Proofpoint offered free webinars and training to some of the largest organizations across the globe during Cybersecurity Awareness Month in October. Our essential training helped raise awareness of cybersecurity risks and threats to businesses and provided tips for people to stay safe at home, too.
When we hosted our webinars and workshops, many people specifically asked us how they can stay safe at work, at home and in their personal life. We heard important questions such as: How can I protect my children? What can I do if my password has been leaked? Should I use a virtual private network (VPN) at home?
If your people are conscious of cybersecurity in their daily lives and focused on ensuring their family members are safe online, they’ll naturally apply this mindset at work as well. Your employees can protect your organization against ransomware and email threats like phishing by being more aware of their own cybersecurity behaviors. In short, a secure culture at home translates to a secure culture at work.
Slow down—don’t just click
Consider the following research findings:
- 94% of cyber attacks use email phishing—and almost all these attacks rely on people clicking on something.
- 75% of ransomware attacks start with email phishing.
- Ransomware is the top threat facing European businesses.
You can prevent ransomware attacks by making email security a high priority for your organization. As part of Proofpoint Security Awareness Training, we highlight phishing as one of the top threats to your people.
Here are some of the key takeaways from our training:
- Phishing can affect everyone
- Don't open links or files "on autopilot."
- Trust the rational side of your brain. If in doubt, don't click – report it.
- Slow down to reduce the possibility of clicking something you shouldn't.
The message to users is simple: Take the time to check.
Don’t just click away on autopilot. With busy lives and jobs and time pressures, it’s all too easy to “just keep clicking, just keep clicking.” But the best thing your people can do is question every link or attachment they receive. If they do that, it will soon become an innate behavior—like a defensive autopilot that turns “just keep clicking” into “just keep checking.”
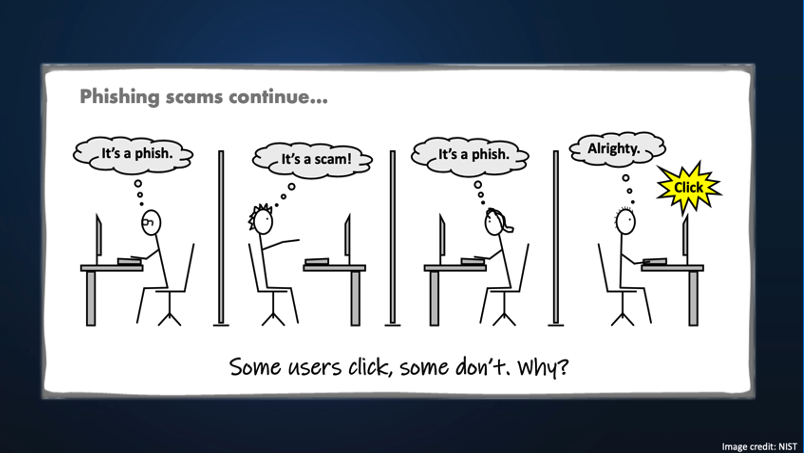
Figure 1. National Institute of Standards and Technology (NIST) cartoon about phishing and user behavior
To click or not to click?
Hackers often use our human and social instincts to trick us into opening harmful emails. They love to draw on our emotional responses. We just can’t help it—as humans, it’s how we’re programmed.
So, urge your people to be on the lookout for emails with overly emotive subject lines, such as, “Unexpected redundancies—please read urgently.” Messages like these are designed to bait users into clicking.
“We got into your network through phishing. The email with the malicious attachment was opened by an employee ... the user is asked to include the document’s macro, to display the content, click on the link, etc.”—Clop Ransomware Gang
Top tips for your people
The following tips can help your users avoid a phishing attack:
Tip 1: Look out for attachments you’re not expecting.
If you must do something before viewing the content of an attachment, STOP, and report it.
Tip 2: Link? Stop. Think.
Fraudulent links could take you to a phishing website where you’re asked to enter your personal login details or carry out a payment. STOP. Think. Don’t click that link.
Tip 3: Be suspicious.
Look out for abnormalities in the email, such as:
- The sender domain name—is it really them?
- The email signature—does it look legitimate?
- Is the sender asking for a payment you weren’t expecting?
- Are they stressing some urgency?
Typos and poor grammar are also big giveaways. If in any doubt—report it, don’t click.
What if a user does click?
If that happens, tell them they should:
- Report it to the IT team so they’re aware of the attack entering the organization.
- If any personal information was shared, think about what was shared and how it could be used. Look out for any phishing attacks that could be related.
- If you logged in to something, change your password directly on the main website.
In addition to educating your users, you can protect your organization from email-based attacks with Proofpoint Email Security and Protection solutions that prevent fraudulent messages from reaching your users in the first place.
Protect the people most important to you
Our extensive research tells us that hackers target people, not technology. And Proofpoint solutions can help you understand who the Very Attacked People™ (VAPs) are in your business.
However, it’s important to remember that people aren’t just targeted at work. Our personal email, our mobile phones, tablets and smart watches, and even our children accessing our devices all could be at risk of attack. So, it’s critical for users to be vigilant at work and at home.
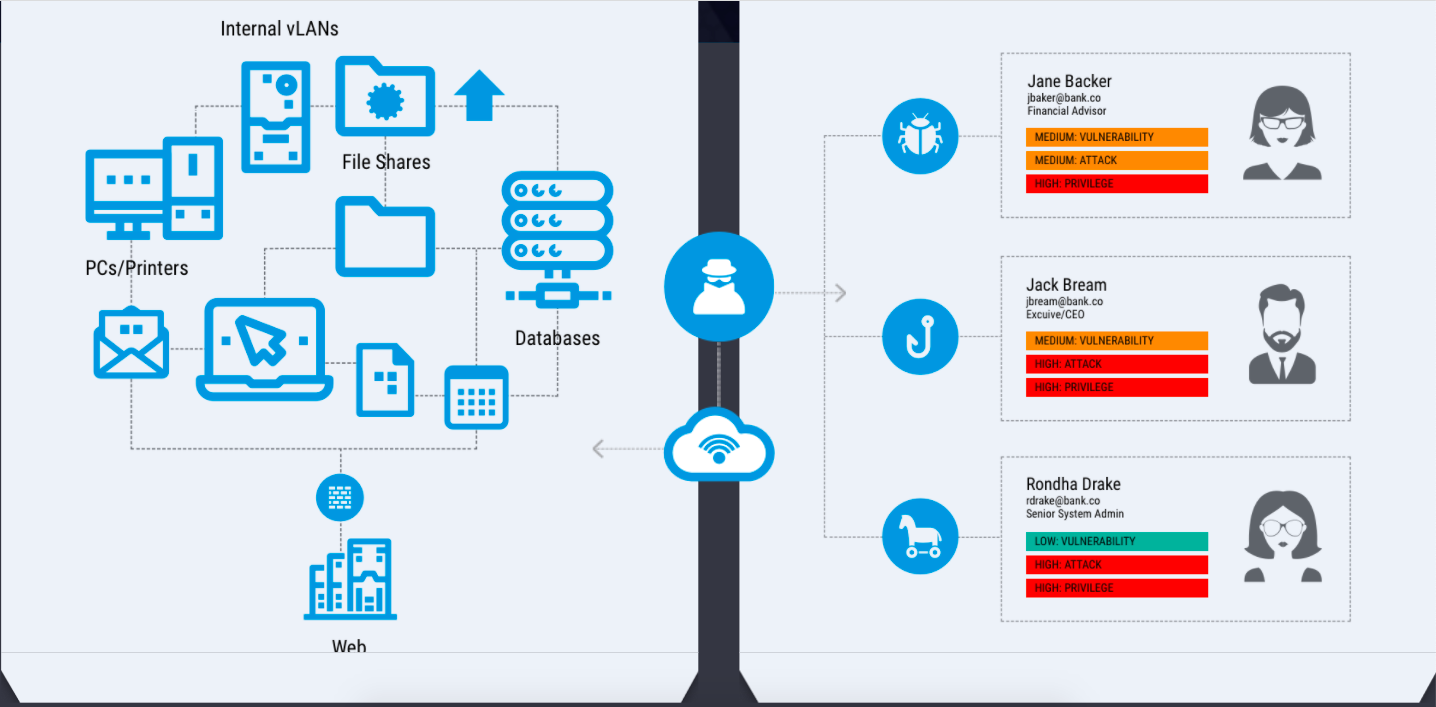
Figure 2. Outdated view of an attack (left) vs. a modern view (right)
Bring cybersecurity home
Encourage your people to follow these practices at home, and they’ll be likely to do the same while at work:
- Make sure to use unique passwords for different websites.
- Don’t share sensitive information publicly.
- Keep software up to date, even your browser. If there’s an update, do it.
- Use the PhishAlarm® phishing button or spam/junk reporting button to report questionable emails.
- Use two-factor authentication wherever you can; this process adds another layer of security beyond using a password.
- Use parental controls on games and apps and be aware of the websites your children are using. Encourage them to talk to you about anything they’re unsure about.
- Use a VPN to improve the privacy of your website traffic from your internet service provider (ISP).
- Make sure your home Wi-Fi network is password-protected.
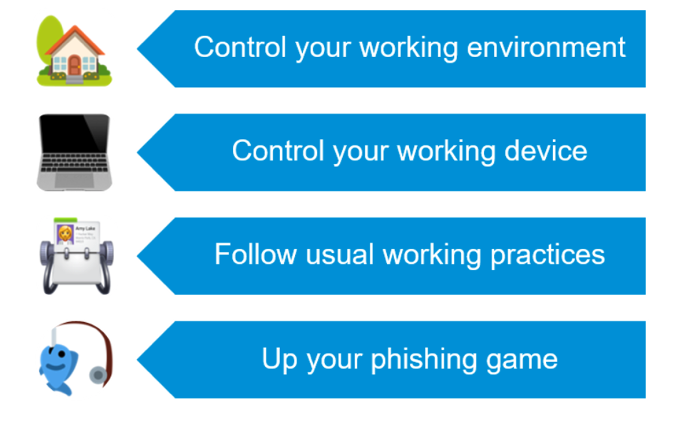
Figure 3. Tips for bringing cybersecurity home
Find out more about how to protect your organization against ransomware in the Proofpoint e-book, Ransomware Survival Guide. Also, remember to tell your users to “just keep checking.”










