Digital transformation, work-from-anywhere environments and employee turnover are increasing insider risk. In fact, insider threats are the top cybersecurity concern among chief information security officers (CISOs) globally, according to the “2022 Voice of the CISO” report from Proofpoint.
As the modern way of working shifts, more data is generated and cloud adoption accelerates, CISOs are questioning if their legacy solutions can meet today’s demands. There is one constant factor among these ongoing shifts: people. After all, data doesn’t lose itself; people lose data. And more than half the time, insider threats can be attributed to careless users. These users unknowingly or unintentionally impact an organization’s data or systems negatively.
Due to the high number of careless users, it’s imperative for organizations to ensure these users are aware of—and adhere to—corporate and cybersecurity policies. That will help reduce insider risk. Decreasing risk from careless users also requires a holistic, targeted approach to security awareness that has C-level support, is tailored to user’s unique knowledge gaps and reinforces positive cyber habits.
The classic careless user
A careless user is someone with good intentions who accidentally makes bad decisions. To understand the behavior of a careless user, let’s look at an example.
Meet Warner. He’s part of the research and development (R&D) team at an automotive supplier. Given his role, he has access to valuable intellectual property and works closely with third-party suppliers. Like many people at his company, Warner works remotely.
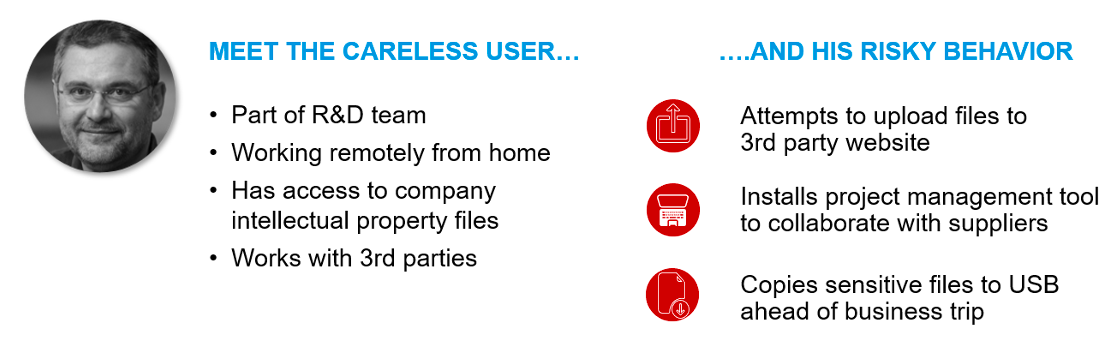
Warner recently started working with a new partner as part of an innovative new product design project. The new partner asked Warner to upload files related to the new product to the website that it uses to manage projects. Warner also decides to install a new project management tool to collaborate with the supplier more easily. Lastly, ahead of a business trip to meet with the supplier, Warner decides he doesn’t want to bring his laptop; instead, he attempts to copy a few sensitive files to a USB drive.
All of Warner’s actions are in violation of corporate policy for handling sensitive intellectual property, so they generate activities and alerts captured by Proofpoint Insider Threat Management.
Given the repeated pattern of Warner’s actions, the security team kicked off an investigation to understand if Warner’s behavior is careless or if he’s motivated by personal gain, which is characteristic of a malicious user. In this scenario, Warner’s behavior is deemed to be careless, and he is enrolled in targeted security awareness training.
Security awareness programs help reduce risk
Security awareness training programs are important inside and outside of the workplace. With the significant increase in remote work driven by the pandemic, users are working from different locations outside their corporate network. Also, people are using personal devices to connect to corporate and personal accounts (e.g., social media, banking, chat services).
As a result, the traditional lines between “professional” and “personal” are blurring, which increases the attack surface. If a user’s personal account gets compromised, for example, it could have devastating consequences for the organization if sensitive corporate data like intellectual property is compromised as a result.
Building good security habits, like reporting malicious messages, helps keep the rest of the organization safe and reduce overall risk. Some critical success factors of an effective security awareness program are that they:
- Move beyond compliance—These programs don’t just stop at “checking a box” or demonstrating completion. They seek to track reporting and click rates to analyze user behavior changes over time.
- Deliver targeted training—Employees have access to various types of data depending on their role and are thus subject to different attack types. Effective security awareness programs provide training based on a user’s unique knowledge gaps and the threats they actively face in the real world.
- Provide training in short, regular intervals—Security teams have limited time to train users, and they also compete with people’s tasks and shortened attention spans. Delivering bite-sized training that users can take in regular intervals not only makes it easier for users to fit into their daily lives, but also reinforces concepts so people don’t forget what they’ve learned over time.
- Assess user knowledge and culture—Knowing how people feel and what they believe about cybersecurity is defined as a security culture. This type of culture influences the likelihood that users will take what they’ve learned and put this knowledge into practice. Thus, it’s critical for security awareness programs to assess security culture and use it to inform future changes to security awareness programs to ensure people stay motivated to learn and apply positive security habits.
- Provide clear reporting and metrics—To ensure that your security awareness program is successful, security teams must get a baseline regularly to help ensure users are changing their behavior and are indeed acting as a strong line of defense. It’s also vital to have clear reports that can help measure success and to share with senior management and the board to get buy-in and budget for future projects.
Take a people-first approach
While most insider threats are attributed to careless users, the good news is that organizations can take tangible steps to educate and bring awareness to risky behavior. To reduce insider risk, organizations should:
- Prioritize educating users on safe cyber practices and share what the consequences of falling for these attacks can be for the organization and their personal lives.
- Make it easy for users to report malicious messages and reinforce this positive behavior through teachable moments. An example is having a “Report Suspicious” phishing email report button.
- Build a security awareness program that fosters a thoughtful cybersecurity culture. Find out what people’s attitudes and beliefs are and help them see the value of being a strong line of defense. Administering a culture assessment survey and analyzing responses is a good starting point. Choose a few changes to implement in the coming year to create a stronger culture if the current one needs improvement.
Users play an important role in safeguarding their organization’s data and systems. And it goes beyond just training users, but ensuring they understand the importance of their behavior.
Learn more
To learn more about decreasing insider risk from careless users with security awareness, view this webinar.
Explore the Insider Threat Management Starter Pack from Proofpoint to gain a deeper understanding of insider threats and how to take a proactive approach.
And to hear how culture assessments can level up your security program, check out this the webinar.










