The lines continue to blur between personal and business use of technology, and the rise of BYOD probably bears much of the blame. This has occurred despite the fact that many organizations do define those lines in “acceptable use” policies that govern use of corporate IT assets, including on-premises internet access and employer-issued laptops, tablets, and smartphones.
Whether at work or school, many of us have agreed to such acceptable use and/or security policies — and soon forgotten or outright disregarded them. In fact, many people are comfortable treating employer-issued devices as their own — even if it means exposing sensitive information, increasing their vulnerability to phishing, or flaunting their organization’s security policy.
Who’s Really Using Your Corporate Devices?
Our 2018 User Risk Report reveals surprising insights about the cybersecurity habits of working adults, including how they use employer-issued devices for personal activities. For the report, we surveyed 6,000 technology users across six countries — the US, UK, France, Germany, Italy, and Australia.
We found that 25% of global respondents regularly use corporate laptops or smartphones at home; that number is significantly higher among US respondents (35%). And there’s nothing necessarily wrong with that: In addition to remote employees, many workers are expected to be available when they are outside the office. The problem comes when people use these devices for personal (and potentially risky) activities — a problem compounded by connecting over unsecured home WiFi networks, another issue revealed by our survey.
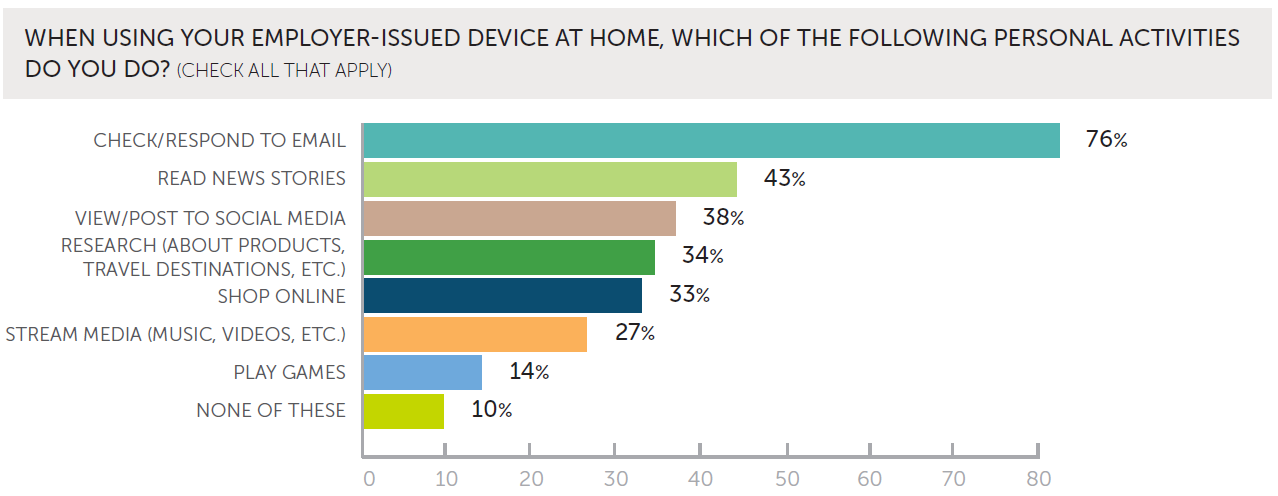
As the following data shows, working adults who use employer-issued devices at home are highly likely to use them for a range of personal activities, including online shopping and gaming. In fact, just 10% of respondents said they do not perform non-work tasks on these devices.
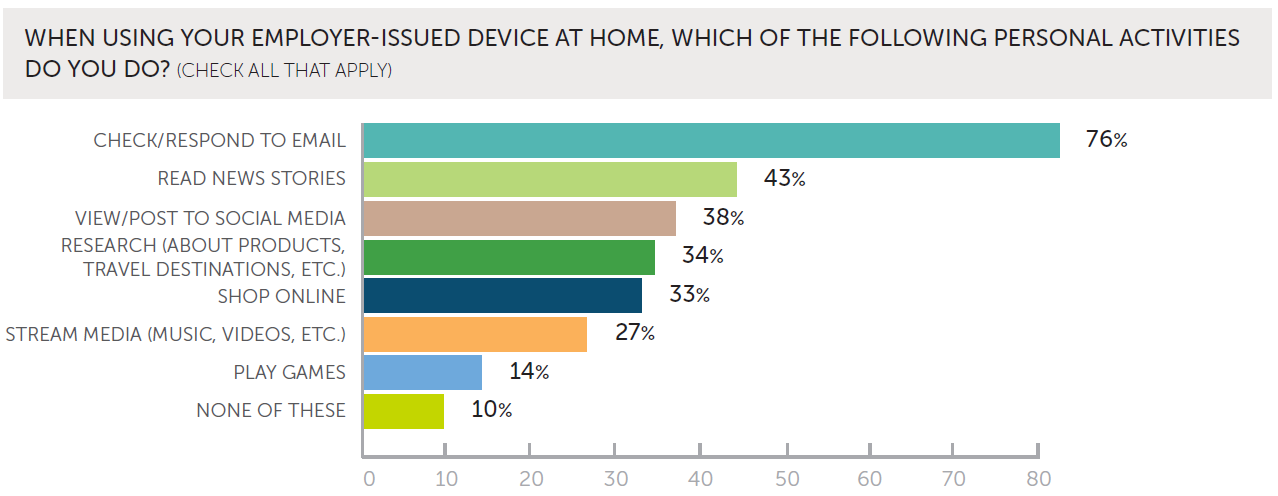
Source: Wombat Security, 2018 User Risk Report.
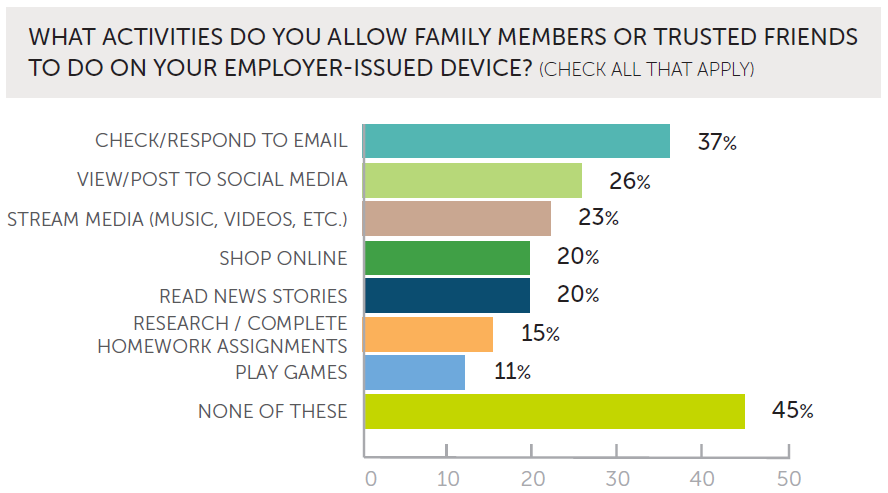
Particularly troubling is that, of those using corporate devices at home, 55% extend access to family members or trusted friends. We found that US respondents were the most permissive: 75% said they grant access to friends and family.
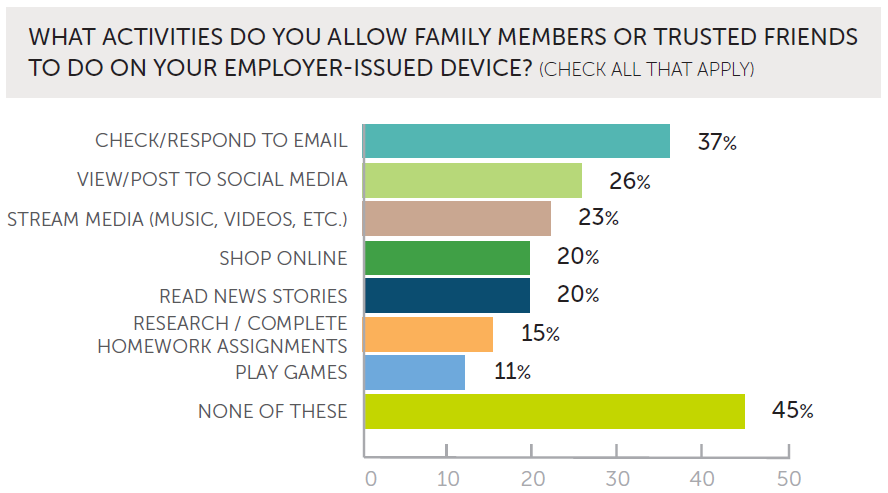
Source: Wombat Security, 2018 User Risk Report.
Why Do Users Violate Security Policies?
Clearly, allowing friends and family to use one’s corporate device introduces unnecessary risks, and almost certainly violates security policies. But many of the personal activities shown in our survey are things that plenty of employees — even infosec professionals — are likely to do at some point. Who hasn’t streamed music from their laptop while working, or occasionally logged in to their personal email account to handle an urgent issue? Bending the rules a bit may seem harmless, but it’s a slippery slope — particularly for untrained employees.
We can only speculate as to why people indulge in these risky behaviors. A recent Dark Reading article offers several explanations for why employees violate security policies, some of which apply to personal use of corporate devices.
The No. 1 reason? Ignorance. A 2018 survey by market research firm Clutch showed that nearly a third of employees don’t know whether their company has a cybersecurity policy. According to Dark Reading, this indicates that “companies are failing to communicate the rules through effective awareness training and internal marketing.”
Convenience is another reason for violating security policies. While the article emphasizes the ways employees get around cumbersome tools and processes, convenience likely plays a role in how they use corporate devices at home. For example, it’s more expedient to access a private email account on a company device than to stop what you’re doing and start up your own laptop.
The Risks of Personal Email and Browsing
Personal email and web browsing activities can do more than just violate policy. They also increase phishing susceptibility, according to a recent article on the Proofpoint blog.
“Email is so well suited to attacks that personal webmail, and personal browsing more generally, is now joining corporate email as a major source of compromised accounts and endpoints,” author Mark Guntrip advises. While corporate email gets much of the attention from infosec professionals, employees can also “fall for a phishing attack through their personal webmail on their corporate laptop, which all too often is accessed off the corporate network and its security controls.”
The article notes that organizations can use technical controls to mitigate the risks inherent in employees’ personal browsing and email activities: Proofpoint’s web isolation solution is designed to prevent malicious content from infecting or impacting corporate devices and to protect end users from known phishing sites.
But what if you don’t (or can’t) apply these technical controls? And what about activities like social sharing and extending device access to family and friends? The surest path to better cyber hygiene and improved security postures is to change employee behaviors. Effective security awareness training is essential for teaching users how to safely manage their email, post to social media, browse the internet, and so on.
Instilling Good Habits, Establishing Boundaries
Some overlap between business and personal technology use may be unavoidable. All the more reason why end users need to understand your organization’s security policy, and be trained to apply cybersecurity best practices — particularly when using corporate devices outside the office. This will help to instill more secure behaviors in your end users — even if they do break the rules regarding personal use.
With that said, one boundary should be made crystal clear, both in policy and in direct training: End users should not lend their employer-issued laptops or smartphones to anyone — including coworkers, family members, and friends — unless authorized by your IT team.
As our User Risk Report shows, many people are all too comfortable with using work devices for personal activities. This propensity is just one of many poor end-user habits that can increase risk for your organization. Interactive, engaging security awareness training is essential to establishing boundaries, instilling good habits, and helping end users understand the reasoning behind your security policies.