Just like peanut butter and chocolate, when you add threat intelligence to a security awareness program, it’s the perfect pairing. Together, they can help you efficiently train one of your most important yet most attacked lines of defense—your people. A robust security awareness program that is tailored, defined and driven by real-world threat insights and context is one of the strongest defenses you can implement.
Every week, the Proofpoint Security Awareness team gets regular updates about new and emerging threats and social engineering trends from the Proofpoint Threat Intelligence Services team. This helps drive the development of our security awareness platform. Likewise, our customers can generate daily, weekly, monthly and ad-hoc threat intelligence reports to boost the efficacy of their security awareness programs.
In this blog, we will discuss some ways that security awareness teams (SATs) can use threat intelligence from Proofpoint to supercharge their awareness programs.
Tailor your program to defend against the latest threats
Not all people within a company see the same threats. And the response to threats differs greatly across teams—even within the same business. That’s why security awareness programs shouldn’t a take one-size-fits-all approach.
Here’s where Proofpoint Threat Intelligence Services can help. Our team regularly briefs customers about which threat actors are targeting their business and industry, who within their company is clicking, which users and departments are attacked most, and what threats they’re being targeted with.
Proofpoint gives SAT teams the data they need so they can tailor the modules, training and phishing simulations to match those that their users face.
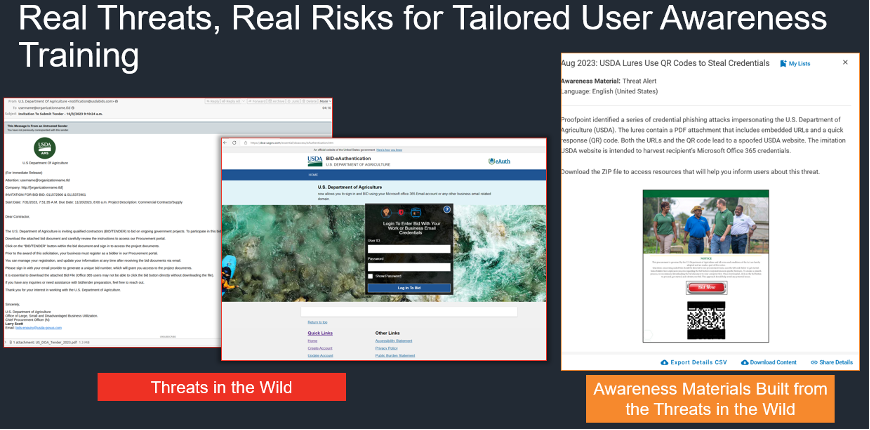
Threats in the wild are converted to valuable, tailored awareness materials.
Use cases
Our threat intelligence services team analyzes exactly what threat actors are targeting when they go after a customer—both in terms of volume, but also at a granular department level. We regularly observe that it’s more common for specific actors to target users within a specific department.
Are threat actors targeting a specific department?
This is a good example of how SAT teams can use threat intelligence to identify departments that are at risk and help keep them safe.
In this case study, Proofpoint Threat Intelligence Services revealed that TA578—an initial access broker—was frequently targeting marketing and corporate communications departments with a standard copyright violation message lure. We highlighted this trend for a particular customer as we reviewed their TAP data.
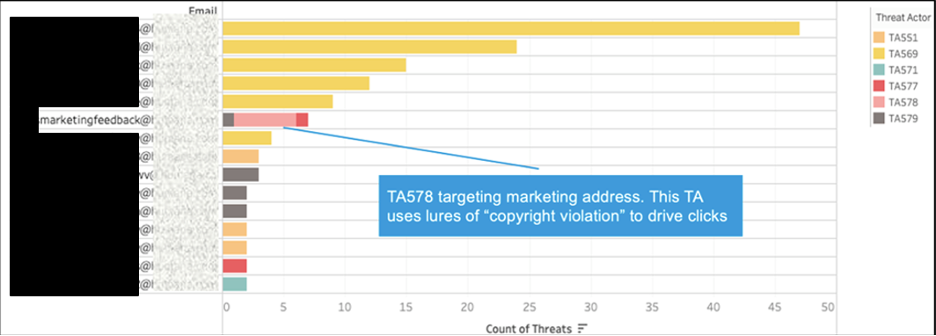
This Proofpoint threat actor victimology report shows that TA578 is targeting a marketing address.
Proofpoint Threat Intelligence Services identified what was happening and also provided additional context about the threat actor, including:
- Tactics, techniques and procedures (TTPs)
- Malware payloads
- Attack chains
- Specific examples of message lures and landing pages
Plus, Proofpoint offered recommendations for remediation and proactive, layered protection.
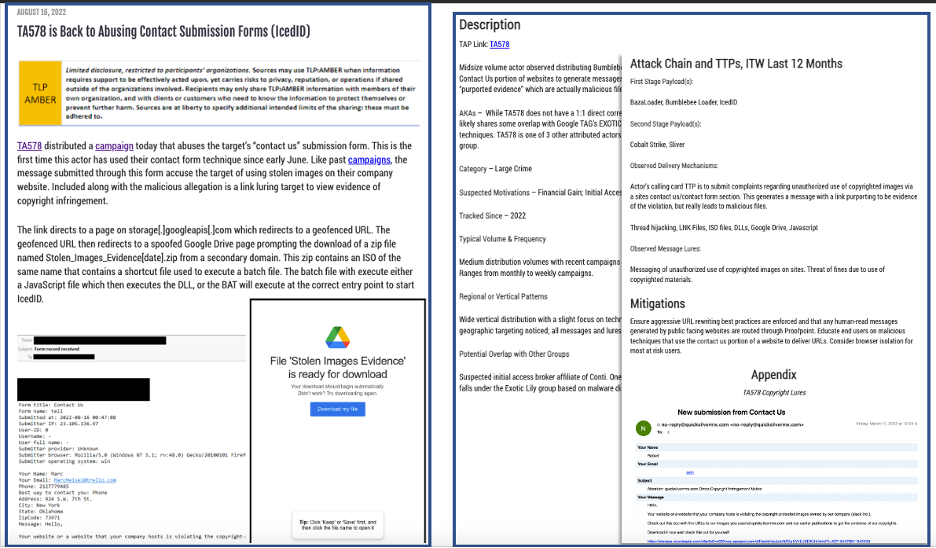
Proofpoint Threat Intelligence Services report on TA578.
The SAT team used this information in its Proofpoint Security Awareness program to train the marketing department about specific message lures. The team also created a phishing simulation that used a similar-style lure and content to educate those users about this unique threat.
Are threat actors targeting specific people?
Another use case for Proofpoint Threat Intelligence Services is that it can help SAT teams understand who at their company is clicking—and what types of message themes they are clicking on.
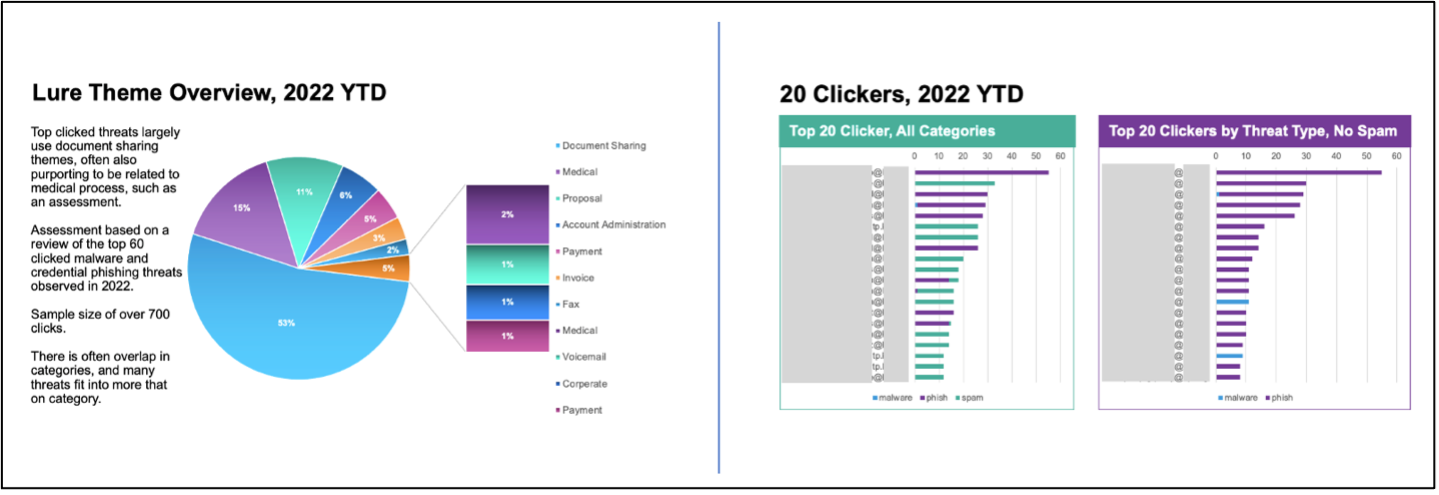
Proofpoint Threat Intelligence Services report for a large healthcare customer.
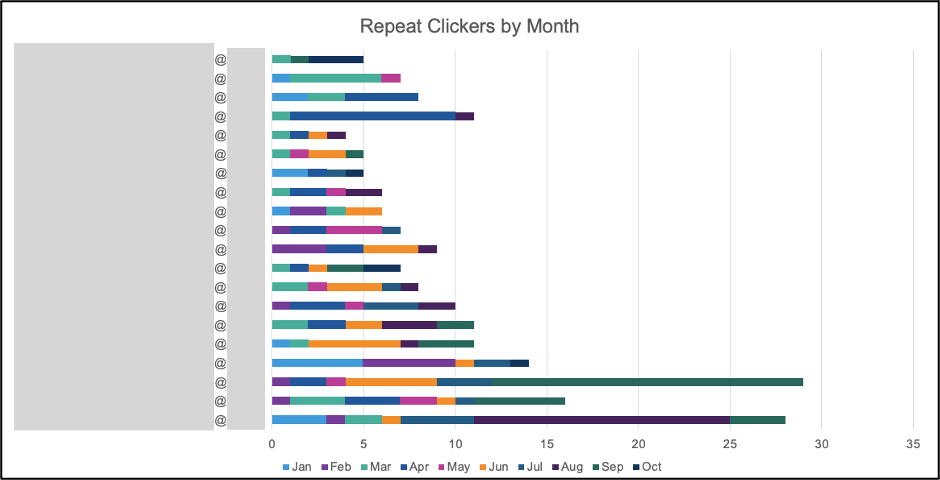
Proofpoint Threat Intelligence Services report shows which users are repeat clickers.
This data is compiled from real threats that users have clicked on. SAT teams can use it to prioritize these users for additional awareness training. They can also pinpoint specific topics that these users—and all users across the company—tend to click on. With this data, SAT teams can ensure their users are seeing the most relevant and targeted awareness training.
Is our program effective?
Another invaluable metric for SAT teams is real-world click rate. It’s helpful to track and compare this rate with a company’s peers in its own vertical, region and size. Proofpoint Threat Intelligence Services generates this report on a monthly basis for our customers. It can help SAT teams to gauge whether their awareness programs are effective at driving down click rates.
Comparing real-world click rates with phishing simulation click rates is another useful metric that can help SAT teams determine the effectiveness of their security awareness programs.
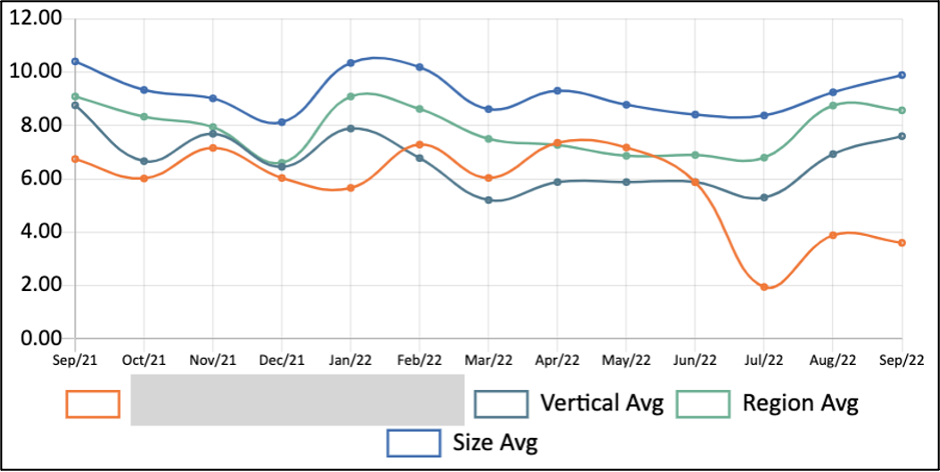
The 12-month click-rate chart generated by Proofpoint Threat Intelligence Services for a large financial services company.
Are threats targeting specific regions?
For businesses that have a global and geographically dispersed employee population, combining click rates with global data can be incredibly effective. Proofpoint Threat Intelligence Services has worked closely with large global businesses to highlight geographically relevant threats for users in certain countries, which their managed Proofpoint Security Awareness teams have been able to use to tailor training based on geography.
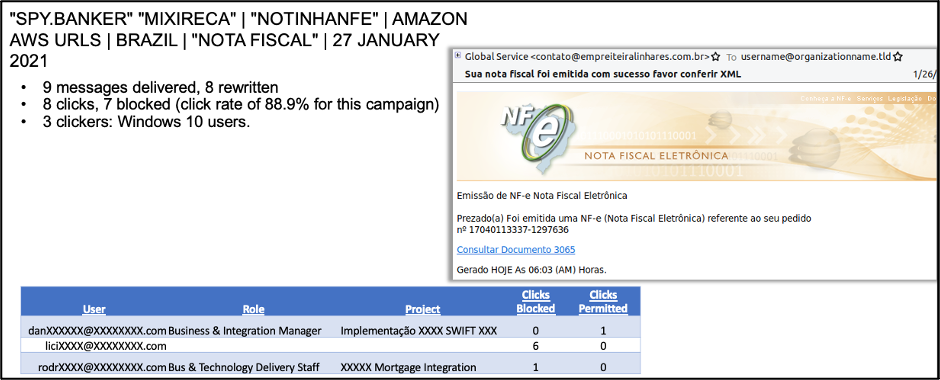
A geo-targeted threat that Proofpoint flagged for additional follow-up action.
A productive partnership
Proofpoint teams in threat intelligence services and security awareness collaborate closely. While the report topics vary, social engineering is a common underlying theme.
This partnership supports a feedback loop of intelligence that benefits the customers of both teams. The Proofpoint Threat Intelligence Services team shares the real-world threats, methodologies and social engineering tactics that threat actors use to encourage victim interaction. And the Proofpoint Security Awareness team provides tailored and actionable recommendations on how to train users to spot these tactics in the wild.
Both teams have partnered on emerging threats where user training may be a top defense measure as other tools evolve to identify these threats. QR code phishing and telephone-oriented attack delivery (TOAD) threats are great examples of emerging threats, and the teams have jointly produced several reports for customers that are focused on these threats.
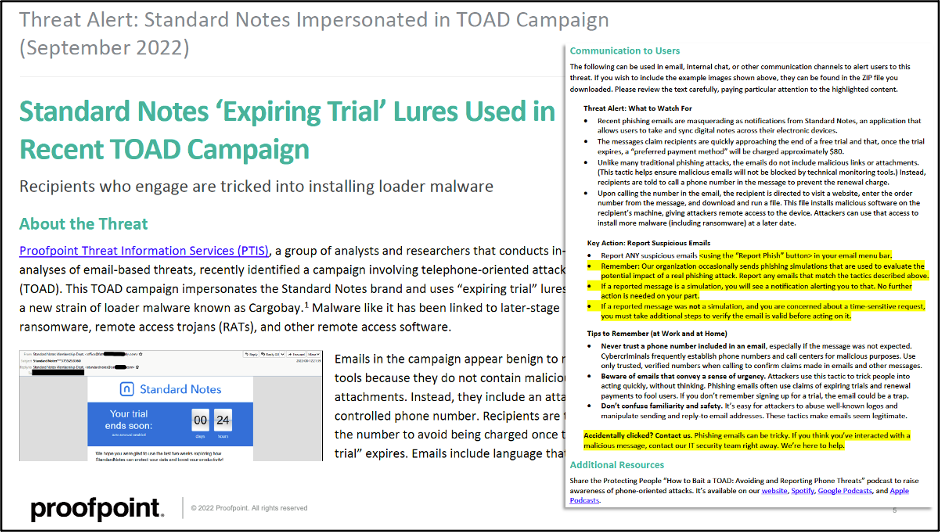
Part of the Proofpoint Security Awareness platform, the Threat Tipper report is based on shared, internal threat intelligence about emerging and novel threats in the landscape.
A few best practices for security awareness programs
Focused threat intelligence can help you to amplify the effectiveness of your security awareness programs. Here are some best practices to keep in mind:
- Use real-world data. You need data to understand who in your business is at the center of the three main categories of risk: Very Attacked People™, top clickers and privileged people.
- Find the individuals and departments who are most at risk. Then, use tailored awareness training to simulate what those users are most likely to see and click on.
- Stay abreast of shifting trends in the landscape. You should know which threats are the most successful. Then, add them to your user awareness training cycle.
- Emphasize that security is a shared responsibility. It’s only through team partnerships and working together that we can keep our organizations safe.
Learn more
When you combine Proofpoint Threat Intelligence Services with Proofpoint Security Awareness, you can increase the effectiveness of your awareness program. To learn more, reach out to your Proofpoint account representative.
If you want to learn how one of our customers uses threat intelligence in its awareness program, check out our webinar, "How McDonald’s Keeps Its Security Awareness Fresh and Relevant."
And get more insights from a customer session we held during Proofpoint Wisdom 2023 entitled “Utilizing Threat Intel to Design a Program that Works.”










