SER narrows the attack surface by scanning emails for malicious links and attachments.
3. Compliance
With our relay solution, you can encrypt, archive and restrict sensitive data to meet regulatory requirements. Payload encryption and DLP can be applied to email to protect PII and PHI.
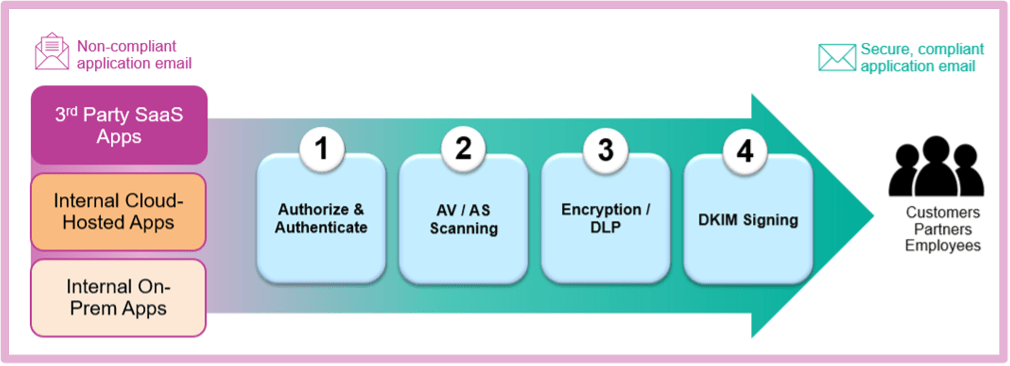
An overview of how Proofpoint SER secures transactional email.
Want to learn more?
You can watch a short video overview, visit the Proofpoint Secure Email Relay product page, or you can join us on June 22, 2023 for our webinar “Stop Email Attacks and Initial Compromise by Securing Transactional Emails” by registering here.










