Cybersecurity is about more than technology and technical controls. While technical controls are certainly important, the heart of your cybersecurity strategy should be people—because it is how people behave with emails, data and cloud applications that directly impact your organization’s security posture.
Addressing the people aspect of cybersecurity is more critical than ever given today’s threat landscape. Attackers continue to target people and commonly use social engineering as part of their attacks. Ransomware attacks often require a person to download a malicious attachment or give up their credentials to gain initial access to your organization. According to the latest Verizon Data Breach Report, 85% of data breaches involved a human element and 61% of breaches involved credentials.
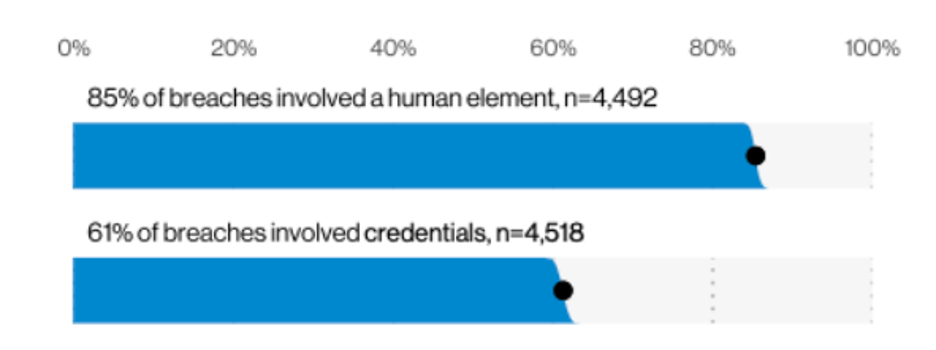
People play a critical role in your organization’s cybersecurity strategy (source: 2021 Verizon Data Breach Report)
Security Culture Drives Employee Behavior
A strong culture of cybersecurity can have an enormous impact on your security posture. Why? Culture drives behavior. For example, in parts of Asia slurping while eating is a sign that you’re enjoying the food. However, in many European countries, eating loudly is considered rude and frowned upon.
A culture that values security shapes employee attitudes and behaviors. When your leaders and employees believe that cybersecurity is everyone’s responsibility and not just IT’s job, then they do things to keep the organization secure because it’s valued and important. More importantly, your people and their security-aware behaviors become a strong line of defense.
How to Build a Security Culture in the Workplace
So, how do you go about building a culture of security within your organization? Here are some starting points to build a stronger culture of security:
- Gain support from the top: While everyone in an organization affects security culture, executives and managers have a greater influence by the nature of their roles. Company leaders often set the tone for the rest of the organization. If the CEO regularly talks about cybersecurity and how it aligns with the organization’s goals at every staff meeting and all-hands meeting, it sends a message that keeping the company’s data and systems secure matters.
- Identify desired security behaviors: If behaviors are a manifestation of culture, what security behaviors do you want to start seeing from your employees? Develop a defined number of key behaviors that are tangible to the employee. Some examples include: “Think before you click,” or “If it looks suspicious, report it.” Once you’ve identified the desired behaviors, provide clear pillars to build your security awareness training program around.
- Make security awareness ongoing: A strong security culture doesn’t happen overnight. It isn’t created from a single event, like annual security awareness training. Building a strong culture for security takes sustained and consistent effort. If you’re doing security awareness training once a year, consider shifting to shorter training delivered quarterly. Also look for internal communication vehicles (e.g., town halls, newsletters, company intranet) to engage your employees and drive behavior change.
- Reward good security behavior: Celebrate when an employee demonstrates good security behavior. Recognizing and rewarding the desired security behavior creates positive reinforcement and encourages others to behave in the same way. Rewards don’t have to be fancy or expensive. Have fun with the rewards. Some organizations give a fish trophy to the employee who reports the most suspicious messages in a quarter. Others give users who report a suspicious message a bag of goldfish crackers.
Security culture is an essential part of any organization's cybersecurity strategy. It can help create sustained behavior change that transforms your people from targets to a strong last line of defense.
To learn more about how you can build a strong cybersecurity culture for your organization, join us for our Art and Science of Building Security Culture virtual event series.










