As the global pandemic continues to run rampant, CISOs are not only struggling to solve traditional cybersecurity challenges, but are also faced with a new surge of pandemic themed phishing scams intended to deceive users and infiltrate organizations. Of these, credential phishing still remains one of the most common tactics used by threat actors. These attacks send an email with a URL that takes victims to a fake website designed to steal their credentials. Most of the time these fake sites are so well crafted that they look real and no matter how much training users have, sooner or later someone is going to click on a bad link and enter in their credentials.
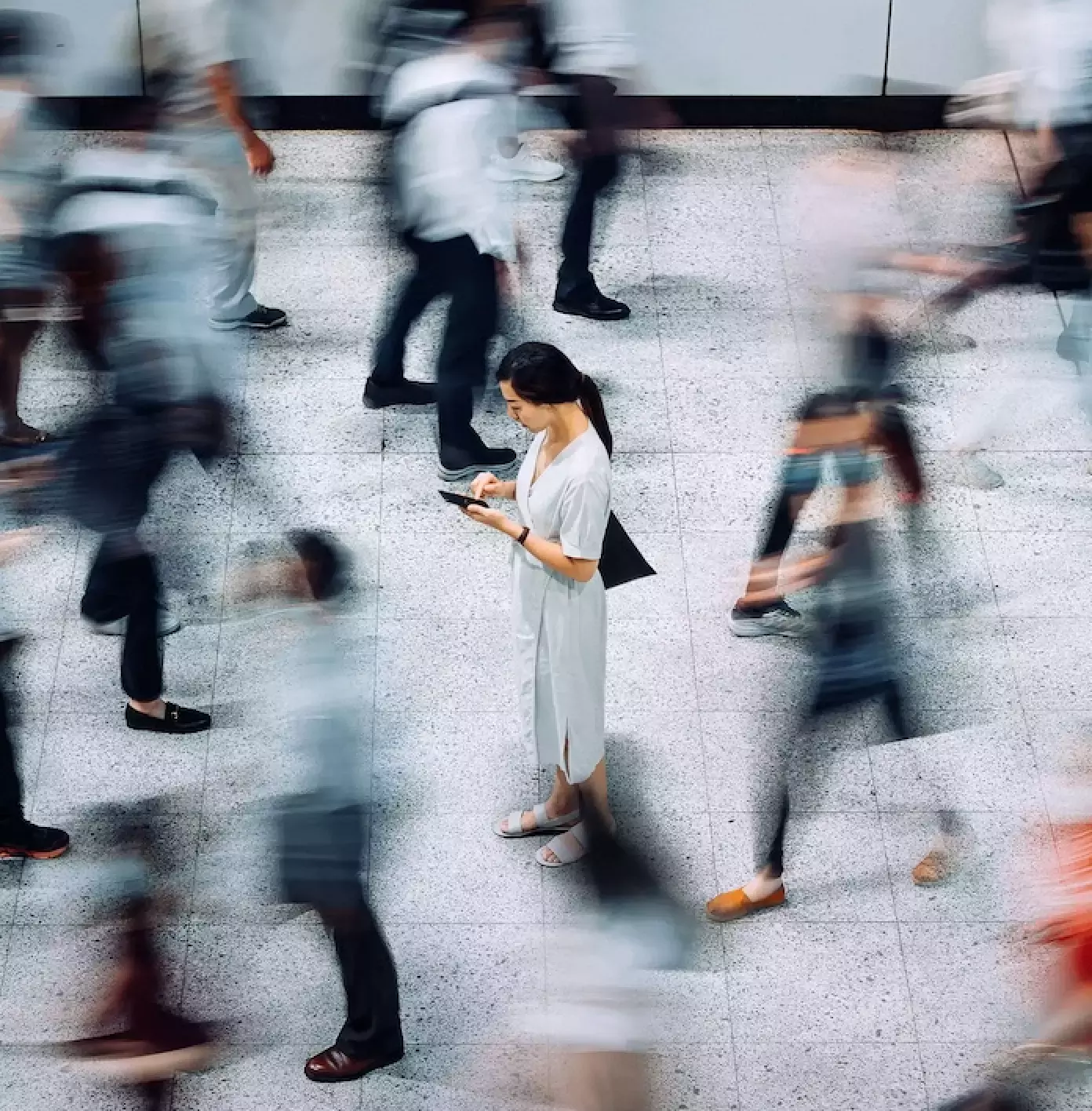
Operating from multiple countries, these threat actors have become increasingly sophisticated in their attempts to lure users into clicking a malicious link and divulging confidential account credentials, often targeting individuals with customized attacks through corporate and personal email. With the shift to work from home and hybrid work environments, many of these people are now working outside the confines of a traditional corporate perimeter, increasing their vulnerability. For that very reason protection must start with people, protecting them from advanced threat tactics and arming them with knowledge and tools to help protect the organization. And protection must focus on email, which is the primary target of attackers.
Understanding the impact of these credential phishing emails and socially engineered attacks is key to implementing a successful people centric security strategy. The Cybersecurity Guide for the Modern Era takes a deep dive into user behavior and phishing, two top concerns of CISOs and top cyber security professionals, and explains how to put the right security tools in place for the way people work today. This report helps answer key questions like:
- How can people-centric data and adaptive security controls help bolster phishing defense?
- How to deploy an effective layered email defense?
- How do I make my users more resilient to phishing scams?
Isolation for today’s changing workforce
As credential phishing emails increasingly putting our people at risk, having the right security measures in place is critical to protecting users and their email. Being able to understand which users are most at risk, how to best train them and being able to apply adaptive security controls are all ways to help implement a successful security strategy. Capabilities like isolation allow you to apply adaptive security controls to users based on risk profiles. This people-centric approach enables you to set custom policies and URL rewriting for targeted users, also known as Very Attacked People™ (VAPs), effectively lowering your attack surface as employees use corporate email. It is important to avoid a one-size-fits-all approach and find a solution that allows you to better protect users and manage risk for your entire organization.
One other important area that is often overlooked is personal email on work related devices. While many employees continue to work from home or remain in a hybrid work environment, there has been a significant increase in the amount of personal activity performed on corporate owned devices. The seventh annual State of the Phish report, which compiles data from millions of simulated phish and user-reported messages, shows that personal email activity on work related devices in the most frequently performed activity outside of their daily work tasks, making this the second largest threat vector for bad actors. That’s why gaining visibility and applying adaptive security controls are critical for protecting your users. Things like email Isolation can allow users to access risky or unknown URLs through their corporate and personal email by isolating sessions in a secure container. This technology helps prevent credential theft and protects users against things like malware and other malicious content. This is especially important for credential phishing emails which contain URLs and become unsafe post-delivery. Best of all, IT Teams can have peace of mind allowing users to navigate to links inside of their email without worrying about accidentally triggering a malicious link or file.
So as credential phishing emails expand putting your company’s infrastructure and people at risk, having the right security tools in place with adaptive security controls is critical. For more details around how to keep your employees, data and customers secure, download our email security guide.
Subscribe to the Proofpoint Blog