Cybersecurity awareness month is here, and with it, a renewed focus on people as an important component of cybersecurity resilience. The 2019 Verizon Data Breach Investigations Report (DBIR) found 94% of breaches are from attacks targeting people, so efforts educating your end users are critical to protecting your organization.
The Washington Post recently highlight a simulated phishing attack gone wrong. The simulated phishing attack in question highlighted executive bonuses at an organization that had endured furloughs and layoffs in recent years. Users considered it insensitive, and the department that had sent the email apologized.
This is a good learning opportunity for information security departments that are running any form of a security awareness program to keep a few of the top tips for cybersecurity awareness month in mind.
Simulated Phish Are Assessments, Not Education
Phishing is the most discussed topic in security awareness programs as it’s the No. 1 threat vector. Consequently admins running security awareness programs spend a lot of time discussing simulated phishing. Will the next simulation be complex and targeted or broad and go to everyone? Will it use a similar attack to one seen in the wild? How did the most recent click rate compare with the last?
These exercises are just tests for understanding vulnerability – not education. They’re a great way to give users the “ah-ha” moment that they’re vulnerable, but don’t engage and teach skills about what to do and how to avoid real phishing messages. The vast majority of users who “fail” and are taken to landing pages or messages that appear quickly, but close it in embarrassment after only a few seconds.
It’s important to build out an awareness and education plan with users outside of simulated phishing exercises to build that knowledge and skillset.
Build Your Education Plan and Focus on the Positives
It’s good to focus your security education on vulnerable users – those clicking simulated or even real attacks. It’s also essential to build rich, educational experiences with a diverse set of engaging content that help users build all the necessary skills to avoid and report today’s attacks.

Delivering education means using multiple, different types of content and channels as your users will likely have different preferences. Some users prefer in-person sessions, others want video, and some want interactive or game-based training. Diversifying how you deliver and reinforce it is essential to making it resonate with your users. Simulated phishing alone will not drive as impactful of behavior change.
As you’re planning your education think about the following:
- Does training follow a consistent theme that will resonate with your users?
- Do users have a choice of training formats?
- Is most of the training corporate or are there opportunities to inject some humor?
- Are there additional security awareness materials (PDFs, infographics, images, etc.) you can leverage in a way to reinforce the message?
- Is training short and repeated throughout the year or does it happen all at once (the former is more effective)?
- Are there opportunities like newsletters, town halls, or other existing channels to get your security awareness message out there?
An important aspect of security awareness is the awareness of your program with users. Users have a lot of competing priorities, so part of your program’s job is to get their attention, and provide them engagements that are valuable to them.
Staying positive goes beyond messaging in the training. Go beyond the click rate (of simulated phish) as the key metric for your security awareness program and think about more positive metrics and ways to present and guide your program efforts:
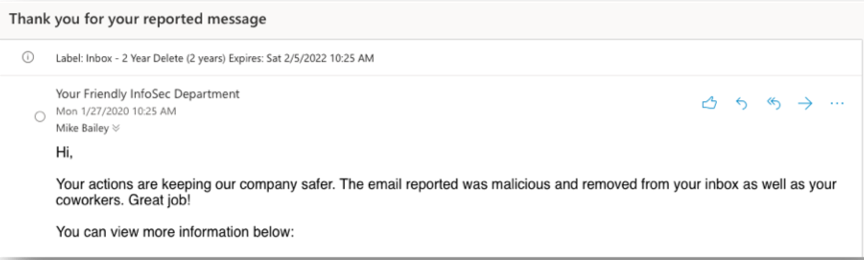
- Is the reporting rate of simulated phishing emails going up?
- Are users reporting more real phish to your abuse mailbox? Are they using an email reporting add-in more frequently?
- Are knowledge levels of key topics improving for your users?
- Are users participating more in security awareness activities?
These metrics demonstrate that not only is user vulnerability decreasing, but user resilience and knowledge is improving to actively stop real attacks.
The Content You Send Reflects on Your Department
Every simulated phish sent, every communication sent to employees, every word and image in training and awareness content is a reflection of your department to the organization. Content should be reviewed by multiple stakeholders in the organization to ensure the message is tailored for your organization and the intended audience.
The goal of simulated phishing is to understand user vulnerability. Verbiage in them can be crafty and even deceiving, but shouldn’t be tone-deaf to the organizational culture or situation.
For organizations distributed in more than one country, different audiences could have different reactions to your message due to cultural nuances. A best practice we’ve heard from many customers is to have local country leaders review messaging to ensure something doesn’t get lost in translation or is insensitive to certain users in your organization.
Get on the Path to Security Awareness Success
When incorporating these security awareness tips, remember that security awareness programs should be positive for users, stakeholders, and people running them. Positive engagement with your program is critical to building a sustainable and effective program.
To help you start your program or improve it by implementing these cybersecurity awareness month tips, we’ve put together a comprehensive e-Book, Driving Real Behavior Change: The Complete Guide to Building a Security Awareness Program that Works. We highlight key facts, strategies, resources, and tips you can utilize regardless of your vendor to implement your security awareness program.