Overview
The fourth quarter of 2017 saw a number of shifts in the threat landscape, from a return to malicious document attachments after Q3’s spike in URLs to the emergence of coin mining modules in major malware strains like The Trick banking Trojan. Through these shifts, however, ransomware remained the top threat by volume across the Proofpoint customer base, while threats in social media channels continued to increase across the board quarter-over-quarter.
Banking Trojans regained some ground in terms of overall message volume, largely as a result of massive campaigns from a single actor, while rapid increases in cryptocurrency values drove noteworthy changes in threat actor behavior beyond the ongoing increases in malicious coin mining activity. Moreover, while exploit kit traffic declined further, a number of document exploits appeared in the wild, adding more elements to threat actors’ toolkits.
Here are key takeaways from this quarter’s Proofpoint Threat Report:
Threat actors made a rapid swing back to the use of malicious document (maldoc) attachments in the fourth quarter of 2017 after high-volume URL-based attacks characterized Q3. Emails bearing maldocs jumped 300%, with much of this traffic stemming from massive attack campaigns that abused Microsoft's Dynamic Data Exchange (DDE) protocol. Other exploits also drove increased distribution of malicious documents as actors attempted to burn them before patches were widely deployed.
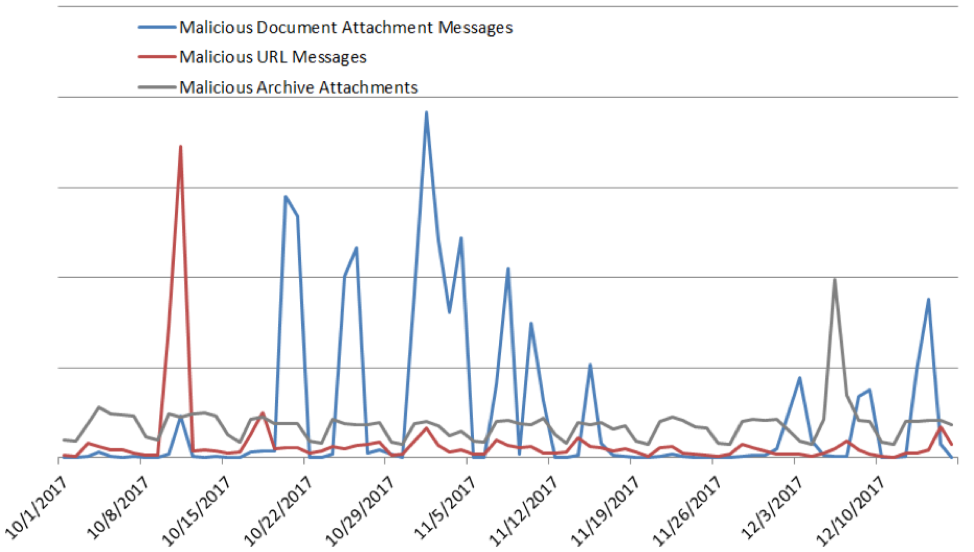
Figure 1: Indexed malicious message volume by attack type
Whether distributed with document attachments or via URLs, ransomware remained the top payload distributed in malicious messages, accounting for 57% of all malicious message volume. Rapid and wide swings in cryptocurrency values also appeared to affect the ransomware market, with payment demands denominated in Bitcoin falling 73% quarter over quarter. Instead, attackers are increasingly setting ransom amounts in terms of U.S. dollars or local currency, although payments themselves are still generally made in Bitcoin.
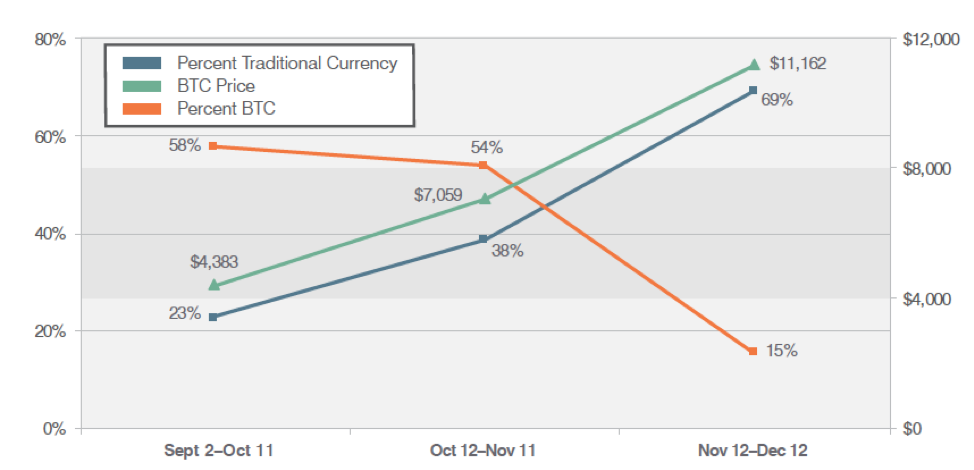
Figure 2: Denomination of ransomware ransoms, 90-day trend
Banking Trojans, notably The Trick and Emotet, also appeared frequently. The Trick was the most widely distributed banking Trojan via email, accounting for 84% of all malicious spam that contained a banking Trojan. The Trick, like many other malware strains, also added a coin mining module, creating new monetization pathways for its operators.
A wide range of attacks continued to incorporate spoofing and social engineering techniques including lookalike and typosquatted domains. For the first time, we analyzed lookalike domains and found that character-swapping was the top technique used to create domains that could be confused with those of an established brand or organization.
Exploit Kits and Web-Based Attacks
Exploit kit (EK) traffic fell another 31% from Q3, hitting its lowest level in years. However, social engineering techniques continued to grow in web-based attacks while remaining EK activity consolidated around RIG EK.
Social Media
Both of the key threats that we track on social media channels grew during Q4. Fraudulent customer support accounts on social media used for so-called “angler phishing” rose 30%. At the same time, phishing links in social media grew 70% from the previous quarter.
Proofpoint Recommendations
The Q4 Threat Report provides insight into the shifting threat landscape that can inform your cybersecurity strategy. Here are our top recommendations for how you can protect your company and brand in the coming months.
Assume users will click. Social engineering is increasingly the most popular way to launch email attacks and criminals continue to find new ways to exploit the human factor. Leverage a solution that identifies and quarantines both inbound email threats targeting employees and outbound threats targeting customers before they reach the inbox.
Build a robust email fraud defense. Highly-targeted, low volume email fraud scams often have no payload at all and are thus difficult to detect. Invest in a solution that has dynamic classification capabilities that you can use to build quarantine and blocking policies.
Protect your brand reputation and customers. Fight attacks targeting your customers over social media, email, and mobile—especially fraudulent accounts that piggyback on your brand. Look for a comprehensive social media security solution that scans all social networks and reports fraudulent activity.
Partner with a threat intelligence vendor. Smaller, more targeted attacks call for sophisticated threat intelligence. Leverage a solution that combines static and dynamic techniques to detect new attack tools, tactics, and targets, as well as a constantly shifting landscape—and then learns from them.
For more details about Q4 threats and trends, download the full report.










